All posts tagged "Security"
-

 338Data Security
338Data SecurityFlaw in NSA’s GHIDRA leads to remote code execution attacks
GHIDRA is NSA’s reverse engineering tool released earlier this month. Earlier this month, Hackread.com posted about the National Security Agency’s (NSA) publicly releasing...
-

 242News
242NewsMicrosoft Office Is The Most Exploited Software By Cybercriminals
A list of the top 10 most exploited vulnerabilities in 2018 has revealed that Microsoft Office was the favorite victim of cybercriminals. Microsoft...
-
 243News
243NewsMySpace loses 12 years worth of photos, songs & video files
MySpace says it happened during a server migration project. Last time the once prominent social network website MySpace made headlines in 2016 after it...
-
 372Data Security
372Data SecurityHackers are using 19-year-old WinRAR bug to install nasty malware
By using the bug, hackers are desperately dropping persistent malware through generic trojan on systems using the old version of WinRar. McAfee security firm’s...
-

 398News
398NewsPakistani Govt’s passport application tracking site hacked with Scanbox framework
Hackers are after anyone seeking Pakistani passport while there is no response from the website’s administrator. Researchers at information security firm Trustwave...
-

 196Data Security
196Data Security“BreedReady” database of 1.8m Chinese women surfaced online
Another day, another data breach; this time, Victor Gevers, a Dutch security researcher from GDI Foundation has discovered a publically exposed database...
-

 330Data Security
330Data SecurityMore than Half of Android apps ask for dangerous permissions. Is yours among?
It wasn’t very long ago that I revealed that most free VPN services are provided as a front for the big corporations...
-
 448Data Security
448Data SecurityVerifications.io breach: Database with 2 billion records leaked
Verifications.io breach is one of the largest data breaches but the good news is that it does not involve passwords. Another day,...
-

 235Data Security
235Data SecurityVulnerable smart alarms allowed hackers to track & turn off car engine
By gaining access to the vehicles, hackers can not only locate them but also open their doors and even turn off the...
-
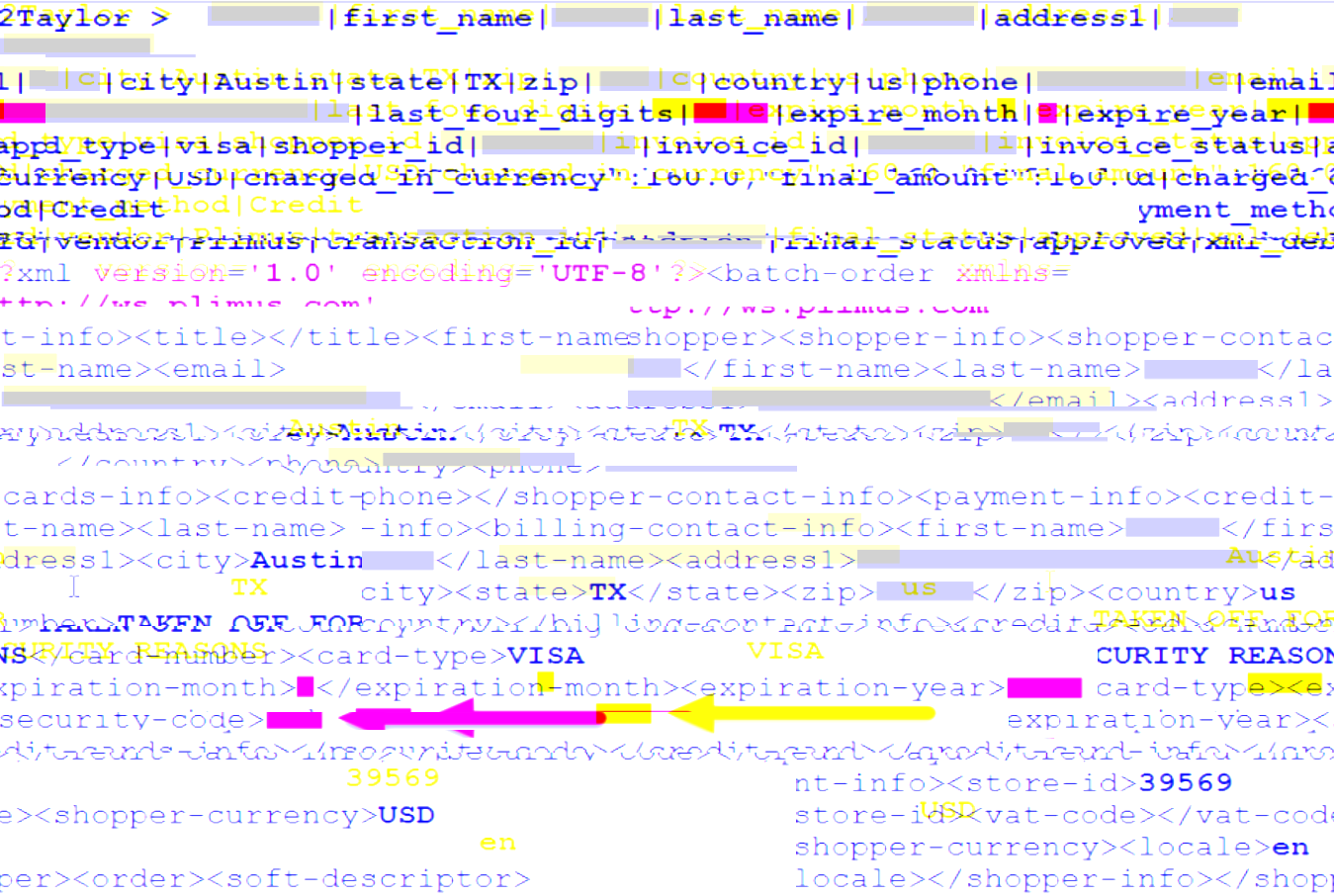
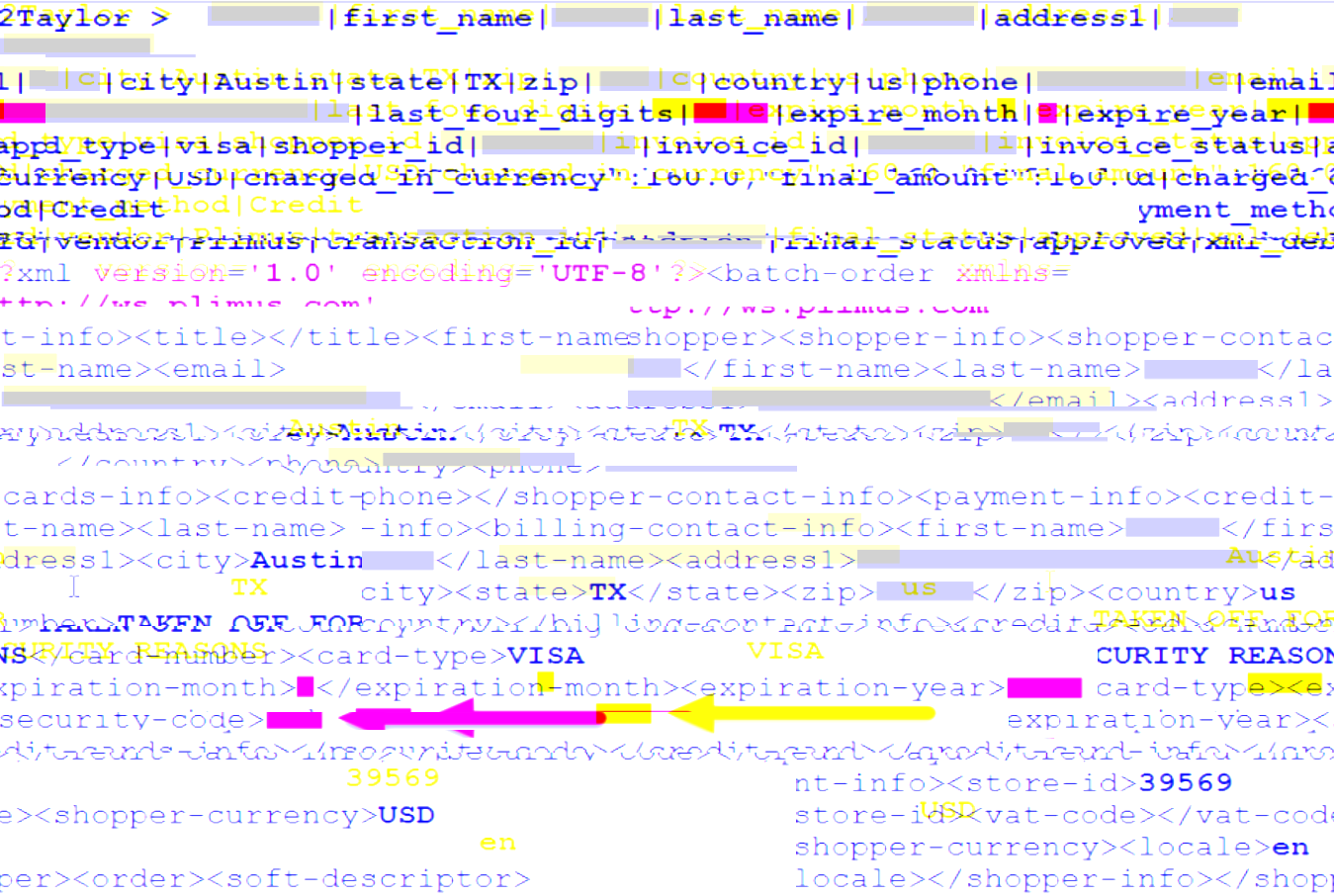
 313Data Security
313Data SecurityNew backdoor malware hits Slack and Github platforms
The cybersecurity researchers at Trend Micro have discovered A new malware strain tapped into GitHub posts and Slack channels. Dubbed Slub by researchers; the malware works by exploiting...
-

 269Hacked
269HackedThe Pirate Bay Users Targeted By Russian Doll ‘PirateMatryoshka’ Malware
While P2P file sharing isn’t illegal, torrent websites turn out to be the biggest sources to download copyright-protected media. Due to a plethora...
-

 332Data Security
332Data SecurityThe Pirate Bay spreading malware PirateMatryoshka via reputed seeders
Cybercriminals often use torrent services to distribute malicious code since users who look for illegal content usually disable their privacy and security...
-

 420Data Security
420Data SecurityWordPress security: Steps to assess an employee before granting admin access to WordPress
Are you planning to hand over admin access of your WordPress site to someone else? You certainly need to take some steps...
-

 223Data Security
223Data SecurityDark web hacker selling admin access to a Chinese railway company
The IT security researchers at Sixgill‘s threat intelligence team have identified an “experienced threat actor” on the dark web selling access to...
-

 312Data Security
312Data SecurityThe Pirate Bay’s preferred cryptominer Coinhive shutting down next week
The Pirate Bay was caught twice secretly mining Monero cryptocurrency using Javascript powered by Coinhive. Popular in-browser crypto-mining service will be shutting down...
-

 247News
247NewsImplementing Operational Security, The Process and Best Practices
procedural security is what we call operational security (OPSEC), it is kind of risk management process that encourages admin to monitor operations...
-

 211Data Security
211Data SecurityDow Jones’ screening watchlist data exposed online
A database hosted on Amazon Web Services (AWS) and owned by Dow Jones has accidentally been exposed putting approx. 2.4 million corporate...
-

 349Data Security
349Data SecurityCellular networks flaws expose 4G & 5G devices to IMSI capturing attacks
A team of researchers has disclosed their findings at the NDSS (Network and Distributed System Security) symposium 2019 held in San Diego,...
-

 187Infosec
187InfosecHow Does Worlds Highly Secured Google Network Works ? Google’s Effort & Dedication
Google always Maintain the Extremely strong Cyber Security Culture for Data Security, Network Security, Cloud Security and Physical security. Google’s this extreme...
-
 417Data Security
417Data SecurityCheck your VPN DNS test tool legitimacy: Is it “legit” or deceptive
Does your VPN leaks DNS data? Does the DNS testing tool you’re using shows actual or sponsored results for affiliate marketing? Virtual...
-

 1.3KData Security
1.3KData SecurityMemory and Swap File Protection: Reforms Password Managers Need To Implement
If you are using passwords in multiple Web services etc., if that one-and-only password gets leaked, your entire Internet identity and access...






