All posts tagged "Vulnerabilities"
-

 949Data Breach
949Data BreachThe Data Breach Hits Marriott Hotels Group Exposes 5 Million Guest Details
Late last year, we have featured here in Hackercombat.com the story about Marriot International Hotel chain data breach and the resulting accusation...
-

 251Vulnerabilities
251VulnerabilitiesVulnerabilities in automobiles affect their resale price
Many owners of software-faulted vehicles claim that these errors represent a decrease in their value According to cybersecurity and ethical hacking specialists...
-
 296Incidents
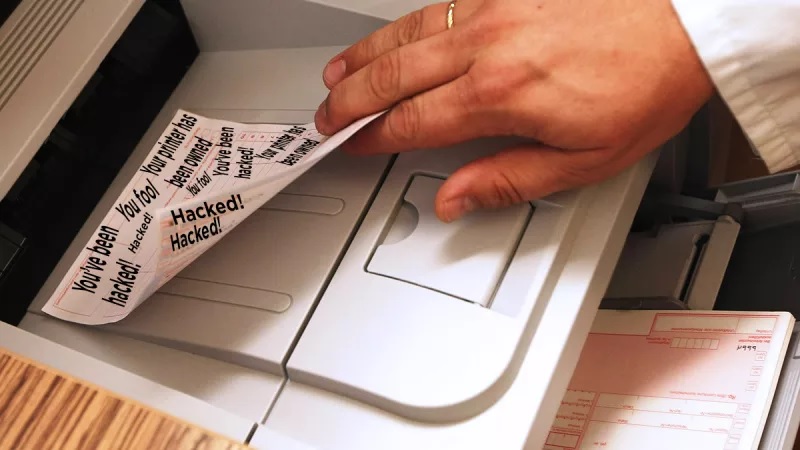
296Incidents#PrinterHack2: Hackers attack again and compromise 100k printers
The attackers claim that this time they have compromised hundreds of thousands of devices around the world, in what they themselves called...
-

 250News
250NewsProcessor Woes Continue: 7 New Meltdown and Spectre Bugs Arrive Weeks Before The Holidays
2018 is not a good year for chip vendors, as they have not received any break when it comes to the continued...
-

 203Hacked
203HackedThis New Bug Is Exploiting A Security Flaw in ‘Nearly All’ PCs And Macs
A research report published by F-Secure has unearthed a new flaw that makes most of the devices including those that are equipped...
-

 295News
295NewsUK Based Firm EE Hit by Two Security Vulnerabilities
As revealed by Tech Crunch, the UK-based telecommunication firm EE, endured recurrent flaws in its online system. In one week, EE fixed...
-

 361News
361NewsNew Mirai Botnet Variant Now Infects Vulnerable IoT Devices Near You
Right after the smartphone and tablet revolution that disrupted the laptop market considerably, the next big thing is the proliferation of IoT...
-

 273Cyber Crime
273Cyber CrimeCheckpoint Research Released Video Demo of a Nasty WhatsApp flaw
WhatsApp, the $19.3 billion mobile instant messaging platform acquisition of Facebook four years ago in 2014, has finally acknowledged the critical bug...
-

 285News
285NewsWhy Penetration Testing is Important
For enterprises, encountering IT security vulnerabilities have become common incident around their enterprise networks and IT systems. These IT security vulnerabilities can...
-

 188News
188NewsThese Vacuum Cleaner Vulnerabilities Are The New IoT Nightmare
Cybersecurity researchers have detected a couple of vulnerabilities in an IoT vacuum cleaner lineup that could let hackers spy on the victims,...
-

 200News
200NewsUK IT professionals are better at handling security vulnerabilities
A survey was conducted by Outpost24 to identify the managing of cyber-security exposure. This survey was conducted at Infosecurity and around 250...
-

 208News
208NewsVulnerabilities in PGP and SMIME Will Leak Emails in Plain Text
Pretty Good Privacy (PGP) and S/MIME Email encryption are affecting the users and it has been found that a new set of vulnerabilities...
-

 324Pentest
324PentestExploit Pack V10.07 Released with More than 38.000+ Exploits Including Zero-Days
Exploit Pack is a well-integrated open source tool for conducting professional penetration tests. As like any other penetration testing tool it requires...
-

 154News
154NewsAbbott Releases Firmware Upgrade to Fix Vulnerabilities
Abbott, the leading manufacturer of medical devices, releases a firmware upgrade that would fix cyber security vulnerabilities in certain cardiac devices. Health...
-

 298News
298NewsOver Four Million Vulnerabilities Detected by GitHub Security
GitHub security alerts significantly reduced the time it takes for developers to remove vulnerabilities from their Ruby and JavaScript projects, says GitHub....
-

 193Cyber Crime
193Cyber CrimeCyber Attacks Turning Biggest Risk to Businesses and Brands: Report
As per a recent study report, cyber attacks are now becoming the No. 1 risk to businesses, brands, operations and financials. It’s...
-

 212News
212NewsAttackers Exploit Tinder Vulnerability Using Phone Number
A Tinder user’s phone number- that’s all that a hacker could need, to take over the account itself, as per recent reports...
-

 334News
334NewsHackerCombat Guide on How to Prevent Phishing Attacks
Phishing attacks are now very common; every one who uses the internet comes across phishing emails almost daily and it seems that...
-

 253News
253News2017 Saw Software Vulnerabilities Increase by 31 Percent
Reports say that there has been a 31 percent increase in the number of software vulnerabilities in 2017 compared to 2016 and...
-

 222News
222NewsThe Likely Technology Trends in 2018
The Elon Musk’s giant solar battery in South Australia comes in as an exciting technology, and this was followed by the most...
-

 244News
244NewsWeb Site Security and Marketers Should be Cautious.
Edward Roberts, Director of Product Marketing at Distil Networks, says “Many marketers assume website security is not their problem. However, as the stewards of...






