All posts tagged "email"
-
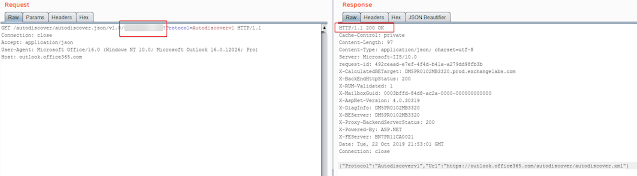
 609Information Gathering
609Information GatheringUhOh365 – Check If An Email Address Is Valid In Office365 (User/Email)
A script that can see if an email address is valid in Office365. This does not perform any login attempts, is...
-

 1.9KIncidents
1.9KIncidents20 years in prison for sending malware emails and infecting computers
According to ethical hacking specialists, two Romanian citizens have been sentenced to 20 years in prison for infecting more than 400,000 computer...
-
 152.0KData Security
152.0KData SecurityAMP for Email: why so secure and how to get whitelisted?
If you’re reading this post, you are probably more or less familiar with brand new AMP for Emails technology developed by Google....
-

 3.9KData Security
3.9KData SecurityGmail is the most secure email service. What about the most insecure? It’s AOL. Full list of email services most exposed to hackers
Unfortunately, data breaches are very common incidents today, with email addresses being one of the most exposed data in these cases. In...
-

 523Data Breach
523Data BreachClick2mail Hacked – Hackers Starts Sending Spam Emails To Stolen Email Address of Users
Famous Email service provider Click2mail suffering from a massive data breach that leaked their customer sensitive personal information, and the attackers used...
-

 293Incidents
293IncidentsHacker sends strange message to all customers of a shoe company
A threat actor has played a bad trick on the IT team and many of the customers of a popular shoe company....
-

 388Cyber Crime
388Cyber CrimeA pervert Yahoo employee hacked 6,000 accounts using internal system
Once hacking Yahoo Mail accounts, the employee also compromised accounts to access his victims’ Dropbox, Facebook, Gmail, and iCloud accounts. Yahoo Mail...
-

 401Incidents
401IncidentsOperation reWired: The FBI arrests 300 hackers in different countries
Cybercrime has been punched in the face. Ethical hacking specialists report that the FBI has commanded an international operation that led to...
-
 344Surveillance
344SurveillanceProtonMail denies that it offers real-time surveillance assistance (Updated)
A Swiss lawyer has accused ProtonMail that the company has initiated offering IP Logging upon request of Swiss authorities. ProtonMail, the famous...
-

 436Lists
436Lists7 Best Free Email Services For 2019 — Get An Email Account Without Paying
Are you looking for some free email services for 2019? Well, you have landed in the right place. We have already talked...
-

 392Data Security
392Data SecurityWhat to do if your email is found on the Dark Web
If your email is on the dark web it is quite possible that its password is leaked as well either in plain...
-
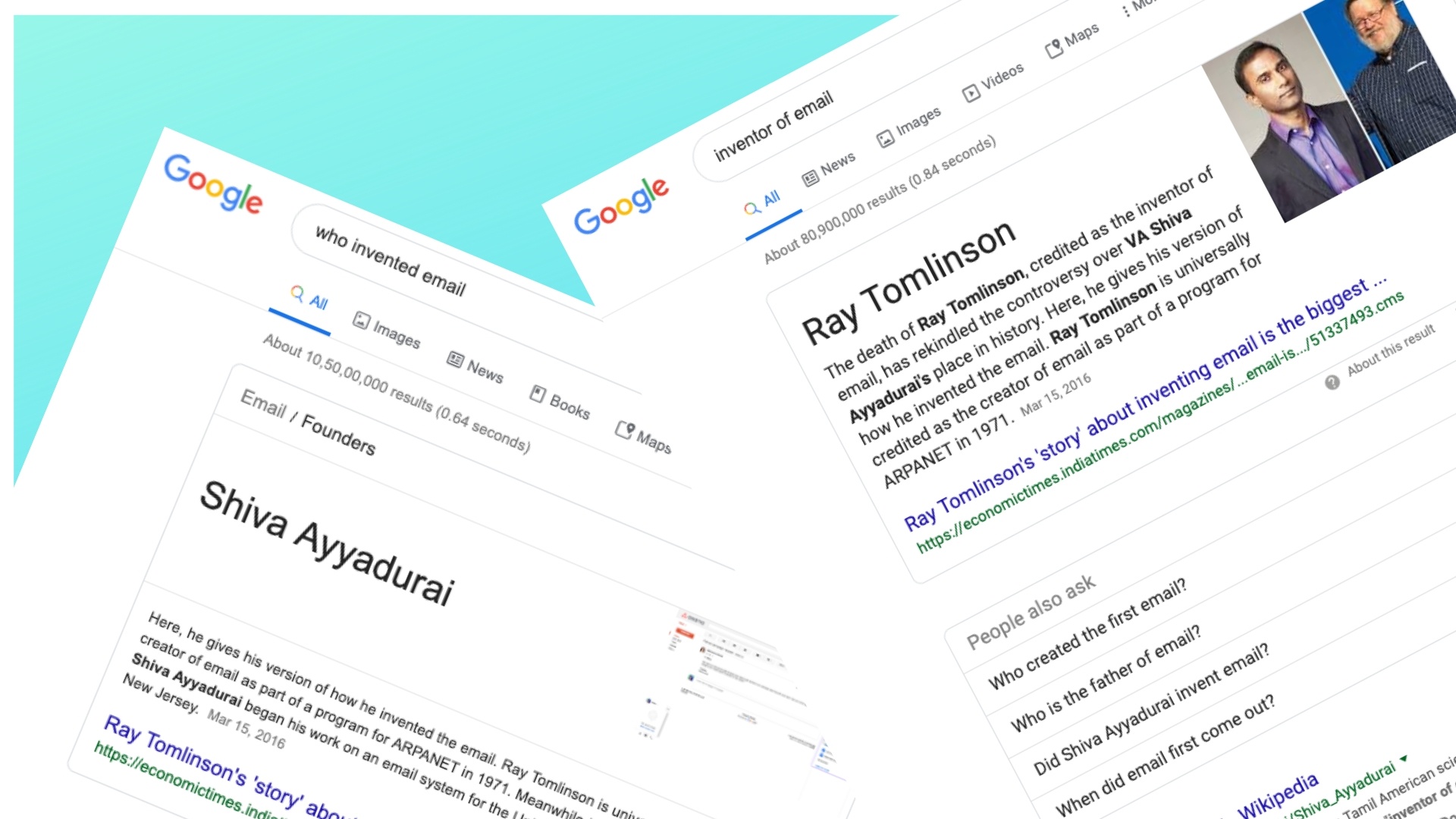
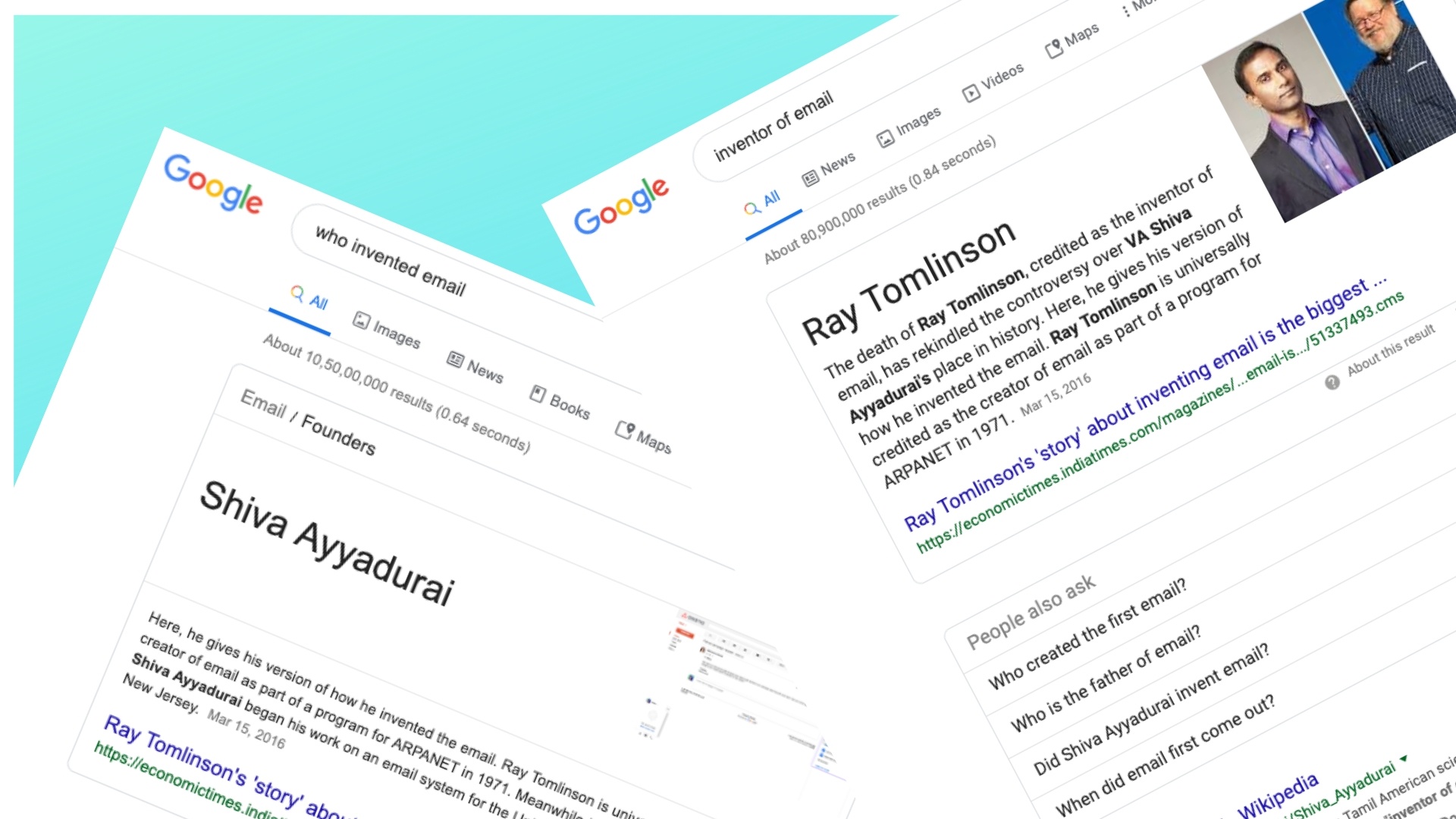 307News
307NewsThe Biggest Problem With Google Search
We’ve come across the human bias factor seeping into AI algorithms from time-to-time — the latest being Google Images showing pictures of...
-

 443Phishing
443PhishingTop 10 Best Preventive Methods to Secure Email Accounts from Email Hackers
Secure Email Accounts is one of the most important concerns in the digital world since the email account is one of the...
-

 354News
354NewsFacebook Caught Asking Email Account Passwords From Some Users
It hasn’t even been a month since Facebook admitted that it stored millions of user passwords in plaintext on its servers. Now, Facebook wants some...
-
 251Data Breach
251Data Breach800 Million Emails Leaked Online From Worlds Largest Email Verification Service
Researchers discovered the 150GB volume of biggest and most comprehensive email unprotected MongoDB that leaked 800 Million Email data online that belongs...
-

 370Malware
370MalwareNew URL filter evasion method for phishing campaigns
Malicious campaign operators have devised a new method for sending documents with malicious files Phishing campaign operators found ways to prevent malware-loaded...
-
 232Malware
232MalwareHackers Bypass Google Filters & Launching CSV Malware via Google Sheets
Cybercriminals are using new sophisticated techniques to spread CSV malware via Google sheets instead of using Microsoft Excel sheet which is often...
-

 238Incidents
238IncidentsThousands of web domains were hijacked due to GoDaddy vulnerability
An unknown attacker has exploited this weakness to deploy multiple malicious email campaigns At the end of last year a campaign of...
-

 397Incidents
397IncidentsTwitter: “Your private tweets were public for years”
A new security incident shakes this social network The social network Twitter has just announced the finding of a security flaw that...
-

 322Data Security
322Data SecurityThird-Party Apps May Read Your Email: Learn How to Protect
Sad news about the unauthorized viewing of email messages by third-party application developers has alarmed Gmail users. It’s understood the Internet giant...
-
 285Hacked
285HackedGoogle Slammed For Giving Gmail Access To Third Party Developers (Humans)
There are many third-party apps that require access to your Gmail account. For instance, the ones that help you plan trips or...






