All posts tagged "Mac"
-

 270Exploitation Tools
270Exploitation ToolsXAttacker – Website Vulnerability Scanner & Auto Exploiter
XAttacker is a Website Vulnerability Scanner & Auto Exploiter developed by Mohamed Riahi Auto Cms Detect [1] WordPress : [+] Adblock Blocker...
-

 220Articles
220ArticlesMaker of sneaky Mac adware sends security researcher cease-and-desist letters
The maker of a sneaky adware that hijacks a user’s browser to serve ads is back with a new, more advanced version...
-
 277Information Gathering
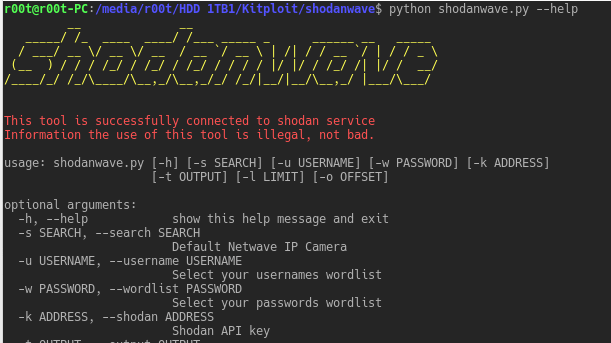
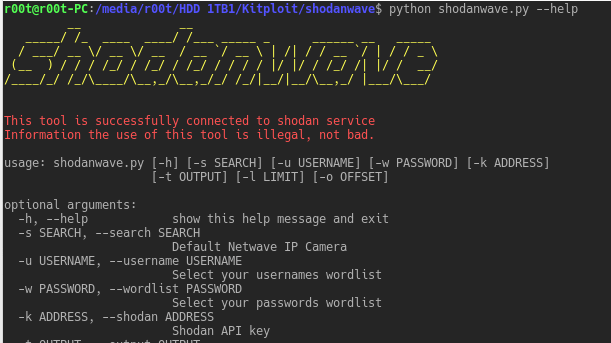
277Information GatheringShodanwave – Exploring and Obtaining Information from Netwave IP Camera
Shodanwave is a tool for exploring and obtaining information from cameras specifically Netwave IP Camera. The tool uses a search engine called...
-

 226Exploitation Tools
226Exploitation ToolsAmber – POC Reflective PE Packer
Amber is a proof of concept packer, it can pack regularly compiled PE files into reflective PE files that can be used...
-
 236Information Gathering
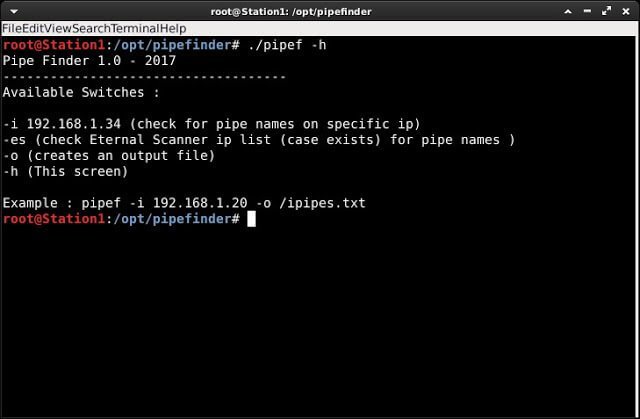
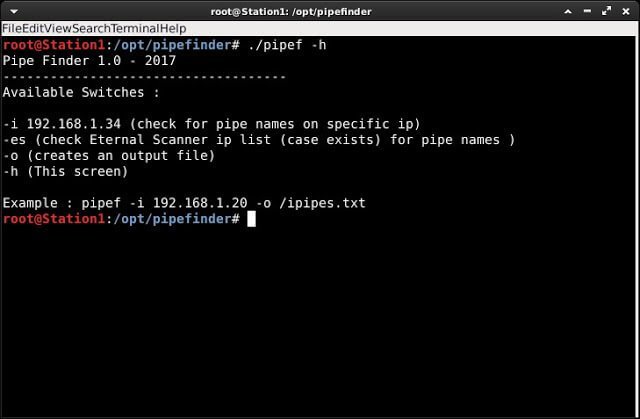
236Information GatheringPipe Finder – Automated script to search in SMB protocol for available pipe names
Automated script to search in SMB protocol for availables pipe names. Requirements metasploit-framework wget pipe_audit_v2.rb module (https://github.com/peterpt/pipe_auditor_fb) – It will be installed...
-
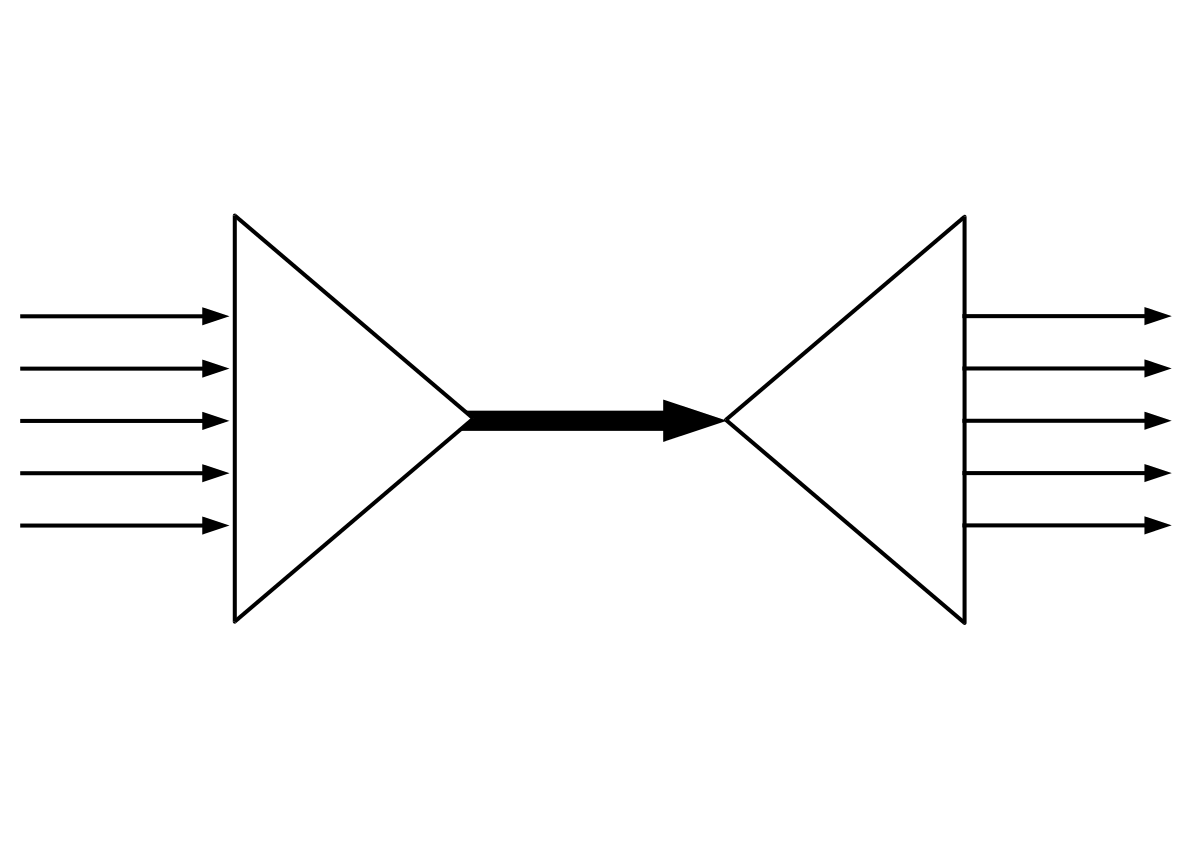
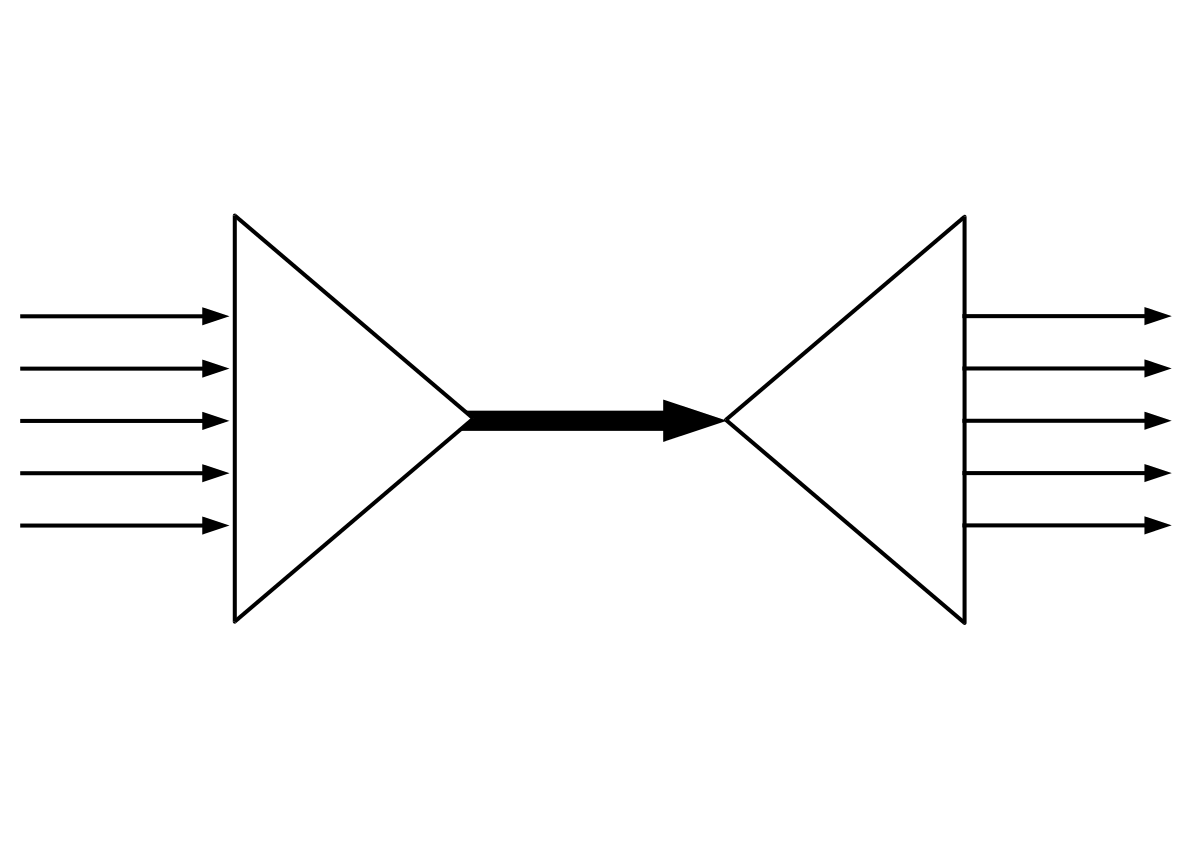 232Network Tools
232Network ToolsSSLH – Applicative Protocol Multiplexer
sslh accepts connections on specified ports, and forwards them further based on tests performed on the first data packet sent by the...
-
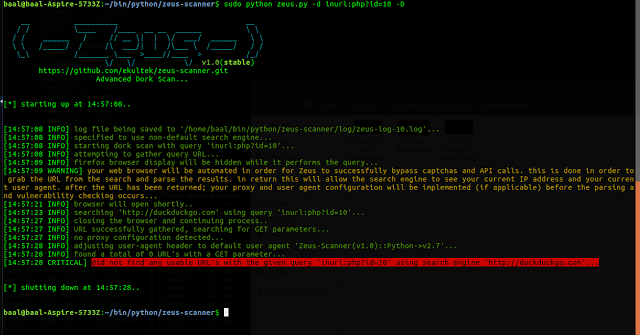
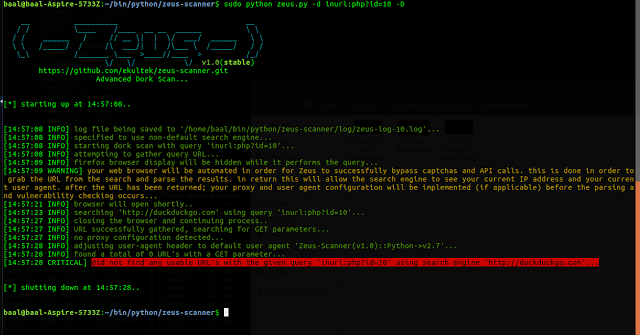 251Information Gathering
251Information GatheringZeus-Scanner – Advanced Reconnaissance Utility
Zeus is an advanced reconnaissance utility designed to make web application reconnaissance simple. Zeus comes complete with a powerful built-in URL parsing...
-
 242Exploitation Tools
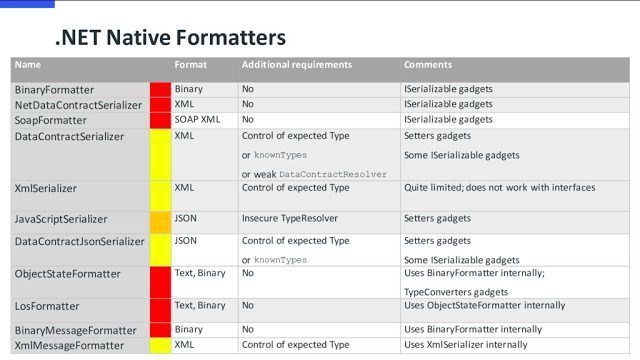
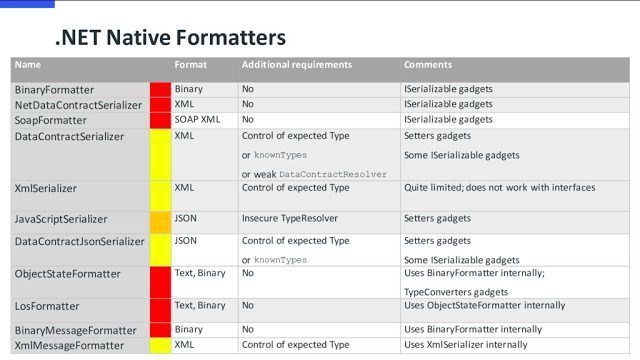
242Exploitation Toolsysoserial.net – Deserialization payload generator for a variety of .NET formatters
A proof-of-concept tool for generating payloads that exploit unsafe .NET object deserialization. Description ysoserial.net is a collection of utilities and property-oriented programming...
-
 274Hacked
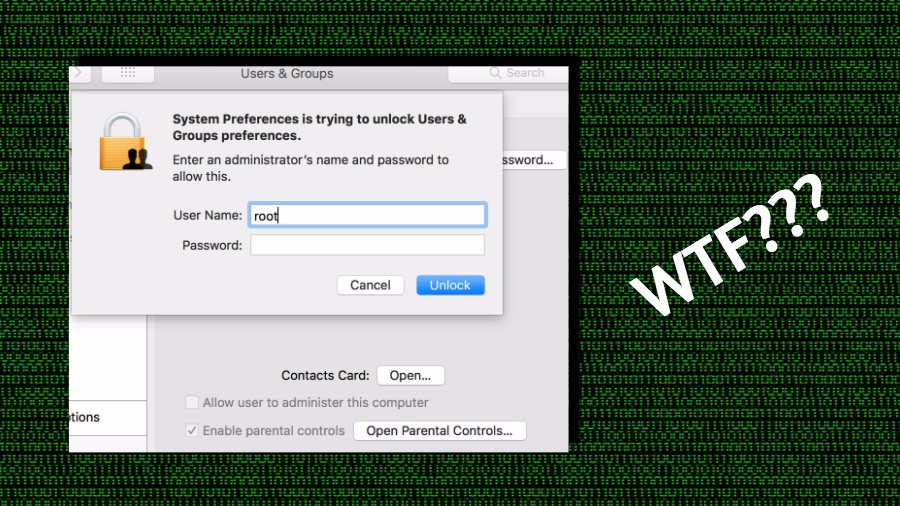
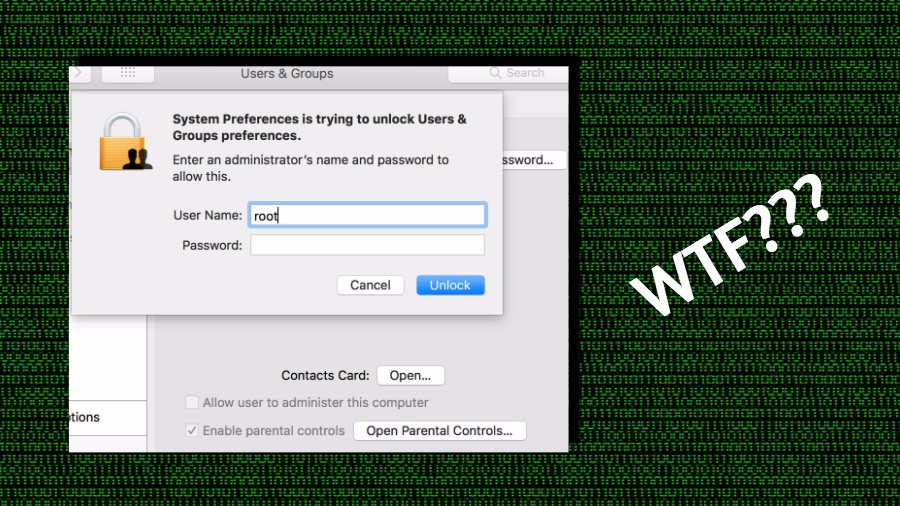
274HackedALERT: Anyone Can Access Your Mac As Root With No Password — Here’s How To Fix
If you’re currently working on a macOS-powered machine, there are good chances that you might be running the latest macOS High Sierra operating...
-

 260Information Gathering
260Information GatheringOpenWPM – Web Privacy Measurement Framework
Web Privacy Measurement is the observation of websites and serves to detect, characterize and quantify privacy-impacting behaviors. Applications of Web Privacy Measurement...
-
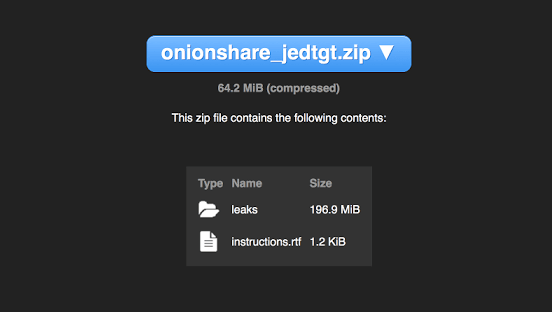
 312Cryptography and Encryption
312Cryptography and EncryptionOnionShare – Securely and anonymously share a file of any size
OnionShare lets you securely and anonymously share files of any size. It works by starting a web server, making it accessible as...
-
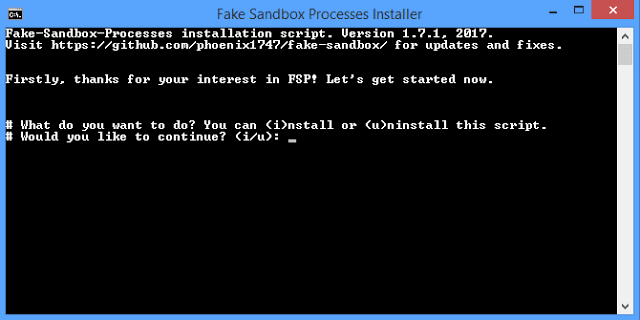
 239Vulnerability Analysis
239Vulnerability AnalysisFake Sandbox Processes (FSP) – Tool to simulate fake processes of analysis sandbox/VM software
This small script will simulate fake processes of analysis, sandbox and/or VM software that some malware will try to avoid. You can...
-
 224Forensics Tools
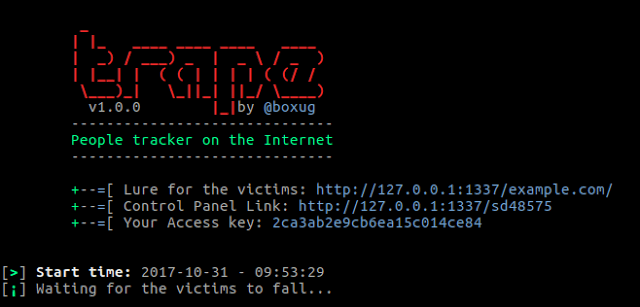
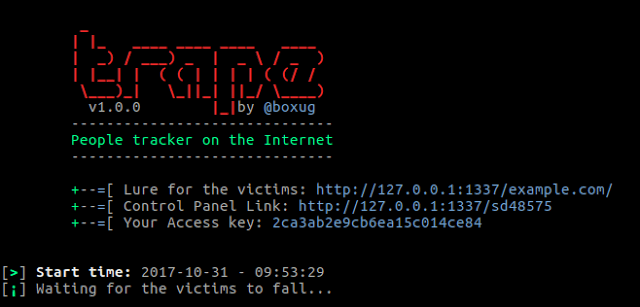
224Forensics ToolsTrape – People tracker on the Internet (The evolution of phishing attacks) OSINT
Trape is a recognition tool that allows you to track people, the information you can get is very detailed. We want to...
-
 178Information Gathering
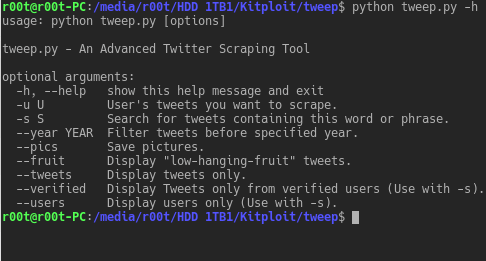
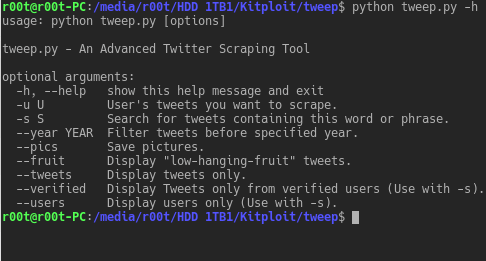
178Information GatheringTweep – An Advanced Twitter Scraping Tool
Tweep is an advanced Twitter scraping tool written in python that allows for scraping Tweets and pictures from Twitter profiles without using...
-
Exploitation Tools
OWASP ZAP 2.6.0 – Penetration Testing Tool for Testing Web Applications
The OWASP Zed Attack Proxy (ZAP) is one of the world’s most popular free security tools and is actively maintained by hundreds...
-

 291Incidents
291IncidentsOSX/Proton spreading again through supply-chain attack
During the last hours, ESET researchers noticed that Eltima, the makers of the Elmedia Player software, have been distributing a version of their...
-
 284Geek
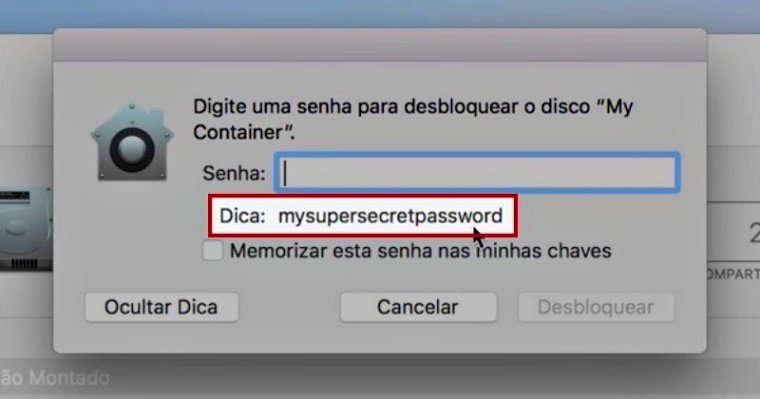
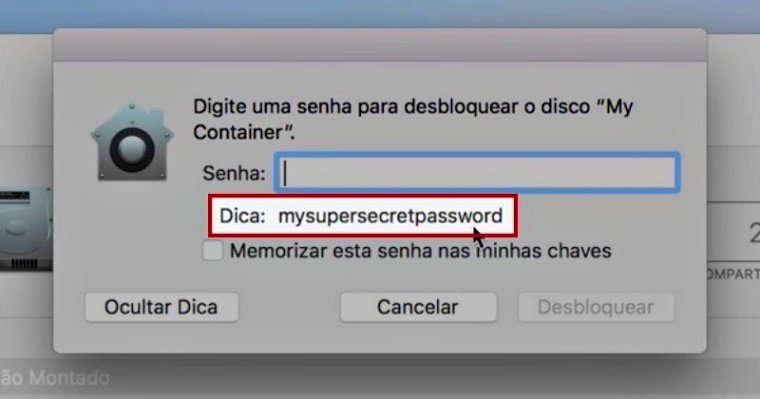
284GeekApple patches bug that showed device password rather than hint
If you have updated your MacOS from the older version to MacOS High Sierra make sure you also apply the new security patch released...
-

 196News
196NewsMillions Of Apple MACs Are Vulnerable To EFI Firmware Attack
EFI Firmware Attack is one of the most popular and critical tips that any security expert strongly suggests to follow to avoid...
-
 151Geek
151GeekLinux Doubles Its Market Share Since 2015, Windows And Mac Adoption Slows Down
We’ve been hearing the phrase “year of the Linux desktop” from times immemorial. The FOSS and Linux community tosses up this idea...
-
 334Data Security
334Data SecurityWikileaks Exposes CIA’ 3 Linux/macOS Malware- Aeris, Achilles, SeaPea
We all know what CIA is capable of but what WikiLeaks has been publishing lately under the Vault 7 leaks series is...
-

 259Cyber Attack
259Cyber AttackBeware! Apple Users,Undetectable Malware Targeting Mac Computers
Yes, even Mac could have viruses that could spy on their users silently. So if you have a Mac and think it...






