All posts tagged "phishing"
-

 2.7KCyber Crime
2.7KCyber Crime5 Personal Cyber Security Tips
Cyber attacks are evolving, thanks to cybercriminals who are equipping themselves with new skills and capabilities – In this scenario, from business...
-

 2.1KData Security
2.1KData SecurityMicrosoft warns of credential phishing attack abusing open redirect links
So far, the ongoing phishing attack has utilized more than 350 unique domains to target Microsoft Office 365 users. Microsoft has warned about...
-

 4.9KData Security
4.9KData SecurityNew WeTransfer phishing attack spoofs file-sharing to steal credential
The phishing email claims that WeTransfer has shared two files with the victim, and there’s a link to view them. According to...
-

 3.3KCyber Crime
3.3KCyber CrimeiCloud phishing scam – Man stole private photos of 620,000 women
LA County resident booked in iCloud phishing scam pretended to be an Apple representative. A Los Angeles County man identified as Hao...
-

 4.3KCyber Crime
4.3KCyber CrimeThreat actors using CAPTCHA to evade phishing, malware detection
According to researchers, cybercriminals are abusing legitimate challenge and response services like Google’s reCAPTCHA or deploying customized fake CAPTCHA-like validation. Palo Alto...
-

 864Cyber Crime
864Cyber CrimeSpear phishing attacks underline how much dangerous phishing has gotten
Phishing is getting smarter. A type of social engineering attack in which the attacker uses fraudulent messages that are designed to fool...
-
 5.2KCyber Crime
5.2KCyber CrimeNew LinkedIn phishing campaign found using Google Forms
In the latest LinkedIn phishing scam, the sender’s email address appears to be from Paul University which is based in Nigeria. Phishing...
-

 2.7KCyber Crime
2.7KCyber CrimeEmail claiming Kaseya patch drops Cobalt Strike malware
The email contains varying subject lines revolving around “order shipping” with messages instructing users to install the patch released by Microsoft. A...
-

 4.9KCyber Attack
4.9KCyber AttackSolarWinds Hackers Breach Microsoft Customer Support to Target its Customers
In yet another sign that the Russian hackers who breached SolarWinds network monitoring software to compromise a slew of entities never really...
-

 720Cyber Crime
720Cyber Crime4 Ways For Employees To Distinguish Phishing Attacks
Many movies and other media may have a bit of a warped idea of what hackers do, exactly. But one show that...
-

 4.8KHow To
4.8KHow ToHow gamers should secure their accounts from cyber attacks
Gaming is a multi-billion industry that is why it is a lucrative target for cybercriminals as well. Gaming giants on the other...
-
 4.4KData Security
4.4KData SecuritySolarWinds hackers using NativeZone backdoor against 24 countries
Microsoft has disclosed that the SolarWinds hackers or SolarWinds supply chain attack-fame threat actors are back in action. This time, they are targeting...
-

 931Data Security
931Data SecurityEmployee training is key to keeping your enterprise safe
No matter how strong a company’s defense systems are, it’s critical that they include comprehensive employee training for all employees. Imagine that...
-

 3.8KCyber Crime
3.8KCyber CrimeFeds seize fraud domain claiming to provide COVID-19 vaccine
The website was scamming users in the name of providing the COVID-19 vaccine but actually collecting their personal data for malicious purposes....
-

 4.4KCyber Crime
4.4KCyber CrimeWhatsApp Pink is malware spreading through group chats
If installed; the fake and malicious WhatsApp pink app takes full control of a targeted device. An unusual baiting technique has appeared...
-
 4.9KGeek
4.9KGeekNew Android malware poses as “System Update” to steal your data
The malware is also capable of controlling the device’s front and back camera to take photos periodically. The IT security researchers at...
-

 2.4KData Security
2.4KData SecurityToxicEye RAT hits Telegram app to spy, steal user data
ToxicEye is a new remote access Trojan (RAT) malware that has been used for more than 130 attacks over the past three...
-

 814Phishing
814PhishingSpear Phishing is the Next Big Challenge for CISOs
Phishing, which started off as Nigerian Prince scams in the 1990s, has become a common attack vector ever since. As though phishing...
-
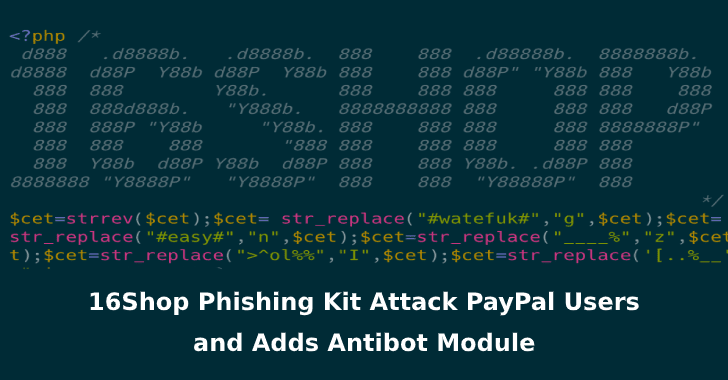
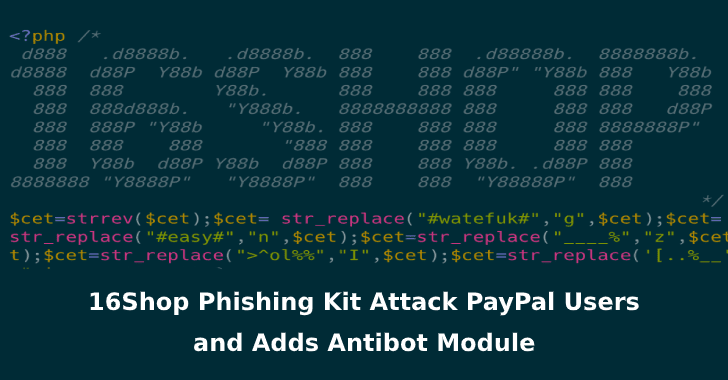 5.5KPhishing
5.5KPhishing16Shop – Malware-as-a-service Phishing Toolkit Attack PayPal Users With Anti-Detection Techniques
A prolific phishing kit distribution network dubbed “16Shop” believed to be active since 2018 and developed by a hacking group called the...
-

 4.3KData Security
4.3KData SecurityHackers now use web skimmers to steal credit card data
People often make a great effort to protect their credit/debit card details against fraudulent transactions. This has been further helped by banks...
-

 3.9KData Security
3.9KData SecurityCyborg ransomware posing as Windows update hits PCs
If you’ve updated your Windows today like me, this article may just end up scaring you a bit. In the latest, it...






