All posts tagged "Security"
-
 300Data Security
300Data SecurityWarning as small planes found vulnerable to hacking
The IT security researchers at Rapid7 have reported a critical vulnerability in the modern flight systems of small planes allowing hackers with...
-

 382Data Security
382Data SecurityNew Android ransomware uses pornographic posts to infect devices
The new Android ransomware was initially being spread through Reddit and XDA-Developers’ forum. A new type of Android ransomware attack has been...
-

 353How To
353How ToImprove security of your Linux OS with simple steps
It’s normal to hear Linux users brag about security and sometimes tease Windows users. Some Linux users have this perception that security...
-

 362How To
362How ToWhat makes a secure & successful website: A Guide
There’s nothing more frustrating – especially for small and fledgling businesses – than making a huge investment in a sleek, modern website,...
-
 232News
232NewsEvilGnome Is A Linux Spyware That Records Audio And Steals Your Files
Malware is a common thing in the Windows and Android world, but Linux malware is rare owing to the core architecture of...
-
 325News
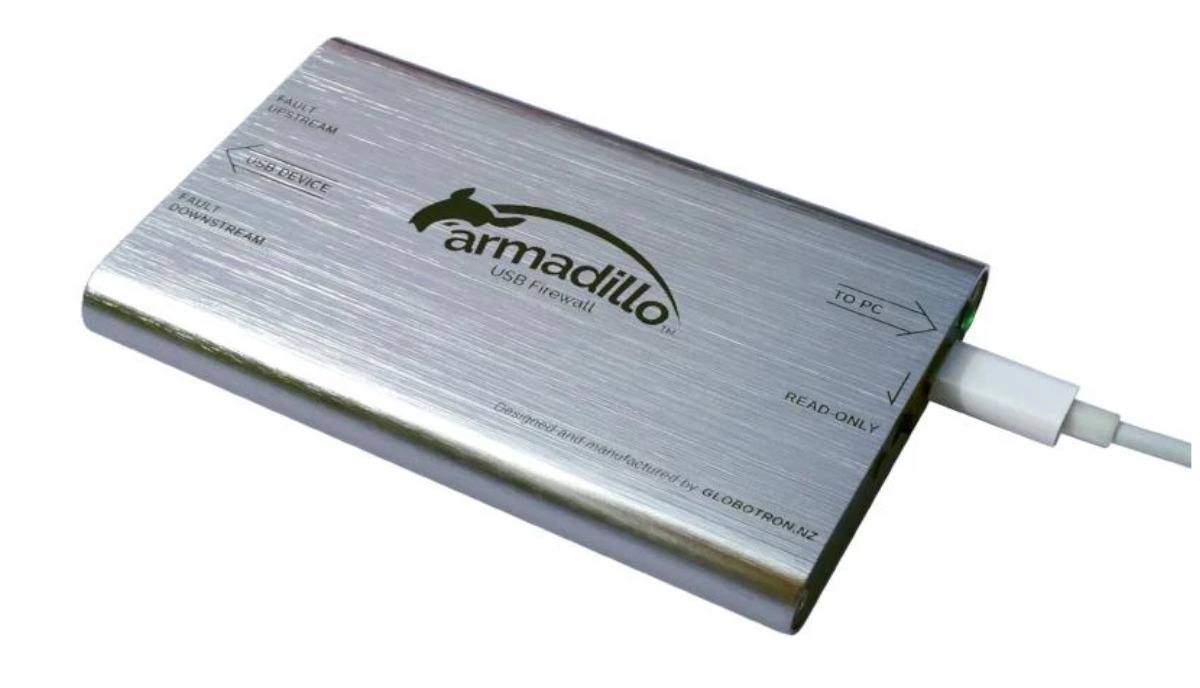
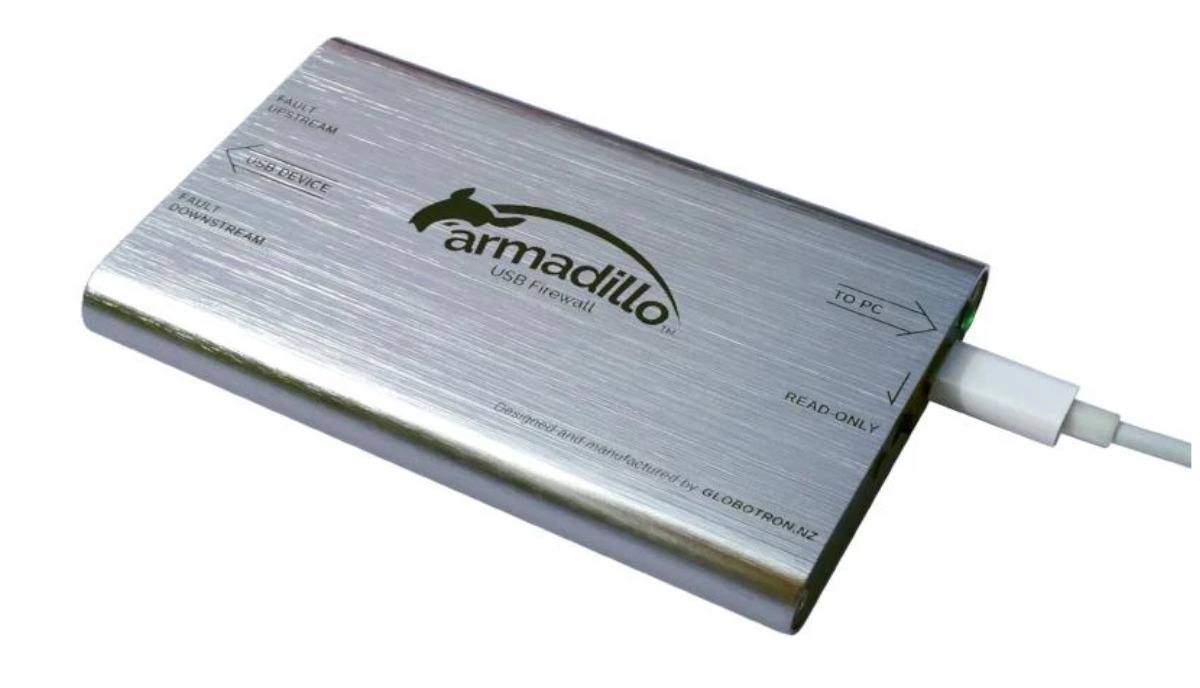
325NewsArmadillo Is An Open-Source “USB Firewall” Device To Protect You Against USB Attacks
Exchanging data using USB devices is something that we do on a daily basis. But how often do you think that the...
-

 394Geek
394GeekMeet IRpair & Phantom; powerful anti-facial recognition glasses
IRpair and Phantom are the first-ever collections of anti-facial recognition glasses and sunglasses designed to block facial recognition, eye tracking & infrared...
-

 328Data Security
328Data SecurityHackers used Samsung website to access Sprint’s customer data
Sprint Corporation, an American telecommunications company has announced that it has suffered a data breach after unknown hackers accessed customer accounts credentials...
-

 355Geek
355GeekHacker gets $30,000 for reporting hack Instagram account flaw
The flaw allowed anyone with knowledge of brute force attack to hack Instagram accounts without raising any suspicion. How to hack Instagram...
-

 449Geek
449GeekAgent Smith Android malware has infected 25 million devices so far
Agent Smith malware exploits Android vulnerabilities to target unsuspected users for credential stealing. The IT security researchers at CheckPoint have discovered a...
-

 313Infosec
313InfosecA Perfect Way to Start and Strengthen Your Cyber Security Career
Breaking into a cybersecurity career is no different than any other career path or profession. In fact, in some ways, we’d even...
-

 365Geek
365GeekVulnerability in Zoom video conference app lets Mac’s camera hijacking
The vulnerability in the Zoom video conference app lets attackers hijack Mac’s camera by merely using malicious websites. The Zoom video conference...
-

 359Cyber Crime
359Cyber CrimeMan who carried out DDoS attacks against PSN & Xbox jailed
The cybercriminal was also involved in several other cybercrimes including swatting and deleting databases of targeted websites. Austin Thompson, a DDoS attacker...
-
Data Breach
10 Best Hacker-Friendly Search Engines of 2019
The search engines allow users to find any content via the world wide web. It helps to find any information easily and...
-

 377Cyber Crime
377Cyber CrimeThe Logic of a Classic Advanced Persistent Threat Attack
Story of an Advanced Persistent Threat attack against a large corporation that started with a series of blank emails. Advanced persistent threats...
-
 476Data Security
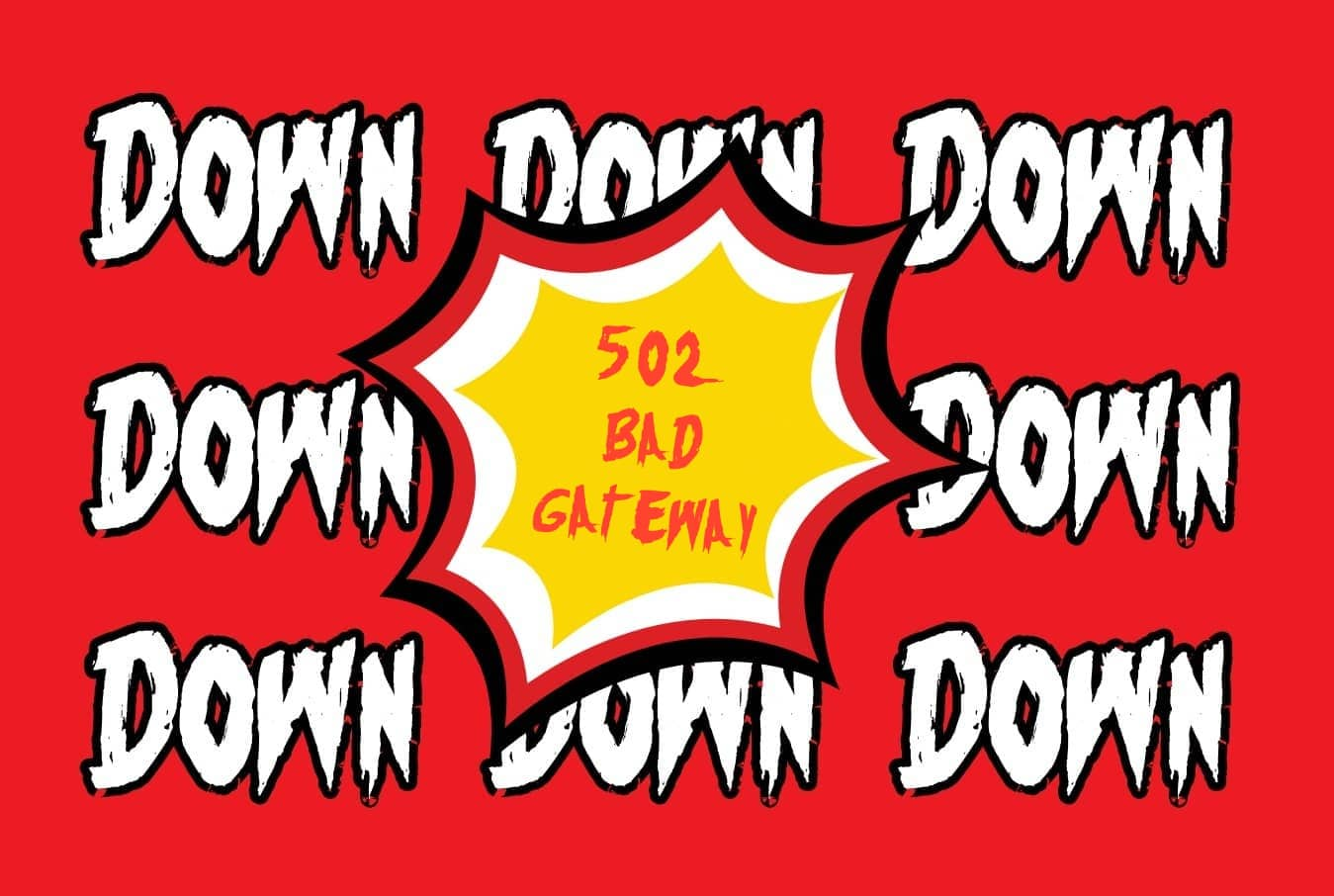
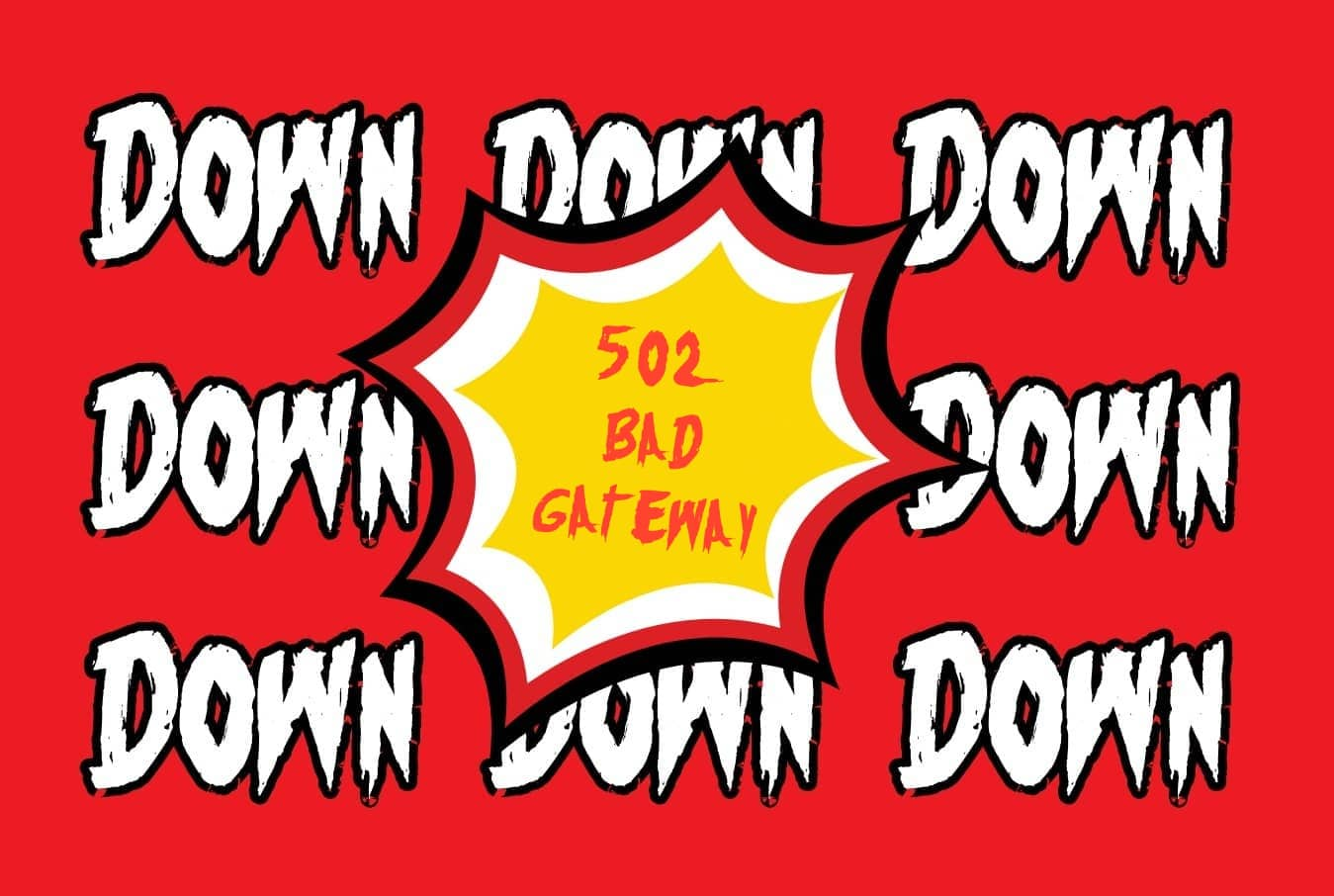
476Data SecurityCloudflare’s recent 502 Bad Gateway outage blamed on bad software (Updated)
If you are visiting a website and it is displaying “502 Bad Gateway” error it is not your fault but an issue...
-

 696Surveillance
696SurveillanceIs Your VPN Provider in a 14 Eyes Country? (What is 14 Eyes?)
The reason people have Virtual private networks (VPNs) is that they protect our online privacy, however, privacy is essentially non-existent if you live in...
-

 315Infosec
315InfosecEmployees Actively Seeking Ways to Bypass Corporate Security Protocols in 95 % of Enterprises
Nowadays cyber incidents activities such as data theft, insider threat, malware attack most are significant security risks and some it caused by the...
-

 5.1KMalware
5.1KMalwareOSX/Linker Malware, A Weaponized Unpatched Security Bug
We rarely feature a story about MacOS security here in Hackercombat.com, as the platform is not really attractive for hackers to target....
-

 4.8KPrivacy
4.8KPrivacyWhat Is Application Control? — Types and Benefits
What Is Application Control? In today’s business environment, applications play a huge role in day-to-day business operations. With the help of applications,...
-

 3.5KPrivacy
3.5KPrivacyDevice Control Measures: Should You Really Do It?
Today, removable devices like flash drives and external hard drives help make data transport much easier. Large amounts of corporate data can...






