All posts tagged "iPhone"
-
 299News
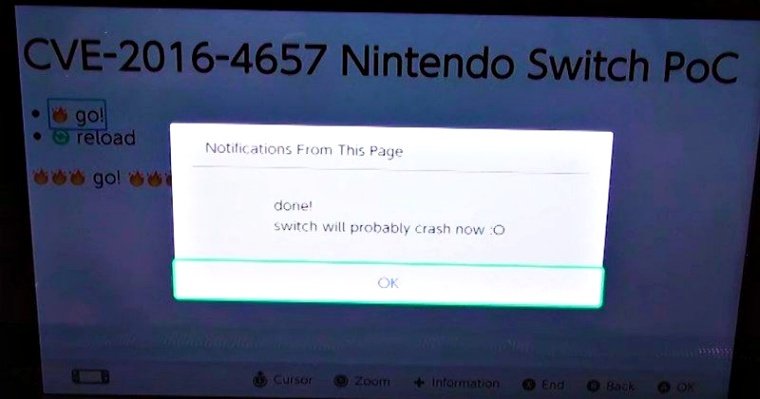
299NewsNintendo Switch Can Be Hacked, Thanks to iOS 9.3 Webkit Exploit
Having a high-profile and so very sought-after device like Nintendo Switch is a risky deal as cyber-criminals are always on the hunt...
-

 376Geek
376GeekCellebrite Can Now Unlock, Extract Data From iPhone 6 and 6 Plus
Cellebrite, the famous Israeli firm known for reportedly cracking the iPhone 5C of San Bernardino shooter is back in the news and...
-

 117Incidents
117IncidentsiPhone Robbers Try to iPhish Victims
In another strange tale from the kinetic-attack-meets-cyberattack department, earlier this week I heard from a loyal reader in Brazil whose wife was...
-

 290Geek
290GeekApple May Introduce Facial Recognition Instead of Touch ID in iPhone 8
Apple had introduced fingerprint scanning feature to prevent users from the hassle of forgetting their passwords and also to make sure that...
-

 248Cyber Crime
248Cyber CrimePayPal users hit with “Payment Successfully Made Via Ali Express” Phishing Scam
PayPal is one of the most used platforms for sending and receiving payments by small medium and large enterprises. This makes it the...
-

 278Geek
278GeekDeleted browsing history on safari may not actually be deleted
Elcomsoft is a Moscow based firm that creates forensics software said it was possible [Pdf] to retrieve your deleted browser history beyond...
-

 369News
369NewsHacker Dumps Hacking Tools Allegedly Stolen from Cellebrite
A hacker is now dumping a large size of sophisticated cracking tools that are said to have been stolen from Cellebrite, the...
-

 171Data Security
171Data SecurityiPhone lock: Did hackers drive Apple to kill iCloud activation checker?
An iPhone serial number hack could explain why Apple killed its iCloud Activation Lock checker. Apple’s decision to remove its Activation Lock...
-

 97Incidents
97IncidentsJapanese researchers: your peace-sign selfies are putting you at risk
If flashing a peace sign is your go-to selfie move, you might want to think about coming up with a new signature...
-

 359Geek
359GeekiCloud Glitch? Woman buys iPhone, finds contact details of top celebs
What would be your reaction if you buy a new iPhone and find your phonebook filled with personal contact numbers of hundreds...
-
 328Geek
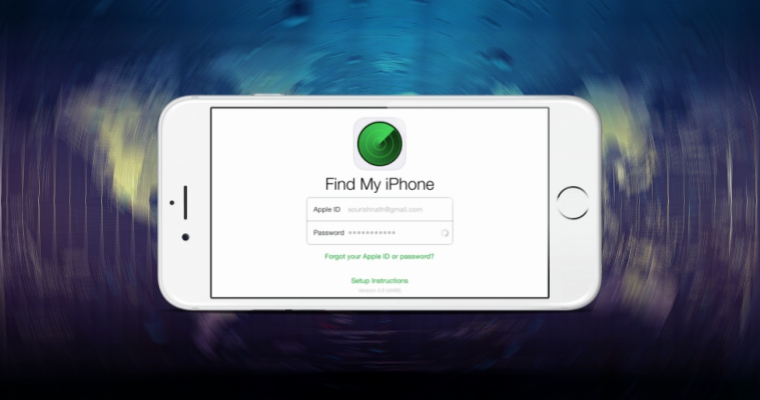
328GeekHow to find your iPhone using “Find my iPhone” app
Our mobile phones are nothing short of a treasure trove of sensitive, private information. We have started relying a lot on our...
-

 207Hacked
207HackedThis Text Message Hack Crashes And Breaks ANY iPhone Messages App In Seconds
Short Bytes: A new iPhone crashing exploit is here to take down and break your iMessages app. Hacker Vincedes3 has uncovered a hack...
-

 193Mobile Security
193Mobile SecurityCritical Bug:Single MMS Can Crash Message application On IOS
A solitary instant message could be abused to impair the Messages application on any iPhone because of an as of late found...
-

 328News
328NewsLeaked info confirms in-house hacking capabilities of Israeli firm Cellebrite
Most iPhone users assume a certain level of security regarding the data on their device. However, a recent report from ZDNet detailing...
-

 107Data Security
107Data SecurityLeaked documents show breadth of iPhone data accessible by Cellebrite forensic tool
Thanks to the recent encryption debate many smartphone owners are keenly aware of personal data stored on their iPhone, from contacts to...
-

 270Cyber Crime
270Cyber CrimeStudent makes documentary after spying on thief who stole his smartphone
It is a fact that we cannot even move from one room to another without our smartphone. Nowadays, smartphones have become a...
-

 187Geek
187GeekMan accused of taking pics under skirt told by court to share his iPhone Passcode
As per the Fifth Amendment, a US citizen cannot be forced to surrender his private information such as passwords or login credentials....
-
 298Lists
298Lists21 Weird Apple Products You Never Knew Existed
Apple did various product experiments in its early years. They tried their clothing lines and some limited stuff. But many people don’t...
-

 218Geek
218GeekU.K. Police don’t pay to unlock iPhones, they mug you while phone is unlocked
If this had happened in the United States, the FBI would have spent millions of dollars from taxpayers money and employed an...
-

 104How To
104How ToVproxy – Forward HTTP/S Traffic To Proxy Instance
Vproxy is a python script tool which configures a PPTP VPN server that will redirect HTTP/HTTPS traffic to your proxy instance host....
-

 392Geek
392GeekIsraeli Firm Says It Can Crack Any Locked Smartphone
For the last few months, Israeli spy firms have been making some strange claims such as Ability says that their “Unlimited Interception...






