All posts tagged "Cyber-Attack"
-
 4.3KCyber Events
4.3KCyber EventsIranian Gas Stations Crippled After Suffering Cyberattack
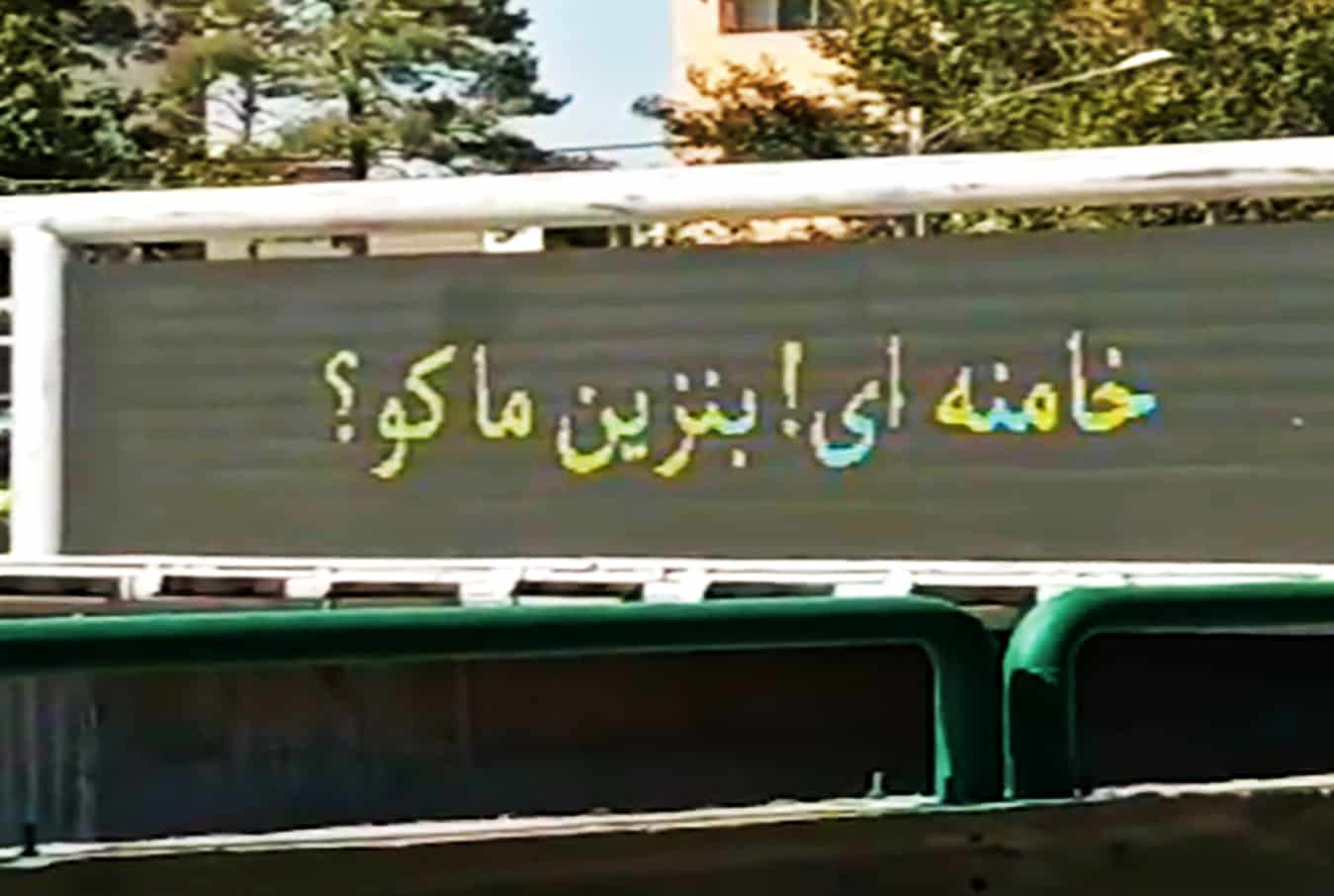
Soon after the cyberattack, videos and posts started surfacing on social media displaying messages that read: “Khamenei! Where is our gas?” Another...
-
 3.4KCyber Attack
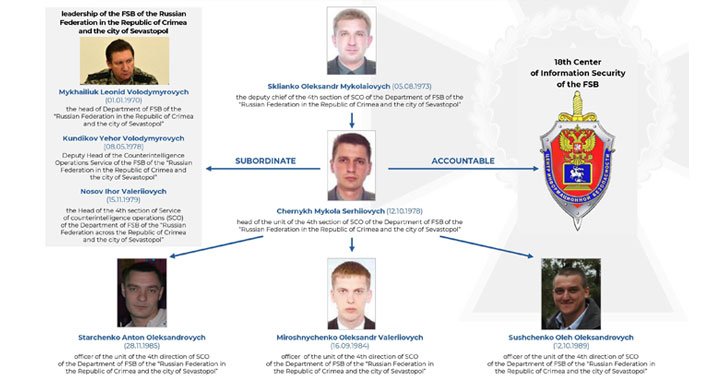
3.4KCyber AttackUkraine Identifies Russian FSB Officers Hacking As Gamaredon Group
Ukraine’s premier law enforcement and counterintelligence agency on Thursday disclosed the real identities of five individuals allegedly involved in digital intrusions attributed...
-

 3.3KCyber Attack
3.3KCyber AttackU.S. Federal Agencies Ordered to Patch Hundreds of Actively Exploited Flaws
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has published a catalog of vulnerabilities, including from Apple, Cisco, Microsoft, and Google, that...
-

 4.1KMalware
4.1KMalwareU.S. Offers $10 Million Reward for Information on DarkSide Ransomware Group
The U.S. government on Thursday announced a $10 million reward for information that may lead to the identification or location of key...
-

 3.6KMalware
3.6KMalwareUS Sanctions Pegasus-maker NSO Group and 3 Others For Selling Spyware
The U.S. Commerce Department on Wednesday added four companies, including Israel-based spyware companies NSO Group and Candiru, to a list of entities...
-
 4.2KCyber Attack
4.2KCyber AttackResearchers Uncover ‘Pink’ Botnet Malware That Infected Over 1.6 Million Devices
Cybersecurity researchers disclosed details of what they say is the “largest botnet” observed in the wild in the last six years, infecting...
-
 2.3KMalware
2.3KMalwareRussian TrickBot Gang Hacker Extradited to U.S. Charged with Cybercrime
A Russian national, who was arrested in South Korea last month and extradited to the U.S. on October 20, appeared in a...
-
 1.2KData Security
1.2KData SecurityCloud security is an ongoing struggle to keep sensitive data safe. Is it getting any easier?
The latest cloud security breaches show that we have miles to go as we keep fighting to keep our sensitive data safe. ...
-

 2.9KData Security
2.9KData SecuritySolarWinds hackers, Nobelium, hit cloud providers and resellers
So far, Microsoft has informed 140 companies about the new attack campaign being carried out by Nobelium 14 of which were compromised...
-

 574Cyber Attack
574Cyber AttackCyber Attack in Iran Reportedly Cripples Gas Stations Across the Country
A cyber attack in Iran left petrol stations across the country crippled, disrupting fuel sales and defacing electronic billboards to display messages...
-

 4.9KMalware
4.9KMalwareLatest Report Uncovers Supply Chain Attacks by North Korean Hackers
Lazarus Group, the advanced persistent threat (APT) group attributed to the North Korean government, has been observed waging two separate supply chain...
-
 994Cyber Attack
994Cyber AttackHackers Exploited Popular BillQuick Billing Software to Deploy Ransomware
Cybersecurity researchers on Friday disclosed a now-patched critical vulnerability in multiple versions of a time and billing system called BillQuick that’s being...
-

 3.8KMalware
3.8KMalware‘Lone Wolf’ Hacker Group Targeting Afghanistan and India with Commodity RATs
A new malware campaign targeting Afghanistan and India is exploiting a now-patched, 20-year-old flaw affecting Microsoft Office to deploy an array of...
-

 703Cyber Crime
703Cyber CrimeDDoS booter customers received warning letters by Dutch police
Apparently, the individuals who received the warning were identified as suspects and will be prosecuted for a cyber offense if they continue...
-

 4.8KCyber Crime
4.8KCyber CrimeHow using the purple team approach helps in addressing cybercrime
Automated purple teaming is one of the best ways to address cybercrime as it does not only test for the deficiencies in...
-

 2.7KCyber Attack
2.7KCyber AttackTwo Eastern Europeans Sentenced for Providing Bulletproof Hosting to Cyber Criminals
Two Eastern European nationals have been sentenced in the U.S. for offering “bulletproof hosting” services to cybercriminals, who used the technical infrastructure...
-

 1.5KCyber Attack
1.5KCyber AttackLightBasin Hackers Breach at Least 13 Telecom Service Providers Since 2019
A highly sophisticated adversary named LightBasin has been identified as behind a string of attacks targeting the telecom sector with the goal...
-
 5.0KData Security
5.0KData SecurityIran-linked hackers hit Israeli, US and EU defense tech firm
Microsoft has warned that hackers linked to Iran are mainly targeting Office 365 clients in defense technology firms. Researchers at Microsoft Threat...
-

 3.4KData Security
3.4KData SecurityWhy Businesses Need To Go Lean With Cybersecurity
As hackers get smarter than ever, cybersecurity becomes a key concern for businesses. Attackers have ways to break into even the most...
-

 2.5KCyber Events
2.5KCyber EventsMicrosoft Azure customer hit by 2.4 Tbps DDoS attack
Microsoft has confirmed to mitigate a massive DDoS attack originated from a botnet comprising 70,000 compromised IoT devices. Microsoft reported that an...
-
Cyber Attack
Google: We’re Tracking 270 State-Sponsored Hacker Groups From Over 50 Countries
Google’s Threat Analysis Group (TAG) on Thursday said it’s tracking more than 270 government-backed threat actors from more than 50 countries, adding...






