All posts tagged "SSH"
-
 263Data Security
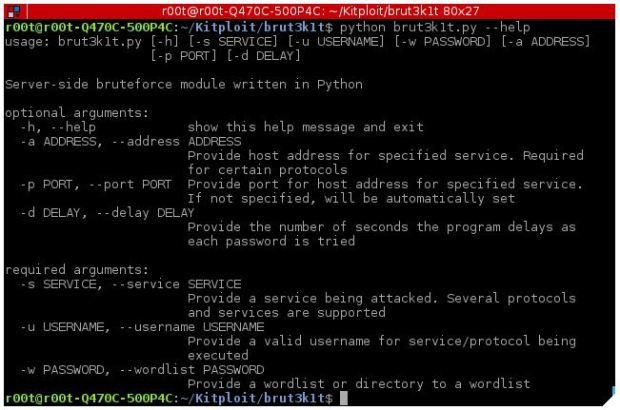
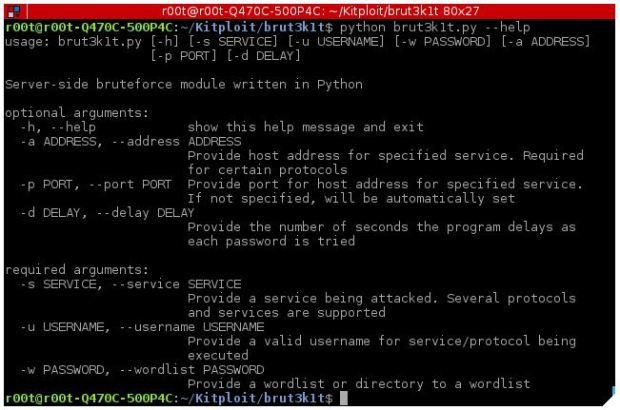
263Data SecurityTool to perform brute force attacks on ssh, smtp, facebook and Instagram- brut3k1t
As an introduction, brut3k1t is a bruteforce module on the server side that supports dictionary attacks for various protocols, information security experts say. Some...
-
 250Cryptocurrency
250CryptocurrencyPyCryptoMiner – A New Linux Crypto-miner Botnet Spreading over the SSH Protocol to Mining Monero
Highly Sophisticated Python Script Based Linux Crypto-miner botnet called PyCryptoMiner abusing SSH port and targeting Linux users to mining Monero CryptoCurrency. Its written...
-

 317Password Attacks
317Password AttacksRedLogin – SSH Brute-force Tools
Red Login: SSH Brute-force Tools. Features: High speed and precision CLI ( Console based ) Run the arbitrary command after the attack is successful (...
-
 243Security Tools
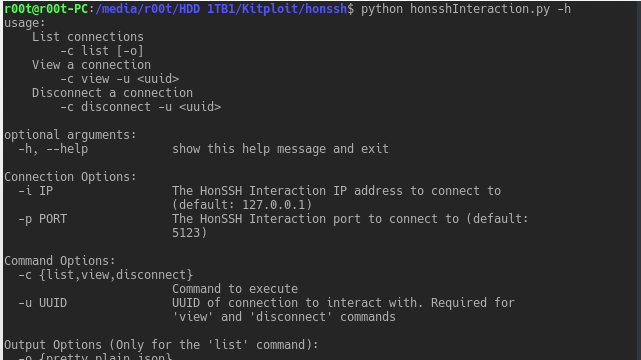
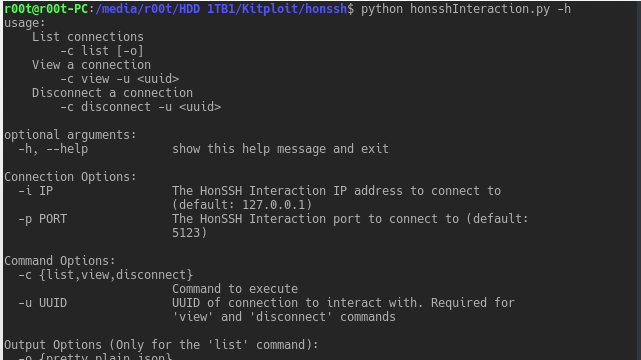
243Security ToolsHonSSH – Log all SSH communications between a client and server
HonSSH is a high-interaction Honey Pot solution. HonSSH will sit between an attacker and a honey pot, creating two separate SSH connections...
-

 229Hacked
229HackedBothanSpy & Gyrfalcon: CIA Malware To Steal SSH Credentials From Windows & Linux PCs
Short Bytes: WikiLeaks has recently published new documents, revealing new CIA malware implants. The first implant, named BothanSpy, targets SSH client Xshell...
-

 200How To
200How ToSetting up Linux Encrypted Networking Tool Secure Shell (SSH)
Much like the title explains, SSH or Secure Shell is an encrypted networking tool. Aimed at allowing users of various systems access...
-

 223How To
223How Tossh-audit – SSH Server Auditing
ssh-audit is a tool for ssh server auditing. SSH1 and SSH2 protocol server support; grab banner, recognize device or software and operating...
-
 201Vulnerabilities
201VulnerabilitiesAdvantech ICS Gear Still Vulnerable to Shellshock, Heartbleed
Twice in the past year, security researchers have found and reported critical vulnerabilities in Modbus gateways built by Advantech that are used...
-

 190Geek
190GeekMicrosoft Debuts Its First Release of Homemade SSH for Windows
Short Bytes: Working to fulfill its promise, Microsoft has released the first build of the Windows Powershell version of SSH tool. The...
-
 225How To
225How ToSentry – Prevents Brute Force Attacks Against SSH, FTP, SMTP and More
Supporting OS (operating system) FreeBSD Mac OS X Linux (CentOS, Debain, Ubuntu) Download Command: bash || sh export SENTRY_URL=https://raw.githubusercontent.com/msimerson/sentry/master/sentry.pl curl -O $SENTRY_URL...






