All posts tagged "malware"
-

 199Vulnerabilities
199VulnerabilitiesD-Link Accidentally Leaks Private Code-Signing Keys
A simple mistake by networking gear manufacturer D-Link could have opened the door for costly damage. Private keys used to sign software...
-
 111Malware
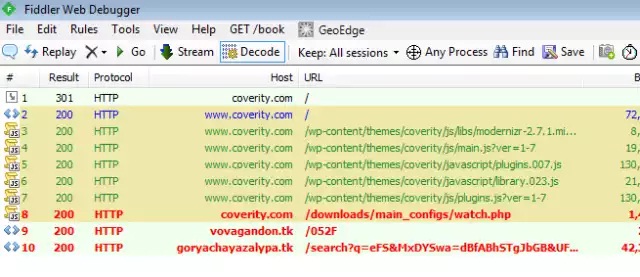
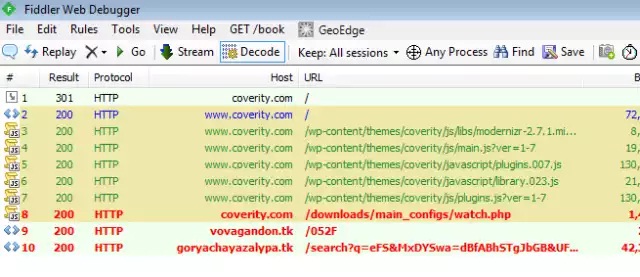
111MalwareActive malware campaign uses thousands of WordPress sites to infect visitors
15-day-old campaign has spiked in past 48 hours, with >5,000 new infections daily. Attackers have hijacked thousands of websites running the WordPress...
-
 102Malware
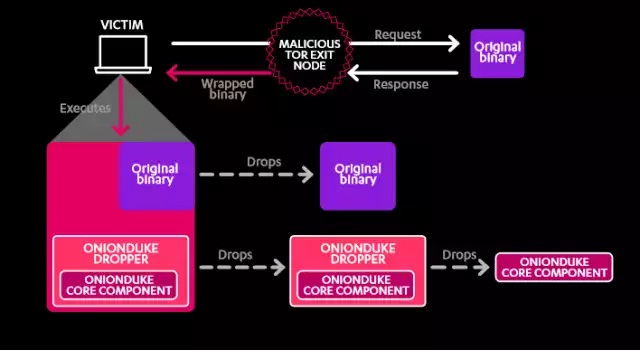
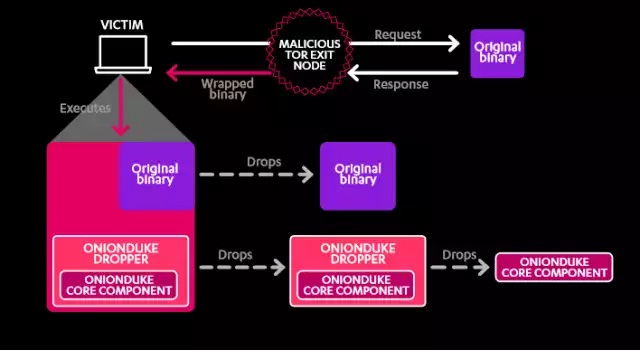
102MalwareSeven years of malware linked to Russian state-backed cyberespionage
F-Secure report details “The Dukes” malware family and its Russian connections. For the past seven years, a cyberespionage group operating out of...
-

 186Cyber Crime
186Cyber CrimeRussian hacker Responsible for Massive Data Breach Finally Pleads Guilty
The infamous Russian hacker, Vladimir Drinkman, has admitted his contribution in what has been regarded by the Justice Department as “the largest...
-

 296Geek
296GeekNATO Will Check for Backdoors in Microsoft’s Products
Microsoft has taken NATO onboard in its program which presents information about vulnerabilities and provides access to source code. A Security Agreement...
-

 314Data Security
314Data SecurityCisco Routers Vulnerable To Malware Attacks Via Backdoor Firmware Installation
It has always been believed that Cisco routers being used in the enterprise environment could be hacked via installation of backdoor firmware,...
-

 159Cyber Crime
159Cyber CrimeHackers Can Infect ATM With Malware To Hold Your Card
Security researchers over at FireEye have discovered a serious security flaw within the ATM (Automated Teller Machine) that could be exploited by...
-

 195Geek
195GeekNew Android Malware Changes PIN Code and Demand Ransom
Android users need to be highly careful while using your smartphone as ESET researchers have identified simplocker, a new screen-locking malware that...
-
 125Data Security
125Data SecuritySurvey Shows Most Americans are Fine with Backdoor in Their Devices
A recent survey from Vormetric revealed that people in the United States are OK with the addition of backdoors in their devices/software....
-

 207News
207NewsAndroid Users Beware: Verified Apps on Play Store can Spread MKero malware
If you think that all the Android apps currently available on the legitimate Google Play Store are reliable and free-of-malware, then you...
-
 117Data Security
117Data SecurityMusical Chairs Campaign Found Deploying New Gh0st RAT Variant
Researchers have peeled back the layers on a new campaign that spans multiple years and involves a new variant of the ubiquitous Gh0st remote...
-

 260Malware
260MalwareAndroid Malware Secretly Subscribes Victims to Premium SMS Services
The Android.Trojan.MKero.A malware is making a comeback in Androidland, and this time around, hackers found a method to bundle it with legitimate...
-

 209Geek
209GeekAndroid Ransomware Hidden Behind Fake Pornography App
Android is one of the most vulnerable OS in the world — If you are an Android user you need to be...
-

 212Data Security
212Data SecurityStudy Reveals Xiaomi, Huawei, Lenovo Phones Contain Malware By-default
A startling revelation made in GData study is that some of the Chinese smartphone units that are being shipped to Asia and...
-

 167Vulnerabilities
167VulnerabilitiesAttackers bundle an old version of TeamViewer to exploit vulnerability
We’re used to seeing malware that exploits unpatched vulnerabilities in software. But in a new twist attackers are bundling an old version...
-

 269Data Security
269Data Security24 Chinese Android Smartphones Models Come With Pre-Installed Malware
G DATA security experts published their latest research in which they’ve analyzed top Chinese Android smartphone models and found that a large...
-

 163Malware
163MalwareMatch.com suspends UK advertising after malware warning
Online daters risk being held to ransom in possible cyber attack on Match.com Match.com has suspended advertising on its UK site whilst...
-

 104Data Security
104Data SecurityNew Android Ransomware Communicates over XMPP
A new strain of Android ransomware disguised as a video player app uses a means of communication unseen in other similar malware....
-

 116Malware
116MalwareNew Versions of Carbanak Banking Malware Seen Hitting Targets in U.S. and Europe
New variants of the notorious Carbanak Trojan have surfaced in Europe and the United States, and researchers say that the malware now has...
-

 106Malware
106MalwareHidden password-stealing malware lurking in your GPU card? Intel Security thinks not
Fears that malware is hiding in people’s graphics chipsets may be overclocked, according to Intel Security. Earlier this year, researchers from the...
-
 184Data Security
184Data SecurityCoreBot Can Steal Your Credentials, Download and Execute Malware
CoreBot is a new malware that steals user credentials and have the ability to cause a great amount of trouble. This stealer...






