All posts tagged "Security"
-
 4.4KCyber Crime
4.4KCyber CrimeWhy torrenting on Elon Musk’s Starlink is not a good idea?
Starlink sends piracy warnings to users urging them to avoid downloading any illegal content by using their service. If you are one...
-

 2.5KData Security
2.5KData SecurityWifiDemon – iPhone Wifi bug exposed devices to remote attacks
Dubbed WifiDemon by researchers; the attack required the victim’s wifi to be set on auto-join which is by default in iPhones. Just...
-

 4.6KData Security
4.6KData SecurityU.S Govt launches new website to fight ransomware, help victims
The US government is also offering $10 million in rewards for information on foreign hackers involved in ransomware attacks on the United...
-
 722Data Security
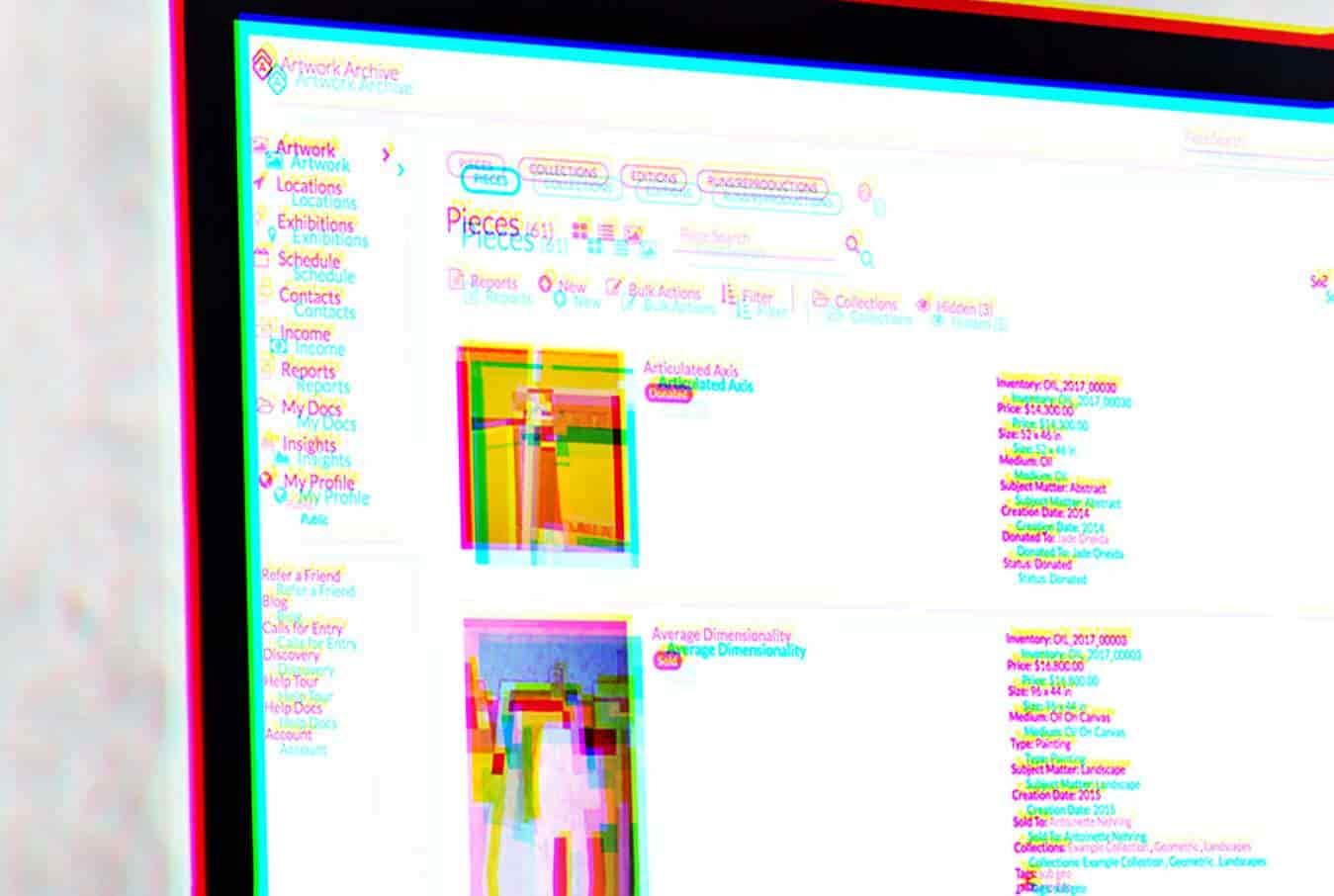
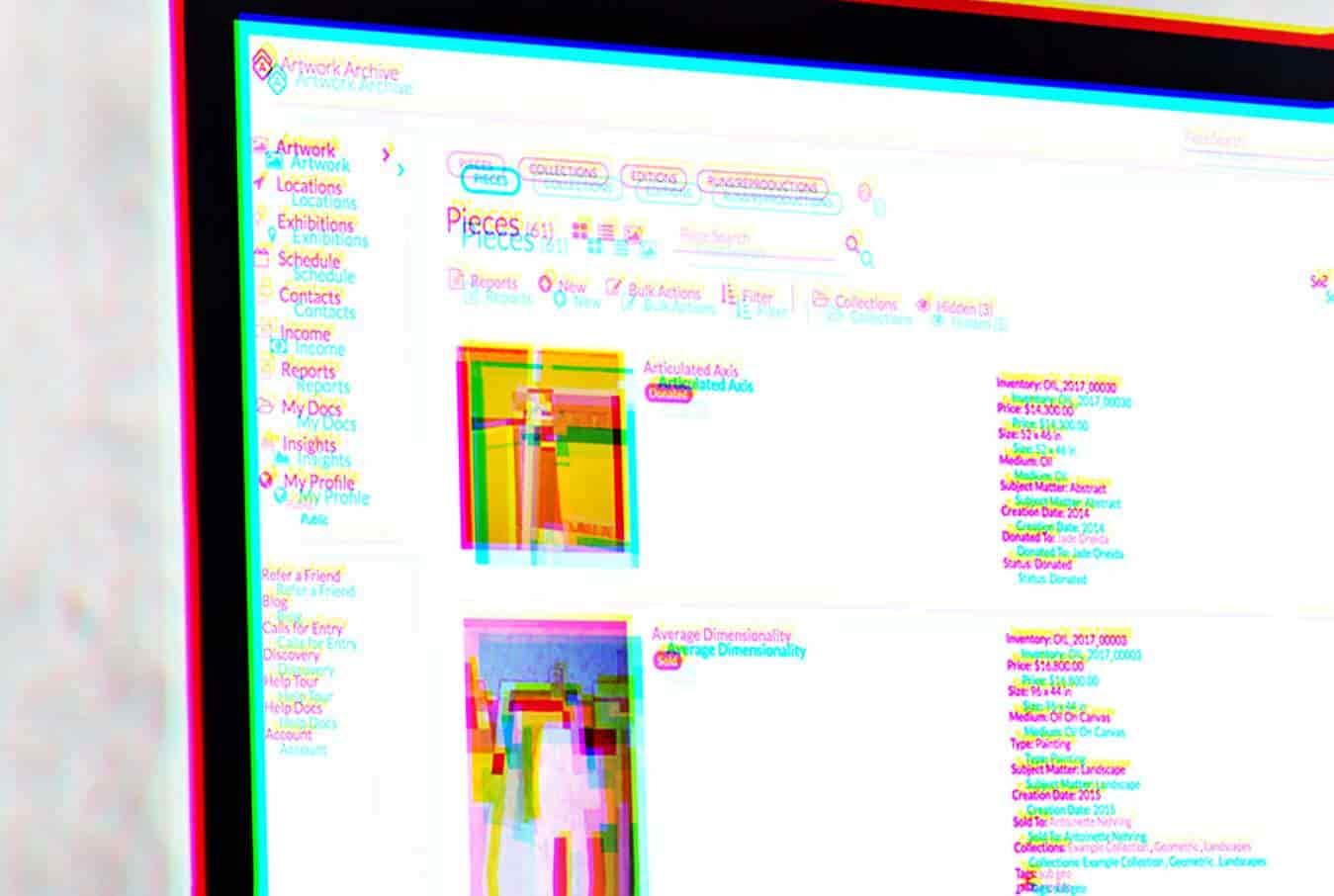
722Data SecurityMisconfigured AWS bucket exposed 421GB of Artwork Archive data
The trove of data was left exposed unencrypted and without any password or security authentication. The team of IT security researchers at...
-
 3.4KData Security
3.4KData SecurityHow data collected in gaming can be used to breach user privacy
“Surveilling the Gamers: Privacy Impacts of the Video Game Industry,” a new research reveals how personal and financial data collected by gaming...
-
 3.1KData Security
3.1KData SecurityPasswords by Kaspersky Password Manager exposed to brute-force attack
If you are using Kaspersky Password Manager (KPM) for creating passwords, you might want to consider regenerating those you created before October...
-

 2.5KData Security
2.5KData SecurityHackers leak scraped data of 87,000 GETTR users
GETTR, a pro-Trump social media platform, has been attacked twice since its launch on July 4th, 2021. GETTR is a Twitter-inspired social...
-
 4.1KData Security
4.1KData SecurityHackers disabling Macro security warnings in new malspam campaign
Usually, hackers utilize weaponized MS Office documents or other social engineering tactics in malspam campaigns to trap unsuspecting users and let them...
-
 5.2KCyber Crime
5.2KCyber CrimeNew LinkedIn phishing campaign found using Google Forms
In the latest LinkedIn phishing scam, the sender’s email address appears to be from Paul University which is based in Nigeria. Phishing...
-

 2.8KData Security
2.8KData SecurityMicrosoft issues emergency patch to fix PrintNightmare vulnerability
Microsoft is urging customers to “install these updates immediately.” Last week, the IT security researchers at Sangfor revealed a critical 0-day vulnerability...
-

 2.6KNews
2.6KNewsT-Mobile hacker used brute force attack to steal customers’ data
A 21-year-old US citizen named John Binns has claimed responsibility for the T-Mobile data breach and labeled the carrier’s “security is awful.”...
-
 2.4KCyber Crime
2.4KCyber CrimeSEC charges dark web user of insider trading, money laundering
The accused is a Greek national who used AlphaBay marketplace with the alias “The Bull” on the dark web for insider trading...
-

 535Data Security
535Data SecurityOnline learning provider New Skills Academy alerts users of data breach
According to New Skills Academy’s data breach notification email seen by Hackread.com, the number of victims impacted by the breach is yet...
-
 4.6KData Security
4.6KData SecurityWestern Digital My Book Live hard drives remotely wiped by hackers
In recent news, people are shocked to find out all of their data stored on their Western Digital My Book Live hard...
-

 3.9KNews
3.9KNewsWatch as hackers disrupt Iran’s prison computers; leak live footage
The group of hackers behind the cyberattack on the Iranian prison goes by the name of Edaalate Ali – The footage shows...
-
 3.3KData Security
3.3KData SecurityMicrosoft signed a driver called Netfilter, turns out it contained malware
Microsoft acknowledged the incident and currently investigating the issue but at the same time downplaying its impact. In recent news, it has...
-
 5.1KNews
5.1KNewsNew variant of PRISM Backdoor ‘WaterDrop’ targets Linux systems
According to researchers, the PRISM backdoor has been on their radar for more than 3.5 years. Security researchers at AT&T Labs have...
-
 2.0KData Security
2.0KData SecurityA hacker is selling 700 million LinkedIn users accounts
LinkedIn has not suffered data breach but the records being sold are collected through data scraping technique. Two months back, Hackread.com exclusively...
-

 4.1KCyber Crime
4.1KCyber CrimeREvil Ransomware targets 1000+ businesses causing holiday havoc
Reportedly, Revil ransomware is demanding $5 million in ransom. Not many ransomware gangs survive long enough to victimize one company after another...
-
 2.6KData Security
2.6KData SecurityUnpatched flaws exposing Linux marketplaces to remote attacks
Cybersecurity researchers at Berlin-based infosec company Positive Security have identified two serious zero-day vulnerabilities impacting Pling-based FOSS (free and open-source software) marketplaces...
-

 1.6KNews
1.6KNewsMillions of IoT devices, baby monitors open to audio, video snooping
The vulnerability would allow threat actors to remotely compromise a targeted ThroughTek IoT device and watch the real-time video feed, listen to...






