All posts tagged "exploits"
-

 1.0KExploitation Tools
1.0KExploitation ToolsSecurityNotFound – 404 Page Not Found Webshell
Clone me! Clone or download the project: git clone https://github.com/CosasDePuma/SecurityNotFound.git SecurityNotFound cd SecurityNotFound “Installation” The src/404.php file should be located on...
-
 359Malware
359MalwareNew Variant of Mirai Malware Using 13 Different Exploits to Hack Routers Including D-Link, Linksys, GPON, Netgear, Huawei
Researchers discovered a new wave of Mirai Variant that used 13 different exploits to attack various router models and other network devices....
-

 285Malware
285MalwareNow Mirai Malware Attack as Miori delivered via Delivered via Remote Code Execution Exploit
Most Destructive IoT malware Mirai now being delivered as Miori and its spreading via dangerous remote code execution exploits. Mirai malware has...
-
 331Information Gathering
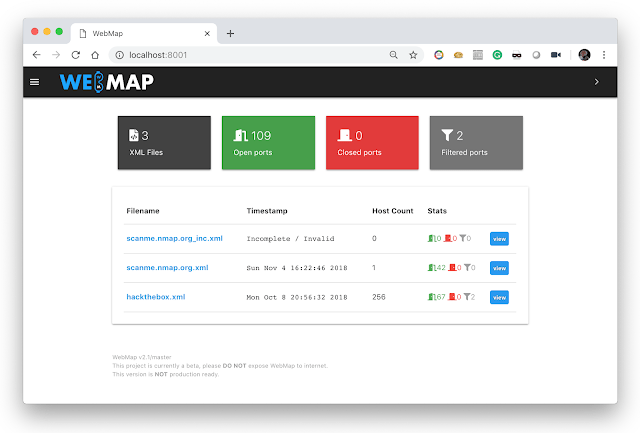
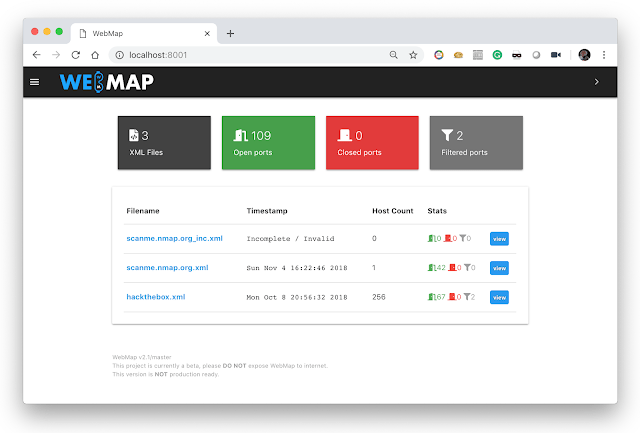
331Information GatheringWebMap – Nmap Web Dashboard And Reporting
A Web Dashbord for Nmap XML Report Usage You should use this with docker, just by sending this command: $ mkdir /tmp/webmap...
-
 224Exploitation Tools
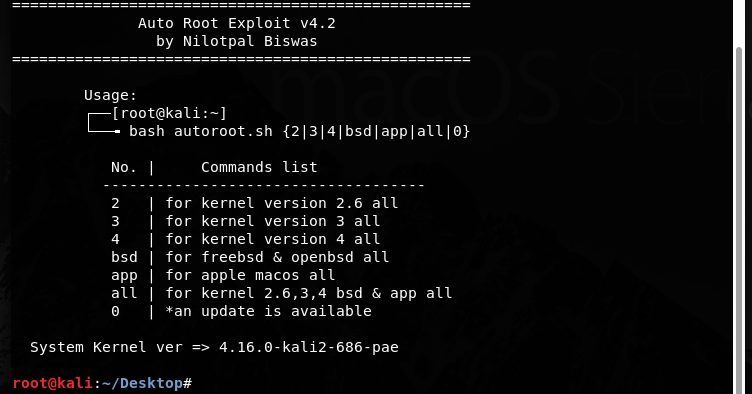
224Exploitation ToolsAuto-Root-Exploit – Auto Root Exploit Tool
Auto Root Exploit Tool Author : Nilotpal Biswas Facebook : https://www.facebook.com/nilotpal.biswas.73 Twitter : https://twitter.com/nilotpalhacker USAGE : for kernel version 2.6 all bash...
-
 271Exploitation Tools
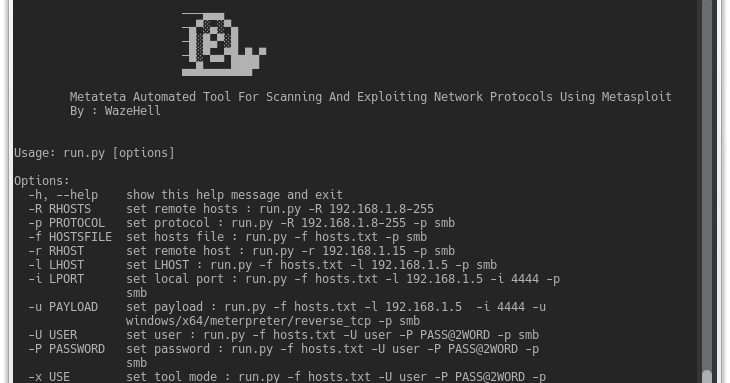
271Exploitation ToolsMetateta – Automated Tool For Scanning And Exploiting Network Protocols Using Metasploit
Metateta Automated Tool For Scanning And Exploiting Network Protocols Using Metasploit For faster pen testing for large networks What You Can Do...
-

 322Pentest
322PentestExploit Pack V10.07 Released with More than 38.000+ Exploits Including Zero-Days
Exploit Pack is a well-integrated open source tool for conducting professional penetration tests. As like any other penetration testing tool it requires...
-
 272Malware
272MalwareHackers Distributing Variety of New Exploits and Malware via Microsoft Office Document Exploit Kit
Newly discovered Microsoft office document exploit kit contains a variety of recent exploits and Malware such as Lokibot, Formbook and tracking kit...
-
 246Exploitation Tools
246Exploitation Toolsroxysploit – Penetration Testing Suite
roxysploit is a community-supported, open-source and penetration testing suite that supports attacks for numerous scenarios. conducting attacks in the field. Some containing Plugins in...
-
 263Exploitation Tools
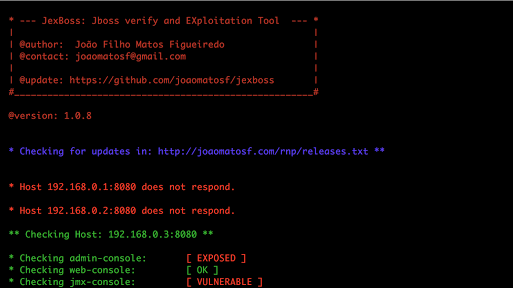
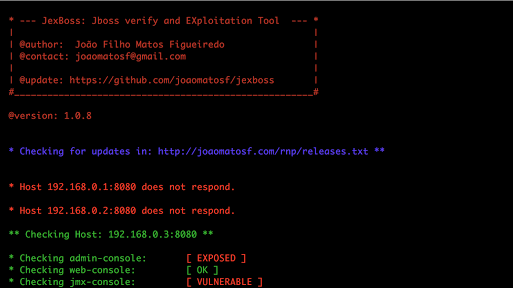
263Exploitation ToolsJexBoss – JBoss (and others Java Deserialization Vulnerabilities) verify and Exploitation Tool
JexBoss is a tool for testing and exploiting vulnerabilities in JBoss Application Server and others Java Platforms, Frameworks, Applications, etc. Requirements Python...
-
Stress Testing
drinkme – Shellcode Testing Harness
drinkme is a shellcode test harness. It reads shellcode from stdin and executes it. This allows pentesters to quickly test their payloads...
-
Exploitation Tools
Generate Shellcodes & Backdoors using ShellSploit Framework and Kali Linux 2017.2
Hey Guys, In this video i show you how to generate shellcodes and Backdoors using ShellSploit Framework and Kali Linux 2017.2. ShellSploit:...
-

 237How To
237How ToDAVScan – Fingerprints Servers, Finds Exploits & Scans WebDAV
DAVScan is a quick and lightweight webdav scanner designed to discover hidden files and folders on DAV enabled webservers. The scanner works...
-

 169Vulnerabilities
169VulnerabilitiesLinux bug leaves 1.4 billion Android users vulnerable to hijacking attacks
Off-path attack means malicious hackers can be located anywhere on the Internet. An estimated 80 percent of Android phones contain a recently discovered...
-

 316Cyber Events
316Cyber Events5 most dangerous cyber security vulnerabilities that are exploited by hackers
Here are 5 of the most dangerous cyber security vulnerabilities that are exploited by hackers All the major government organizations and financial firms...
-

 390Cyber Events
390Cyber EventsExploit Flash Heap Isolation for a chance to “win” $100,000
Exploit Flash Heap Isolation for a chance to “win” $100,000 If you can exploit Adobe’s Heap Isolation mitigation in Flash player version...






