All posts tagged "Vulnerabilities"
-

 308News
308NewsBelkin Wemo Insight Smart Plug Vulnerability Remains Exploitable
If you own a smart home, then you may probably be aware of Belkin Wemo Insight smart plug. Yes, it helps you...
-

 291News
291NewsProtect Your WordPress Website from SQL Injection
WordPress websites need to be protected against SQL injection threats. SQL (Structured Query Language) is a widely used database language, a domain...
-

 303News
303NewsYet Another WordPress Hack Exploiting Plugin Vulnerabilities
Here comes news about another WordPress website security breach carried out by exploiting plugin vulnerabilities. Reports say that hackers have been exploiting...
-

 324Vulnerabilities
324VulnerabilitiesDragonBlood, a set of vulnerabilities that affect WiFi WPA3 standard
Penetration testing course specialists from the International Institute of Cyber Security (IICS) report the finding of a set of vulnerabilities, dubbed DragonBlood,...
-

 261News
261NewsSerious Vulnerabilities Detected in the WPA3 Protocol
Almost one year after its launch, some very serious vulnerabilities that could lead to online password cracking have been detected in the...
-
 230Vulnerabilities
230VulnerabilitiesCritical vulnerabilities in Intel mini PC and Media SDK
According to penetration testing course from the International Institute of Cyber Security (IICS), Intel has launched update patches to correct two critical...
-

 181Data Security
181Data SecurityMicrosoft paid over $2M USD in its vulnerability bounty program last year
According to the authors of the book Learn ethical hacking, Microsoft paid more than $2M USD to security experts who participated in...
-

 257Vulnerabilities
257VulnerabilitiesResearchers Find 36 security vulnerabilities in LTE standard
Each new research conducted by experts from the best ethical hacking Institute and specialists from the International Institute of Cyber Security (IICS)...
-

 364News
364NewsThreat Intelligence With Two Most Used Operating Systems
With 4.312 billion users in the world, comprising 55.6% of the global population, the Internet has become an everyday center hub for...
-

 295Vulnerabilities
295VulnerabilitiesApple fixes critical vulnerabilities in its latest iOS update
Apple just launched iOS 12.2, updating its operating system to correct a total of 51 security vulnerabilities that impacted on iPhone 5s...
-

 373News
373NewsHow To Deal With DNS Vulnerabilities?
Believe it or not, in the early days of the Internet, all the domain names (nodes) it had been listed in just...
-

 386Mobile Security
386Mobile SecuritySHAREit App Vulnerabilities Allows Hackers to Bypass Android Device Authentication & Download Arbitrary Files Remotely
Researchers recently discovered 2 new critical vulnerabilities in the SHAREit App lets attackers bypass the Android device authentication mechanism and download the...
-

 1.1KCryptocurrency
1.1KCryptocurrencyCryptojacking Apps Placed in the Microsoft App Store By Attackers
Security researchers found a cryptomining app in the Microsoft App Store. Researchers say that it was placed in the store between April...
-

 323News
323News617 Million Stolen Accounts For ‘Clearance Sale’ In The DarkWeb
The Dark Web is once again is hosting a ‘clearance sale’ of at least 617 million user credentials, collectively coming from recently...
-

 201Vulnerabilities
201VulnerabilitiesVulnerability allows hacking an Android smartphone using only a PNG image
Google claims that this vulnerability has not yet been exploited in the wild Ethical hacking and network security specialists from the International...
-
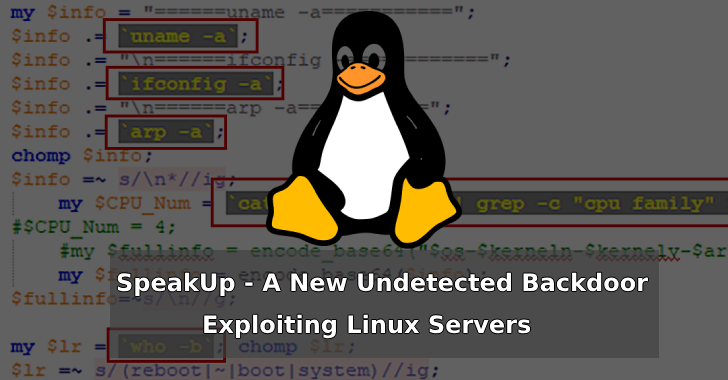
 282Malware
282MalwareSpeakUp – A New Undetected Backdoor Exploiting Six Linux Distributions With Known Vulnerabilities
A new trojan dubbed SpeakUp exploiting six different Linux distributions with know vulnerabilities. The campaign primarily targeting East Asia and Latin America,...
-

 284Cyber Crime
284Cyber CrimeAPT39 Iranian Cyber Espionage Team, Active In The Wild Again
The infamous APT39, the alleged Iran-funded cyber espionage team has been identified by FireEye as actively targeting Europe, USA, Australia, South Korea...
-

 256News
256NewsVulnerability Audit Before 2020 Tokyo Olympics, Launches in Japan
The Japanese government is seen as very proactive in its goal of making the 2020 Tokyo Olympics secure as possible, yes including...
-

 167Vulnerabilities
167VulnerabilitiesFaceTime vulnerability allows spying on Apple users
It is recommended that Apple users disable this app, at least until it is updated Network security and ethical hacking specialists from...
-

 4.1KCyber Attack
4.1KCyber AttackWordPress Websites Attacked via Zero-Day in Abandoned Plugin
Many WordPress websites have come under attack via a zero-day flaw in an abandoned plugin. The “Total Donations” plugin, which was earlier...
-

 344Vulnerabilities
344VulnerabilitiesCritical vulnerabilities in Cisco routers affect thousands of companies in the entire world
The firm has already released update patches for several SMEs products The Cisco technology firm recently launched update patches to address two...






