All posts tagged "Cyber Security"
-

 282Malware
282MalwareFancy Bear APT Hackers Owned Zebrocy Malware Opens Backdoor on Victims Machine to Control it Remotely
Cybercriminals from Sednit group, also known as Fancy Bear, APT28, Sofacy launching new Zebrocy Malware that indented to open backdoor on the...
-
 257Cyber Events
257Cyber EventsWhy So Many Businesses Can Never Recover After Cyber Attacks
A cyber attack can cripple critical infrastructure and businesses and generate negative press. In other cases, it could open you and your...
-
 464Malware
464Malware8 Common Hacking Techniques & 3 Ways to Avoid Them All
Hackers come in many forms with sophisticated Hacking Techniques, While there has been a lot of discussion about online security in recent...
-

 202Data Breach
202Data BreachHackers Breach Stack Overflow Q&A Site, Some Users’ Data Exposed
Note: We have updated this story to reflect new information after Stack Overflow changed its original announcement and shared more details on...
-

 232Malware
232MalwareWhat is Deception Technology and why Virtual Reality will be the Ultimate Weapon against Cyberattacks
Development with technologies such as Deception Technology has become either a boon for cyber professionals or hackers, and this can go either...
-

 3.0KPrivacy
3.0KPrivacyBusiness Intelligence is the Key to Stronger Cybersecurity – Here’s Why
Cybersecurity has been moving further and further towards the top of the corporate agenda for a number of years now, and for...
-

 231News
231NewsThis Hacker Is Selling Dangerous Windows 0-Day Hacks For Past 3 Years
A report by ZDNet has revealed that a mysterious hacker is selling Windows zero-day exploits to the world’s most notorious cybercrime groups...
-

 331Data Breach
331Data BreachTop Reasons Let Hackers Compromise the Healthcare Industry that Leads to Data Breaches
In recent times we have seen a numerous number of cyber attacks targeting the healthcare firm. For example the case of Oklahoma...
-

 365Data Security
365Data Security5 Cybersecurity Best Practices You Should Be Following Right Now
If you have a business and you don’t have an online presence, you’re handicapping yourself. That’s just how it is today. Without harnessing...
-

 243Data Security
243Data SecurityHow to Respond to a Cyber Attack on Your Business
Cyber security affects businesses of all sizes, and in every industry. Today it is a board-level agenda item, which has been placed...
-
 265Data Breach
265Data BreachDocker Hub Suffers a Data Breach, Asks Users to Reset Password
Docker Hub, one of the largest cloud-based library of Docker container images, has suffered a data breach after an unknown attacker gained...
-

 367Data Breach
367Data BreachNew York, Canada, Ireland Launch New Investigations Into Facebook Privacy Breaches
Facebook has a lot of problems, then there are a lot of problems for Facebook—and both are not going to end anytime...
-

 291Data Breach
291Data BreachOver 100 Million JustDial Users’ Personal Data Found Exposed On the Internet
An unprotected database belonging to JustDial, India’s largest local search service, is leaking personally identifiable information of its every customer in real-time...
-

 199Data Security
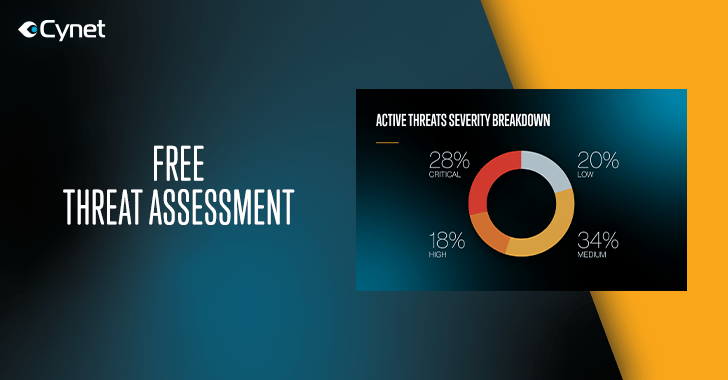
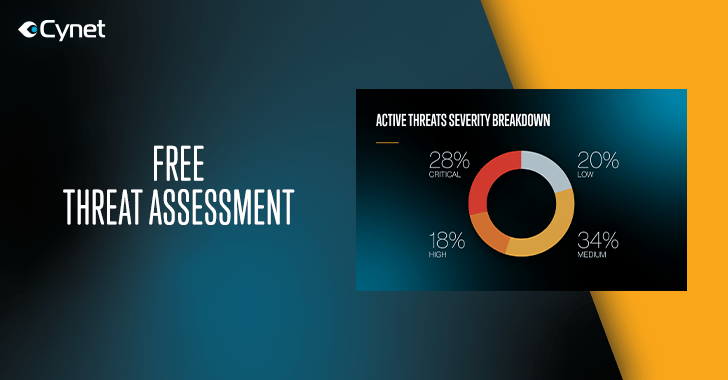
199Data SecurityCynet is Launching a Free Threat Assessment for Businesses
In the age of regular cyber attacks and constant digital threats, it’s no wonder that businesses find themselves spending more and more...
-
 289Infosec
289InfosecCynet Offers a Free Threat Assessment for Mid-Sized and Large Organizations – Take a Free Ride Now
Visibility into an environment attack surface is the fundamental cornerstone to sound security decision making. However, the standard process of 3rd party...
-

 381News
381NewsTesla autopilot feature hacked to risk oncoming traffic
Tesla’s High-End Vehicle’s Lane Recognition System not Free from Technical Glitches- Keen Labs Claims in New Research. Cybersecurity firm Keen Labs published...
-
 195Infosec
195InfosecAI Can Help You Sleep Better But What about Security Concerns?
Have you ever wondered where that mid-afternoon crash comes from? Most of us experience it, and it makes for a miserable day...
-

 298News
298NewsFirefox, Edge, Safari, Tesla & VMware pwned at Pwn2Own
Pwn2Own 2019 has yet again proved that a secure system is nothing else but a myth. In its two days running, the...
-
 336Articles
336ArticlesGoogle Will Prompt European Android Users to Select Preferred Default Browser
Google announced some major changes for its Android mobile operating system in October after the European Commission hit the company with a...
-

 276Articles
276ArticlesNew MageCart Attacks Target Bedding Retailers My Pillow and Amerisleep
Cybersecurity researchers today disclosed details of two newly identified Magecart attacks targeting online shoppers of bedding retailers MyPillow and Amerisleep. Magecart is...
-

 317Articles
317ArticlesPuTTY Releases Important Software Update to Patch 8 High-Severity Flaws
The popular SSH client program PuTTY has released the latest version of its software that includes security patches for 8 high-severity security...






