All posts tagged "malware"
-

 170Incidents
170IncidentsJohn McAfee Apparently Tried to Trick Reporters Into Thinking He Hacked WhatsApp
John McAfee, noted liar and one-time creator of anti-virus software, apparently tried to convince reporters that he hacked the encryption used on...
-

 351News
351NewsPornHub Gets Hacked Days After Launching Bug Bounty Program
A teen hacker has taken over PornHub servers and sold the data for $1000 — PornHub claims it’s just a hoax! The famous adult...
-
 163Data Security
163Data SecurityHancitor and Ruckguv Reappear, Updated and With Vawtrak On Deck
Proofpoint researchers have recently observed the re-emergence of two malware downloaders that had largely disappeared for several months. Hancitor (also known as...
-
 166Incidents
166IncidentsCompression tool 7-Zip pwned, pain flows to top security, software tools
Attackers can score user privileges thanks to heap corruption hassle Some of the world’s biggest security and software vendors will be rushing...
-

 299Cyber Crime
299Cyber CrimeUS Congress Dumps Yahoo Mail Over Phishing Attacks
Yahoo mail Hammered by Congress for its Inefficiency in Preventing Phishing Attempts Symantec’s newest threat report claims that email phishing scams have...
-

 199Data Security
199Data SecurityPornhub Bug Bounty Program: Report critical flaws, earn $25,000
The famous adult content website Pornhub has decided to let hackers report security flaws and vulnerability on its computer system and earn...
-

 261Geek
261GeekViking Horde Malware Turns Android Devices into BotNet
Viking Horde malware gains root access of any Android device — It can steal your personal data, conduct DDoS attacks and ad frauds....
-
 248Hacked
248HackedThis Botnet, Called Jaku, Only Targets Scientists, Engineers, And Academics
Short Bytes: Jaku Botnet discriminates while targeting its victims in the wild. It is easier to download from the famous sources like images...
-
 160Data Security
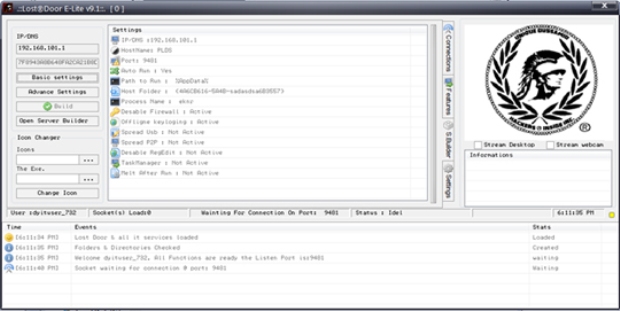
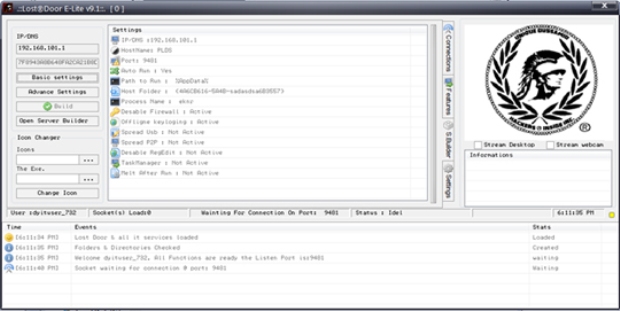
160Data SecurityLost Door RAT: Accessible, Customizable Attack Tool
We recently came across a cyber attack that used a remote access Trojan (RAT) called Lost Door, a tool currently offered on...
-

 232Geek
232GeekWindows ‘God Mode’ Feature Exploited by New Malware to Avoid Identification
Researchers have identified a new malware taking advantage of Windows God Mode and infecting users. Malware in a Window OS is not...
-
 318Geek
318GeekNew Android Malware RuMMS Targeting Users through Smishing
The malware is targeting Russian users but it’s about time when the same tactics will be used by other cyber criminals outside...
-

 132Data Security
132Data SecurityCrooks Deliver Android Malware via Fake Google Chrome Updates
Our research team has recently seen a large amount of activity in our cloud related to an Android infostealer disguised as a...
-
 171Malware
171MalwareMalware Takes Advantage of Windows ‘God Mode’
Microsoft Windows has hidden an Easter Egg since Windows Vista. It allows users to create a specially named folder that acts as...
-

 282Data Security
282Data SecurityEx Tor developer now working for government, responsible for Tor malware
The US government hired an insider to help it with the anonymous browser Tor. Tor is used by millions of people around...
-

 130Data Security
130Data SecurityFormer Tor developer created malware for the FBI to hack Tor users
How does the U.S. government beat Tor, the anonymity software used by millions of people around the world? By hiring someone with...
-

 135Data Security
135Data SecurityRUMMS: THE LATEST FAMILY OF ANDROID MALWARE ATTACKING USERS IN RUSSIA VIA SMS PHISHING
Recently we observed an Android malware family being used to attack users in Russia. The malware samples were mainly distributed through a...
-

 104Data Security
104Data SecurityHacking group “PLATINUM” used Windows’ own patching system against it
Unknown group attacked South East Asian targets, sometimes for years at a time. Microsoft’s Windows Defender Advanced Threat Hunting team works to track down...
-

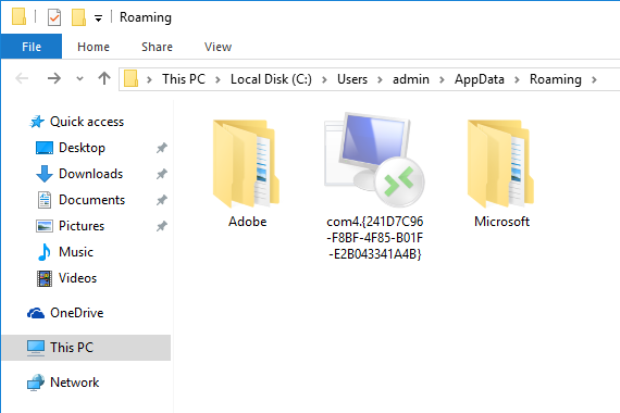
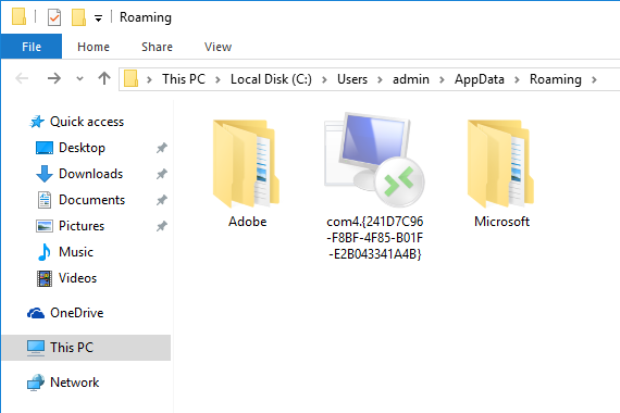
 95Data Security
95Data SecurityYeabests.cc: A fileless infection using WMI to hijack your Browser
Windows comes with a tool called the Windows Management Instrumentation, or WMI, that can be used by system administrators to receive information...
-

 154Data Security
154Data SecurityHackers Who Got Caught by a Typo Were Trying to Take Over the World
The hackers behind a large-scale Bangladesh bank hack went further than simply stealing money. Now it turns out that they created malware...
-

 264Geek
264GeekGoogle marks itself as potentially dangerous website to visit
Has Google Admitted that it is a source of Malware? — Yes indeed! ? Google.com has become a potent source of malware...
-

 276Geek
276GeekSecurity Experts Discover Malware in Facebook’s Staff Server
This bug bounty hunter hacked Facebook but soon realize there’s something fishy going on A hacker taking advantage of Facebook’s bug bounty...






