All posts tagged "Pentesting"
-
 4.2KTutorials
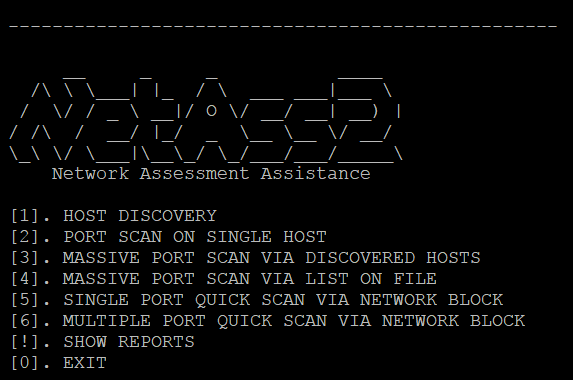
4.2KTutorialsHow to do penetration testing of your network – Step by Step Guide
Network pentesting which helps pentesters/ network administrators to finds vulnerability in a particular system. Network pentesting is done to secure the network....
-
 380Vulnerability Analysis
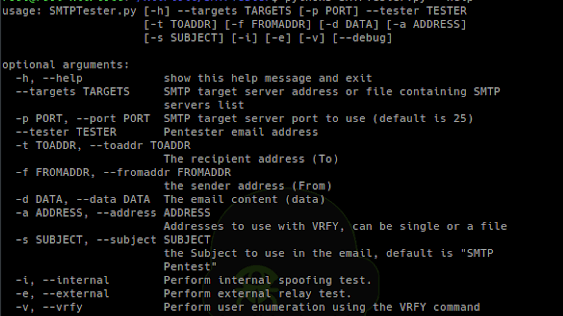
380Vulnerability AnalysisSMTPTester – Tool To Check Common Vulnerabilities In SMTP Servers
SMTPTester is a python3 tool to test SMTP server for 3 common vulnerabilities: Spoofing – The ability to send a mail...
-

 366Incidents
366IncidentsTwo court-hired pentesters accused of intrusion; what would have happened if they hadn’t had permission to perform the tests?
Ethical hacking experts report the arrest of two security specialists hired to evaluate a US court’s IT infrastructure; according to the reports,...
-
 326Pentest
326PentestWireless Penetration Testing Checklist – A Detailed Cheat Sheet
Wireless Penetration testing actively examines the process of Information security Measures which is Placed in Wireless Networks and also analyses the Weakness,...
-

 406Data Security
406Data SecurityLinux Parrot 4.6, new version of the operating system for pentesters
When we require working with a functional operating system for security analysis and ethical hacking, cybersecurity experts consider that Parrot Linux is,...
-
 411Infosec
411InfosecAdvanced ATM Penetration Testing Methods
ATM Penetration testing, Hackers have found different approaches to hack into the ATM machines. Programmers are not restricting themselves to physical assaults,...
-
 328Data Security
328Data SecurityNew version of Kali Linux 2019.1 with Metasploit 5.0 available
The latest version of the operating system has multiple upgrades and updates Network security and ethical hacking specialists from the International Institute...
-
 236Pentest
236PentestPenetration Testing Checklist for Android, windows, Apple & Blackberry Phones
Here we are going to have a look about some of Common & important Penetration Testing Checklist for widely used OS Platforms...
-

 277Infosec
277InfosecPentesting with Killcast Tool to Manipulate Chromecast Devices in Your Network
Recently HackerGiraffe and j3ws3r hijacked more than 70,000 Chromecasts to make people aware about the security risks of devices exposed to internet...
-
 263Vulnerability Analysis
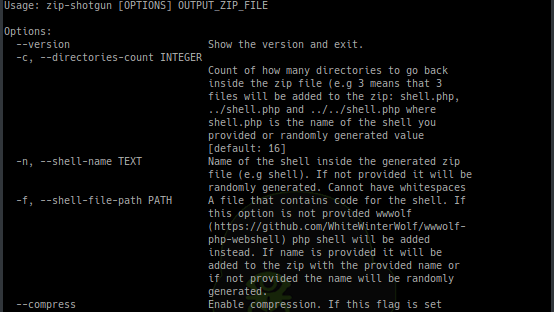
263Vulnerability AnalysisZIP Shotgun – Utility Script To Test Zip File Upload Functionality For Vulnerabilities
Utility script to test zip file upload functionality (and possible extraction of zip files) for vulnerabilities. Idea for this script comes from...
-
 225Information Gathering
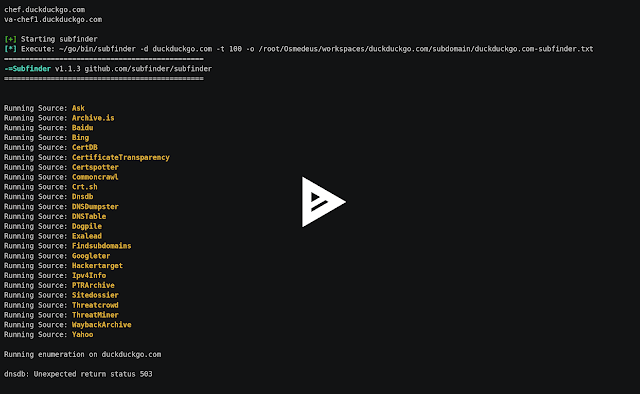
225Information GatheringOsmedeus – Automatic Reconnaisance And Scanning In Pentesting
Automatic Reconnaisance and Scanning in Penetration Testing What is Osmedeus? Osmedeus allow you to doing boring stuff in Pentesting automatically like reconnaissance...
-
 267Wireless Attacks
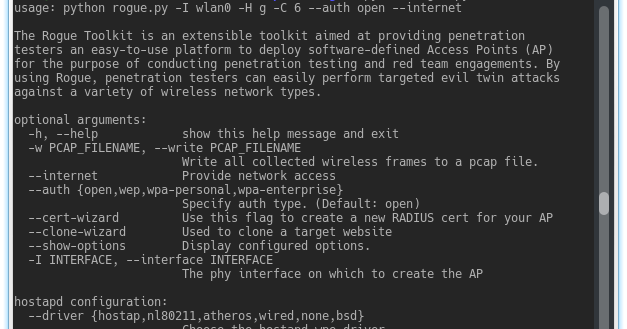
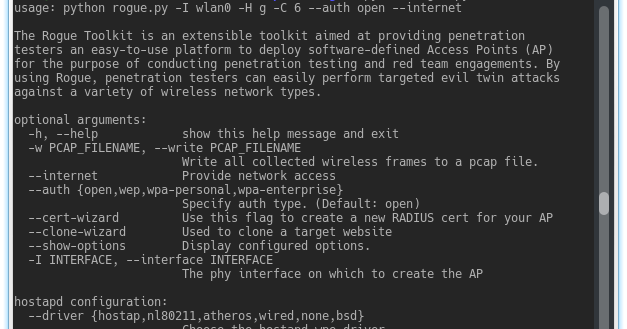
267Wireless AttacksThe Rogue Toolkit – An Extensible Toolkit Aimed At Providing Penetration Testers An Easy-To-Use Platform To Deploy Access Points
The Rogue Toolkit is an extensible toolkit aimed at providing penetration testers an easy-to-use platform to deploy software-defined Access Points (AP)...
-

 344Data Security
344Data SecurityDownload Kali Linux 2018.2 with new security features
Kali Linux 2018.2 is now available for download with new security features and easier Metasploit script access and fixes for the notorious Spectre...
-

 320How To
320How ToParrot Security – Linux Designed For Cloud Pentesting And IoT Security
Security GNU/Linux distribution designed with cloud pentesting and IoT security in mind. Parrot Security includes a full portable laboratory for security and digital...
-
 202Incidents
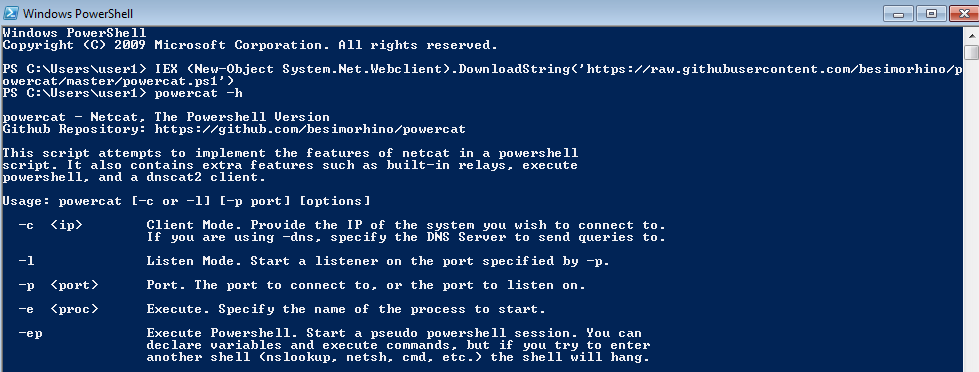
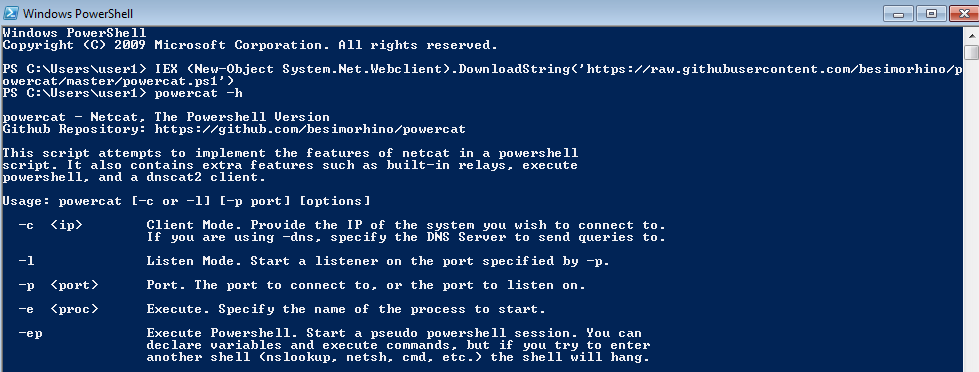
202IncidentsPentesting Windows environments: remote delivery of PowerShell payloads
PowerShell is an amazing post-exploitation tool available to the attacker during engagements in Windows environments. Tools like PowerSploit or PowerShell Empire help...
-

 267How To
267How ToTop 10 Pentesting Tools You Can Use in Windows
NMAP : Nmap is a free tool for network discovery and security auditing. It can be used for host discover, open ports,...






