All posts tagged "Security"
-
 3.7KData Security
3.7KData SecurityStealthy RotaJakiro backdoor malware targeting Linux for 3 years
New RotaJakiro Stealthy Linux Malware With System Backdoor Capabilities Went Unnoticed for 3 Years. Qihoo 360’s Network Security Research Lab, aka 360...
-

 2.1KData Security
2.1KData SecurityTesla cars can be remotely hacked using drone, WIFI dongle
While analyzing vulnerabilities researchers were able to unlock Tesla Model X’s doors with a remote hack using a DJI Mavic 2 drone...
-

 1.8KHow To
1.8KHow To8 steps to develop secure and unique app for your business
Are you planning to create an app for your business? If yes, you are in the right place! A smartphone app is...
-
 5.4KHow To
5.4KHow ToHow to repair suspect database in SQL Server
Programs work with databases, and if the database crashes essential information can be lost and this will be disastrous to the user....
-

 3.2KCyber Crime
3.2KCyber CrimeCombatting Email Spam – What you should know
It is difficult to protect yourself from spammers. You can register on the site and leave your mail, subscribe to the newsletter,...
-

 3.3KNews
3.3KNews1-click code execution vulnerabilities in popular software apps
The IT security researchers at Positive Security Fabian Bräunlein and Lukas Euler have identified multiple one-click vulnerabilities across various popular software applications...
-
 5.0KGeek
5.0KGeekA child sent out gibberish tweet from official US Nuclear-agency account
A Child’s Gibberish Tweet from US Nuclear-agency Account Sends Twitter into Frenzy – Sparks Debates on National Security. How is it possible...
-
 1.4KNews
1.4KNewsA hacker claims to be selling sensitive data from OTP generating firm
The OTP-generating firm has some of the top giants as clients including Google, Facebook, Amazon, Apple, Microsoft, Signal, Telegram and Twitter, etc....
-

 4.4KNews
4.4KNewsHackers claims to be selling 13tb of Domino’s India data
According to IT security researcher Rajshekhar Rajaharia, “If you ever had ordered pizza online from Domino’s India your data is leaked now.”...
-
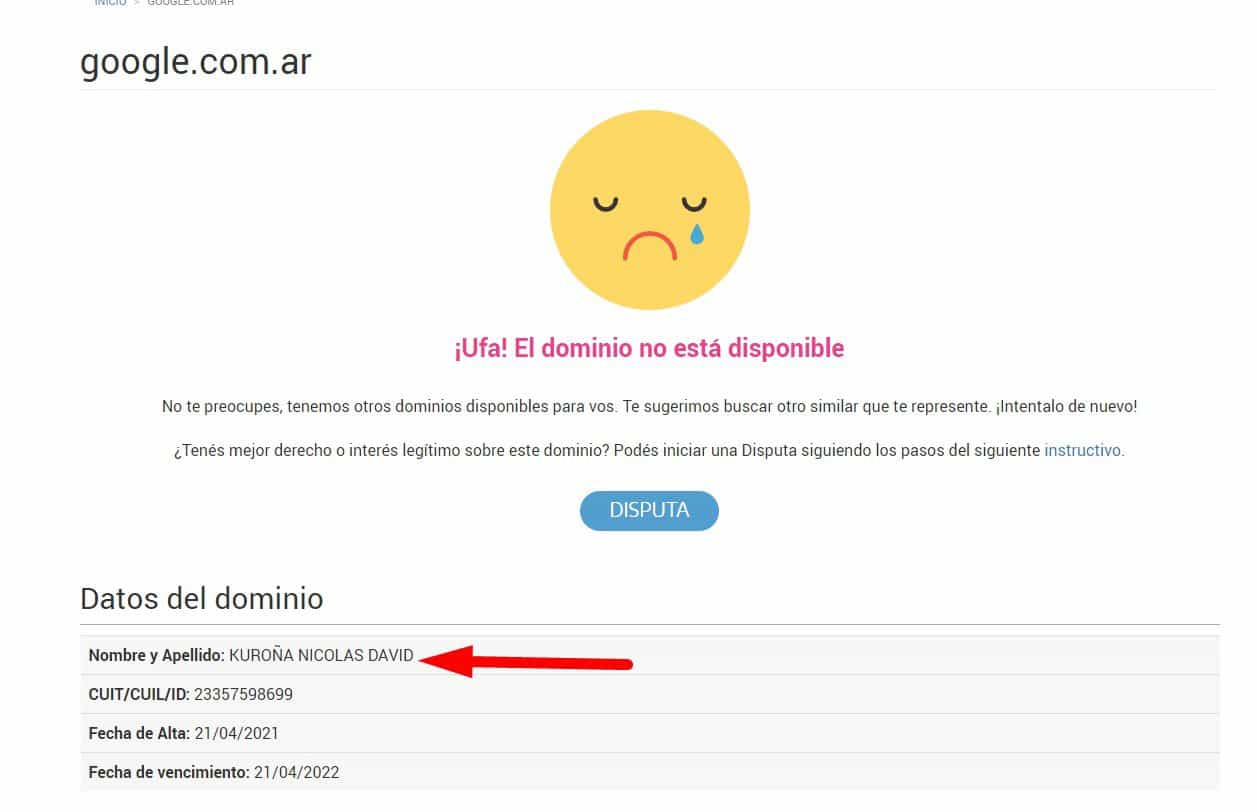
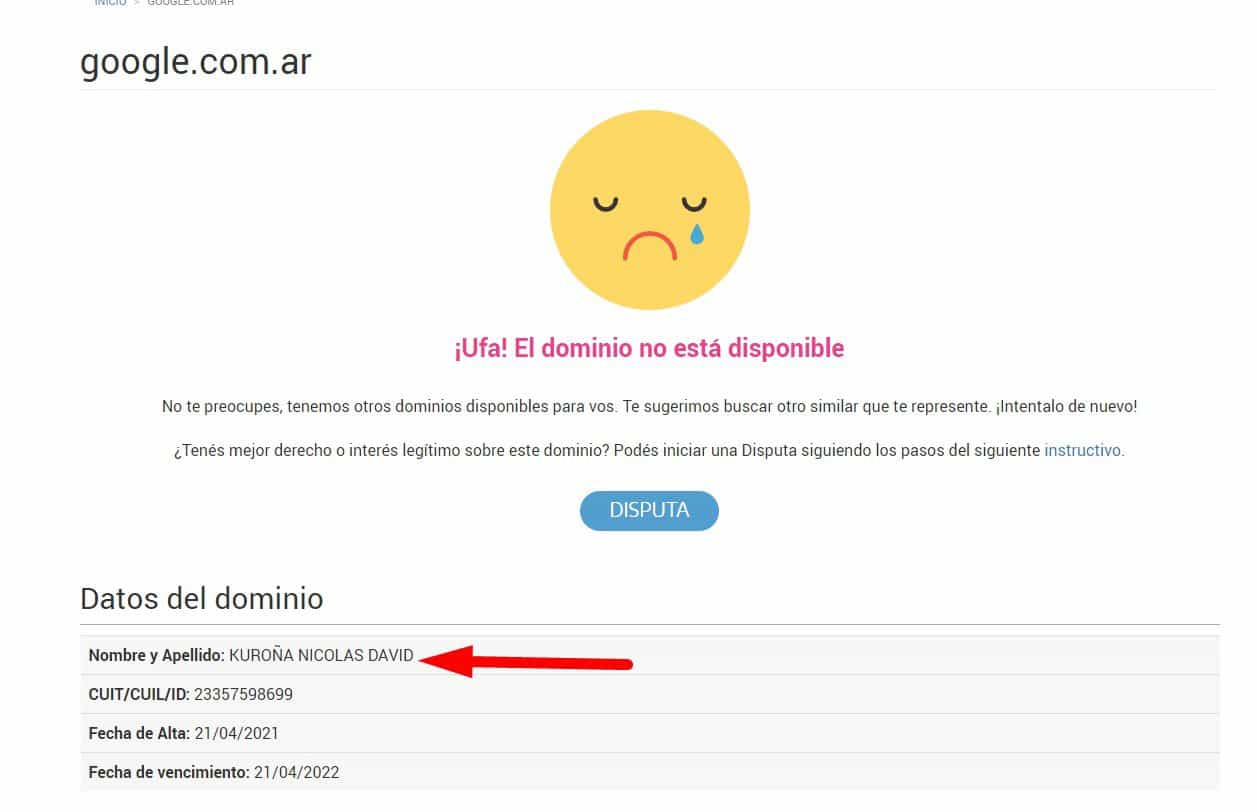 2.5KGeek
2.5KGeekGoogle Argentina domain bought by a random citizen for $5
The official Google Argentina domain went down for hours after its ownership was transferred to an Argentinan citizen. On Wednesday, Google users...
-
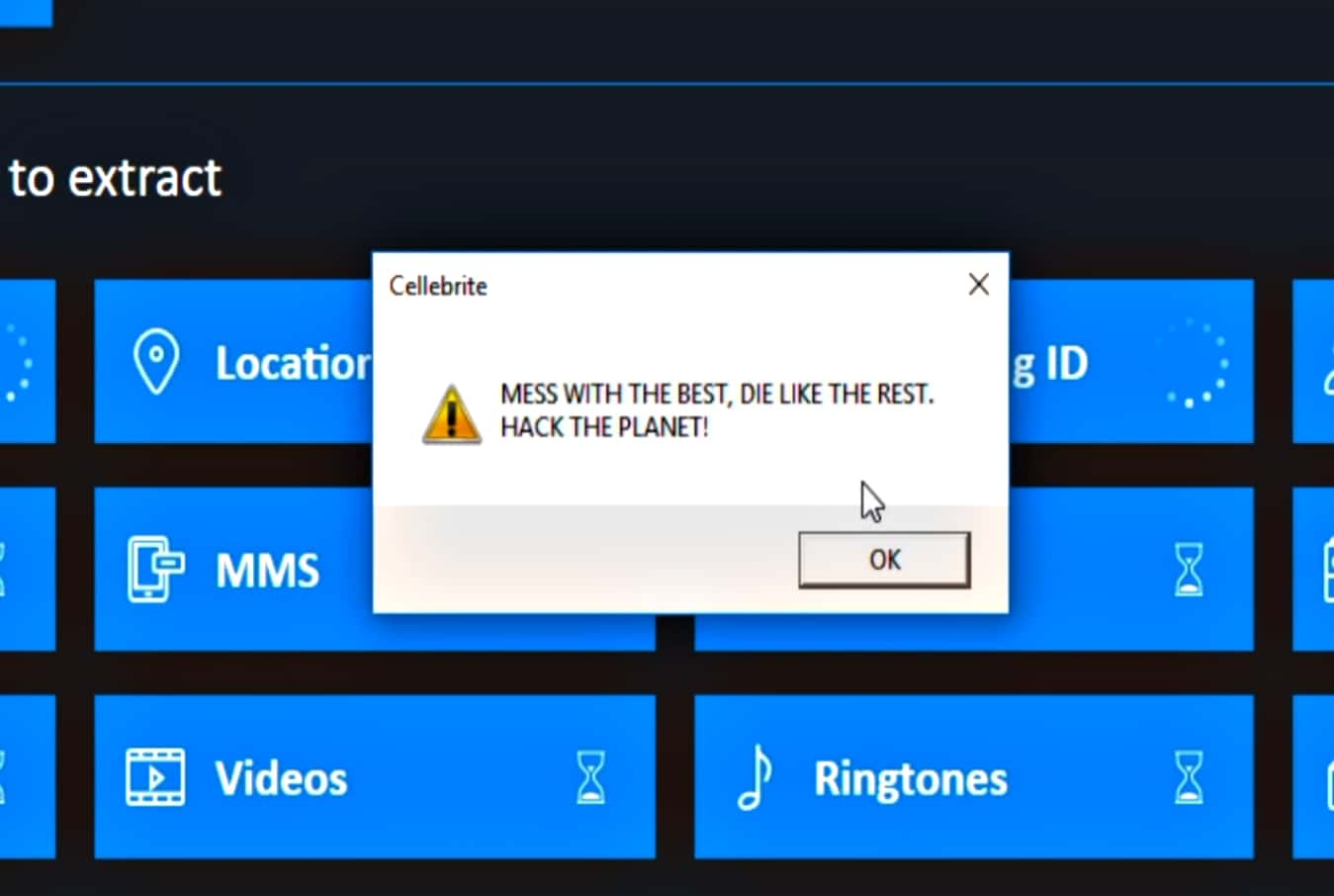
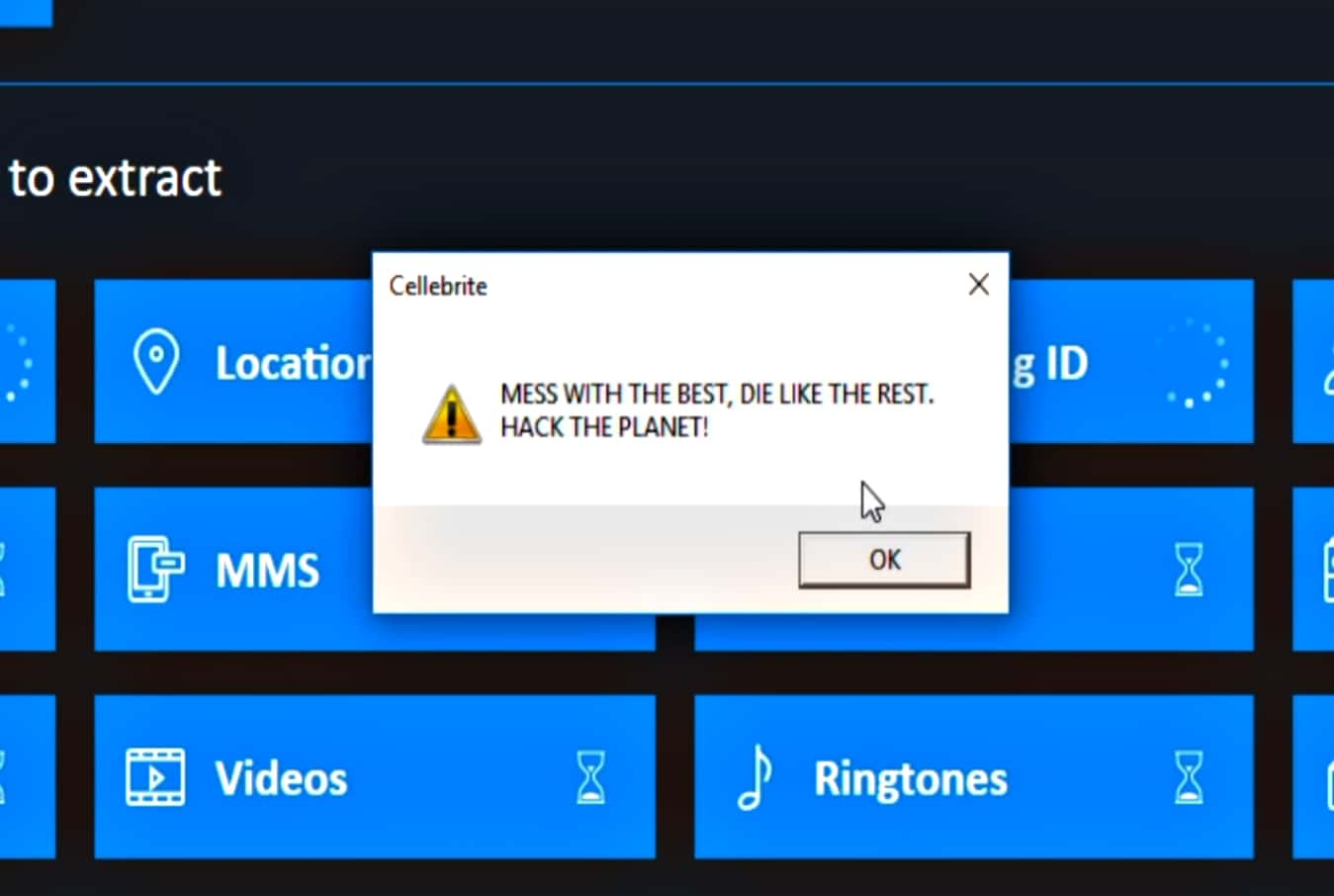 3.4KData Security
3.4KData SecuritySignal CEO hacks Cellebrite cellphone hacking, cracking tool
Moxie Marlinspike, CEO of Signal states that since Cellebrite itself makes a living from undisclosed vulnerabilities, he decided to disclose the vulnerability...
-
 3.2KData Security
3.2KData SecurityHacker dumps sensitive household records of 250M Americans
On April 22nd, 2021, a hacker going by the online handle of Pompompurin leaked a database containing personal and sensitive household data...
-
 3.0KSurveillance
3.0KSurveillanceScraped data of 1.3 million Clubhouse users published online
Clubhouse has confirmed that it did not suffer a data breach and leaked records are in fact collected through data scraping. In...
-

 1.6KNews
1.6KNewsSyncStop Is A USB Condom That You Need To Protect Your Data
Bad actors have evolved over time, and so have techniques for stealing your data from your device. Earlier this month, the Los...
-
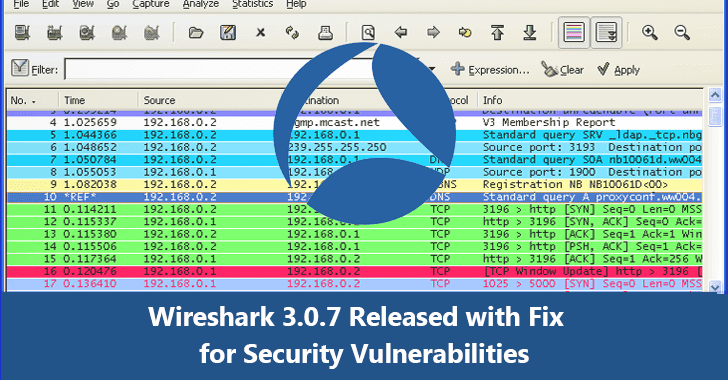
 3.1KVulnerabilities
3.1KVulnerabilitiesWireshark 3.0.7 Released – Fixes for Security Vulnerabilities & Update for BGP, IEEE 802.11, TLS Protocols
Wireshark 3.0.7 released with a number of security updates and fixed several other bugs that reside in the Wireshark components. Wireshark also...
-

 2.4KNews
2.4KNewsNew SMS Alternative ‘RCS Standard’ Is Exposing Users To Security Threats
Replacing the regular SMS with the RCS or Rich Communication Services is making users vulnerable to text-based attacks, call interception, location tracking,...
-

 4.4KGeek
4.4KGeekHow Will Blockchain Technology Revolutionize Logistics?
If you haven’t noticed, blockchain technology is taking the world by storm, catapulting technology into unchartered, new territory, allowing for greater transactional...
-
 1.5KCyber Crime
1.5KCyber CrimeBotnet found using YouTube to illegally mine cryptocurrency
Hundreds of botnets operate internationally to achieve various malicious objectives. One such botnet named Stantinko which has been operating since 2012 in...
-

 5.1KCyber Events
5.1KCyber EventsSmall businesses also need protection from cyber attacks
If you run a small business, it’s a matter of when, not if, your computer system or cyberinfrastructure falls prey to cybercriminals....
-

 1.4KHow To
1.4KHow ToHow To Stop Someone From Spying On Your Cell Phone
People have the right to privacy on their mobile phones. However, with the increase of malicious hackers and the use of third-party...
-

 5.1KData Security
5.1KData SecurityFacebook & Twitter suffer data breach via third-party developers
Another day, another breach involving Facebook, Twitter, and third-party developers. On Monday, both Facebook and Twitter announced that the data of hundreds...






