All posts tagged "malware"
-

 421Malware
421MalwareBest Ways to Remove Trojans, Malware and Viruses From Your Android Phone
According to MalwareBytes’s 2019 State of Malware Report, Trojans and crypto miners are the dominate malware threats of 2019. Android phones may...
-

 246Data Security
246Data SecurityShadowHammer: ASUS software updates exploited to distribute malware
The victims of ShadowHammer malware attack are Windows users. Kaspersky Lab researchers have made a startling new revelation that the world’s leading computer...
-

 275News
275NewsLockerGoga: The Dangerously Changing Face Of Ransomware
Ransomware is a type of malware which encrypts the user’s file until he/she does not hand over a designated sum of ransom. However,...
-

 281Malware
281MalwareInsecure UC Browser ‘Feature’ Lets Hackers Hijack Android Phones Remotely
Beware! If you are using UC Browser on your smartphones, you should consider uninstalling it immediately. Why? Because the China-made UC Browser...
-

 279Malware
279MalwareThe Recent Widely Spreading Lockergoga Ransomware Infection Can Be Stopped by creating a Shortcut (LNKfile)
Lockergoga infection was first spotted in January 2019, the ransomware particularly targets on critical infrastructure. The Lockergoga ransomware encrypts all the files...
-
 326Malware
326MalwareASUS Hacked – Hackers Hijacked ASUS Company servers to Inject the Malware in Millions of Users Computer
Cyber Criminals abused the worlds largest computer maker ASUS computers software update tool by hijacking the company server and install the malware....
-

 377Malware
377MalwareAsus laptops users: Don’t update your software as new update has a backdoor
According to the authors of the book ‘Learn ethical hacking’, a group of hackers has infected hundreds of thousands of Asus computers...
-
 227Malware
227MalwareWarning: ASUS Software Update Server Hacked to Distribute Malware
Remember the CCleaner hack? CCleaner hack was one of the largest supply chain attacks that infected more than 2.3 million users with...
-
 288Malware
288MalwareAZORult Malware Abusing RDP Protocol To Steal the Data by Establish a Remote Desktop Connection
Sophisticated AZORult Malware emerges in a new form with advanced information stealing modules that capable of stealing sensitive information from infected computers....
-

 318Malware
318MalwarePirateMatryoshka: The malware that infects The Pirate Bay users
The Pirate Bay is one of the leading copyright-protected content download platforms. According to an expert from the best ethical hacking Institute...
-

 273Malware
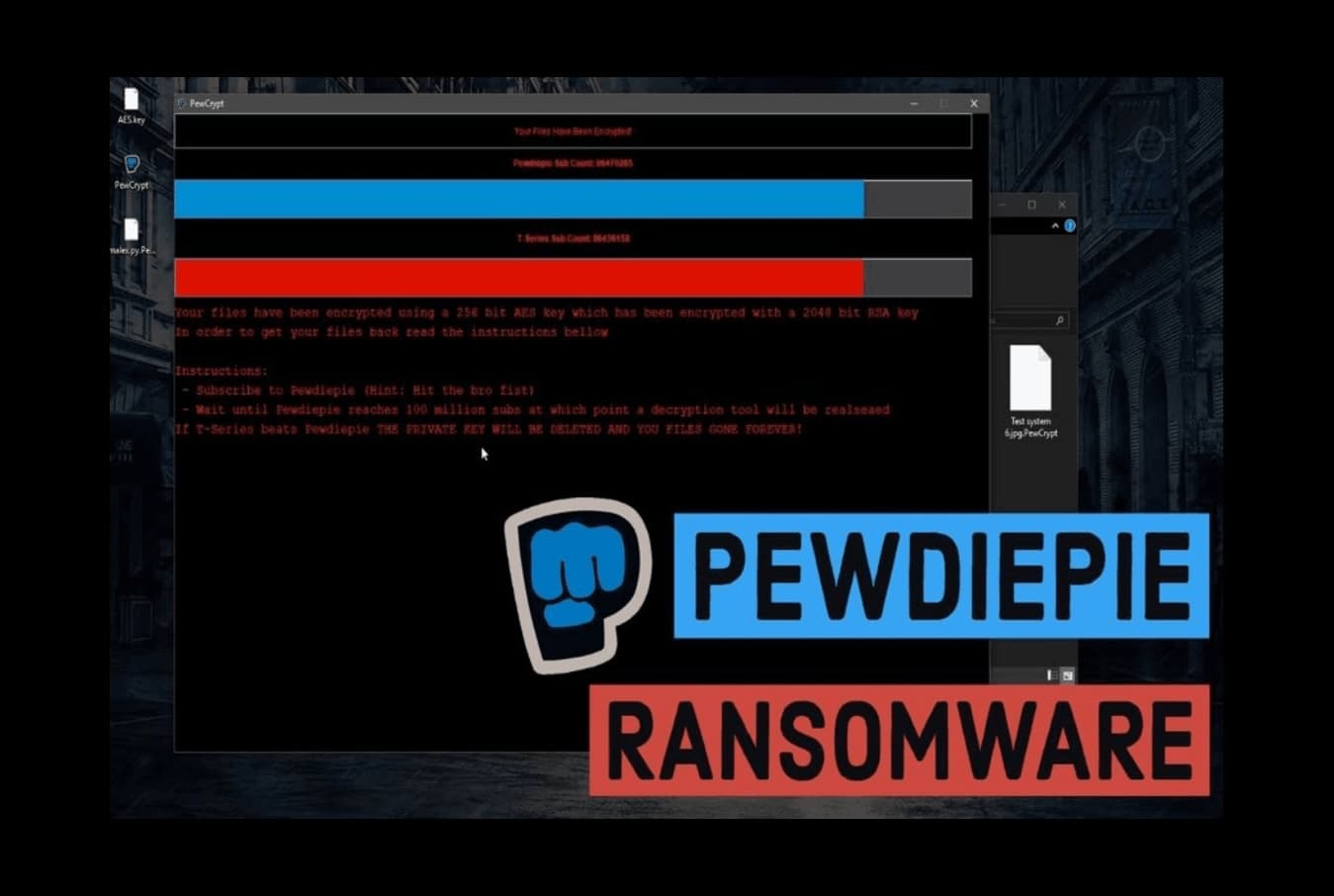
273MalwarePiewDiePie Ransomware: Encrypted files until YouTuber reaches 100 million subscribers
Subscribers to the PewDiePie YouTube channel have decided to take drastic steps to make the famous content creator consolidate as the user...
-
 175Cyber Crime
175Cyber CrimePewDiePie ransomware forcing users to subscribe him on YouTube
T-Series – PewDiePie Battle Takes an Ugly Turn- PewDiePie Fans Launching PewDiePie ransomware to Get Followers. The battle between T-Series and PewDiePie...
-

 1.8KRansomware
1.8KRansomwareTwo Nasty No-Ransom “PewDiePie” Ransomwares, Trouble For Many
Obsession really goes a long way for people to get out of their way to cause trouble for others. As PewDiePie emerges...
-
 317Malware
317MalwareAPT-C-27 Hackers Launching njRAT Backdoor via Weaponized Word Documents to Control the Compromised Device
Goldmouse APT group (APT-C-27) now start exploiting the WinRAR vulnerability (CVE-2018-20250[6]) to hide the njRAT backdoor and targeting users reside in the...
-

 346Cyber Crime
346Cyber CrimeIsraeli fintech firms hit by Cardinal RAT malware
The IT security researchers at Palo Alto Networks’ Unit 42 have discovered a malware that has been targeting Israeli cyberspace especially those dealing...
-
 225Ransomware
225RansomwareExtensive Ransomware Attack Hits Worldwide Operation at Aluminum Manufacturing Gaint Norsk Hydro
Extensive Ransomware Attack forced to shut down operations at, Norsk Hydro, one of the world’s largest aluminum producers. The company suffered production...
-

 2.1KMalware
2.1KMalwareIsraeli Fintech Firms Targeted by Cardinal RAT Malware
According to a blog post from threat research department Unit 42 of cyber security company Palo Alto Networks published on March 19,...
-

 249Ransomware
249RansomwareAlert !! Hackers Launching New JNEC.a Ransomware via WinRAR Exploits – Do not Pay
A brand new JNEC.a ransomware spreading via recently discovered WinRAR vulnerability exploit to compromise windows computer & demand the ransom amount. This...
-
 437Malware
437MalwareNew Mirai Malware Attack on Enterprise Wireless Presentation systems and Supersign TVs
Mirai malware is a powerful strain that compromises a number of Linux devices and uses those devices to launch a massive distributed...
-
 240Malware
240MalwareHackers Bypass Multi-factor Authentication to Hack Office 365 & G Suite Cloud Accounts Using IMAP Protocol
attackers targeting legacy protocols with stolen credential dumps to increase the speed and efficiency of the brute force attacks. Based on Proofpoint...
-

 366Malware
366MalwareHackers using steganography to Drop the Powload Malware & Hide Their Malvertising Traffic
Cyber criminals now approaching a unique way to spread Powload malware with the help of steganography to infect the targeted system. Powload...






