All posts tagged "DoS attack"
-

 1.4KVulnerabilities
1.4KVulnerabilitiesNew HTTP/2 Vulnerability Exposes Web Servers to DoS Attacks
New research has found that the CONTINUATION frame in the HTTP/2 protocol can be exploited to conduct denial-of-service (DoS) attacks. The technique...
-

 3.4KVulnerabilities
3.4KVulnerabilitiesHigh-Severity Flaws Uncovered in Atlassian Products and ISC BIND Server
Atlassian and the Internet Systems Consortium (ISC) have disclosed several security flaws impacting their products that could be exploited to achieve denial-of-service...
-
 2.8KVulnerabilities
2.8KVulnerabilitiesZyxel Firewall Devices Vulnerable to Remote Code Execution Attacks — Patch Now
Networking equipment maker Zyxel has released patches for a critical security flaw in its firewall devices that could be exploited to achieve...
-

 3.2KVulnerabilities
3.2KVulnerabilitiesApple Releases iPhone and iPad Updates to Patch HomeKit DoS Vulnerability
Apple on Wednesday rolled out software updates for iOS and iPadOS to remediate a persistent denial-of-service (DoS) issue affecting the HomeKit smart...
-

 5.1KVulnerabilities
5.1KVulnerabilitiesOpenSSL Releases Patches for 2 High-Severity Security Vulnerabilities
The maintainers of OpenSSL have released a fix for two high-severity security flaws in its software that could be exploited to carry...
-
 420Vulnerabilities
420VulnerabilitiesNew Critical Exim Flaw Exposes Email Servers to Remote Attacks — Patch Released
A critical security vulnerability has been discovered and fixed in the popular open-source Exim email server software, which could allow a remote...
-

 418DDOS
418DDOSHacker Sentenced 27 months in prison for Launching Massive DDoS Attacks on Sony and Gaming Networks
A man from Utah sentenced 27 months in prison for launching massive DDoS attack against Sony and online gaming companies and its servers....
-

 252News
252NewsNvidia GPU Display Drivers Could Be Exploited To Launch DoS Attack
Nvidia GPU display drivers could be on the radar of hackers. According to the latest news, Nvidia is prompting Geforce graphics card...
-

 211Incidents
211IncidentsHackers deceive millions of mobile device users to launch massive DoS attack
One of the most constant threats faced by website, web applications, and online infrastructure operators are the so called denial-of-service (DoS) attacks....
-

 268Incidents
268IncidentsDoS attack over Blizzard
A denial-of-service attack (DoS) to Blizzard Entertainment that lasted the entire weekend and caused a severe delay for some players and prevented others from...
-
 335Hacked
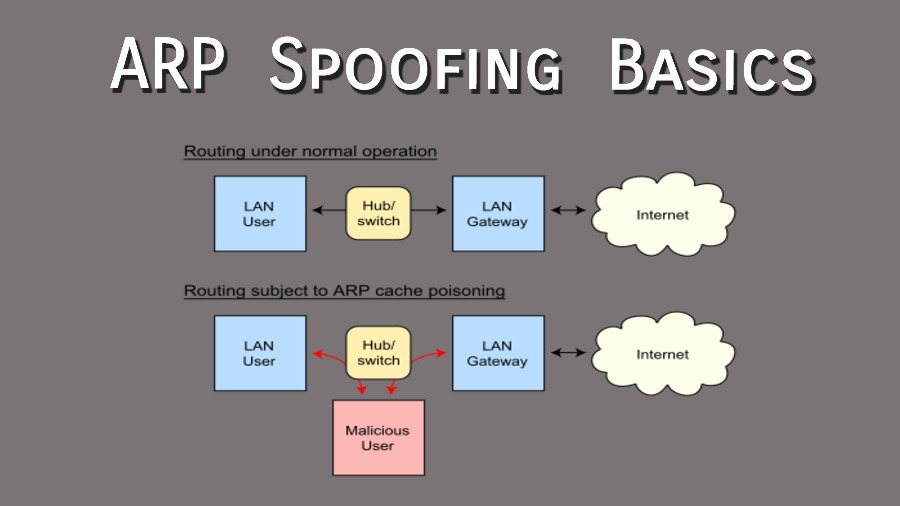
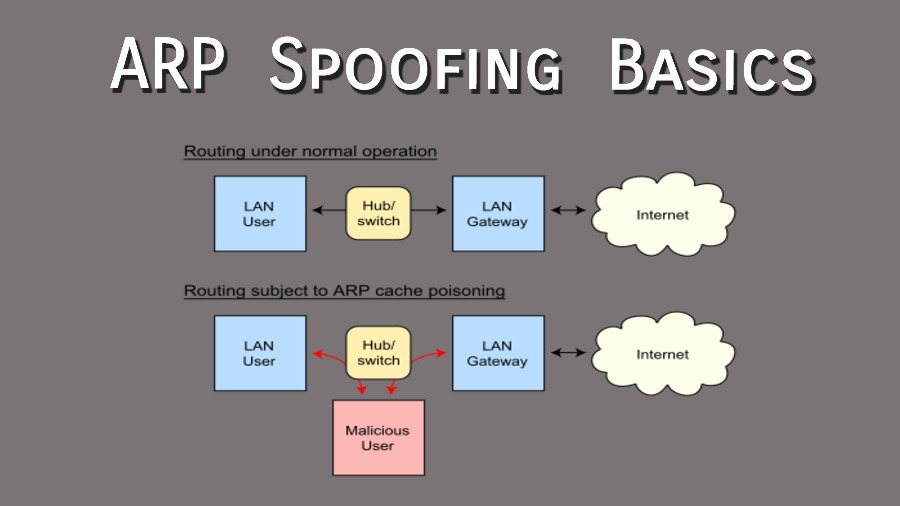
335HackedWhat Is ARP Spoofing? — Attacks, Detection, And Prevention
Spoofing is often defined as imitating (something) while exaggerating its characteristic features for comic effect. Not in the real world but also...
-
Man-In-The-Middle
Xerosploit – Advanced Man In The Middle Framework
Xerosploit is a penetration testing toolkit whose goal is to perform man in the middle attacks for penetration testing purposes. It brings...
-
 205Trojan / Worms
205Trojan / WormsDOS Computer worm SQL Slammer made a Comeback
DOS Computer worm SQL Slammer is hitting again. A computer worm is an independent malware computer program that recreates itself to spread to...
-

 208Hacked
208HackedDoS And DDoS Attacks — The Origin Of A Species
Short Bytes: Over the last few months, we’ve seen some of the largest DDoS attacks to date and, by far, the most disruptive. You...
-
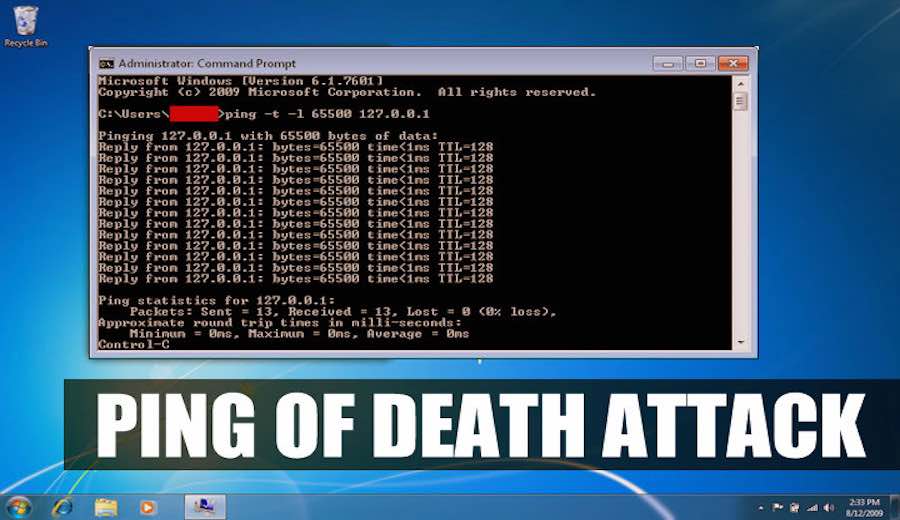
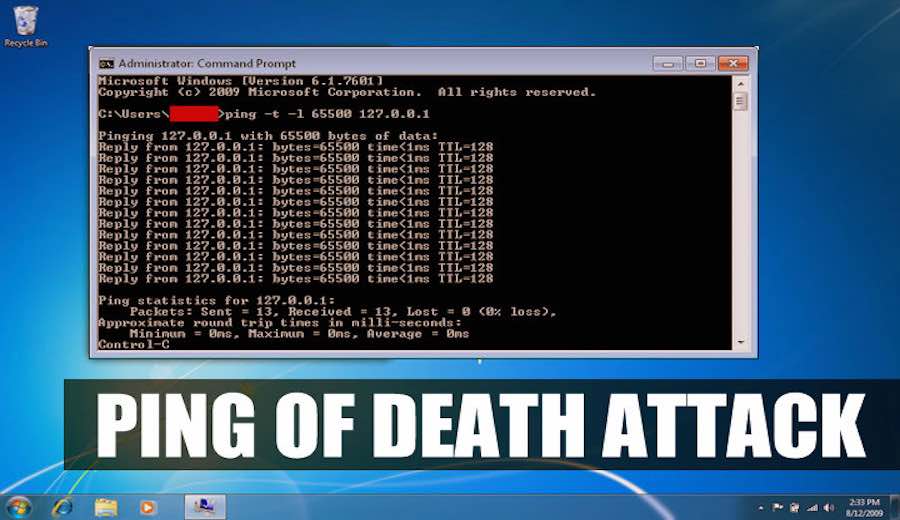 474How To
474How ToHow To Perform Ping of Death Attack Using CMD And Notepad (Just For Learning)
Short Bytes: A ping packet can also be malformed to perform denial of service attack by sending continuous ping packets to the...
-

 252Hacked
252HackedYour BitTorrent Client Can Be Exploited for DoS Attacks, Research Warns
Short Bytes: According to a new research, your BitTorrent client and BitTorrent Sync can be targeted and successfully exploited for DoS (Denial...
-

 317Denial of service
317Denial of serviceHow to perform a simple DOS attack
Performing a DOS attack may seem confusing at first , but when you have the right tools and knowledge , it’s quite...






