All posts tagged "cybersecurity"
-

 3.6KMalware
3.6KMalwareHeadCrab 2.0 Goes Fileless, Targeting Redis Servers for Crypto Mining
Cybersecurity researchers have detailed an updated version of the malware HeadCrab that’s known to target Redis database servers across the world since...
-
 2.0KMalware
2.0KMalwareWarning: New Malware Emerges in Attacks Exploiting Ivanti VPN Vulnerabilities
Google-owned Mandiant said it identified new malware employed by a China-nexus espionage threat actor known as UNC5221 and other threat groups during...
-
 3.7KMalware
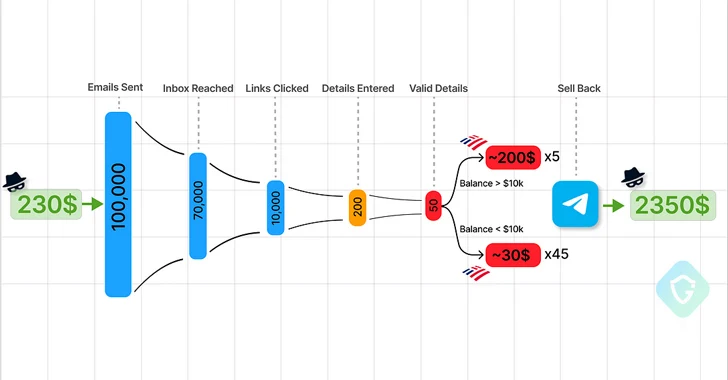
3.7KMalwareTelegram Marketplaces Fuel Phishing Attacks with Easy-to-Use Kits and Malware
Cybersecurity researchers are calling attention to the “democratization” of the phishing ecosystem owing to the emergence of Telegram as an epicenter for...
-

 2.4KData Breach
2.4KData BreachThe SEC Won’t Let CISOs Be: Understanding New SaaS Cybersecurity Rules
The SEC isn’t giving SaaS a free pass. Applicable public companies, known as “registrants,” are now subject to cyber incident disclosure and...
-

 3.9KVulnerabilities
3.9KVulnerabilitiesURGENT: Upgrade GitLab – Critical Workspace Creation Flaw Allows File Overwrite
GitLab once again released fixes to address a critical security flaw in its Community Edition (CE) and Enterprise Edition (EE) that could...
-
 598Malware
598MalwareChina-Linked Hackers Target Myanmar’s Top Ministries with Backdoor Blitz
The China-based threat actor known as Mustang Panda is suspected to have targeted Myanmar’s Ministry of Defence and Foreign Affairs as part...
-

 554Data Breach
554Data BreachTop Security Posture Vulnerabilities Revealed
Each New Year introduces a new set of challenges and opportunities for strengthening our cybersecurity posture. It’s the nature of the field...
-
 836Vulnerabilities
836VulnerabilitiesJuniper Networks Releases Urgent Junos OS Updates for High-Severity Flaws
Juniper Networks has released out-of-band updates to address high-severity flaws in SRX Series and EX Series that could be exploited by a...
-

 2.3KMalware
2.3KMalwareRiding the AI Waves: The Rise of Artificial Intelligence to Combat Cyber Threats
In nearly every segment of our lives, AI (artificial intelligence) now makes a significant impact: It can deliver better healthcare diagnoses and...
-

 4.6KMalware
4.6KMalwareMalicious PyPI Packages Slip WhiteSnake InfoStealer Malware onto Windows Machines
Cybersecurity researchers have identified malicious packages on the open-source Python Package Index (PyPI) repository that deliver an information stealing malware called WhiteSnake...
-

 3.0KVulnerabilities
3.0KVulnerabilitiesAllaKore RAT Malware Targeting Mexican Firms with Financial Fraud Tricks
Mexican financial institutions are under the radar of a new spear-phishing campaign that delivers a modified version of an open-source remote access...
-

 3.5KVulnerabilities
3.5KVulnerabilitiesCritical Cisco Flaw Lets Hackers Remotely Take Over Unified Comms Systems
Cisco has released patches to address a critical security flaw impacting Unified Communications and Contact Center Solutions products that could permit an...
-

 3.1KVulnerabilities
3.1KVulnerabilitiesCritical Jenkins Vulnerability Exposes Servers to RCE Attacks – Patch ASAP!
The maintainers of the open-source continuous integration/continuous delivery and deployment (CI/CD) automation software Jenkins have resolved nine security flaws, including a critical...
-

 424Data Breach
424Data BreachTech Giant HP Enterprise Hacked by Russian Hackers Linked to DNC Breach
Hackers with links to the Kremlin are suspected to have infiltrated information technology company Hewlett Packard Enterprise’s (HPE) cloud email environment to...
-

 888Malware
888MalwareNorth Korean Hackers Weaponize Research Lures to Deliver RokRAT Backdoor
Media organizations and high-profile experts in North Korean affairs have been at the receiving end of a new campaign orchestrated by a...
-

 2.4KMalware
2.4KMalwareInvoice Phishing Alert: TA866 Deploys WasabiSeed & Screenshotter Malware
The threat actor tracked as TA866 has resurfaced after a nine-month hiatus with a new large-volume phishing campaign to deliver known malware...
-

 4.2KMalware
4.2KMalwareExperts Warn of macOS Backdoor Hidden in Pirated Versions of Popular Software
Pirated applications targeting Apple macOS users have been observed containing a backdoor capable of granting attackers remote control to infected machines. “These...
-

 492Data Breach
492Data BreachMFA Spamming and Fatigue: When Security Measures Go Wrong
In today’s digital landscape, traditional password-only authentication systems have proven to be vulnerable to a wide range of cyberattacks. To safeguard critical...
-

 2.3KVulnerabilities
2.3KVulnerabilitiesPixieFail UEFI Flaws Expose Millions of Computers to RCE, DoS, and Data Theft
Multiple security vulnerabilities have been disclosed in the TCP/IP network protocol stack of an open-source reference implementation of the Unified Extensible Firmware...
-
 3.5KMalware
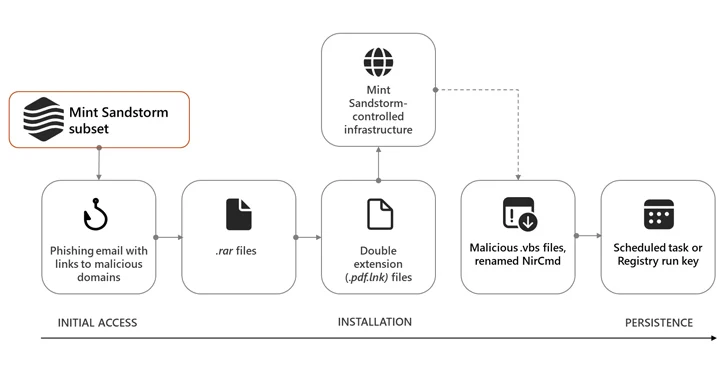
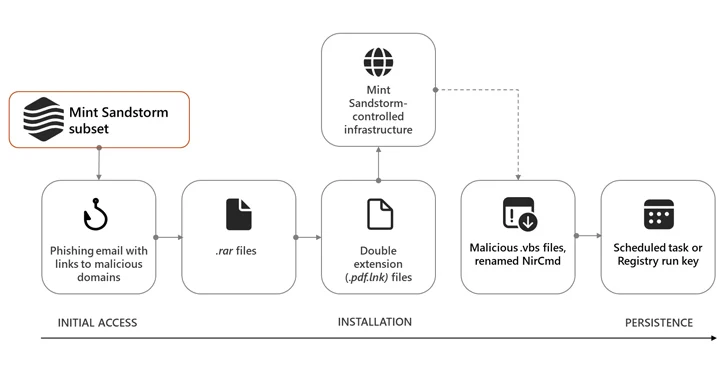
3.5KMalwareIranian Hackers Masquerade as Journalists to Spy on Israel-Hamas War Experts
High-profile individuals working on Middle Eastern affairs at universities and research organizations in Belgium, France, Gaza, Israel, the U.K., and the U.S....
-

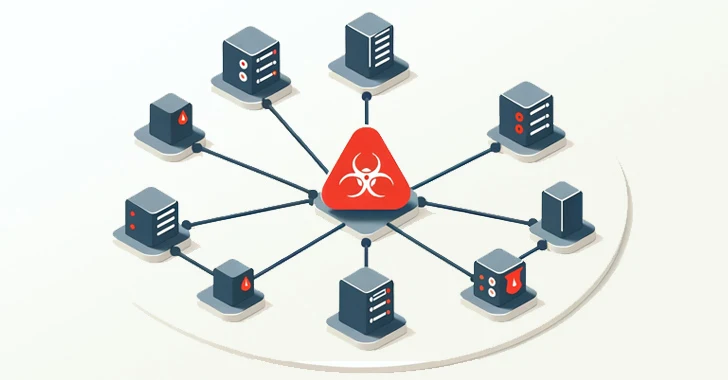
 4.1KMalware
4.1KMalwareFeds Warn of AndroxGh0st Botnet Targeting AWS, Azure, and Office 365 Credentials
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) and the Federal Bureau of Investigation (FBI) warned that threat actors deploying the AndroxGh0st...






