All posts tagged "Cyber Crime"
-

 117Cyber Crime
117Cyber CrimeFBI Randomly Used Malware on TORMail Users While Busting Pedophiles
Report Hints on Possible Invading of TORMail users Privacy for Capturing Global Child Porn Gang by the FBI In 2013, the Federal...
-

 161Geek
161Geek“New Facebook Message” Email Not Only Drops Malware But Phish You
If you receive an email claiming to have a ”new message” from Facebook just delete it because the attachment contains Nivdort malware...
-
 107News
107NewsCryptsy Hacked: Bitcoin Worth $USD 6 Million Stolen
The hacker inserted a Trojan malware into Cryptsy’s code so that he could access precious information and transfer cyber currencies. Paul Vernon, also...
-

 350Hacked
350Hacked26-year-old Hacker Sent To Jail For 334 Years, Highest Ever For A Cybercriminal
Short Bytes: A young Turkish hacker namedOnur Kopçak was sentenced to 334 years in prison. The cyber criminal was convicted for credit...
-

 336News
336NewsFBI Hacked Tor To Hunt Down Paedophiles On The Deep Web
FBI has taken down a site involved in Child pornography through some hacking techniques that have never been used in the history...
-

 300Cyber Crime
300Cyber CrimeBTCC Bitcoin Trader Confronts DDoS Attackers Like A Pro
Bitcoin-for-DDoS extortion scheme has a new victim and its none other than the BTCC — However, the hacker was unfortunate this time...
-

 140Data Security
140Data SecurityProxyBack Malware Converts Your PC Into Proxy
Palo Alto Networks researchers have identified a unique malware that infects home PCs and transforms them into internet proxies using HTTP tunnel....
-
 431News
431NewsTop 15 Cyber Attacks and Security Breaches in 2015
With 2016, just a few days away, let’s have a flashback of the top 15 security incidents that took place this year....
-

 346Cyber Crime
346Cyber CrimePolice Dogs Trained To Sniff Out Hard Drives Coming For Pedophiles
After using malware on pedophiles, law enforcement authorities in the United States have decided to add Hard-Drive Sniffing Dogs in their units...
-

 197Cyber Events
197Cyber EventsHackers Shutdown EA and Steam Servers Because It’s Christmas
Last week HR reported about a hacking group “Phantom Squad” that is planning ruin holidays for the gamers. It looks like the...
-

 313Cyber Crime
313Cyber CrimeLearn How to Identify, Protect Yourself from Phishing Scams
Each day we hear about new phishing attacks being carried out by hackers or scammers and despite the continuing awareness from multiple...
-

 263Data Security
263Data SecurityGhostware and Two-Faced Malware Coming in 2016
Summary: Malware is increasingly sophisticated. In 2016, look for two developing malware families. First, as law enforcement becomes more specialized in identifying...
-

 318Cyber Crime
318Cyber CrimeHackers Vow To ShutDown PlayStation, XboxLive This Christmas
Last New Years Eve, a hacking group “Lizard Squad” spoiled the party for gamers with a DDoS attack on the Play Station...
-

 281Geek
281GeekBible and Quran Apps Infected with Malware Capable of Spying
There are a hundred types of malware hidden inside the Bible and Quran apps, most of which are available all over the...
-

 277Surveillance
277SurveillanceUK May Approve Bill Allowing Spying on Individuals via Their Kids Toys
British government’s new investigatory bill (pdf) has a proposal on making it legal to hack smart toys in order to allow investigators to...
-
 111Cyber Crime
111Cyber CrimeAttacker Embeds Malware in The Guardian’s Cybercrime Article
An article published by The Guardian in 2011 on the topic Cybercrime: is it out of control? received a nasty response from a...
-

 142Cyber Crime
142Cyber CrimeMassive DDoS Attack Leaves UK Universities Without Internet
Some unknown cyber criminals have attacked a publicly funded network “Janet” which was used by many universities throughout the United Kingdom. On...
-

 136News
136NewsTuneCore Record Label Hacked, Musicians’ Data At Risk
TuneCore, an online music distribution/record label service on Friday, revealed that its database was breached by the hackers and they have been...
-

 348Data Security
348Data SecurityFallout 4 Pirated Copy Leads To Bitcoin Theft
People who download stuff from torrents and other cracked software providing websites have a very bad news because a user recently downloaded...
-
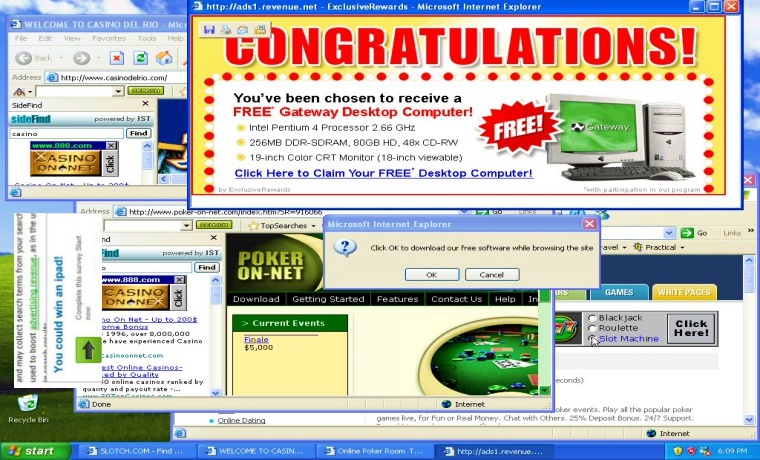
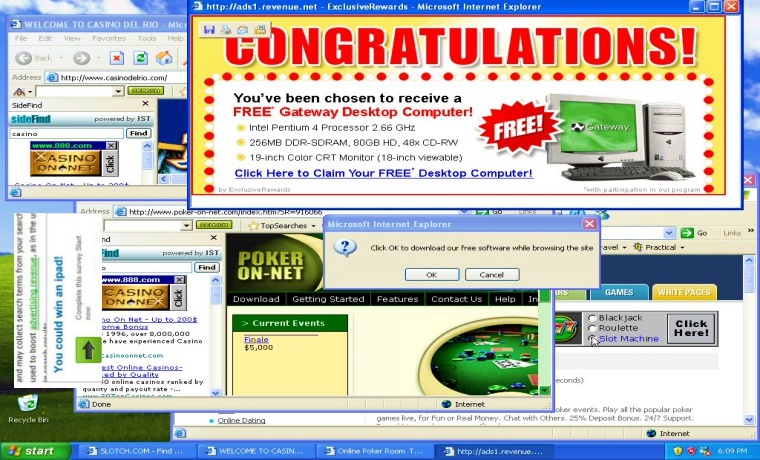 210Data Security
210Data SecurityUnwanted Browser Ads, A Sign Your PC is Infected with Malware
If your browser displays unwanted and wrongly placed ads such as an adult website ad on a website for kids or showing...
-

 234News
234NewsCanadian Police Vow to Hunt Cyber Criminals and Anonymous
Will Canada’s new Cybercrime division Curb Cybercrimes and capture Anonymous? Since the approval of Canadian Anti-Terror Bill C-51, online privacy is in...






