All posts tagged "malware"
-
 189Malware
189MalwareDharma Ransomware Abusing Legitimate Anti-virus Tool to Trick Victims And Infect Their Computers
A new variant of Dharma ransomware masquerading as an ESET AV Remover Installer, to trick the users and to hide its malicious...
-

 229Malware
229MalwareWhat is Deception Technology and why Virtual Reality will be the Ultimate Weapon against Cyberattacks
Development with technologies such as Deception Technology has become either a boon for cyber professionals or hackers, and this can go either...
-

 292News
292NewsPhishing Attacks Mostly Impersonate Microsoft, Netflix & PayPal Accounts
Phishing attacks are evolving in their approach. The latest report from Vade Secure concludes that big consumer software companies like Microsoft, Netflix,...
-

 301Malware
301MalwareMalware affects users of tax payment software Wolters Kluwer
Website security audit specialists reported a malware infection at Wolters Kluwer, a widely used accounting and tax payment software platform; this incident...
-

 531Cyber Events
531Cyber EventsChinese hackers accessed NSA hacking tools before Shadow Brokers leak
Chinese hackers then used NSA’s hacking tools and technology to target American allies. Symantec researchers have discovered that in 2016, Chinese intelligence...
-
 243Malware
243MalwareHackers Launching Qakbot Malware to Steal Login Credentials and Wipe the Bank Accounts
A new wave of Qakbot or Qbot banking malware campaign utilizes the advanced persistent mechanism to steal credentials and draining their bank...
-

 319Ransomware
319RansomwareRansomware Attack on the Cleveland Hopkins International Airport in U.S – Lessons learned
Cleveland Hopkins International Airport In U.S fell victim to a cyber attack on April 29th and officials have confirmed its a ransomware...
-

 180Malware
180MalwareHackers Use GitHub to Host Malware to Attack Victims by Abusing Yandex Owned Legitimate ad Service
Threat actors distribute malware by posting malicious ads that redirect users to the websites that offering malicious downloads disguised as document templates....
-

 262News
262News‘Sodinokibi’ Is A New Ransomware That Exploits Oracle Zero Day Flaw
A couple of weeks back, a zero-day vulnerability was discovered in Oracle WebLogic Servers that can trigger the deserialization of malicious code and allow...
-

 249News
249NewsKodi Hardware Add-on Users, Mostly At Risk With Malware
Kodi used to be a software-only solution that provides a user seeking to share media in a certain geographic area seamless, but...
-

 253Malware
253MalwareHackers Exploiting SS7 Protocol & Inject ATM Malware to Attack Banks and Financial Sectors
The Banking and Financial sectors were hit with a constant stream of cyber attacks when compared to any of the other industries....
-

 241News
241NewsPuma Australia Hit With Credit Card Hack Malware
Sophisticated malware was planted by hackers on Puma Australia’s website, with the intention to steal customer’s credit card information at checkout, a...
-
 358Malware
358MalwareNew way to detect the malware hidden in hardware
While detecting malicious software hidden in hardware parts is an incredibly complex task, cyber forensics course specialists believe that important steps are...
-

 328Data Security
328Data SecurityHackers targeting embassies with trojanized version of TeamViewer
Researchers believe the trojanized version of TeamViewer is being spread by a Russian speaking hacker. The latest report from Check Point reveals...
-
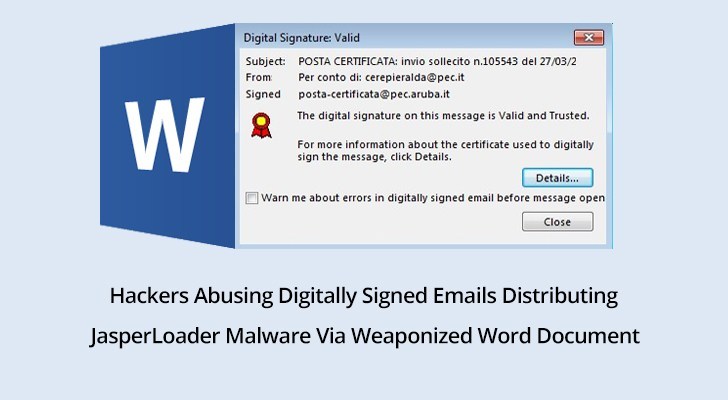
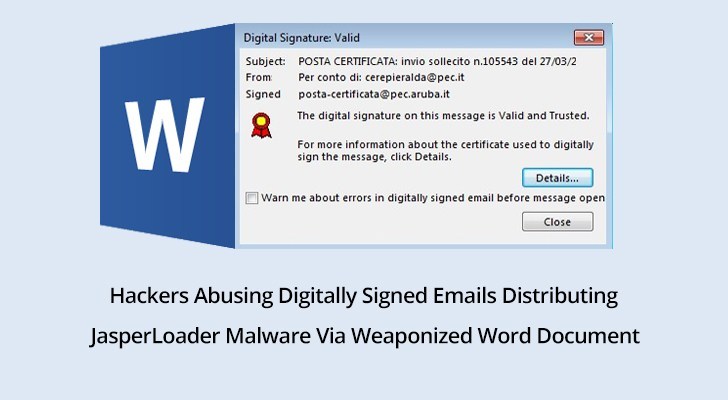 291Malware
291MalwareHackers Abusing Digitally Signed Emails to Launch JasperLoader Malware Via Weaponized Word Document
Security researchers tracked a new malware loader JasperLoader, which has been active for the last few months and distributed through digitally signed...
-

 3.2KRansomware
3.2KRansomwareRansomware In Cleveland Hopkins Airport, Is There A Cover-up?
The world is still suffering from ransomware, even after the growth of its less noisy cousin, the crypto jacking malware. Cleveland Hopkins...
-

 354Data Security
354Data SecurityThousands of firms hit by Beapy malware using NSA hacking tools
EternalBlue and DoublePulsar hacking tools are back in action. Symantec security researchers have identified that cybercriminals are still utilizing the classified exploits/hacking...
-

 293News
293NewsThis Invisible Malware Is A Nightmare For Your Antivirus Software
There is a constant game of cat and mouse between malware writers and security analysts, and it seems that malware writers are...
-

 276Malware
276MalwareEmotet Malware’s New Evasion Technique Lets Hacked Device Used as Proxy command and control (C&C) servers
A new wave of Emotet malware using a special type of evasion technique to fool the security software and hide the POST-infection...
-

 265Malware
265MalwareHackers Abuse Windows Installer MSI to Execute Malicious JavaScript, VBScript, PowerShell Scripts to Drop Malware
Hackers use malicious MSI files that download and execute malicious files that could bypass traditional security solutions. The dropped malware is capable...
-

 373News
373NewsGlobal Threat Statistics for the week of April 5, 2019
Cryptojacking Boosts Botnet Expansion Botnets have been essential tools in distributed denial of service attacks for many years. With the continued success...






