All posts tagged "Linux"
-

 316Geek
316GeekEverything About Ubuntu’s New Default Theme “Yaru”: Here’s How To Try It
If you follow the Ubuntu development process closely, you must be knowing about the Ubuntu Communitheme that has been under development for some...
-
 469Geek
469GeekHow To Create A Bootable USB Media Using Rufus For Installing Linux/Windows
USB Drives are the most convenient go-to devices nowadays when the need to prepare a Bootable media arises. For a reason being...
-
 269Network Tools
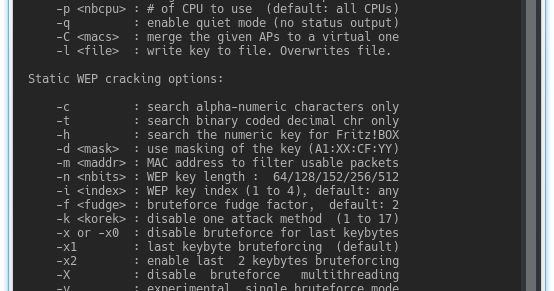
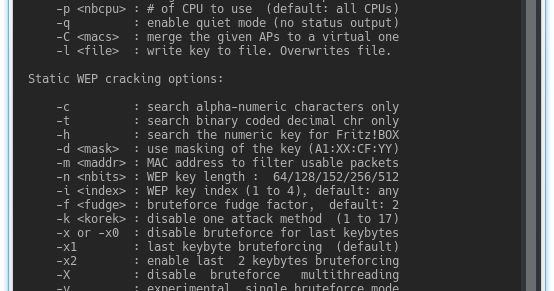
269Network ToolsAircrack-ng 1.3 – Complete Suite Of Tools To Assess WiFi Network Security
Aircrack-ng is a complete suite of tools to assess WiFi network security. It focuses on different areas of WiFi security: Monitoring: Packet...
-

 289Geek
289GeekSlackware, The Oldest Active Linux Distro, Turns 25
On July 16th, 1993, Slackware Linux distribution was officially released. Based entirely on the Softlanding Linux System (SLS) system, it was designed...
-

 270Geek
270GeekDebian 9.5 Released: “Rock Solid” GNU/Linux Distro Arrives With Spectre v2 Fix
Following the fourth point release of Debian 9 “stretch” in March, the developers of the popular GNU/Linux distro have shipped the latest...
-
Exploitation Tools
Pure Blood – A Penetration Testing Framework Created For Hackers / Pentester / Bug Hunter
A Penetration Testing Framework created for Hackers / Pentester / Bug Hunter Menu Web Pentest | Banner Grab | Whois | Traceroute...
-

 179Data Security
179Data SecurityMalicious software packages at Linux repositories
Another sign that the user-controlled software repository should not be fully trusted One of the most popular Linux distros, Arch Linux, has...
-
 255Exploitation Tools
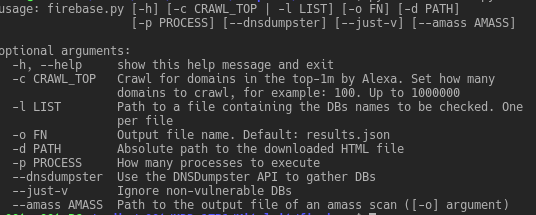
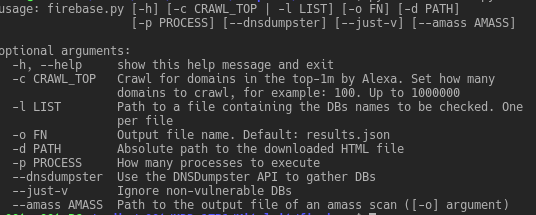
255Exploitation ToolsFirebase Exploiting Tool – Exploiting Misconfigured Firebase Databases
Exploiting vulnerable/misconfigured Firebase databases Prerequisites Non-standard python modules: dnsdumpster bs4 requests Installation If the following commands run successfully, you are ready to...
-

 309Information Gathering
309Information GatheringBlack Owl – Tool To Gather Information, Based On Operative-Framework
This is a simple tool to gather information, based on Operative-Framework. Requirements requests pythonwhois beautifulsoup4 Install requirements $ pip install -r requirements.txt...
-

 261Hacked
261HackedMalware Attack On Arch Linux AUR Repository; Three Packages Infected So Far
Arch Linux software repository named Arch User Repository (AUR) has been infected by malware. As many as three Arch Linux packages available...
-
 213Hacked
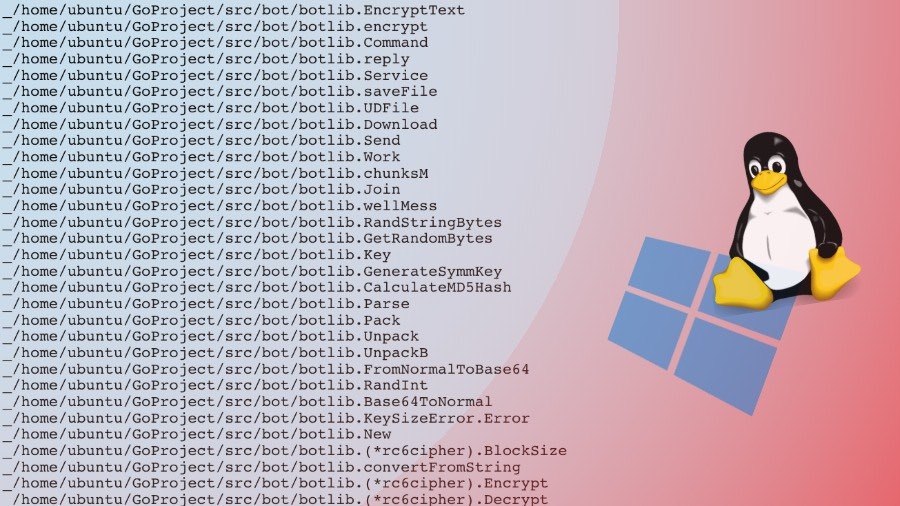
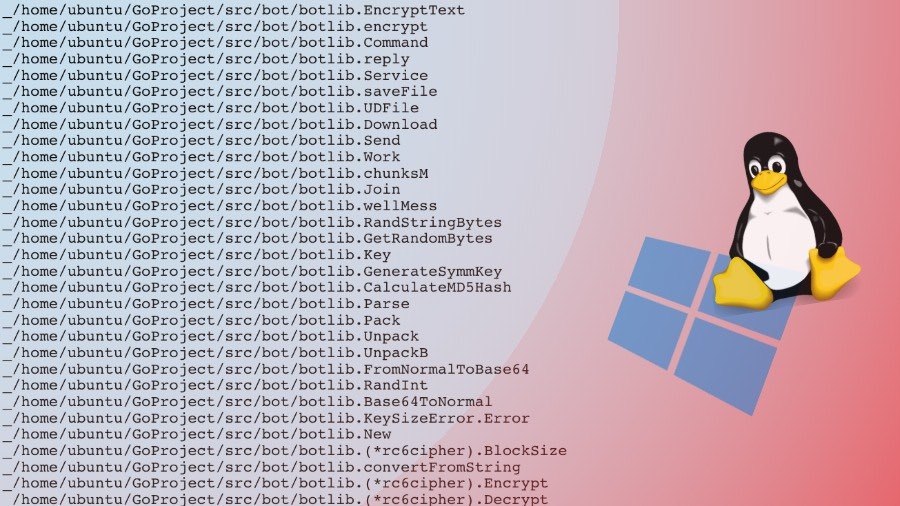
213HackedWellMess: This Go-based Malware Attacks Both Linux And Windows Machines
There’s no doubt that Linux and Mac are more secure operating system choices as opposed to Microsoft Windows. But this doesn’t mean...
-

 294Geek
294GeekRaspberry Pi’s Own App Store Is The Newest Reason To Love This Mini Computer
The Raspberry Pi Foundation keeps updating its Debian-based Raspbian operating system from time to time. The developers keep adding new features to...
-

 256News
256NewsSUSE Linux Has Been Sold For More than $2.5 Billion
SUSE Linux, the open source software company owned by the British company Micro Focus International, was sold to a Swedish private equity...
-
 281Password Attacks
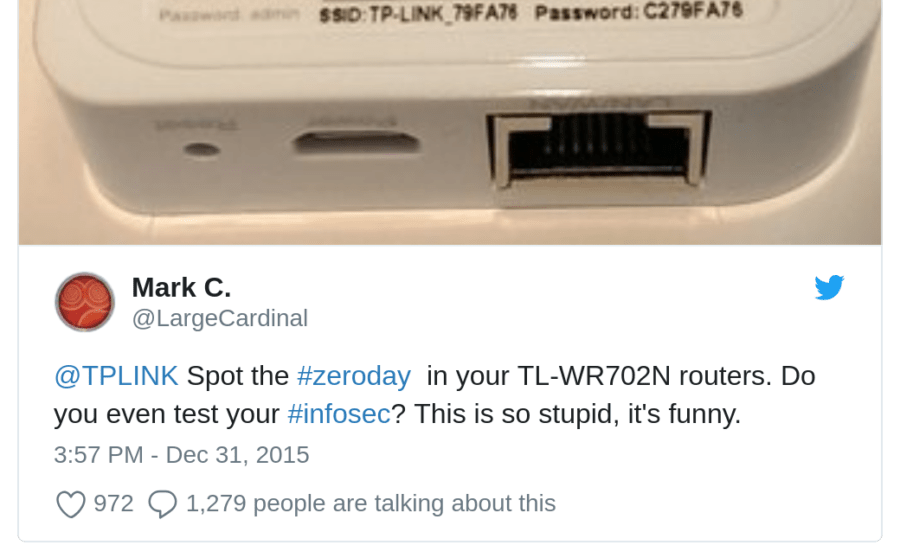
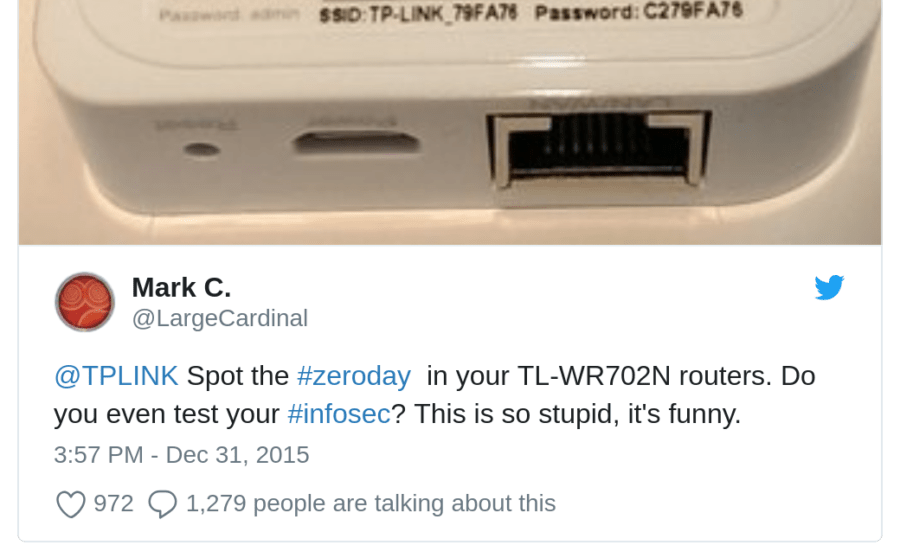
281Password AttacksTP-Link-defaults – Python Script For Trying Default Passwords For Some TP-Link Hotspots
Python script for trying default passwords for some TP-Link Hotspots Inspired by Usage usage: scan.py [-h] [-p] Python script for trying default...
-

 326Geek
326GeekTop 7 Most Popular and Best Cyber Forensics Tools
We often watch experts in movies using forensic tools for their investigations but what cyber forensic tools are used by experts? Well,...
-
 208Geek
208GeekSUSE Linux Is Selling Itself (Again) For $2.5 Billion
The ownership SUSE is getting transferred from UK-based Micro Focus International to Sweden’s investment firm EQT VIII. The deal, which is yet to...
-

 495Geek
495GeekLinux Mint 19 “Tara” Released With New Features: Download Cinnamon, Xfce, MATE Editions Here
Soon after the Linux Mint team started shipping the MintBox Mini 2, they released Linux Mint 19 “Tara,” the most recent and...
-

 262Data Security
262Data SecurityLinux distro suffers hack on GitHub
Data breaches are always bad news, and this is peculiarly bad. Gentoo, a popular Linux distribution (or distro), has suffered the hacking of its...
-
 268Wireless Attacks
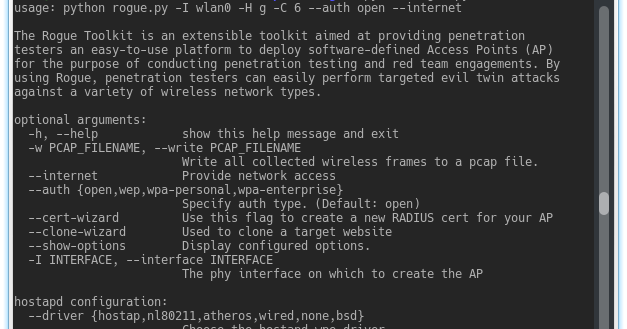
268Wireless AttacksThe Rogue Toolkit – An Extensible Toolkit Aimed At Providing Penetration Testers An Easy-To-Use Platform To Deploy Access Points
The Rogue Toolkit is an extensible toolkit aimed at providing penetration testers an easy-to-use platform to deploy software-defined Access Points (AP)...
-

 332Geek
332GeekGentoo Linux Distro Hacked: All Code On GitHub Compromised
Gentoo Linux holds the reputation of being a “build it yourself” distribution; it needs you to download the source code from the...
-
 347Information Gathering
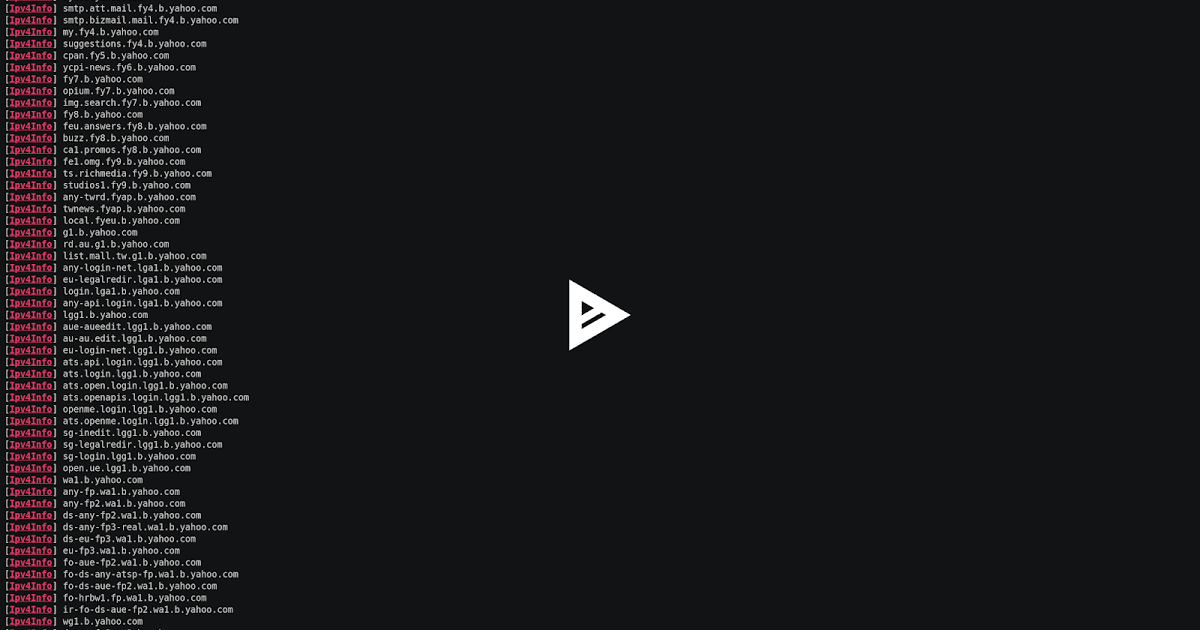
347Information GatheringSubFinder – A Subdomain Discovery Tool That Discovers Valid Subdomains For Websites
SubFinder is a subdomain discovery tool that discovers valid subdomains for websites by using passive online sources. It has a simple modular...






