All posts tagged "malware"
-

 160Malware
160MalwareTargeted SamSam Ransomware Attacks Continues to Breaking & Lock 67 Different Organizations Network
Cybercriminals group behind the SamSam Ransomware continuously targeting various organizations network which is located in different countries in order to encrypt the...
-
 220Information Gathering
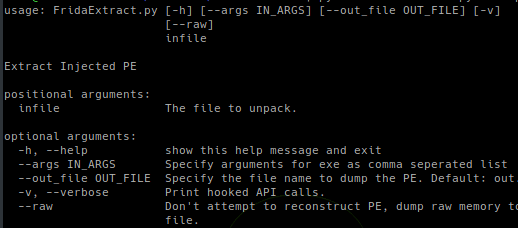
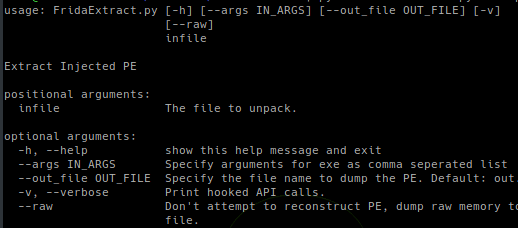
220Information GatheringFrida-Extract – Frida.re Based RunPE (And MapViewOfSection) Extraction Tool
FridaExtract is a Frida.re based RunPE extraction tool. RunPE type injection is a common technique used by malware to hide code within...
-
 211Malware
211MalwareOutlaw Hacking Group Using Command Injection Flow To Attack Organizations Network using Botnet via C&C Server
Outlaw Hacking group uses command injection vulnerability in IoT devices and Linux servers to distribute botnets. The threat actors compromised the FTP...
-

 282Malware
282MalwareGovernment employee who used to watch porn at work alleged guilty of infecting with malware a network
The employee infected a government network, in addition to some devices Cybersecurity and digital forensics researchers found that a US government network...
-
 227Malware
227MalwareHackers Drops New Emotet Malware to Perform Mass Email Exfiltration From Victims Email Client
Emotet Malware re-emerging to perform mass email exfiltration with a new form of infection capabilities to steal sensitive Email data directly from...
-

 271Data Security
271Data SecurityEmployee infects US govt network with malware after visiting 9,000 porn sites
Due to the carelessness of an employee, who apparently was a porn fan, the network of the satellite imaging facility, the U.S....
-
 377Malware
377MalwareEmployee Watched Porn at Work via 9000 Web pages Drops Malware on U.S Government Network
An Employee of US Geological Survey (USGS) has a habit of watching pornography contents during Work hours and visiting the extensive history of porn...
-
 269Malware
269MalwareBeware! Downloader Malware Disguised as Game Apps Found On Google Play with More Than 51,100 Installations
The downloader malware dubbed Android.DownLoader.819.origin malware found on Google play downloaded by more than 51,100 Android users. The downloader malware is capable...
-
 181Malware
181MalwareUnpatched Critical Bug in Microsoft Word Online Video Feature Allow Attacker to Deliver Powerful Malware
An unpatched bug that abusing Microsoft word Online Video future that allow an attacker to deliver malicious files into the victim’s system....
-
 300Malware
300MalwareNew Malware Abusing Two Legitimate Windows Files to Steal Victims Personal Data
Researchers discovered a new malware that abusing two legitimate windows files and use it against compromised victims to steal sensitive information. One...
-

 3.5KDDOS
3.5KDDOSDue to Misconfigured Component: DemonBot Malware Infects Multiple Apache Hadoop Servers
DDoS (Denial of Service Attack) malware have been wreaking havoc to online services on a fairly regular basis these days. Since last...
-

 174Cyber Crime
174Cyber CrimeCyber Criminal’s Effective Human-Scale Methods
As we use publicly accessible services, whether it is an airline, a bank, or a government transaction – we are at the...
-

 240News
240NewsTimpDoor Android malware turning devices into hidden proxies
Android users in North America are the current target of TimpDoor malware. The McAfee Mobile Research team has identified an active phishing campaign...
-

 337DDOS
337DDOSChalubo Botnet Compromise Your Server or IoT Device & Use it for DDOS Attack
Newly Discovered Chalubo Botnet that compromises the internet facing SSH servers on Linux-based systems, IOT Devices and uses it for Distributed denial-of-service...
-

 336Data Security
336Data SecurityRussia launched Triton malware to sabotage Saudi petrochemical plant
A few days ago it was reported that a new malware called GreyEnergy has been targeting high-profile industrial and energy sector with...
-

 283Cryptocurrency
283CryptocurrencyWarning: More iOS Devices Are Infected by Cryptocurrency Mining Malware
In the mobile computing and gadgets world, Android has been the whipping boy when it comes to the issue of security vulnerabilities...
-

 202Data Security
202Data SecurityVesta control panel servers infected with DDoS malware after supply chain attack
An open-source hosting panel software provider, Vesta Control Panel (VestaCP), has admitted that the company became a victim of a supply chain...
-

 352Data Security
352Data SecurityHow to Choose the Most Secure Software for your Business
When it comes to protecting your business, how do you choose the best available and secure software on the market? Security software...
-

 309Malware
309MalwareDarkPulsar – A Shadow Brokers Group’s New Hacking Tool Leak To Open Backdoor & Provide Remote Control
Shadow Brokers Hacking Group’s new administrative module Tool called DarkPulsar Leaks with persistance backdoor to provide remote control to the attackers. There...
-

 209Malware
209MalwareAPT Group Uses Datper Malware To Launch Cyber Attack on Asia Countries by Executing Shell Commands
An advanced persistent threat (APT) actor group known by several different names such as Tick, Redbaldknight and Bronze Butler carried out a...
-

 268Cyber Crime
268Cyber CrimeAuthor of Luminosity RAT Gets 2.5 Years in Federal Prison
Colton Ray Grubbs, 21 from Stanford, Kentucky has been sent to 30 months (2.5 years) in prison for developing and operating the infamous...






