All posts tagged "phishing attack"
-

 245News
245NewsWipro, the Indian IT Service Giant Attacked By Phishing
IT Services giant, Wipro Ltd which is headquartered in India has become the latest victim of spear phishing. According to the initial...
-

 274News
274NewsElements Of A Well Researched Phishing Email Attempt
Phishers for decades have honed their skills of persuasion, that is why the art of fooling people through an Internet-messaging method is...
-

 2.7KMalware
2.7KMalwareBeware! Even Good Domains Also Carries Malicious URLs
According to an article on helpnetsecurity.com, it reads that nearly 40 percent of good domains carried malicious URLs. So now the question...
-
 338Hacked
338HackedPorn-Lovers Got “Phished” 10 Times More In 2018: Report
Adult websites have been prone to various malware activities and cyber threats, and a new research report by Kaspersky Lab further sheds...
-

 316Malware
316MalwareHackers Launching New Muncy Malware as .EXE File Worldwide via DHL Phishing Campaign
Cyber Criminals now distributing new dubbed Muncy malware as a EXE file format via DHL phishing campaigns to target the users around...
-

 260News
260NewsKent County Community Mental Health Hit By Phishing Attack
Since late October of 2018, Kent County Community Mental Health Authority is being attacked by a massive number of phishing messages. Their...
-
 364Malware
364MalwareCyber Attack Prevention Checklist to Keep Your Business Safe & Secure From Hackers
Cyber Security manages business risk during the full cycle(monitor, assess, advise, re-mediate). It fights against the cybercrime: detection of attacks and fraud...
-

 342Cyber Crime
342Cyber CrimeBusinesses Should Be Aware of Growing Cyber Attacks
In the coming days, it is estimated that businesses and their owners are likely to be targeted by cybercriminals. There is a strong...
-

 2.9KCryptocurrency
2.9KCryptocurrencyNorth Korean Hackers Stole $571 Million Worth of CryptoCoins in Less Than 24 Months
Cryptocurrency is a hot commodity these days that facilitate online transactions without any regulation or control from any government entity, banking facilities,...
-

 471Leaks
471LeaksTwo-Factor Authentication Controversy Facing Facebook, User Mobile Numbers Used for Ads
Two-factor authentication has been a near silver-bullet that prevents phishing attacks and online account thefts. It is very effective, as it provides...
-

 280News
280NewsThe Common Factors in Phishing
Nowadays, the Internet plays a significant role in online commerce and business activities. However, the weak security awareness of users on the...
-

 178News
178NewsOptus Email Scam Target Customers with Fake Late Payment Penalties
Phishing emails are an everyday occurrence, as they are effective in taking advantage of people’s easy propensity to trust corporate logo-bearing messages....
-

 174News
174NewsTech Giant Google Now Turns To Physical Locks For Security
As the EU slaps Google with a $5 billion fine resulting from an Android antitrust case, the search giant is now set...
-

 230News
230NewsHeighten End-User’s Responsibility with Fighting Phishing
Antimalware companies have made many innovations for many decades in order to keep individuals and enterprises secure from cyber risks. However, human...
-

 334Phishing
334PhishingHackers can Bypass Two-Factor Authentication with Phishing Attack
Two-factor authentication is an additional layer of security on top of the username and password. It makes harder for attackers to gain...
-
 307Phishing
307PhishingActive Business Phishing Campaign Targeting Fortune 500 Companies to Steal Financial Assets
Hackers involved in Business Phishing Campaign using well crafted social engineering methods to harvest login credentials and to steal money. The attack...
-

 214Phishing
214PhishingPhishing Campaign Targeting Your Netflix Account ask for Login Details, Credit card and Photo ID
Phishing is one of the most common problems for Internet Users, hackers find a new innovative method to create believable URL’s to...
-

 267Phishing
267PhishingBeware !! LinkedIn User Credentials Stealing via Sophisticated Phishing Attack
Nowadays Linkedin is suffering by many Social Engineering attack that is used to harvesting the user Credentials and Linkedin is widely used...
-

 212Cyber Crime
212Cyber CrimeNCSC Intensifies Cybersecurity Across UK Public Sector
The National Cyber Security Centre (NCSC), UK has introduced four ‘Active Cyber Defence’ (ACD) programmes aimed at improving basic cyber security measures...
-
 628How To
628How ToHow To Hack Facebook ID Using Phishing Attack 2019
In my previous post, I explain the easy method to hack facebook, WhatsApp, Instagram, etc. So you need to read my previous...
-
 243Hacked
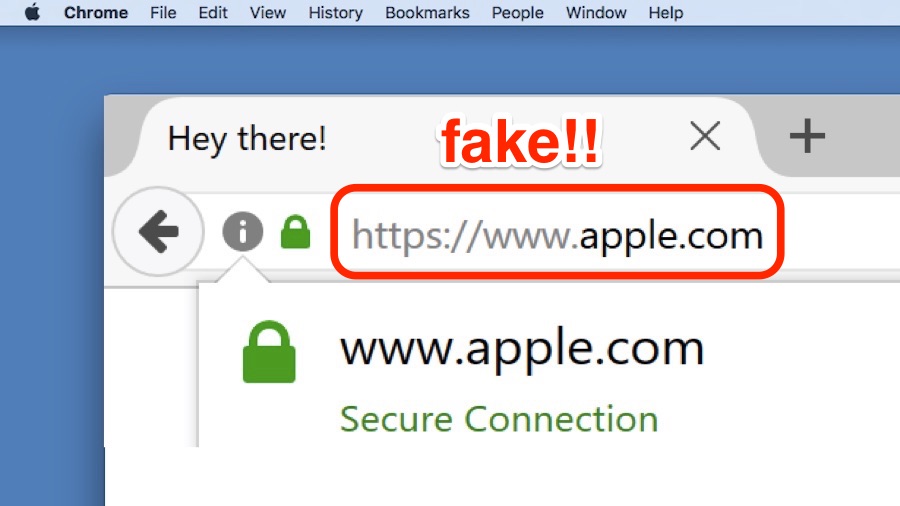
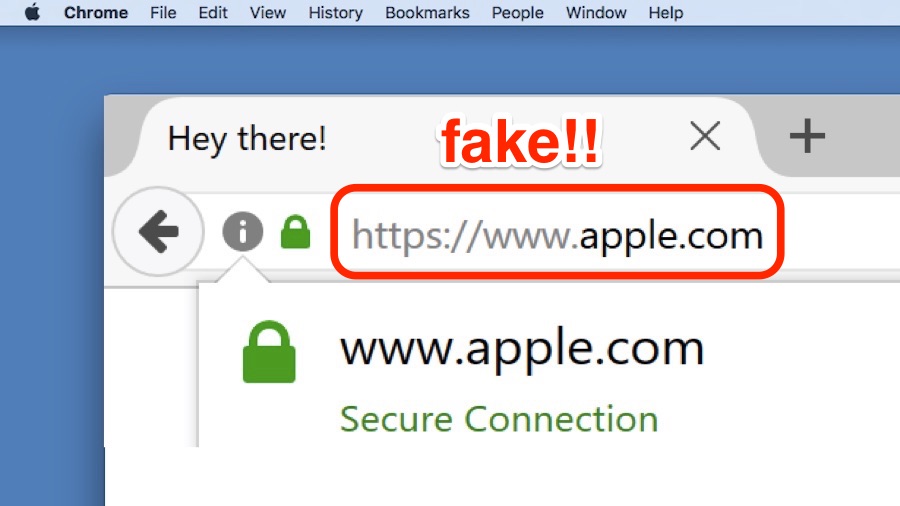
243HackedThis Scary Phishing Attack Is Impossible To Detect — Here’s How It Affects Your Browsers
Short Bytes: A Chinese security researcher has demonstrated a scary phishing attack that’s virtually impossible to detect in web browsers like Chrome,...






