All posts tagged "Security"
-

 449Data Security
449Data SecurityHacker publishes ‘unpatchable’ permanent jailbreak for iPhone 4s to iPhone X
Apple’s jailbreak just became easier. While a jailbreak is technically illegal, Apple users have been doing them since the launch of the...
-

 534How To
534How ToHow to Secure a Website by Monitoring DNS Records
What is DNS and How Does It Work A Domain Name System, or DNS, takes a familiar and understandable website name like...
-

 402Cyber Events
402Cyber EventsInformation Security Professional Degeneration
00:35 Ministry of Sound, London, UK – We all know what professional development is; I am going to talk about going to...
-

 526How To
526How ToHow to Protect Your Online Store from Cyber Threats
Owning an online store can be a fabulous and lucrative venture in today’s marketplace. With so many sales and transactions taking place...
-

 468Data Security
468Data SecurityThe Benefits of Using a VPN at Home
To many people, the idea of using a VPN is still in its infancy while some believe that VPNs are for those...
-

 391Surveillance
391SurveillancePoor security: 15,000 private webcams exposed to creeps
Your exposed webcams are backdoor for creeps. Every cybersecurity article you’ll find will include some sort of reminder emphasizing the use of...
-

 480How To
480How ToHow To Keep Your Data Safe When Traveling With A Laptop
When we travel, it’s rare we go without some form of electronic device, whether that be our smartphones, tablets or even laptops....
-

 415Data Security
415Data SecurityEvery Ecuadorian has been compromised in massive data breach
Data of Julian Assange, founder of Wikileaks was also found in this breach who lived in the Ecuadorian embassy in London since...
-
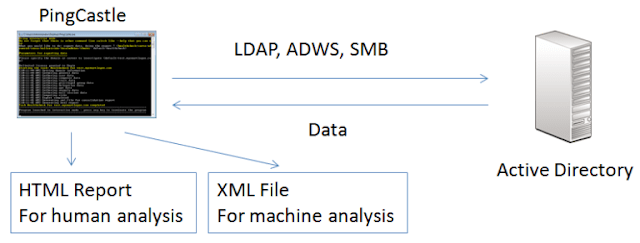
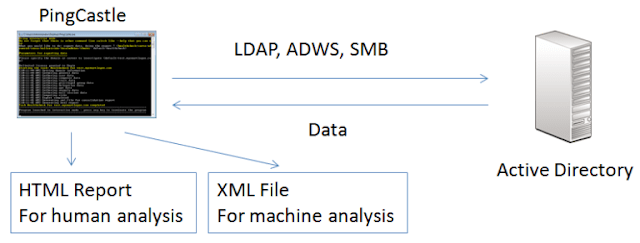 362Security Tools
362Security ToolsPingCastle – Get Active Directory Security
The risk level regarding Active Directory security has changed. Several vulnerabilities have been made popular with tools like mimikatz or sites...
-
 399Data Security
399Data SecurityMalware called InnfiRAT is creeping into cryptocurrency wallets
Cryptocurrencies have been known to be the cause of fortune for quite a few people. It all started from 2009 and even...
-

 347Hacked
347Hacked‘Eva Richter’ Scam Encrypts Your Files By Posing As A Fake Resume
Opening a job email titled “Bewerbung via Arbeitsagentur – Eva Richter” (Application via Employment Agency – Eva Ritcher) could prove disastrous to...
-
 645Geek
645GeekThe Joker is haunting Google Play Store with malware
Another day, another Android malware – This time; The Joker malware is here not to creep you out but steal from you....
-
 552Data Security
552Data SecuritySimjacker vulnerability lets attackers track your location with an SMS
The Simjacker vulnerability could extend to over 1 billion mobile phone users globally. As time passes, we’re witnessing more exploits building upon...
-

 2.3KPrivacy
2.3KPrivacyThe Five Incident Response Steps
It is important to remember that implementing incident response steps is a process and not an isolated event. For a truly successful...
-
 514How To
514How ToHow Can SEO Help Increase Website Security?
Though many think that SEO (Search Engine Optimization) and security do not go hand in hand, they are a lot closer than...
-

 329Hacked
329Hacked99% Email Attacks Require Human Interaction: Security Researchers
Email-based cyber attacks have become common these days. I am not the only one receiving emails saying that the file in the...
-
 2.0KData Security
2.0KData SecurityWikipedia suffers DDoS attack causing worldwide service disruption
The DDoS attack on Wikipedia is first of its kind. The popular online encyclopedia Wikipedia has suffered a DDoS attack over the...
-
 374Data Security
374Data SecurityHackers can break into Android devices by sending a text
Not long ago, we saw the emergence of sim swapping attacks utilizing a loophole in the two-factor authentication process. Now in the...
-

 421Data Security
421Data Security7 Tips to Increase Your WordPress Security
Do you have a WordPress website? Here are some quick and easy tips to increase your WordPress security and keep your site...
-

 359Hacked
359HackedThis Technique Claims To Make Passwords 14 Million% Tougher To Crack
Tide, an Australia-based non-profit organization has come up with a technique called ‘Splintering’ that claims to make usernames and passwords 14 million...
-

 579Data Security
579Data SecurityUnsecured database leaks phone numbers of 419 million Facebook users
Another day, another privacy disaster hits Facebook users. To add insult to the already enraged privacy advocates, Facebook has yet again disappointed...






