All posts tagged "malware"
-

 1.6KMalware
1.6KMalwareAlert: New Stealthy “RustDoor” Backdoor Targeting Apple macOS Devices
Apple macOS users are the target of a new Rust-based backdoor that has been operating under the radar since November 2023. The...
-

 4.9KMalware
4.9KMalwareRaspberry Robin Malware Upgrades with Discord Spread and New Exploits
The operators of Raspberry Robin are now using two new one-day exploits to achieve local privilege escalation, even as the malware continues...
-

 2.8KMalware
2.8KMalwareMoqHao Android Malware Evolves with Auto-Execution Capability
Threat hunters have identified a new variant of Android malware called MoqHao that automatically executes on infected devices without requiring any user...
-

 5.0KCyber Attack
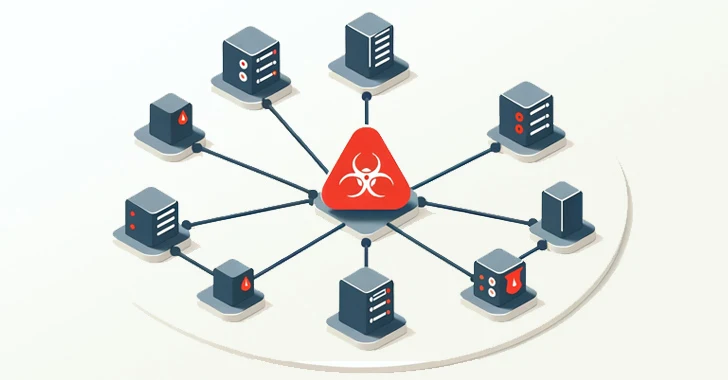
5.0KCyber AttackAfter FBI Takedown, KV-Botnet Operators Shift Tactics in Attempt to Bounce Back
The threat actors behind the KV-botnet made “behavioral changes” to the malicious network as U.S. law enforcement began issuing commands to neutralize...
-

 3.6KMalware
3.6KMalwareChinese Hackers Exploited FortiGate Flaw to Breach Dutch Military Network
Chinese state-backed hackers broke into a computer network that’s used by the Dutch armed forces by targeting Fortinet FortiGate devices. “This [computer...
-
 1.9KMalware
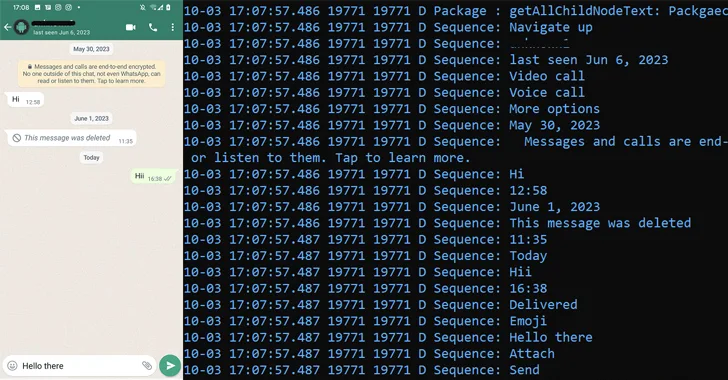
1.9KMalwarePatchwork Using Romance Scam Lures to Infect Android Devices with VajraSpy Malware
The threat actor known as Patchwork likely used romance scam lures to trap victims in Pakistan and India, and infect their Android...
-

 2.1KMalware
2.1KMalwarePegasus Spyware Targeted iPhones of Journalists and Activists in Jordan
The iPhones belonging to nearly three dozen journalists, activists, human rights lawyers, and civil society members in Jordan have been targeted with...
-

 1.5KMalware
1.5KMalwareNew Mispadu Banking Trojan Exploiting Windows SmartScreen Flaw
The threat actors behind the Mispadu banking Trojan have become the latest to exploit a now-patched Windows SmartScreen security bypass flaw to...
-

 2.6KMalware
2.6KMalwareDirtyMoe Malware Infects 2,000+ Ukrainian Computers for DDoS and Cryptojacking
The Computer Emergency Response Team of Ukraine (CERT-UA) has warned that more than 2,000 computers in the country have been infected by...
-

 1.9KMalware
1.9KMalwareCloudzy Elevates Cybersecurity: Integrating Insights from Recorded Future to Revolutionize Cloud Security
Cloudzy, a prominent cloud infrastructure provider, proudly announces a significant enhancement in its cybersecurity landscape. This breakthrough has been achieved through a...
-

 3.6KMalware
3.6KMalwareHeadCrab 2.0 Goes Fileless, Targeting Redis Servers for Crypto Mining
Cybersecurity researchers have detailed an updated version of the malware HeadCrab that’s known to target Redis database servers across the world since...
-
 1.9KMalware
1.9KMalwareWarning: New Malware Emerges in Attacks Exploiting Ivanti VPN Vulnerabilities
Google-owned Mandiant said it identified new malware employed by a China-nexus espionage threat actor known as UNC5221 and other threat groups during...
-
 3.7KMalware
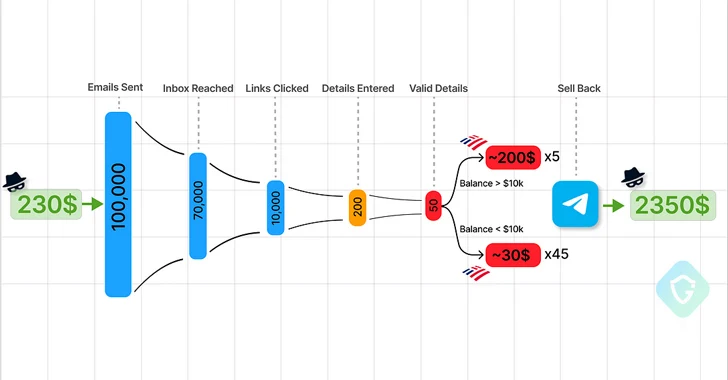
3.7KMalwareTelegram Marketplaces Fuel Phishing Attacks with Easy-to-Use Kits and Malware
Cybersecurity researchers are calling attention to the “democratization” of the phishing ecosystem owing to the emergence of Telegram as an epicenter for...
-

 3.7KVulnerabilities
3.7KVulnerabilitiesHackers Exploiting Ivanti VPN Flaws to Deploy KrustyLoader Malware
A pair of recently disclosed zero-day flaws in Ivanti Connect Secure (ICS) virtual private network (VPN) devices have been exploited to deliver...
-
 585Malware
585MalwareChina-Linked Hackers Target Myanmar’s Top Ministries with Backdoor Blitz
The China-based threat actor known as Mustang Panda is suspected to have targeted Myanmar’s Ministry of Defence and Foreign Affairs as part...
-

 3.3KMalware
3.3KMalwareNew ZLoader Malware Variant Surfaces with 64-bit Windows Compatibility
Threat hunters have identified a new campaign that delivers the ZLoader malware, resurfacing nearly two years after the botnet’s infrastructure was dismantled...
-

 3.7KVulnerabilities
3.7KVulnerabilitiesAlbabat, Kasseika, Kuiper: New Ransomware Gangs Rise with Rust and Golang
Cybersecurity researchers have detected in the wild yet another variant of the Phobos ransomware family known as Faust. Fortinet FortiGuard Labs, which...
-

 743Malware
743MalwareMalicious Ads on Google Target Chinese Users with Fake Messaging Apps
Chinese-speaking users have been targeted by malicious Google ads for restricted messaging apps like Telegram as part of an ongoing malvertising campaign....
-

 4.3KVulnerabilities
4.3KVulnerabilitiesSystemBC Malware’s C2 Server Analysis Exposes Payload Delivery Tricks
Cybersecurity researchers have shed light on the command-and-control (C2) server workings of a known malware family called SystemBC. “SystemBC can be purchased...
-
 788Malware
788MalwareChina-backed Hackers Hijack Software Updates to Implant “NSPX30” Spyware
A previously undocumented China-aligned threat actor has been linked to a set of adversary-in-the-middle (AitM) attacks that hijack update requests from legitimate...
-

 2.9KMalware
2.9KMalwareKasseika Ransomware Using BYOVD Trick to Disarm Security Pre-Encryption
The ransomware group known as Kasseika has become the latest to leverage the Bring Your Own Vulnerable Driver (BYOVD) attack to disarm...






