All posts tagged "Hacking"
-

 3.6KData Security
3.6KData Security5 Top Cybersecurity Threats to Businesses
Cybersecurity threats are unpredictable but taking a closer look at them and implementing proper security measures seems like a wise decision. The...
-
 4.4KData Security
4.4KData SecuritySolarWinds hackers using NativeZone backdoor against 24 countries
Microsoft has disclosed that the SolarWinds hackers or SolarWinds supply chain attack-fame threat actors are back in action. This time, they are targeting...
-

 588Malware
588MalwareChinese Cyber Espionage Hackers Continue to Target Pulse Secure VPN Devices
Cybersecurity researchers from FireEye unmasked additional tactics, techniques, and procedures (TTPs) adopted by Chinese threat actors who were recently found abusing Pulse...
-

 3.8KCyber Crime
3.8KCyber CrimeRussian admin of cybercrime marketplace Deer.io jailed in US
Kirill Victorovich Firsov, a Russian Citizen has been jailed for 30 months (2.5 years) in US prison for running popular cybercrime marketplace...
-

 4.1KCyber Crime
4.1KCyber Crime22 people indicted on malware, credit card fraud charges
The cyberattack actually occurred back in 2016 and 2017 when an individual installed malware on multiple computers of a retail chain, headquartered...
-

 1.4KMalware
1.4KMalwareMalvertising Campaign On Google Distributed Trojanized AnyDesk Installer
Cybersecurity researchers on Wednesday publicized the disruption of a “clever” malvertising network targeting AnyDesk that delivered a weaponized installer of the remote...
-
 790News
790NewsTop Japanese dating app Omiai hacked; 1.71 million users at risk
Hackread.com can confirm that threat actors on several hacker forums are already hunting for stolen Omiai database. In recent news, Japan’s biggest...
-

 2.9KData Security
2.9KData SecurityAudio equipment giant Bose hit by ransomware attack, data breach
Bose reveals it suffered “a sophisticated cyber-attack that disrupted some of its systems” in the United States. Ransomware attacks are the new...
-

 1.7KData Security
1.7KData SecurityIranian hackers hit Israel with disk wiper in disguise of ransomware
According to SentinelOne, Iranian hackers have developed a combo of disk wiper and ransomware and their target is Israeli cyberinfrastructure. The Agrius...
-

 5.1KVulnerabilities
5.1KVulnerabilitiesCritical RCE Vulnerability Found in VMware vCenter Server — Patch Now!
VMware has rolled out patches to address a critical security vulnerability in vCenter Server that could be leveraged by an adversary to...
-

 3.7KVulnerabilities
3.7KVulnerabilitiesNew High-Severity Vulnerability Reported in Pulse Connect Secure VPN
Ivanti, the company behind Pulse Secure VPN appliances, has published a security advisory for a high severity vulnerability that may allow an...
-

 4.3KVulnerabilities
4.3KVulnerabilitiesNew High-Severity Vulnerability Reported in Pulse Connect Secure VPN
Ivanti, the company behind Pulse Secure VPN appliances, has published a security advisory for a high severity vulnerability that may allow an...
-

 2.7KMalware
2.7KMalwareNew Bluetooth Flaws Let Attackers Impersonate Legitimate Devices
Adversaries could exploit newly discovered security weaknesses in Bluetooth Core and Mesh Profile Specifications to masquerade as legitimate devices and carry out...
-

 5.1KMalware
5.1KMalwareNew Bluetooth Flaws Let Attackers Impersonate Legitimate Devices
Adversaries could exploit newly discovered security weaknesses in Bluetooth Core and Mesh Profile Specifications to masquerade as legitimate devices and carry out...
-

 4.1KMalware
4.1KMalwareResearchers Link CryptoCore Attacks On Cryptocurrency Exchanges to North Korea
State-sponsored hackers affiliated with North Korea have been behind a slew of attacks on cryptocurrency exchanges over the past three years, new...
-

 3.4KMalware
3.4KMalwareResearchers Link CryptoCore Attacks On Cryptocurrency Exchanges to North Korea
State-sponsored hackers affiliated with North Korea have been behind a slew of attacks on cryptocurrency exchanges over the past three years, new...
-

 1.0KMalware
1.0KMalwareFBI Warns Conti Ransomware Hit 16 U.S. Health and Emergency Services
The adversary behind Conti ransomware targeted no fewer than 16 healthcare and first responder networks in the U.S. within the past year,...
-

 2.4KMalware
2.4KMalwareAir India Hack Exposes Credit Card and Passport Info of 4.5 Million Passengers
India’s flag carrier airline, Air India, has disclosed a data breach affecting 4.5 million of its customers over a period stretching nearly...
-
 2.5KMalware
2.5KMalwareInsurance Firm CNA Financial Reportedly Paid Hackers $40 Million in Ransom
U.S. insurance giant CNA Financial reportedly paid $40 million to a ransomware gang to recover access to its systems following an attack...
-
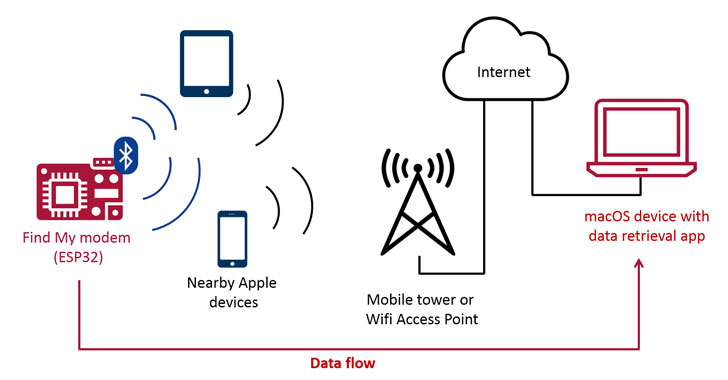
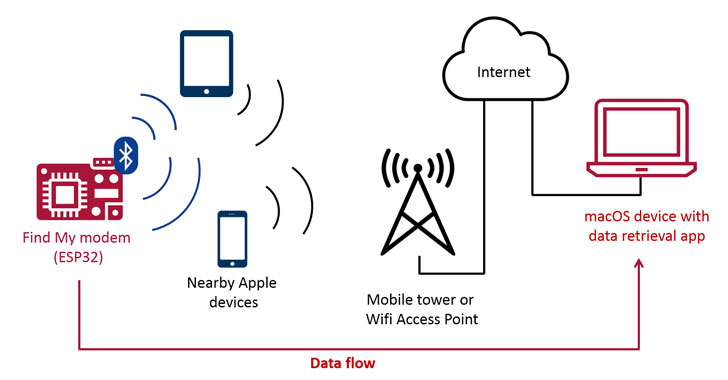 1.1KMalware
1.1KMalwareApple’s Find My Network Can be Abused to Exfiltrate Data From Nearby Devices
Latest research has demonstrated a new exploit that enables arbitrary data to be uploaded from devices that are not connected to the...
-

 1.5KMalware
1.5KMalwareExperts Warn About Ongoing AutoHotkey-Based Malware Attacks
Cybersecurity researchers have uncovered an ongoing malware campaign that heavily relies on AutoHotkey (AHK) scripting language to deliver multiple remote access trojans...






