All posts tagged "malware"
-

 262Data Security
262Data SecurityLenovo to pay $7.3m for installing adware in 750,000 laptops
In 2015, Beijing based laptop manufacturer and seemingly reliable technology company Lenovo made headlines that its 750,000 laptops had pre-installed adware called...
-

 277Data Security
277Data SecurityLinux mining software could steal passwords and disable antivirus
The trojan also installs a rootkit and another malware variant that can lead to denial-of-service conditions Perhaps the malware variants that affect...
-
 320Malware
320MalwareUpgraded TrickBot Malware Attack Point-of-Sale Machines & Services to Steal Credit/Debit card Data
Trickbot, a Banking Trojan that involved various cyber attacks especially target the banking networks, now distributing to target the POS services and...
-

 252Cryptocurrency
252CryptocurrencyPowerful Mobile Malware Rotexy Launched over 70,000 Attacks with Banking Trojan & Ransomware Modules
A new Mobile malware family called Rotexy, launched over 7000 attacks in wide within 3 months of the period from August to October...
-

 222Malware
222MalwareBest way to Remove Malware on Mac, Including Other Unwanted Apps
Some Mac apps are so persistent that you can’t use traditional methods to remove them. Even if you do, there will always...
-

 271Incidents
271IncidentsOver 500k Play Store users have installed 13 games that contain malware
The malicious program could be a cryptocurrency miner, or an adware The Android mobile operating system is one of the most widely...
-

 189Cyber Crime
189Cyber CrimeSophos: Cybercrime is a For-Profit Undertaking, Just Like Any Typical “Business”
The real world is a jungle; it is really is still the survival of the fittest even after hundreds of thousands of...
-

 279Data Security
279Data Security13 malware gaming apps on Play Store installed by half a million users
Android is one of the most used mobile operating systems in the world and that makes it a lucrative target for malicious...
-

 376News
376NewsVisionDirect hacked: Hackers infect domains with malicious Google Analytics code
Hackers using Google Adwords & Google Sites to spread malware VisionDirect, one of Europe’s largest online optical retailer that deals with contact...
-

 298News
298News6500 sites down after hackers wipe out database of dark web hosting firm
Daniel’s Hosting, one of the largest hosting service providers on Dark Web has come under a massive cyber attack forcing its website along...
-

 341Malware
341MalwareMost of the ATM’s Around the World Can be Hacked Under 30 Minutes
Recent research revealed that most of the ATM’s around the world are vulnerable to compromise and cash out from the ATM by...
-

 3.5KCryptocurrency
3.5KCryptocurrency4 Effective Ways on How to Prevent Cryptocurrency Mining Infection
Today, there are two tried and tested ways for cybercriminals to effectively earn a lot of income. The first one is what...
-

 346Data Security
346Data SecurityDarkGate: New password stealer & cryptomining malware hits Windows devices
“DarkGate” malware uses Akamai, AWS DNS records and multiple payloads for cryptomining, credential theft and endpoint takeover. A sophisticated malware campaign has...
-

 364Data Security
364Data Security5 Privacy Mistakes that Leave You Vulnerable Online
When news broke about Cambridge Analytica, the Internet went into a frenzy: “How could Facebook do this!” “Facebook should be made accountable!” Besides...
-

 410News
410NewsFlawedAmmy, the Only RAT in CheckPoint’s Global Threat Index 2018 List
2017 was a year of ransomware, primarily the WannaCry malware that made $4 billion in profits from the ransom payments of its...
-
 159Malware
159MalwareCall Recorder App on Google Play with Over 5,000 Installs Contains Hidden Malware Dropper
Malware hidden inside Simple Call Recorder app tricks user in downloading and installing an additional app. Security researcher Lukas Stefanko discovered the...
-

 235News
235NewsWordPress GDPR Compliance plugin hacked to spread backdoor
Update your GDPR Compliance plugin right now. Security researchers have identified a critical vulnerability in the popular WP GDPR Compliance plugin assisting over...
-

 425Malware
425MalwareResearchers reveal the malware used by North Korean hackers to attack ATMs
The Lazarus hackers have been using the FastCash Trojan on obsolete AIX servers to steal tens of millions of dollars The researchers...
-

 2.1KCryptocurrency
2.1KCryptocurrencySouth Korean Hackers Arrested for Infecting Cryto Mining Malware
The South Korean hackers’ were arrested for injecting malware in the computer of over 6,000 people. The Korean National Police Agency Cyber...
-

 231Hacked
231HackedThese Apps On Google Play Store Can Steal Your Bank Details
There are several malicious apps on the Google Play Store that can steal your bank info like login credentials and send fake...
-
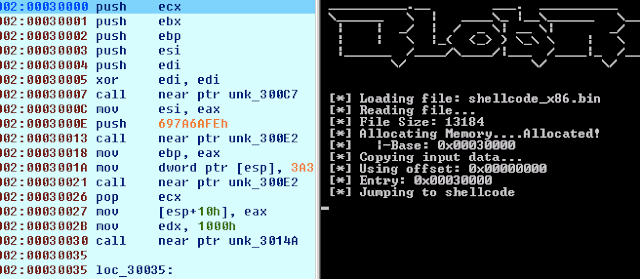
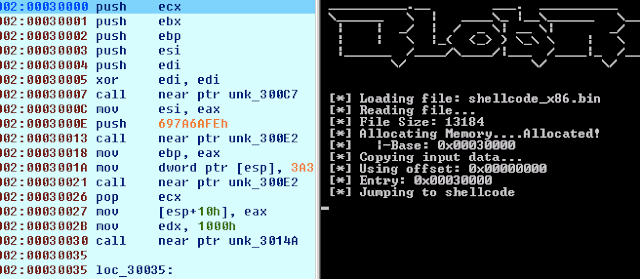 248Reverse Engineering
248Reverse EngineeringBlobRunner – Quickly Debug Shellcode Extracted During Malware Analysis
BlobRunner is a simple tool to quickly debug shellcode extracted during malware analysis. BlobRunner allocates memory for the target file and jumps...






