All posts tagged "Spy"
-
 266Data Breach
266Data BreachHow To Stop Cyber Criminals to Spy & Track Your Smartphone
Many smartphone users are surprised when they get a pop up as soon as they leave a place asking them to rate...
-

 230Incidents
230IncidentsTURNING AN ECHO INTO A SPY DEVICE ONLY TOOK SOME CLEVER CODING
IT’S IMPORTANT NOT to overstate the security risks of the Amazon Echo and other so-called smart speakers. They’re useful, fun, and generally have well thought-out privacy protections. Then...
-

 232Incidents
232IncidentsOnavo, the free VPN that Facebook uses to spy
The free VPN of Facebook called Onavo has been dedicated for five years to collect private information of its users, such as...
-
 227Articles
227ArticlesAndroid Games are using your Mic to Spy on You
Alphonso, a startup that retails media-viewing data, provides a plugin that listens for audio signals in shows and movies. Approximately 250 mobile...
-

 302Incidents
302IncidentsPentagon contractor leaves social media spy archive wide open on Amazon
Trove included more than 1.8 billion posts spanning eight years, many from US people. A Pentagon contractor left a vast archive of...
-

 209Incidents
209IncidentsSpy satellite SpaceX launched might buzz the space station
Known as USA 276, it looks to be headed for the International Space Station, says one amateur spy satellite tracker. Then again,...
-

 202Data Security
202Data SecurityAttackers Can Decipher PINs and Passwords From the Way Users Tilt Their Phone
A JavaScript file secretly loaded without your knowledge on a site, or app you load on your mobile device, can access data...
-

 171Malware
171MalwareHackers are using this Android malware to spy on Israeli soldiers
Social engineering employed to distribute ViperRAT malware which uses infected devices to take photos and record audio. Hackers are carrying out surveillance...
-

 212Vulnerabilities
212VulnerabilitiesIntelligence report claims the Kremlin has cracked Telegram service
A raw intelligence document published last week claims Russian cyber experts have cracked Telegram messaging service to spy on opponents. A raw intelligence...
-

 232Incidents
232IncidentsGreat. Now Even Your Headphones Can Spy on You
CAUTIOUS COMPUTER USERS put a piece of tape over their webcam. Truly paranoid ones worry about their devices’ microphones—some even crack open...
-

 246Incidents
246IncidentsStealth Cell Tower, how to spy on workers with a harmless printer
Stealth Cell Tower, it is an antagonistic GSM base station concealed in an office printer that could be used for surveillance purposes....
-
 176Incidents
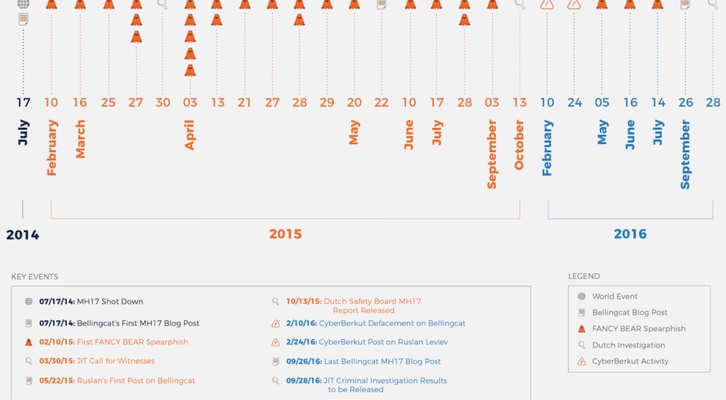
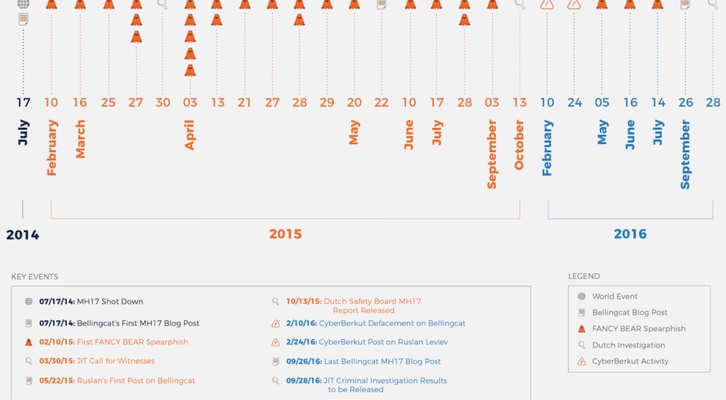
176IncidentsRussian hackers spy on Citizen Journalists investigating on Flight MH17 Crash
Researchers at the Bellingcat agency have been hit with spear phishing attacks and account takeover attempts while investigating flight MH17 crash. Once...
-
 251How To
251How ToDo you cover your webcam? Privacy is important
Privacy is important. If your webcam gets hijacked, hackers can record you with your notice. It’s good to cover your webcam with...
-
 240Data Security
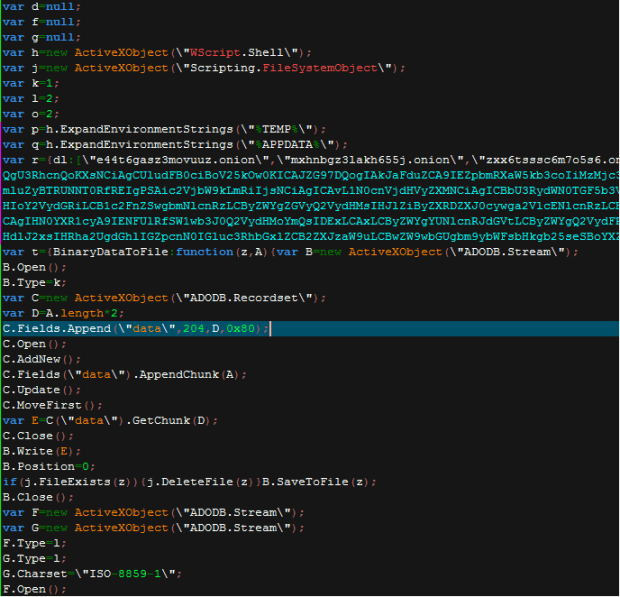
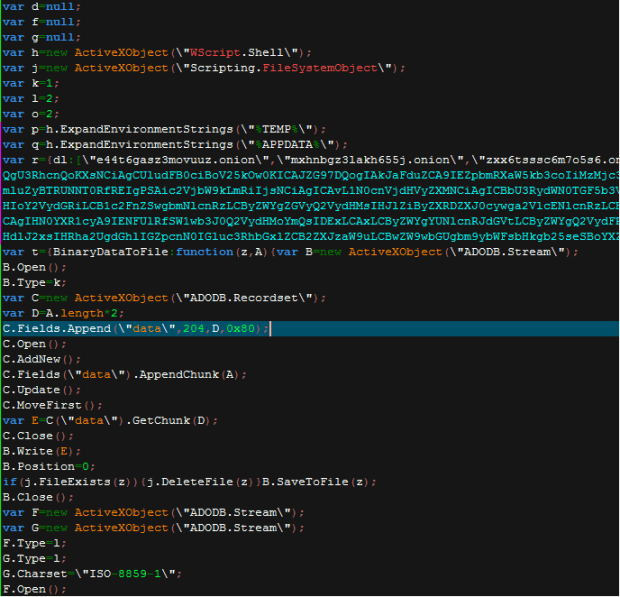
240Data SecurityDouble-click me not: Malicious proxy settings in OLE Embedded Script
Attackers have been using social engineering to avoid the increasing costs of exploitation due to the significant hardening and exploit mitigations investments...
-

 221Data Security
221Data SecurityBackdoor Trojan Uses TeamViewer Components to Spy on PCs in Europe, Russia, US
Crooks also delivering keyloggers and password stealers. A new trojan called BackDoor.TeamViewerENT.1 is using parts of the legitimate TeamViewer application to allow crooks...
-
 195Data Security
195Data SecurityResearchers crack open unusually advanced malware that hid for 5 years
Espionage platform with more than 50 modules was almost certainly state sponsored. Security experts have discovered a malware platform that’s so advanced in...
-

 196Malware
196MalwareKazakhstan Government Uses Malware to Spy on Journalists and Political Activists
EFF exposes threat group operating for Kazakhstan regime. The Electronic Frontier Foundation (EFF) has released a report today named Operation Manul that details...
-

 187Incidents
187IncidentsHow hackers used this Trojan malware to spy on a territorial dispute
F-Secure researchers say parties involved in the South China Sea arbitration case were infected with the data-stealing NanHaiShu Trojan. Hackers have used...
-
 191Data Security
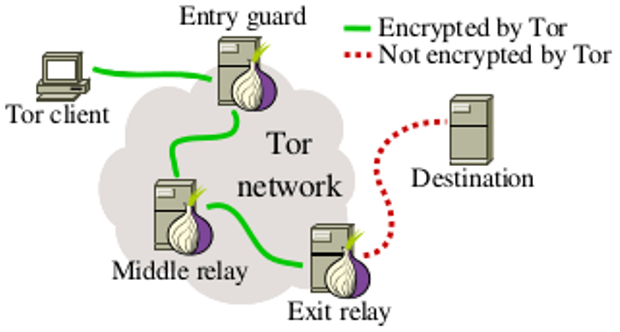
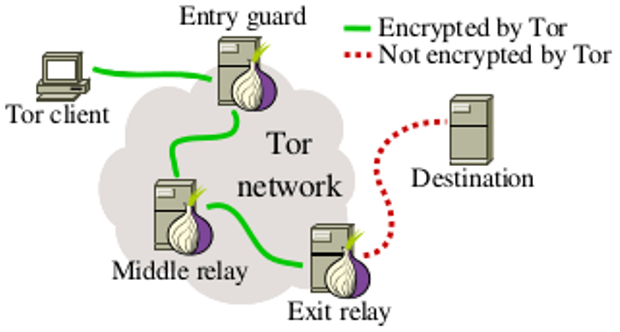
191Data SecurityOver 100 Snooping Tor Nodes Have Been Spying on Dark Web Sites
When it comes to accessing public websites, Tor has an intrinsic security problem: though the nodes between your computer and the public...
-

 220Incidents
220IncidentsQatar National Bank Hacked, Hackers Leak 1.4GB Database
Hackers leak 1.4GB database of information after breaching Qatar National Bank.A group of unknown hackers have claimed to have hacked into the...
-
 201Malware
201MalwareNew Trojan Spies on Linux Users by Taking Screenshots and Recording Audio
Dr.Web, a Russian antivirus maker, has detected a new threat against Linux users, the Linux.Ekocms.1 trojan, which includes special features that allow...






