All posts tagged "malware"
-

 276Data Security
276Data SecurityInformation security company sued for not detecting malware in 2009
Insurance companies Lexington Insurance and Beazley Insurance are suing an information security firm to recover the insurance rates paid to Heartland...
-
 190News
190NewsMost Of The Lokibot Samples Are The Hijacked Versions Of Original Malware
It turns out that most of the naturally distributed LokiBot malware samples are modified versions of the original sample, a security researcher...
-

 258Hacked
258HackedMalware Attack On Arch Linux AUR Repository; Three Packages Infected So Far
Arch Linux software repository named Arch User Repository (AUR) has been infected by malware. As many as three Arch Linux packages available...
-
 211Hacked
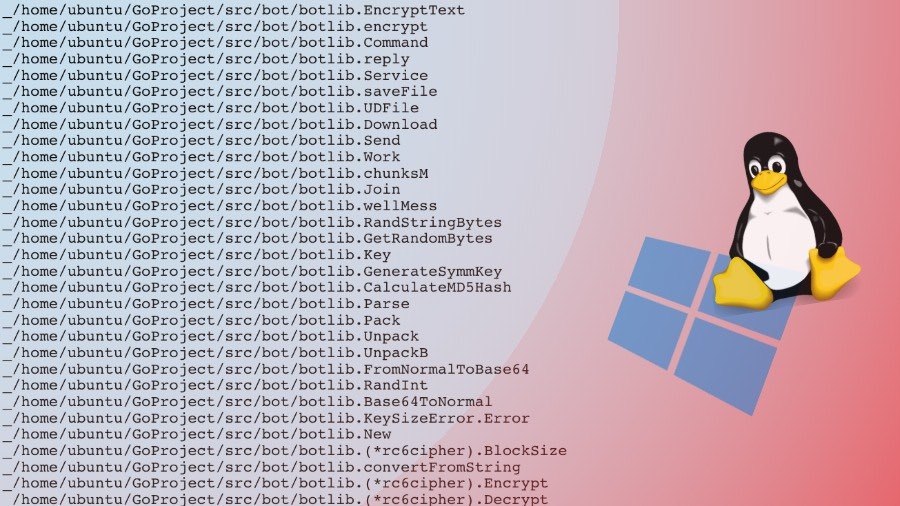
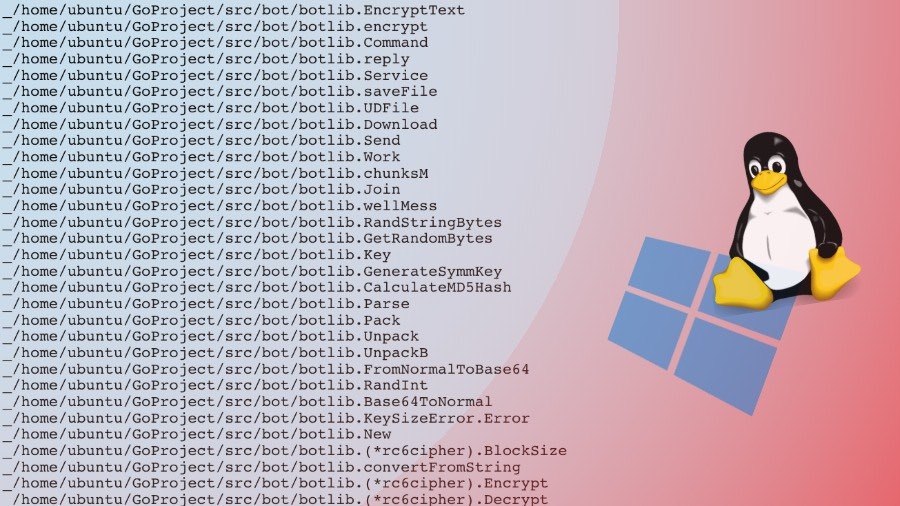
211HackedWellMess: This Go-based Malware Attacks Both Linux And Windows Machines
There’s no doubt that Linux and Mac are more secure operating system choices as opposed to Microsoft Windows. But this doesn’t mean...
-
 227Malware
227MalwareHackers Signed Malware With Stolen Code Signing Certificate From Tech- Companies
A code signing certificate allows an application developer to sign their software before publishing to the web and the end-users can verify...
-

 247Malware
247MalwareOld Malware Gives Criminals Tricky New Choice: Ransomware or Mining
The Rakhni Trojan is now giving bad actors the ability to infect victims either with a ransomware cryptor or a miner. An...
-
 354Malware
354MalwareHackers Delivering Emotet Malware Via Microsoft Office Documents
A new malware campaign that delivers Emotet Malware Via Microsoft Office documents attachments with “Greeting Card” as the document name. Attackers targeted...
-

 427Data Security
427Data SecurityHow a USB could become security risk for your device
A flash drive or USB may provide a capacity as large as 2TB or could have a small space of 256 MB...
-

 214Hacked
214HackedRakhni Trojan Becomes Smart: Now Infecting With Either Ransomware Or Cryptomining
Rakhni Trojan which was first discovered in 2013 has evolved over the course of five years. As an addition to its already...
-

 136News
136NewsFundamentals Of Computing Security
Because the transfer of data used to function through the Sneakernet, personal computing in the 80’s and 90’s was a lot more simple. The slang...
-

 323Malware
323MalwareA virus that decides whether your computer will be attacked with cryptojacking or with ransomware
Pentest specialists discovered a malware piece that infects systems with ransomware cryptocurrency mining programs, depending on equipment specifications and configuration, to decide which...
-

 141News
141NewsPassword Stealing Malware the latest tool for Cybercriminals
Remember last year, Verizon released data breach investigation report that showed 80 percent of the hacking was related to stolen password. The cybercriminals used...
-

 343Data Security
343Data SecurityThe Pirate Bay is silently mining cryptocurrency without user consent
After being offline for over a week, The Pirate Bay is back online with a cryptocurrency mining code. Last year, it was...
-
 182Malware
182MalwareNew Malicious Macro that Hijacks your Windows Desktop Shortcuts and Points to Download Malware
Cybercriminals using a malicious macro that changes the target of Desktop Shortcuts to download malware and when the user clicks on the...
-
 197Malware
197MalwareNew Double Zero-day Exploit Discovered in same PDF file that Affected Adobe Acrobat & Windows 7
A researcher discovered new double Zero-day exploit that affected Adobe Acrobat, Reader and older Windows 7 platforms, Windows Server 2008. This critical Zero-Day...
-
Malware
MACOS Malware Targeting Cryptocurrency Users On Slack and Discord – 100% Undetected Virustotal
Hackers targeting Cryptocurrency users On Slack and Discord chat platforms with MACOS Malware dubbed OSX.Dummy. The malware targeted users in crypto related...
-

 287News
287NewsHow to Stay Vigilant Against Phishing Scams
Phishing attacks have become a common occurrence in the digital age. While most of us already know what these email scams look...
-

 234Malware
234Malware$50 malware allows users to build their own botnets
A new malware was discovered on sale for the amount of 50 dollars in its beta version, but promising the possibility of...
-
 145Malware
145MalwareHacking Group “RANCOR” Identified Using Malware Families LAINTEE and DDKONG
A new Cyber Espionage Group dubbed RANCOR identified targeting South East Asia using new malware families PLAINTEE and DDKONG. The RANCOR group...
-
 202Malware
202MalwareNecurs Botnet Malware Attack Create a FlawedAMMYY Backdoor on Compromised Windows PC
Necurs botnet malware emerging again with new set of futures to create a backdoor on victims machine to steal sensitive data and...
-

 149News
149NewsOrganizations Should Fear These 4 Cybersecurity Risks
For any organization looking to make a successful digital transformation, cybersecurity must be a top priority—hard stop. Damages and data loss related...






