All posts tagged "Cyber-Attack"
-
 603Cyber Attack
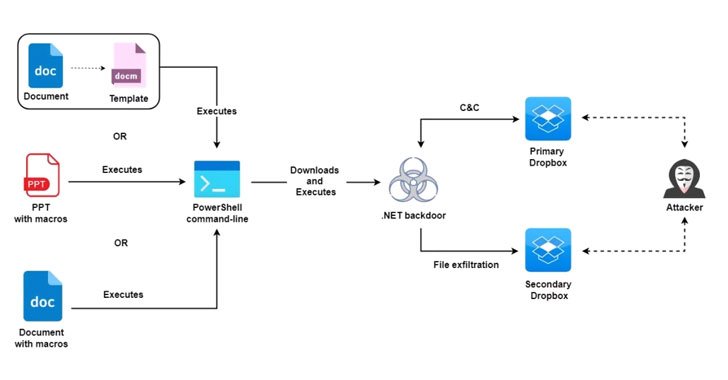
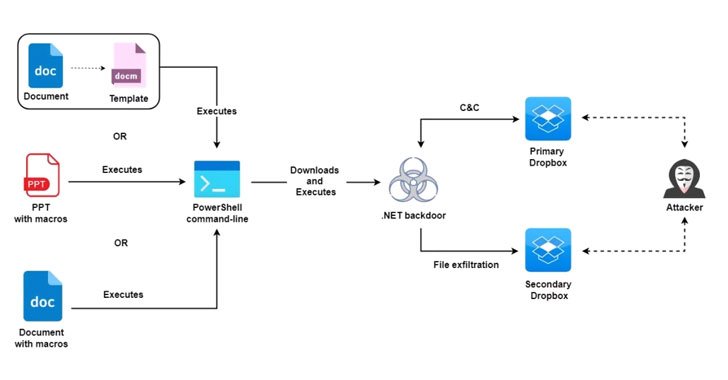
603Cyber AttackMolerats Hackers Hiding New Espionage Attacks Behind Public Cloud Infrastructure
An active espionage campaign has been attributed to the threat actor known as Molerats that abuses legitimate cloud services like Google Drive...
-

 4.4KMalware
4.4KMalwarePrometheus Hacker Group Uses Traffic Direction System to Deliver Malware Binaries to Targets
The TDS (Traffic Direction System) of the Prometheus hacker group has been analyzed recently by the cybersecurity researcher of BlackBerry. During their...
-

 3.2KCyber Attack
3.2KCyber AttackInterpol Busted 11 Members of Nigerian BEC Cybercrime Gang
A coordinated law enforcement operation has resulted in the arrest of 11 members allegedly belonging to a Nigerian cybercrime gang notorious for...
-
 3.1KCyber Attack
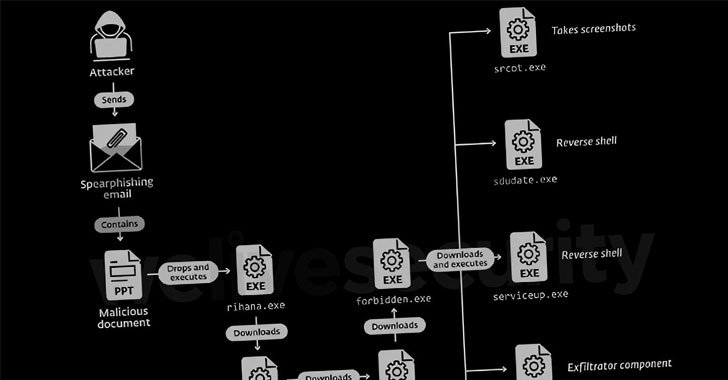
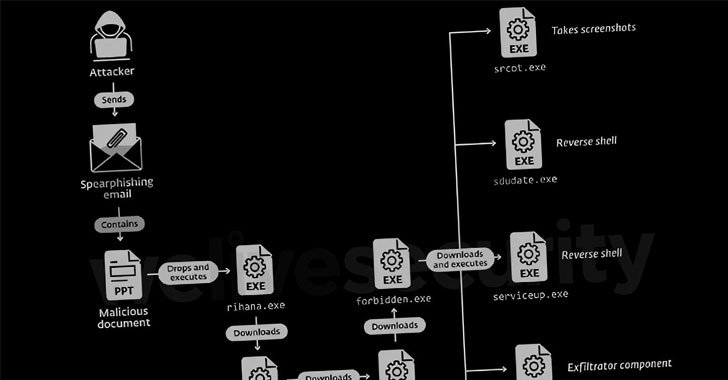
3.1KCyber AttackDoNot Hacking Team Targeting Government and Military Entities in South Asia
A threat actor with potential links to an Indian cybersecurity company has been nothing if remarkably persistent in its attacks against military...
-
 3.2KCyber Attack
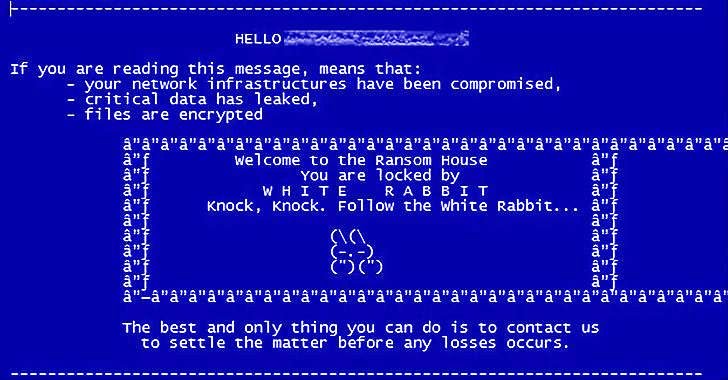
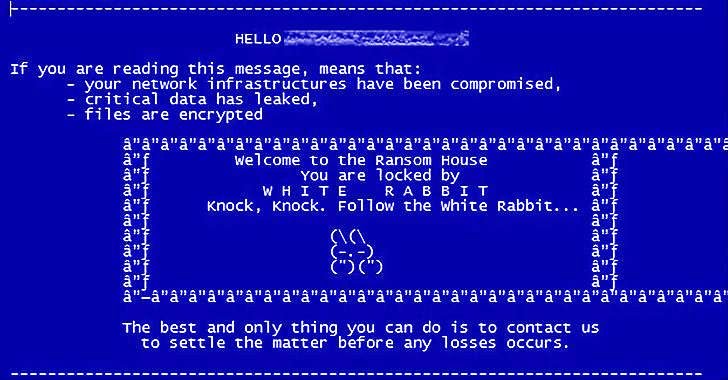
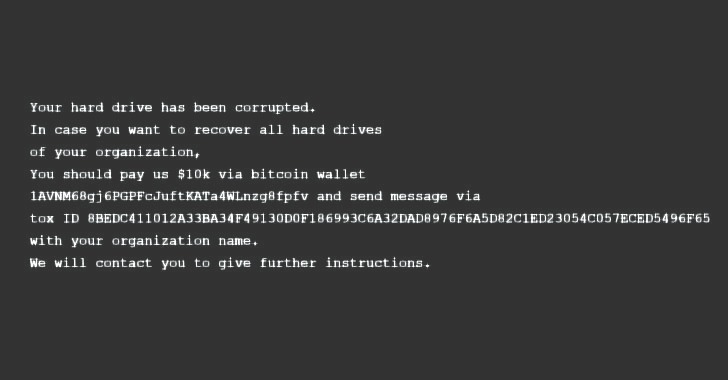
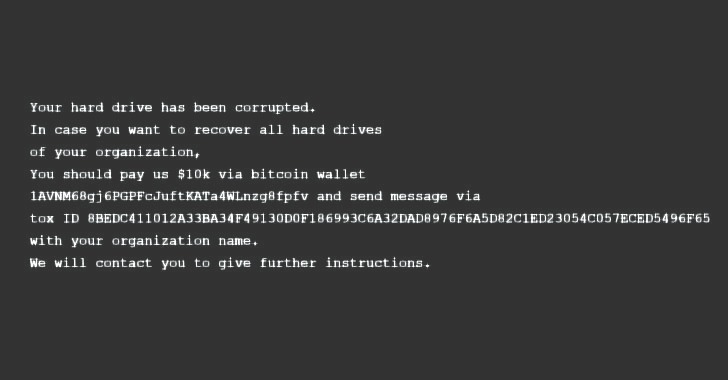
3.2KCyber AttackFIN8 Hackers Spotted Using New ‘White Rabbit’ Ransomware in Recent Attacks
The financially motivated FIN8 actor, in all likelihood, has resurfaced with a never-before-seen ransomware strain called “White Rabbit” that was recently deployed...
-

 1.3KCyber Attack
1.3KCyber AttackUkraine: Recent Cyber Attacks Part of Wider Plot to Sabotage Critical Infrastructure
The coordinated cyberattacks targeting Ukrainian government websites and the deployment of a data-wiper malware called WhisperGate on select government systems are part...
-

 4.8KCyber Attack
4.8KCyber AttackUkrainian Government Officially Accuses Russia of Recent Cyberattacks
The government of Ukraine on Sunday formally accused Russia of masterminding the attacks that targeted websites of public institutions and government agencies...
-
 2.4KMalware
2.4KMalwareA New Destructive Malware Targeting Ukrainian Government and Business Entities
Cybersecurity teams from Microsoft on Saturday disclosed they identified evidence of a new destructive malware operation targeting government, non-profit, and information technology...
-

 4.9KMalware
4.9KMalwareNorth Korean Hackers Stole Millions from Cryptocurrency Startups Worldwide
Operators associated with the Lazarus sub-group BlueNoroff have been linked to a series of cyberattacks targeting small and medium-sized companies worldwide with...
-
 2.1KMalware
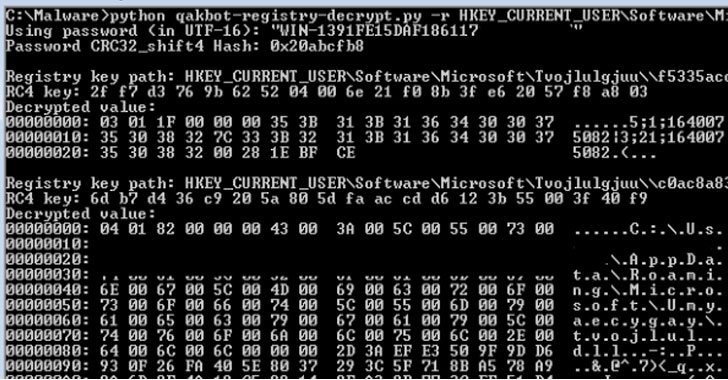
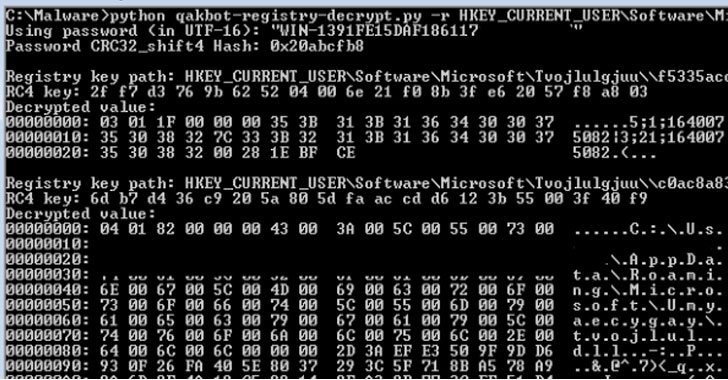
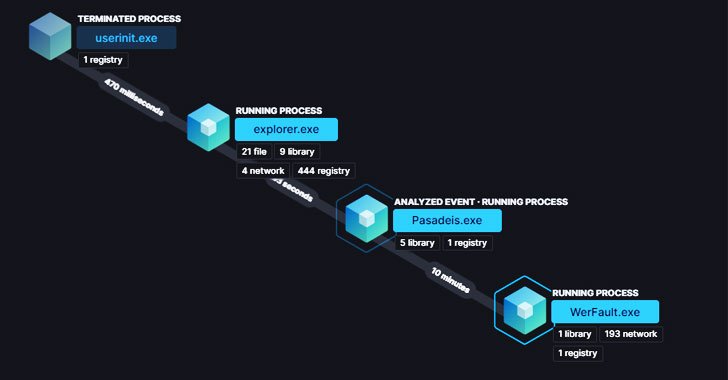
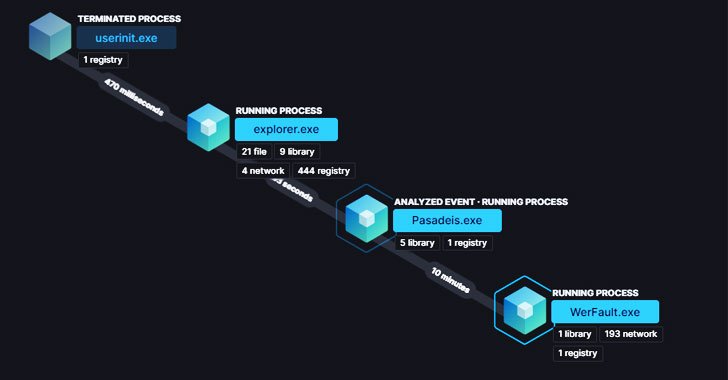
2.1KMalwareResearchers Decrypted Qakbot Banking Trojan’s Encrypted Registry Keys
Cybersecurity researchers have decoded the mechanism by which the versatile Qakbot banking trojan handles the insertion of encrypted configuration data into the...
-
 1.5KCyber Attack
1.5KCyber AttackUS Cyber Command Links ‘MuddyWater’ Hacking Group to Iranian Intelligence
The U.S. Cyber Command (USCYBERCOM) on Wednesday officially confirmed MuddyWater’s ties to the Iranian intelligence apparatus, while simultaneously detailing the various tools...
-
 1.2KCyber Attack
1.2KCyber AttackFBI, NSA and CISA Warns of Russian Hackers Targeting Critical Infrastructure
Amid renewed tensions between the U.S. and Russia over Ukraine and Kazakhstan, American cybersecurity and intelligence agencies on Tuesday released a joint...
-

 4.8KRansomware
4.8KRansomwareHow To Prevent Ransomware Attacks More Successfully?
Ransomware is one of the most common cyber threats that attack both companies and private users. It works by encrypting your files,...
-

 4.1KCyber Attack
4.1KCyber AttackMicrosoft Warns of Continued Attacks Exploiting Apache Log4j Vulnerabilities
Microsoft is warning of continuing attempts by nation-state adversaries and commodity attackers to take advantage of security vulnerabilities uncovered in the Log4j...
-

 4.2KCyber Attack
4.2KCyber AttackChinese APT Hackers Used Log4Shell Exploit to Target Academic Institution
A never-before-seen China-based targeted intrusion adversary dubbed Aquatic Panda has been observed leveraging critical flaws in the Apache Log4j logging library as...
-
 1.5KCyber Attack
1.5KCyber AttackNew BLISTER Malware Using Code Signing Certificates to Evade Detection
Cybersecurity researchers have disclosed details of an evasive malware campaign that makes use of valid code signing certificates to sneak past security...
-

 4.3KData Security
4.3KData Security4 Ways Cybercriminals Exploit Remote Teams
Working from home (WFH) is not a piece of cake especially when cybercriminals exploited every possible vulnerability to break into your workstation....
-

 3.9KCyber Events
3.9KCyber EventsTop workforce management firm Kronos hit by ransomware attack
Kronos has taken down its private cloud services and advises customers to use “alternative business continuity protocols” while the company is working...
-

 4.0KCyber Attack
4.0KCyber AttackCISA Compliance for 2022
The last several years have seen an ever-increasing number of cyber-attacks, and while the frequency of such attacks has increased, so too...
-
 1.9KMalware
1.9KMalwareExperts Discover Backdoor Deployed on the U.S. Federal Agency’s Network
A U.S. federal government commission associated with international rights has been targeted by a backdoor that reportedly compromised its internal network in...
-

 3.1KCyber Crime
3.1KCyber CrimeCanadian Citizen Charged for Ransomware Attacks in Alaska
The accused became a suspect when the FBI contacted Canadian intelligence after observing a surge in ransomware attacks in Alaska in 2018....






