All posts tagged "Security"
-

 4.8KData Security
4.8KData SecurityHackers actively exploiting 0-day in Ubiquitous Apache Log4j tool
Apache has released Log4j version 2.15.0 to address the critical RCE vulnerability and users are urged to apply the update immediately. The...
-

 1.7KCyber Events
1.7KCyber Events3 Ways To Prepare For Cyber Attacks
Although there are countless ways to combat cyberattacks, in this article we are addressing 3 simple yet significant points that users can...
-

 2.4KHow To
2.4KHow ToHow To Secure Your Broadband?
Having an internet connection is very crucial whether you are using your desktop, phone, or smart TV. But if you are planning...
-
 4.6KCyber Events
4.6KCyber EventsHotel claims Conti ransomware attack on system as guests locked out
So far, the Conti ransomware has not demanded any ransom or published any details of the ransomware attack on their official website....
-
 2.7KGeek
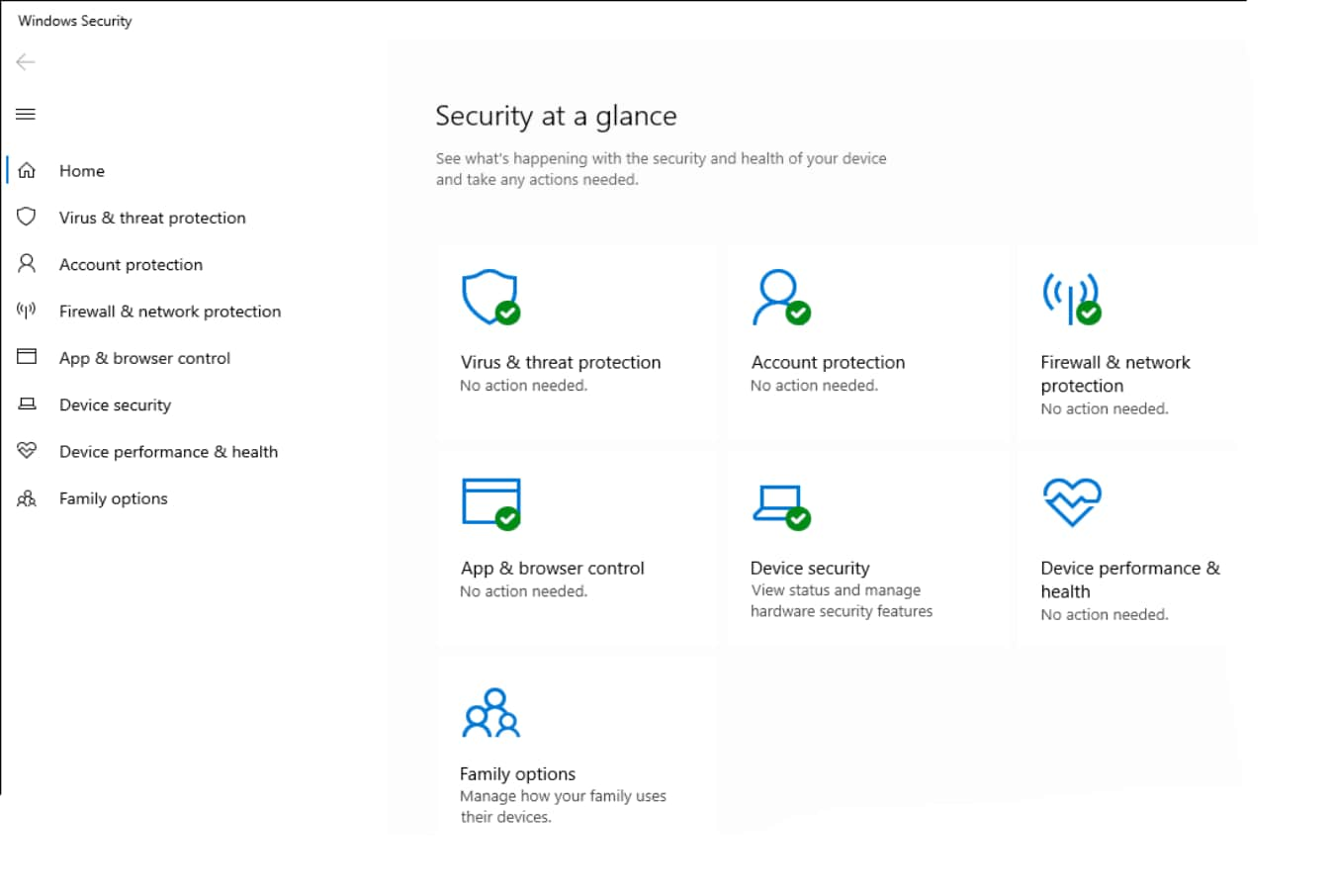
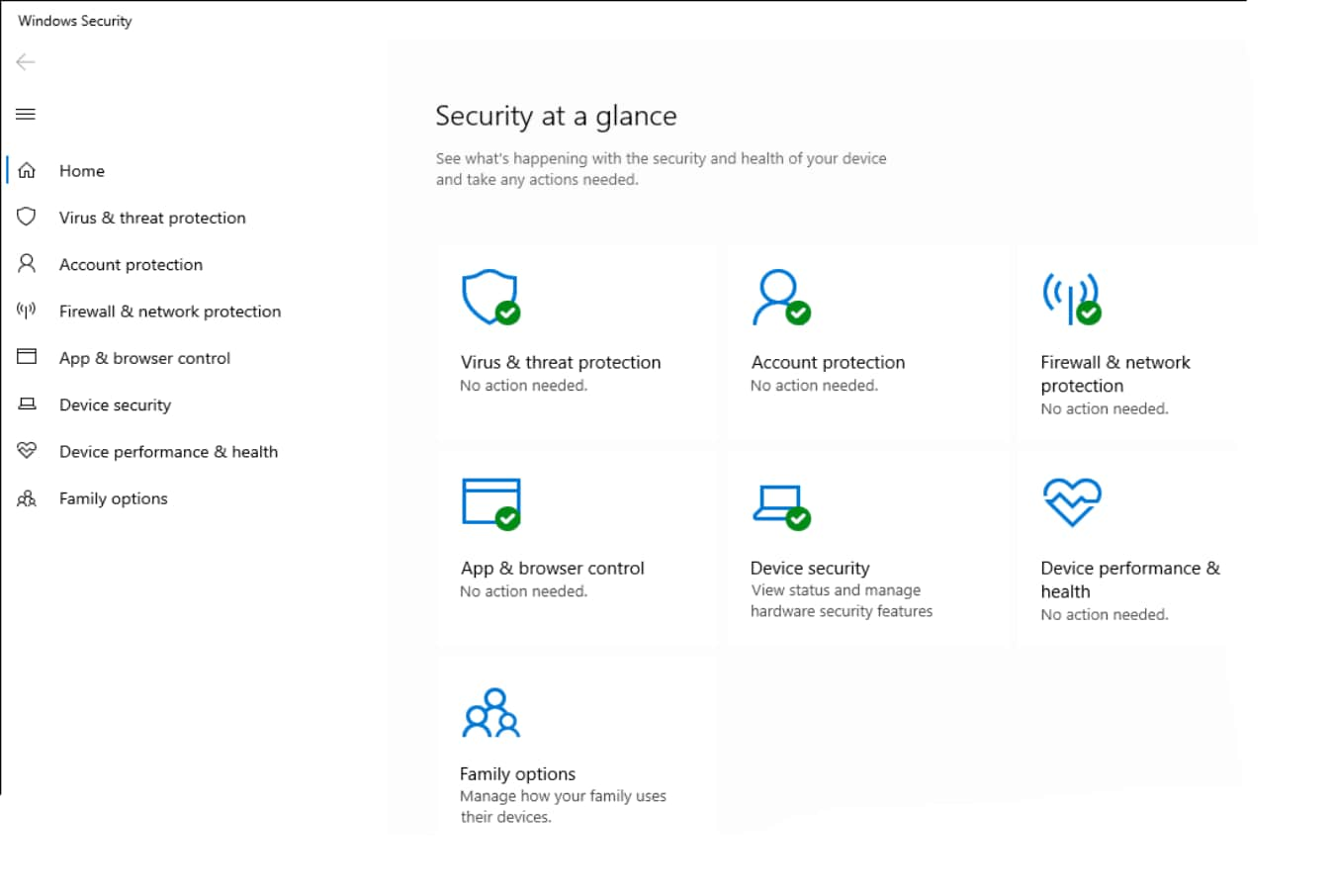
2.7KGeekAttackers exploiting Windows Installer vulnerability despite patching
According to Cisco Talos, abusing the flaw would allow an attacker with limited access to get higher privileges and become an administrator....
-

 1.3KGeek
1.3KGeekUnpatched Microsoft Exchange Servers abused in new phishing campaign
The noteworthy aspect of this phishing campaign is that the emails were sent as replies to previously sent messages, due to which...
-

 2.1KCyber Crime
2.1KCyber CrimeRemote access tools abused to spread malware and steal cryptocurrency
The new campaign also involves replacing cryptocurrency addresses shared via clipboard and setting up fake cryptocurrency websites. Trend Micro researchers have shared...
-
 1.3KNews
1.3KNewsDNA testing service data breach impacting 2.1 million users
DNA Diagnostics Center (DDC) has revealed that hackers managed to access highly sensitive and personal data of users including payment card data....
-

 2.4KData Security
2.4KData SecurityWiFi software management firm exposed millions of users’ data
Brazil-based WiFi management software firm WSpot exposed extensive details of high-profile firms and millions of customers. WSpot provides software to let businesses...
-

 2.7KCyber Events
2.7KCyber EventsSwire Pacific Offshore Operations hit by Cl0p ransomware gang
As seen by Hackread.com, the Cl0p ransomware gang has leaked partial SPO data including names, email addresses, passport scans, and more. Swire...
-

 4.7KNews
4.7KNewsRobinhood Data Breach – Hackers access millions of users’ data
Robinhood data breach involved social engineering attack in which hackers called a customer service staff member and somehow gained access to the...
-
 4.9KNews
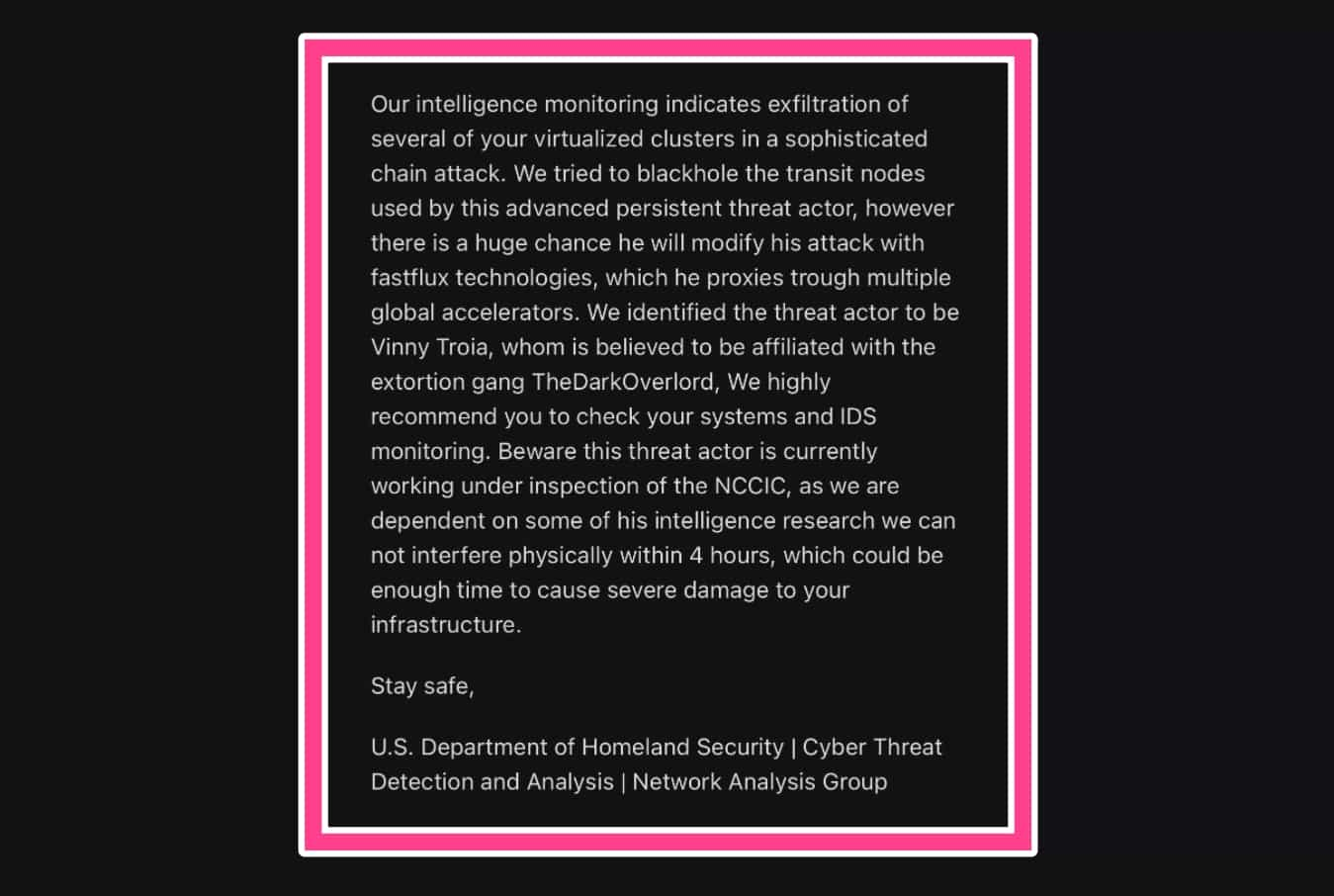
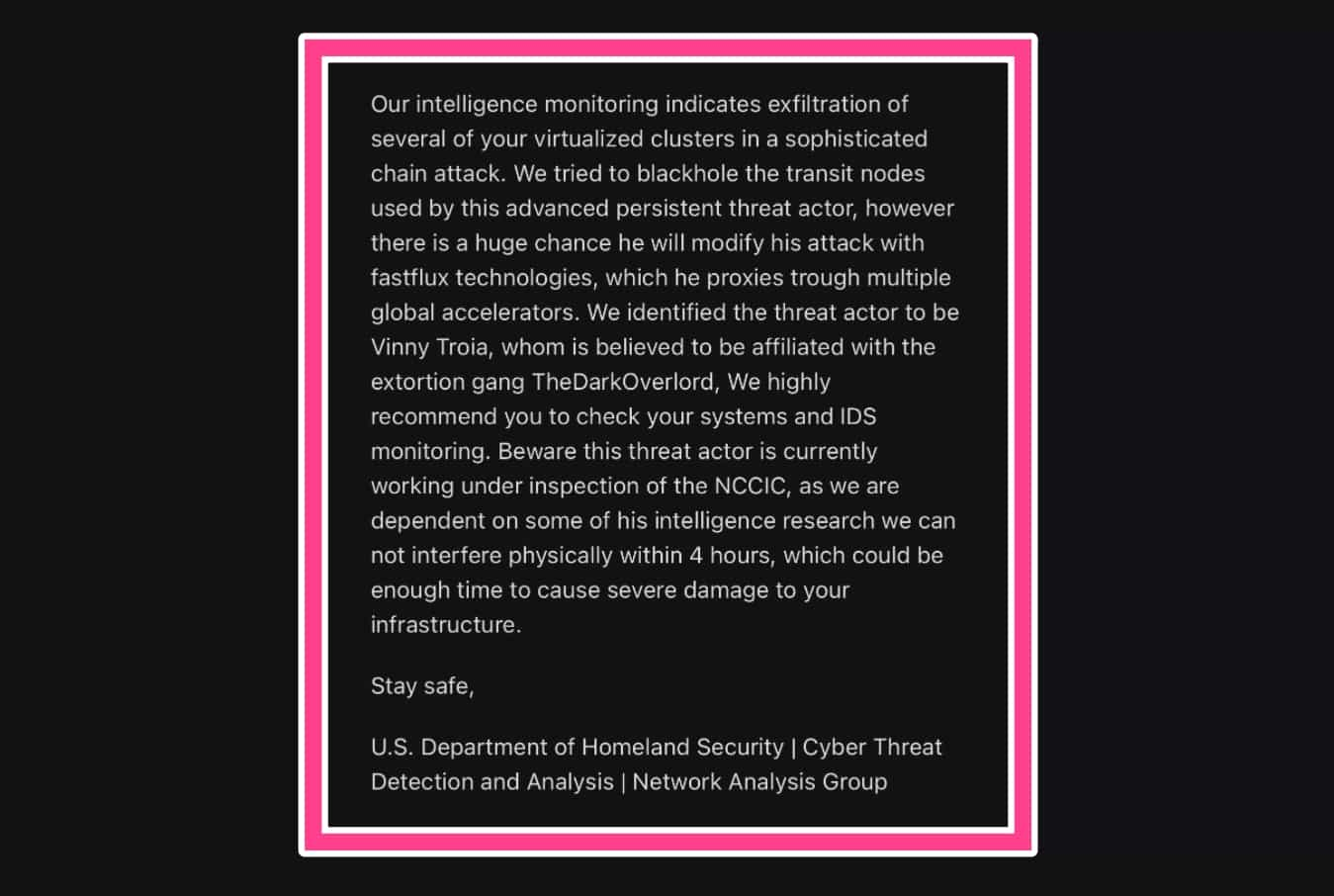
4.9KNewsHacker accessed FBI server to send fake email threats
The FBI acknowledged the unauthorized access over the weekend revealing that spam emails were sent from the agency’s email server to thousands...
-

 1.9KData Security
1.9KData SecurityCritical WordPress plugin vulnerability allowed wiping databases
The vulnerability existed in the WP Reset PRO WordPress plugin which is used by more than 400,000 websites. The IT security researchers...
-
 1.2KData Security
1.2KData SecurityProxyShell vulnerabilities exploited in domain-wide ransomware attacks
The ProxyShell vulnerabilities have prompted threat actors to launch domain-wide ransomware attacks against their targets, revealed a new research report from The...
-

 3.1KData Security
3.1KData SecurityHigh severity Intel chip flaw left cars, medical and IoT devices vulnerable
The vulnerability can be exploited by attackers with physical access to the CPU to breach the security protocols and obtain sensitive information....
-

 4.5KData Security
4.5KData SecurityRevealed: The 200 Most used and Worst Passwords of 2021
”123456” remains the most used and one of the worst passwords of 2021. If you are one of those who believed in...
-

 1.8KCyber Events
1.8KCyber EventsBandwidth.com reports multimillion dollar loss post DDoS attacks
In September 2021, Bandwidth.com suffered a series of days-long DDoS attacks forcing its service to go offline in the United States. In...
-

 2.9KHow To
2.9KHow ToHow to Securely Access Remote Desktop?
Having secure remote access for employees and following best practices is essential to keep your data secure. In the past few months,...
-
 3.5KCyber Crime
3.5KCyber CrimeTwitter hacker charged in sim swapping, cryptocurrency scheme
The 22-year-old British national Joseph James O’Connor, aka PlugwalkJoe, was one of the hackers behind 2020’s massive Twitter hack – PlugwalkJoe also stole...
-

 1.7KGeek
1.7KGeekManaged vs. Unmanaged VPS hosting -What are the Differences?
VPS hosting is beneficial for many reasons but what is the difference between Managed vs. Unmanaged VPS hosting and why does it...
-

 4.1KCyber Crime
4.1KCyber CrimeAuthorities arrest REvil ransomware operators in Kuwait and Romania
The total number of arrests made concerning Sodinokibi/REvil and GandCrab ransomware is now seven. Europol launched a multi-agency operation to catch REvil...






