All posts tagged "malware"
-
 3.8KMalware
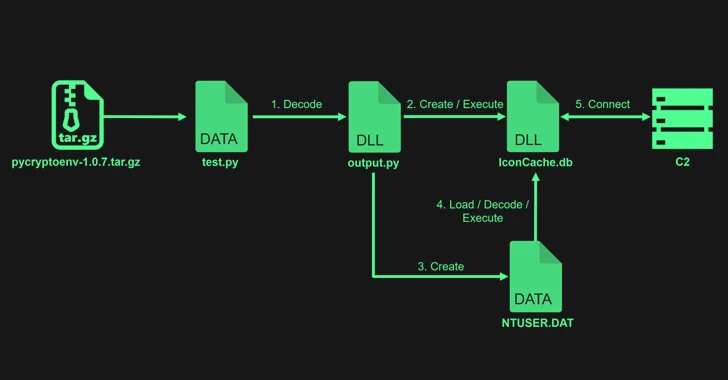
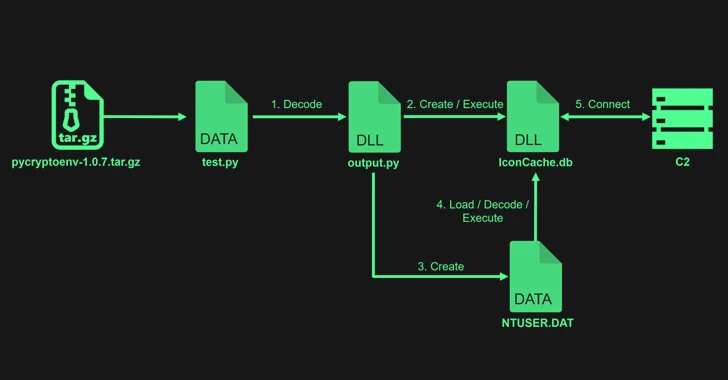
3.8KMalwareLazarus Exploits Typos to Sneak PyPI Malware into Dev Systems
The notorious North Korean state-backed hacking group Lazarus uploaded four packages to the Python Package Index (PyPI) repository with the goal of...
-

 2.3KVulnerabilities
2.3KVulnerabilitiesChinese Hackers Exploiting Ivanti VPN Flaws to Deploy New Malware
At least two different suspected China-linked cyber espionage clusters, tracked as UNC5325 and UNC3886, have been attributed to the exploitation of security...
-

 3.4KMalware
3.4KMalwareIran-Linked UNC1549 Hackers Target Middle East Aerospace & Defense Sectors
An Iran-nexus threat actor known as UNC1549 has been attributed with medium confidence to a new set of attacks targeting aerospace, aviation,...
-

 4.8KMalware
4.8KMalwareOpen-Source Xeno RAT Trojan Emerges as a Potent Threat on GitHub
An “intricately designed” remote access trojan (RAT) called Xeno RAT has been made available on GitHub, making it easily accessible to other...
-

 1.8KMalware
1.8KMalwareFrom Alert to Action: How to Speed Up Your SOC Investigations
Processing alerts quickly and efficiently is the cornerstone of a Security Operations Center (SOC) professional’s role. Threat intelligence platforms can significantly enhance...
-
 4.1KMalware
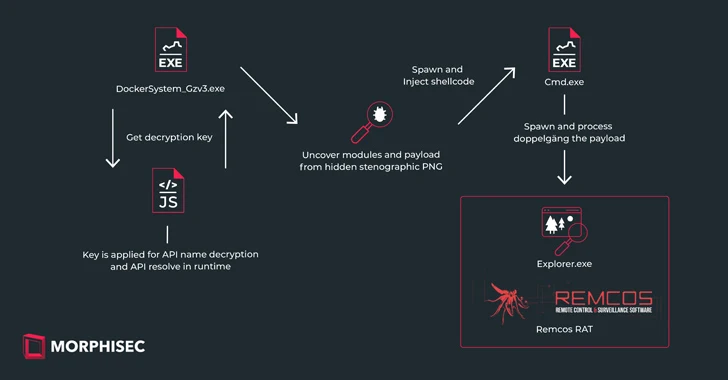
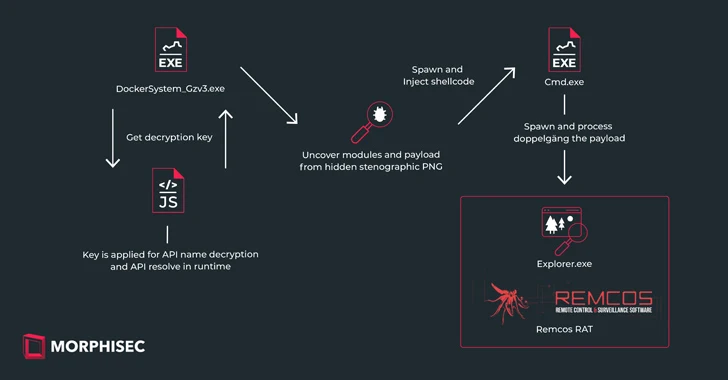
4.1KMalwareNew IDAT Loader Attacks Using Steganography to Deploy Remcos RAT
Ukrainian entities based in Finland have been targeted as part of a malicious campaign distributing a commercial remote access trojan known as...
-

 2.5KMalware
2.5KMalwareDormant PyPI Package Compromised to Spread Nova Sentinel Malware
A dormant package available on the Python Package Index (PyPI) repository was updated nearly after two years to propagate an information stealer...
-

 785Malware
785MalwareCybercriminals Weaponizing Open-Source SSH-Snake Tool for Network Attacks
A recently open-sourced network mapping tool called SSH-Snake has been repurposed by threat actors to conduct malicious activities. “SSH-Snake is a self-modifying...
-
 2.8KMalware
2.8KMalwareRussian Government Software Backdoored to Deploy Konni RAT Malware
An installer for a tool likely used by the Russian Consular Department of the Ministry of Foreign Affairs (MID) has been backdoored...
-
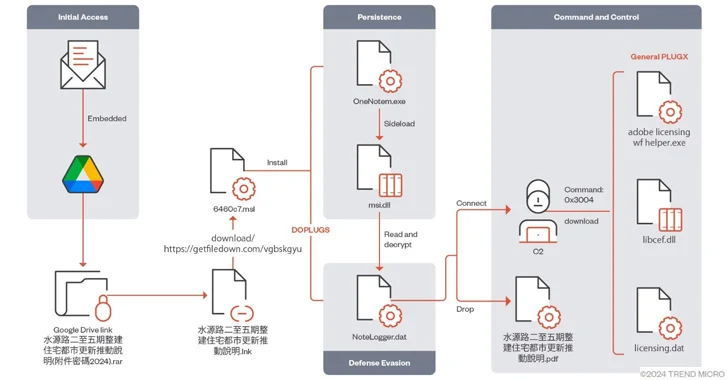
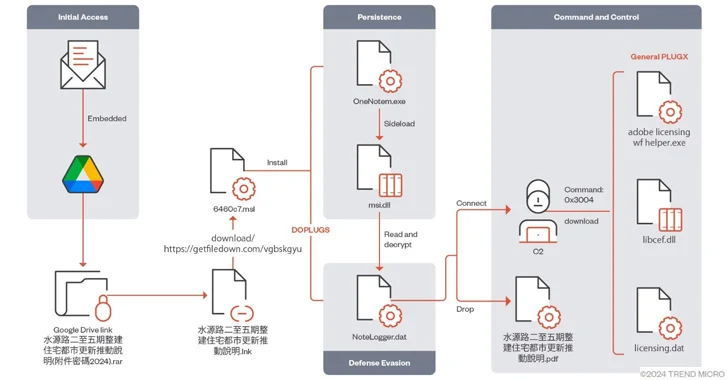 1.4KMalware
1.4KMalwareMustang Panda Targets Asia with Advanced PlugX Variant DOPLUGS
The China-linked threat actor known as Mustang Panda has targeted various Asian countries using a variant of the PlugX (aka Korplug) backdoor...
-
 4.8KMalware
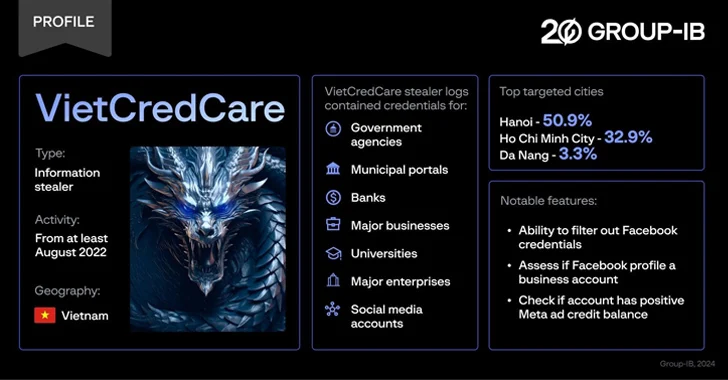
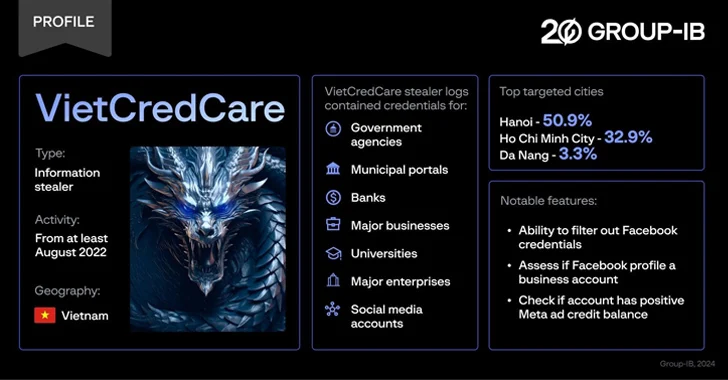
4.8KMalwareNew ‘VietCredCare’ Stealer Targeting Facebook Advertisers in Vietnam
Facebook advertisers in Vietnam are the target of a previously unknown information stealer dubbed VietCredCare at least since August 2022. The malware...
-

 3.8KMalware
3.8KMalwareNew Migo Malware Targeting Redis Servers for Cryptocurrency Mining
A novel malware campaign has been observed targeting Redis servers for initial access with the ultimate goal of mining cryptocurrency on compromised...
-

 4.5KMalware
4.5KMalwareMeta Warns of 8 Spyware Firms Targeting iOS, Android, and Windows Devices
Meta Platforms said it took a series of steps to curtail malicious activity from eight different firms based in Italy, Spain, and...
-

 4.0KMalware
4.0KMalwareFBI’s Most-Wanted Zeus and IcedID Malware Mastermind Pleads Guilty
A Ukrainian national has pleaded guilty in the U.S. to his role in two different malware schemes, Zeus and IcedID, between May...
-

 292Malware
292MalwareRussian Turla Hackers Target Polish NGOs with New TinyTurla-NG Backdoor
The Russia-linked threat actor known as Turla has been observed using a new backdoor called TinyTurla-NG as part of a three-month-long campaign...
-
 1.1KCyber Attack
1.1KCyber AttackMicrosoft, OpenAI Warn of Nation-State Hackers Weaponizing AI for Cyber Attacks
Nation-state actors associated with Russia, North Korea, Iran, and China are experimenting with artificial intelligence (AI) and large language models (LLMs) to...
-
 1.2KVulnerabilities
1.2KVulnerabilitiesUbuntu ‘command-not-found’ Tool Could Trick Users into Installing Rogue Packages
Cybersecurity researchers have found that it’s possible for threat actors to exploit a well-known utility called command-not-found to recommend their own rogue...
-

 587Malware
587MalwareBumblebee Malware Returns with New Tricks, Targeting U.S. Businesses
The infamous malware loader and initial access broker known as Bumblebee has resurfaced after a four-month absence as part of a new...
-

 2.2KMalware
2.2KMalwareDarkMe Malware Targets Traders Using Microsoft SmartScreen Zero-Day Vulnerability
A newly disclosed security flaw in the Microsoft Defender SmartScreen has been exploited as a zero-day by an advanced persistent threat actor...
-

 369Vulnerabilities
369VulnerabilitiesIvanti Vulnerability Exploited to Install ‘DSLog’ Backdoor on 670+ IT Infrastructures
Threat actors are leveraging a recently disclosed security flaw impacting Ivanti Connect Secure, Policy Secure, and ZTA gateways to deploy a backdoor...
-
 2.7KMalware
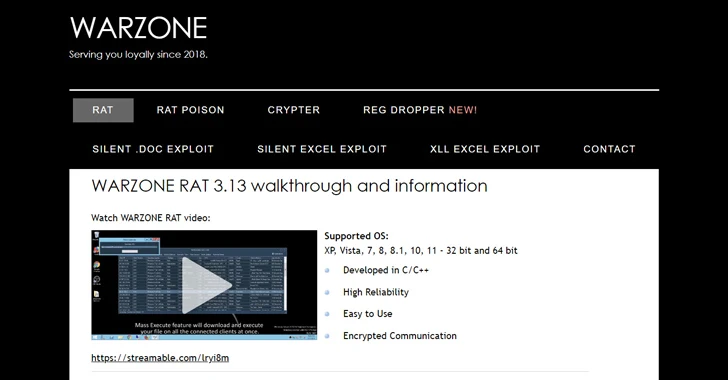
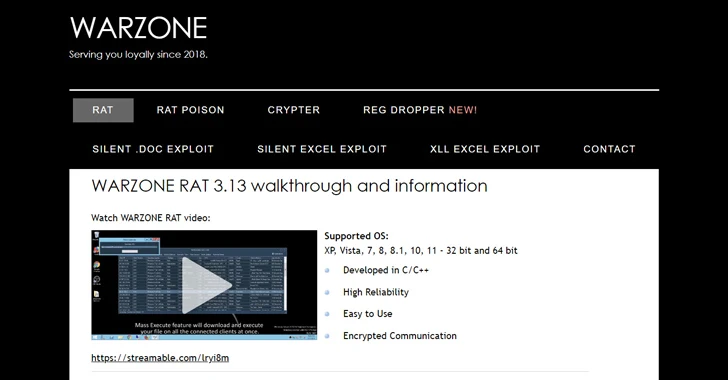
2.7KMalwareU.S. DoJ Dismantles Warzone RAT Infrastructure, Arrests Key Operators
The U.S. Justice Department (DoJ) on Friday announced the seizure of online infrastructure that was used to sell a remote access trojan...






