All posts tagged "Windows"
-

 247Vulnerabilities
247VulnerabilitiesThe last Meltdown patch affected by a serious vulnerability
As has been happening, the problems with the mitigations for the Meltdown fault continue. Recently, information security professional has shown that the Meltdown patch...
-
 277Hacked
277HackedThis Code On USB Can Trigger BSOD Even On Locked Windows PCs
In the past, we’ve told you about the perils of picking any random USB drive and using it. It might contain malware...
-
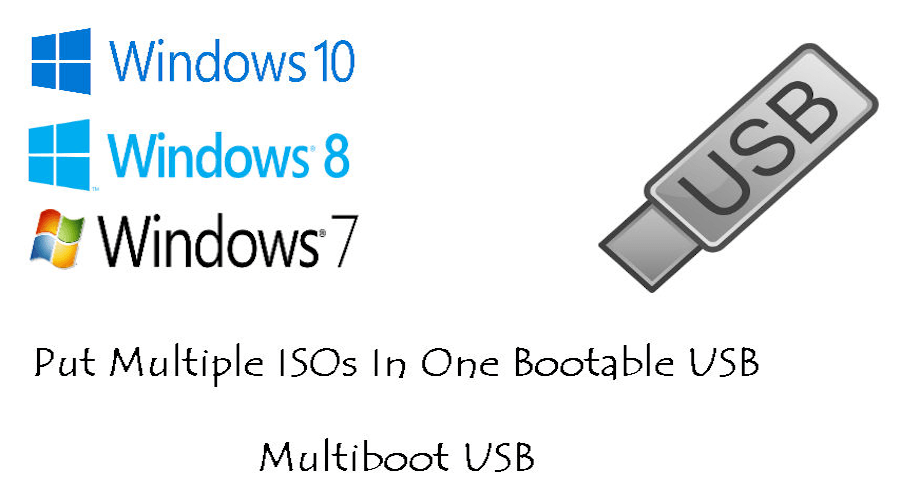
 412How To
412How ToHow To Put Multiple ISO Files In One Bootable USB Disk | Create Multiboot USB Disk
Creating a bootable USB disk comes handy when we have to reinstall our operating system in the case of a system failure....
-

 202Hacked
202HackedHidden For 6 Years, ‘Slingshot’ Malware Hacks Your PC Through Your Router
The researchers at Kaspersky Labs have uncovered a malware, dubbed Slingshot, that has been able to hide for around six years. While...
-

 294Cryptocurrency
294CryptocurrencyBiggest Crypto-Mining Campaign Ever – Hackers Mine $3 Million Worth of Monero Crypto-currency
Security researchers from Checkpoint discovered a largest Monero mining activity that uses XMRig miner on various versions of Windows machines. The hacker...
-

 166Data Security
166Data SecurityCrossRAT a Trojan built with Java that infects Windows, macOS, Linux and Solaris
Last week companies specialized in cyber security discovered the existence of a new Persistent Advanced Threat APT, supposedly sponsored by Dark Caracal, an organization...
-

 373News
373NewsA New Undetectable CrossRat Malware Targeting Windows,MAC OS & Linux
A wide range of cybercriminals now uses new “undetectable” CrossRat malware that addresses Windows, MacOS, Solaris and Linux systems. Last week we...
-

 237Hacked
237HackedLenovo Says It Shipped A Hackable Fingerprint Manager With Its Laptops
In case you’re running a Lenovo business machine with a built-in fingerprint sensor, you might want to install the latest security patch issued...
-
 302Malware
302MalwareMost Advanced APT Malware “CrossRAT” Globally Targeting Individuals & Exfiltrate Text Messages, Photos, Call Records
A multi-platform APT CrossRAT Malware discovered with sophisticated surveillance operation that targeting Windows, OSX, and Linux computer globally both individuals and organizations....
-

 395Lists
395Lists14 Best Free And Open Source Software For Windows 10 Every User Must Know In 2018
Microsoft is mostly criticized by the Linux community for their closed-source Windows operating system which single-handedly outperforms the popularity of all the Linux...
-
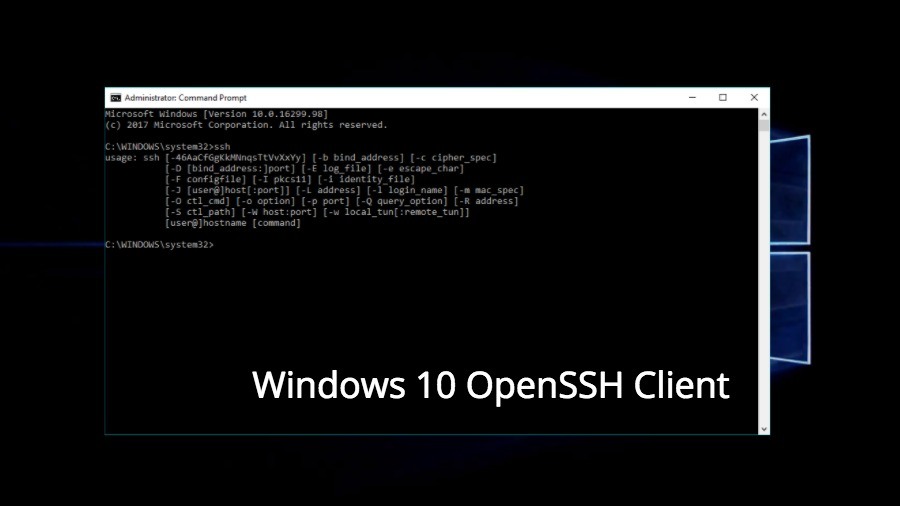
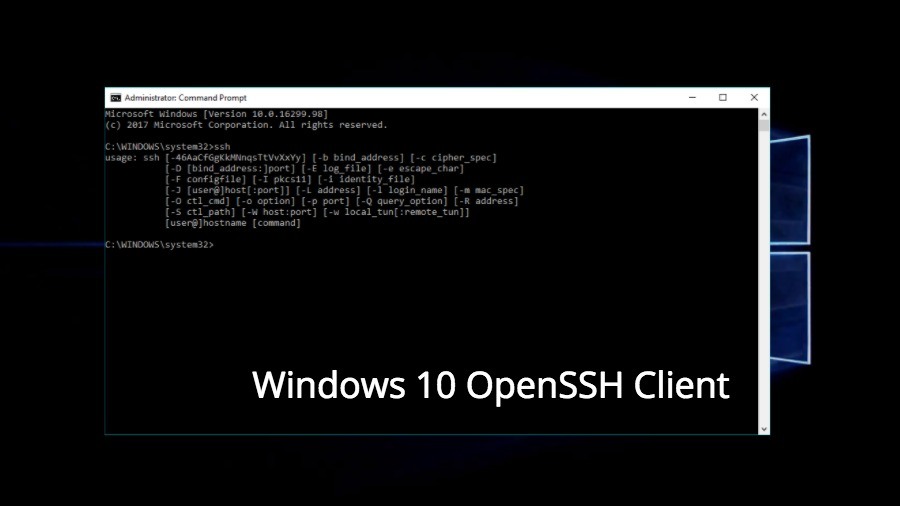 232How To
232How ToHow To Enable New & Built-In Windows 10 OpenSSH Client?
As using and configuring an SSH shell is very easy on any Linux or macOS machine, these operating systems have been a...
-
 130Incidents
130IncidentsPersistent drive-by cryptomining coming to a browser near you
Since our last blog on drive-by cryptomining, we are witnessing more and more cases of abuse involving the infamous Coinhive service that allows...
-
 242Incidents
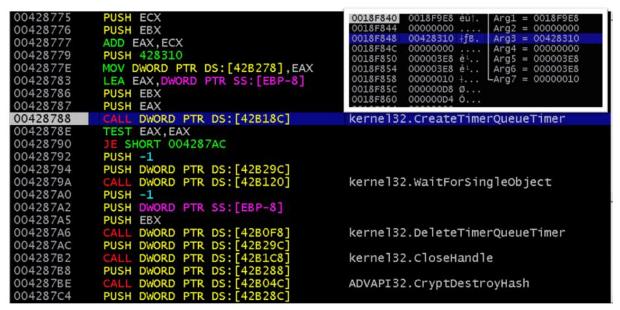
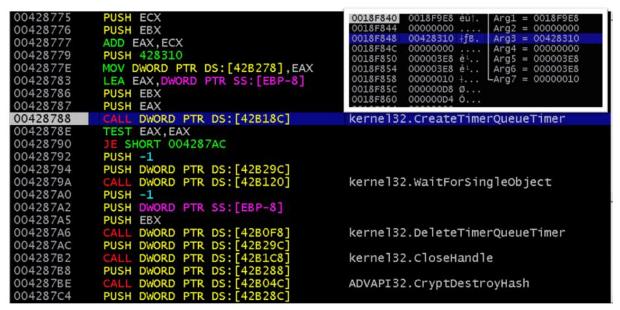
242IncidentsNew EMOTET Hijacks a Windows API, Evades Sandbox and Analysis
We discussed the re-emergence of banking malware EMOTET in September and how it has adopted a wider scope since it wasn’t picky about the...
-
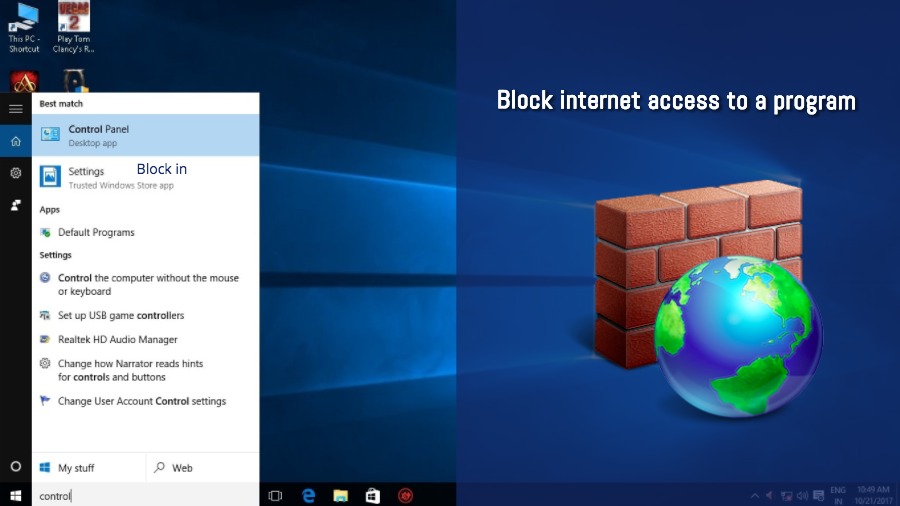
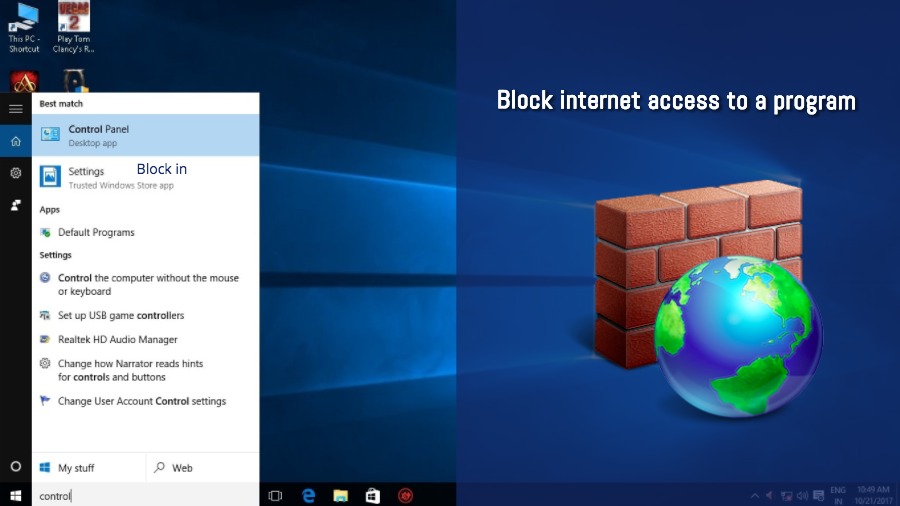 152How To
152How ToHow To Block A Program From Accessing The Internet In Windows?
Most of the third-party software that resides on your computer can access the internet and there are few offline-only programs being developed....
-
 267Lists
267Lists5 Easy Ways To Sign-in/Unlock Your Windows 10 PC
Keeping your PC protected using some digital lock is more than a necessity nowadays. While most Windows users prefer the password-based sign-in...
-

 354Lists
354ListsWindows 10 Fall Creators Update Features: What’s New In The Big Release
The Fall Creators Update is being pushed out as a part of Microsoft’s bi-annual update routine for Windows 10. It’s the fourth...
-

 294Hacked
294HackedKRACK Attack: Fix Released For Windows And Linux, Apple And Google Are Still Working
Yesterday’s news about the WPA2 vulnerabilities, known as KRACK, caused a situation of panic among the WiFi users on the internet. That’s...
-
Articles
Windows 10 Doesn’t comply with Dutch Regulations according to its regulators
To comply with the law, the DPA states that Microsoft requires getting valid user consent this indicates the company must be open about...
-

 189Articles
189ArticlesMicrosoft has killed Windows Mobile
Joe Belfiore continued that he had also shifted to Android himself. Windows 10 Mobile attempted to attract users by making them run...
-

 182Cyber Attack
182Cyber AttackHackers Are Making $63,000 In 3 Months By Exploiting Microsoft Servers To Mine Monero
Mining cryptocurrencies like mine monero can be a costly investment as they require a monstrous amount of computing power, so hackers have begun...
-
 360Vulnerabilities
360VulnerabilitiesCritical BlueBorne Vulnerability Puts More Than 5 Billion Bluetooth Enabled Devices Under Attack
Bluetooth is the leading and most widespread protocol for short-range communications.It is the backbone of short range connectivity in the vast majority...






