All posts tagged "cybersecurity"
-

 3.6KVulnerabilities
3.6KVulnerabilitiesGitHub Rotates Keys After High-Severity Vulnerability Exposes Credentials
GitHub has revealed that it has rotated some keys in response to a security vulnerability that could be potentially exploited to gain...
-
 3.2KVulnerabilities
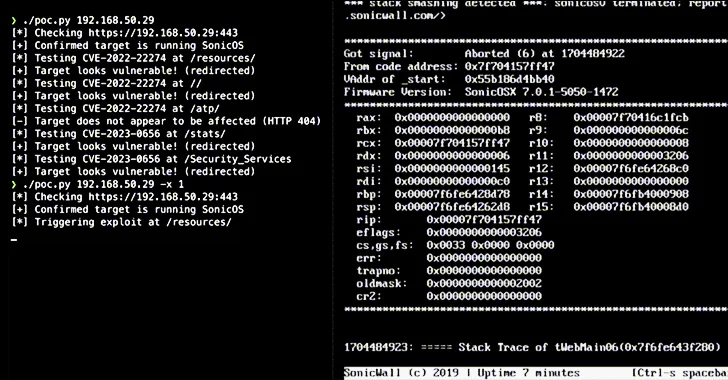
3.2KVulnerabilitiesAlert: Over 178,000 SonicWall Firewalls Potentially Vulnerable to Exploits – Act Now
Over 178,000 SonicWall firewalls exposed over the internet are exploitable to at least one of the two security flaws that could be...
-

 1.1KMalware
1.1KMalwareRemcos RAT Spreading Through Adult Games in New Attack Wave
The remote access trojan (RAT) known as Remcos RAT has been found being propagated via webhards by disguising it as adult-themed games...
-

 810Malware
810MalwareHackers Weaponize Windows Flaw to Deploy Crypto-Siphoning Phemedrone Stealer
Threat actors have been observed leveraging a now-patched security flaw in Microsoft Windows to deploy an open-source information stealer called Phemedrone Stealer....
-

 804Vulnerabilities
804VulnerabilitiesHigh-Severity Flaws Uncovered in Bosch Thermostats and Smart Nutrunners
Multiple security vulnerabilities have been disclosed in Bosch BCC100 thermostats and Rexroth NXA015S-36V-B smart nutrunners that, if successfully exploited, could allow attackers...
-
 1.4KVulnerabilities
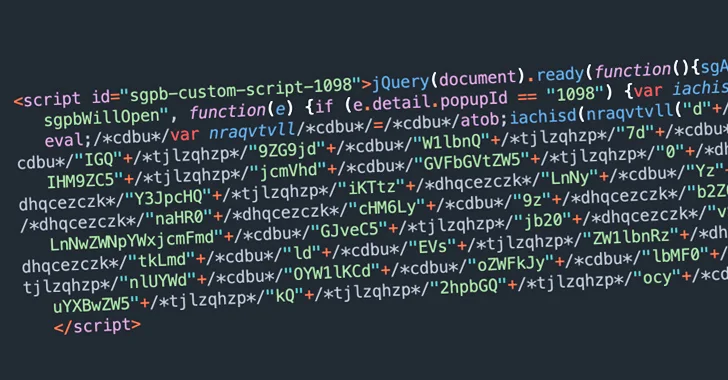
1.4KVulnerabilitiesBalada Injector Infects Over 7,100 WordPress Sites Using Plugin Vulnerability
Thousands of WordPress sites using a vulnerable version of the Popup Builder plugin have been compromised with a malware called Balada Injector....
-
 5.1KVulnerabilities
5.1KVulnerabilitiesNew Findings Challenge Attribution in Denmark’s Energy Sector Cyberattacks
The cyber attacks targeting the energy sector in Denmark last year may not have had the involvement of the Russia-linked Sandworm hacking...
-
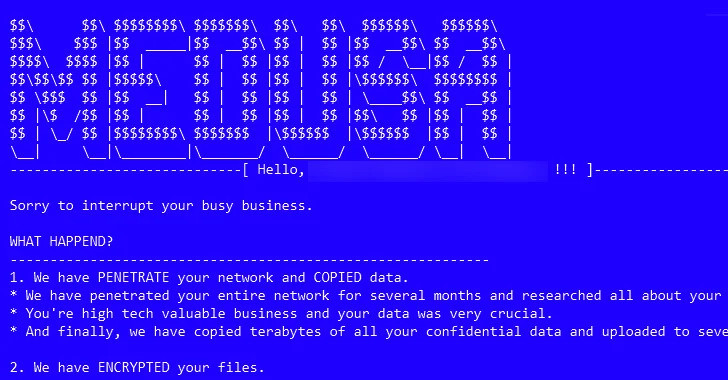
 3.4KMalware
3.4KMalwareMedusa Ransomware on the Rise: From Data Leaks to Multi-Extortion
The threat actors associated with the Medusa ransomware have ramped up their activities following the debut of a dedicated data leak site...
-

 2.8KMalware
2.8KMalwareCryptominers Targeting Misconfigured Apache Hadoop and Flink with Rootkit in New Attacks
Cybersecurity researchers have identified a new attack that exploits misconfigurations in Apache Hadoop and Flink to deploy cryptocurrency miners within targeted environments....
-
 535Malware
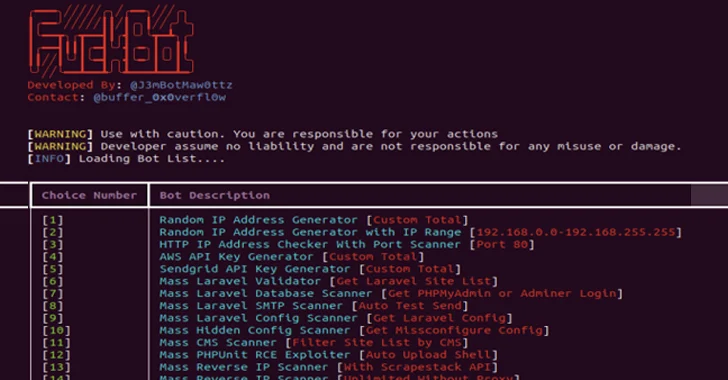
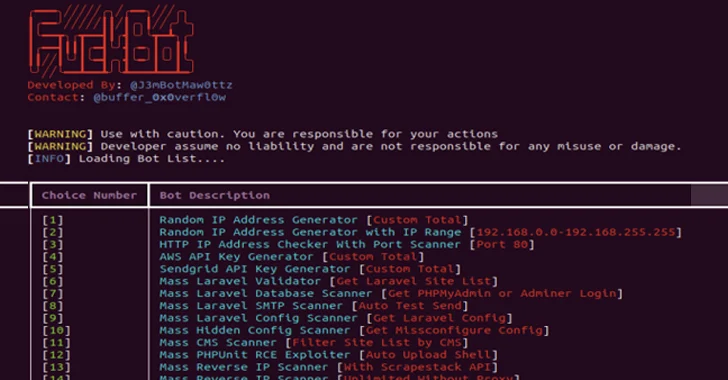
535MalwareNew Python-based FBot Hacking Toolkit Aims at Cloud and SaaS Platforms
A new Python-based hacking tool called FBot has been uncovered targeting web servers, cloud services, content management systems (CMS), and SaaS platforms...
-
 4.1KMalware
4.1KMalwareAtomic Stealer Gets an Upgrade – Targeting Mac Users with Encrypted Payload
Cybersecurity researchers have identified an updated version of a macOS information stealer called Atomic (or AMOS), indicating that the threat actors behind...
-
 231Vulnerabilities
231VulnerabilitiesCisco Fixes High-Risk Vulnerability Impacting Unity Connection Software
Cisco has released software updates to address a critical security flaw impacting Unity Connection that could permit an adversary to execute arbitrary...
-

 1.3KData Breach
1.3KData BreachGetting off the Attack Surface Hamster Wheel: Identity Can Help
IT professionals have developed a sophisticated understanding of the enterprise attack surface – what it is, how to quantify it and how...
-
 3.9KMalware
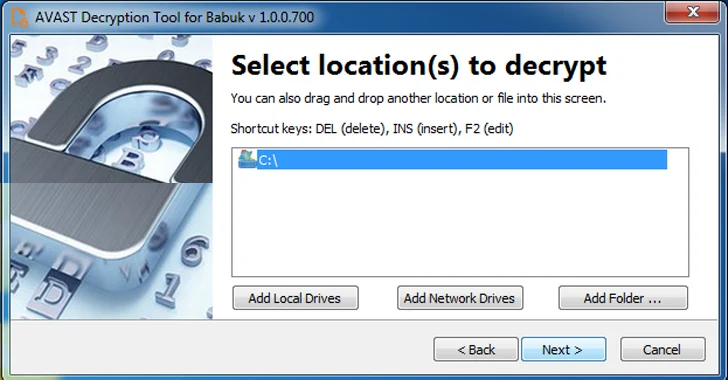
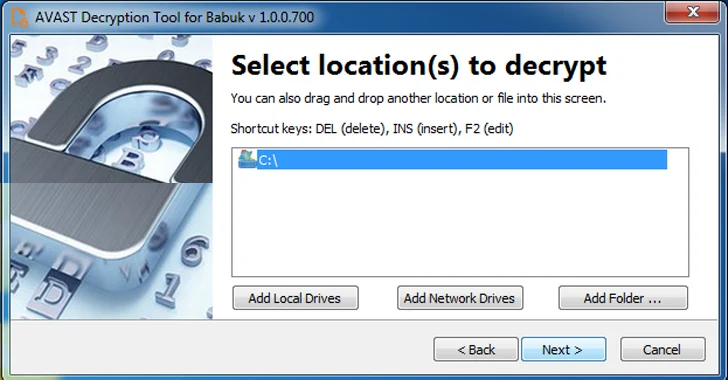
3.9KMalwareFree Decryptor Released for Black Basta and Babuk’s Tortilla Ransomware Victims
A decryptor for the Tortilla variant of the Babuk ransomware has been released by Cisco Talos, allowing victims targeted by the malware...
-
 2.3KVulnerabilities
2.3KVulnerabilitiesCISA Flags 6 Vulnerabilities – Apple, Apache, Adobe, D-Link, Joomla Under Attack
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has added six security flaws to its Known Exploited Vulnerabilities (KEV) catalog, citing evidence...
-
 2.8KVulnerabilities
2.8KVulnerabilitiesWhy Public Links Expose Your SaaS Attack Surface
Collaboration is a powerful selling point for SaaS applications. Microsoft, Github, Miro, and others promote the collaborative nature of their software applications...
-

 2.8KMalware
2.8KMalwareSyrian Hackers Distributing Stealthy C#-Based Silver RAT to Cybercriminals
Threat actors operating under the name Anonymous Arabic have released a remote access trojan (RAT) called Silver RAT that’s equipped to bypass...
-
 1.2KData Breach
1.2KData BreachUnifying Security Tech Beyond the Stack: Integrating SecOps with Managed Risk and Strategy
Cybersecurity is an infinite journey in a digital landscape that never ceases to change. According to Ponemon Institute1, “only 59% of organizations...
-

 5.0KVulnerabilities
5.0KVulnerabilitiesSpectralBlur: New macOS Backdoor Threat from North Korean Hackers
Cybersecurity researchers have discovered a new Apple macOS backdoor called SpectralBlur that overlaps with a known malware family that has been attributed...
-

 1.9KMalware
1.9KMalwareOrange Spain Faces BGP Traffic Hijack After RIPE Account Hacked by Malware
Mobile network operator Orange Spain suffered an internet outage for several hours on January 3 after a threat actor used administrator credentials...
-

 5.0KVulnerabilities
5.0KVulnerabilitiesAlert: Ivanti Releases Patch for Critical Vulnerability in Endpoint Manager Solution
Ivanti has released security updates to address a critical flaw impacting its Endpoint Manager (EPM) solution that, if successfully exploited, could result...






