Search results for "NATO"
-
 2.7KIncidents
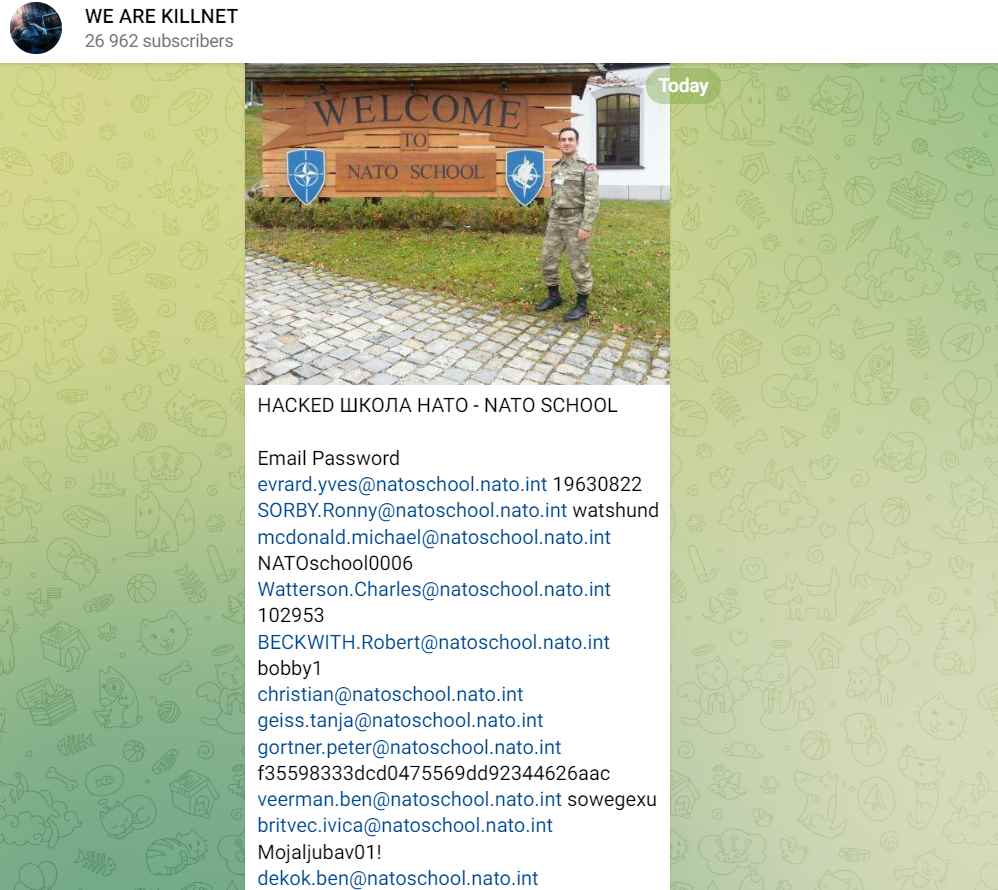
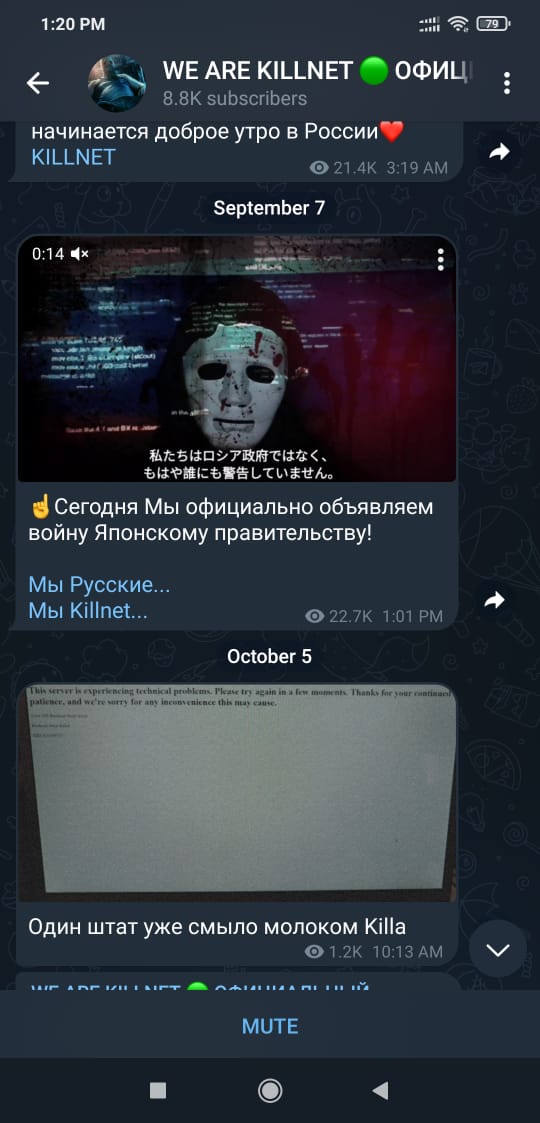
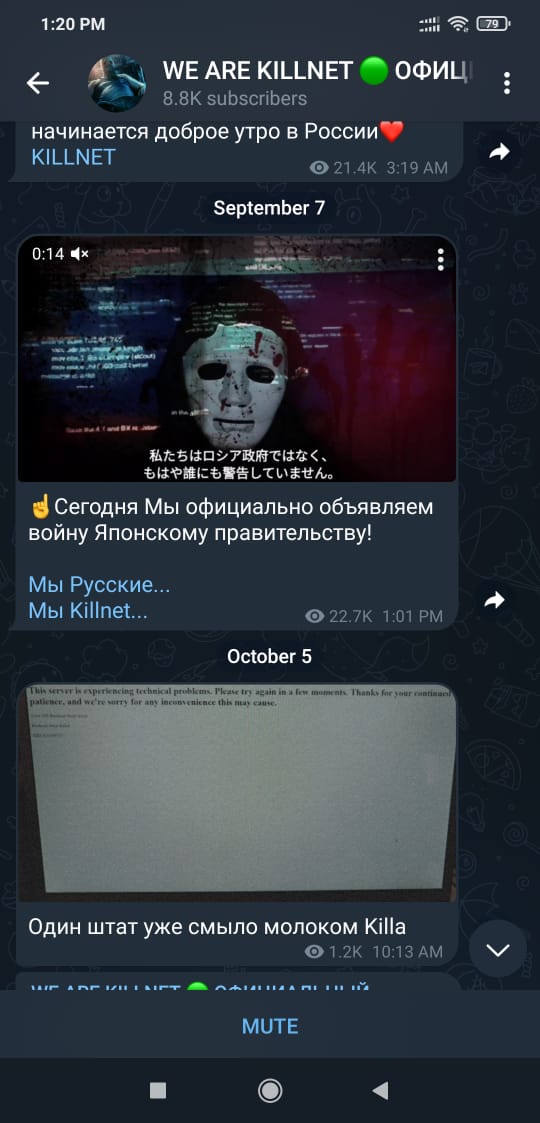
2.7KIncidentsRussian hacker group Killnet leaks confidential data of NATO members
KillNet originally came into being in the midst of the continuing Russian invasion of Ukraine, at which time it positioned itself as...
-
 4.8KScams
4.8KScamsPig butchering scams: The anatomy of a fast‑growing threat
How fraudsters groom their marks and move in for the kill using tricks from the playbooks of romance and investment scammers
-
 4.3KData Security
4.3KData SecurityRussian hacker group Killnet launches USA OFFLINE: F**K NATO campaign to hack all governments websites
Over the next three days, Killnet hacking group intends to cause chaos on official US websites. State and federal websites are listed...
-
 4.4KMalware
4.4KMalwareAnatomy of native IIS malware
ESET researchers publish a white paper putting IIS web server threats under the microscope
-

 472Data Security
472Data Security600 police officers attack a NATO bunker to seize 200 dark web servers and arrest 13 hackers
Just a few days ago a data center operated by cybercriminals was shut down by the authorities in Germany. According to ethical...
-

 619Cyber Crime
619Cyber CrimeDark web data center in former NATO bunker seized for hosting child porn
Bulletproof hoster not so Bulletproof after all. Authorities in Germany have raided, busted and seized a massive data bunker called “Cyberbunker 2.0”...
-
 285Packet Manipulation
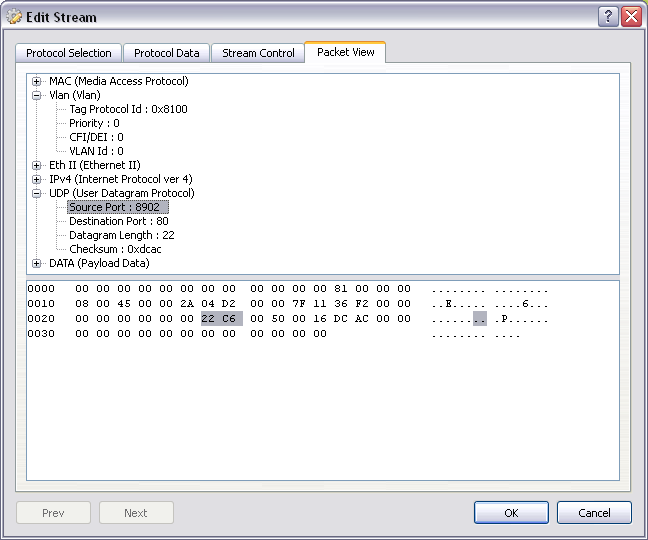
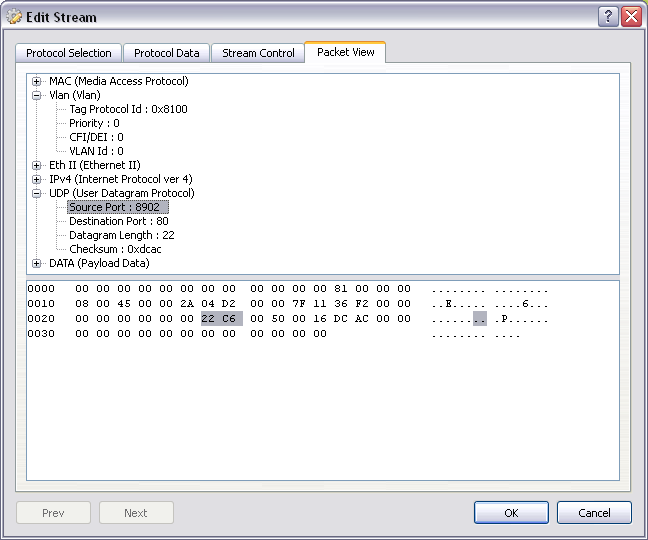
285Packet ManipulationOstinato – Network Traffic Generator
Ostinato is a packet generator and network traffic generator with a friendly GUI. Also a powerful Python API for network test automation....
-

 235Ransomware
235RansomwareNew Anatova Ransomware Encrypt the Users Data & Demands $700 USD Per User to Unlock the Files
Researchers discovered new Anatova Ransomware which is called as modular ransomware that encrypt users data with new techniques and demands $700 to...
-

 209Ransomware
209RansomwareA new Ransomware Anatova Which Hides as Game or Application
A new Ransomware called Anatova has been discovered in a private peer to peer network which is believed to be a very...
-

 260Malware
260MalwareAnatova: The new ransomware infecting hundreds of devices around the world
This new and sophisticated malicious software is able to bypass the best security measures A new ransomware family discovered at the beginning...
-

 263Hacked
263HackedKeyboard Attack “Thermanator” Steals Your Passwords Using Body Heat
Remember the movie “Mission Impossible” where the protagonist, Tom Cruise bypassed a security system using body heat signatures left on the keyboard? Well,...
-
 913Cyber Attack
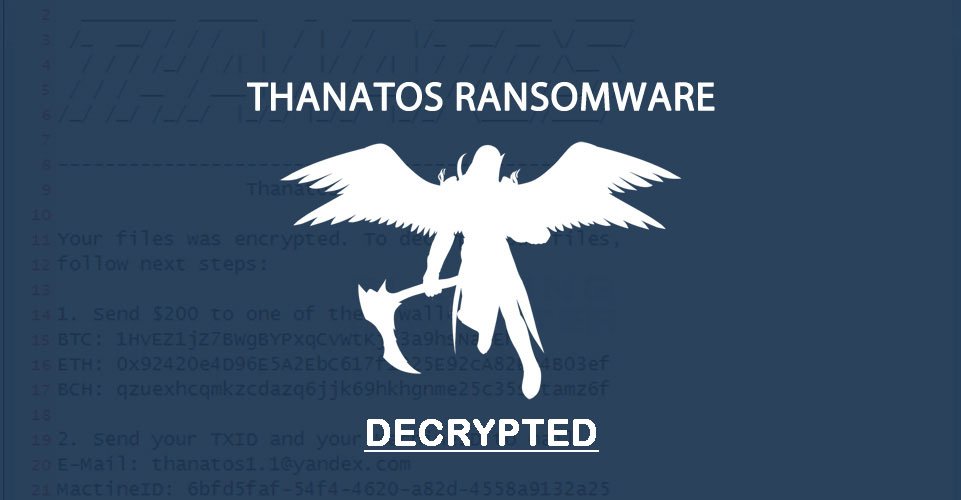
913Cyber AttackFree Thanatos Ransomware Decryption Tool Released
If your computer is infected with Thanatos Ransomware and you are looking for a free Thanatos ransomware decryption tool to unlock or...
-
 260Exploitation Tools
260Exploitation ToolsTerminator – Metasploit Payload Generator
Terminator Metasploit Payload Generator. Payload List : Binaries Payloads 1) Android 2) Windows 3) Linux 4) Mac OS Scripting Payloads 1) Python...
-

 208Hacked
208HackedCops Can Track Your Phone “Within Seconds” — Senator Wants To Know Why
We might have a hint, but we never let our brain trick us into the fact that real-time tracking has made way...
-

 265News
265NewsSmartphones of NATO Soldiers Compromised By Russian Hackers
North Atlantic Treaty Organization, which is universally famous as NATO, has been targeted by none other but the country that is a...
-
 304News
304NewsNATO wants to respond to Petya Ransomware Attack
Following the massive raid on Eastern Europe last week, researchers are reaching a consensus that the incident was cyber attack for political...
-

 167Incidents
167IncidentsSan Bernardino iPhone Hack: U.S. Senator Reveals How Much the FBI Spent on It
Despite the information being deemed classified, the number is now out thanks to Senator Feinstein’s mistake. The FBI won’t reveal how exactly...
-
 282Geek
282GeekLinux Lexicon — Anatomy Of A Man Page
Short Bytes: Software man pages and documentation can be thick and difficult enough for any beginner without the cryptic conventions laced with every...
-

 299News
299NewsAnatomy of a Crypto-Ransomware attack
Ransomware is a type of malware that forces its victims to pay the ransom through certain online payment methods in order to...
-

 260News
260NewsAzerbaijani Hackers Deface NATO-Armenia, Embassy Websites in 40 Countries
Azerbaijani Hackers have hacked NATO-Armenia and embassy websites in 40 countries giving a powerful reply to the Armenian hackers. The cyber war between...
-
 341Hacked
341HackedThe Anatomy of Copyright Lawsuits – Number Of People Sued Drops By 84% Since 2010
Image: Wtamu.edu Short Bytes: A report published by Mathew Sag claims that the number of people sued for illegal file sharing in...






