Search results for "PDF"
-
 3.1KMalware
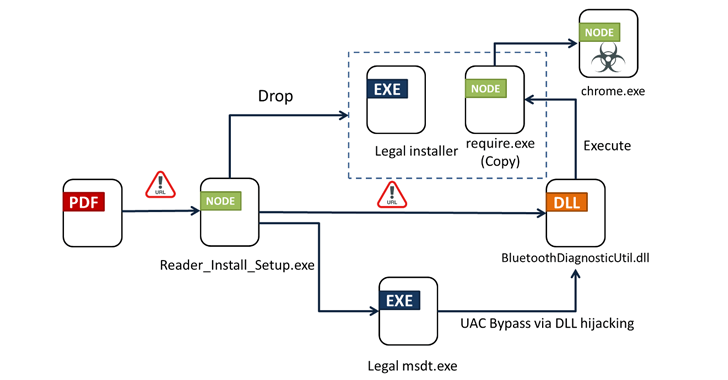
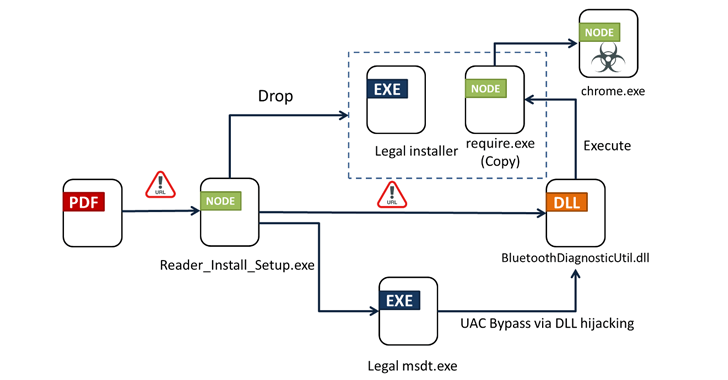
3.1KMalwareFrom PDFs to Payload: Bogus Adobe Acrobat Reader Installers Distribute Byakugan Malware
Bogus installers for Adobe Acrobat Reader are being used to distribute a new multi-functional malware dubbed Byakugan. The starting point of the...
-
 3.4KMalware
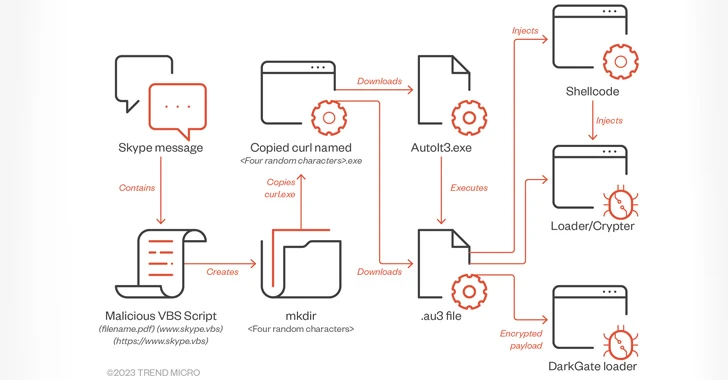
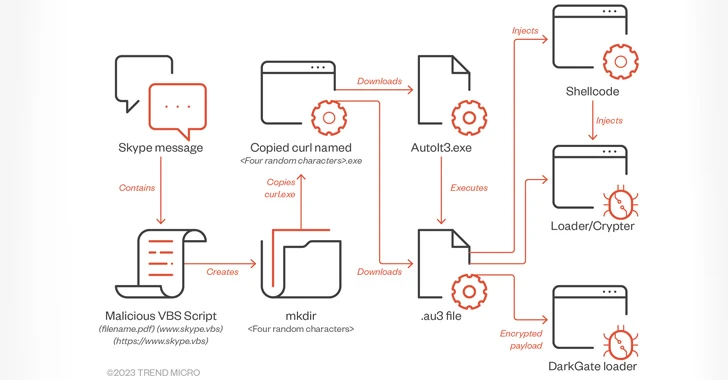
3.4KMalwareDarkGate Malware Spreading via Messaging Services Posing as PDF Files
A piece of malware known as DarkGate has been observed being spread via instant messaging platforms such as Skype and Microsoft Teams....
-
 1.3KMalware
1.3KMalwareWeaponized Excel, OneNote, or PDF Attachments Deliver New WikiLoader Malware
The Italian organizations, including tax agencies, were targeted by a new malware downloader delivering banking Trojan. The new loader malware is presently...
-
 5.1KMalware
5.1KMalwarePDF Malware Distribution Has Increased by 500%, as Reported by VirusTotal
A new edition of the “VirusTotal Malware Trends Report” series, which focuses mostly on “Emerging Formats and Delivery Techniques,” has been published...
-

 932Malware
932MalwareGuLoader Malware is Attacking Law Firms Using Weaponized PDF File
The cybersecurity researchers at Morphisec Labs have been tracking the GuLoader campaign since April of this year and found that it has...
-
 4.3KData Security
4.3KData SecurityExploit code for remotely executing code on victim device exploiting Foxit PDF Reader Vulnerability
Researchers from HackSys Inc. have provided further information on a security issue in the code execution of Foxit PDF Reader. On vulnerable...
-

 1.6KVulnerabilities
1.6KVulnerabilitiesFollina, Microsoft Office vulnerability, also affects Foxit PDF Reader; no patches available
A few days ago, a security researcher reported the detection of a zero-day vulnerability in Microsoft Office that could be exploited using...
-

 2.6KTutorials
2.6KTutorialsHow to perform digital forensics of malicious PDF files? Easily checking if a PDF document has malware or backdoors
The PDF format has become one of the most popular ways to view files, as this format is compatible with all kinds...
-

 5.2KVulnerabilities
5.2KVulnerabilities18 critical vulnerabilities discovered in Foxit PDF Reader and Foxit PDF Editor. Update your software quickly
Cybersecurity specialists reported the finding of multiple vulnerabilities in Foxit PDF Reader and Foxit PDF Editor, two popular tools for viewing and...
-

 2.5KVulnerabilities
2.5KVulnerabilitiesPDF certification process is vulnerable to new attack variants; flaws affect Adobe, Foxit and other PDF tools
A recent research states that certified PDF files are not protected enough, so they are vulnerable to various types of cyberattack. These...
-
 2.9KHow To
2.9KHow To5 PDF Tricks You Should Know To Improve Document Productivity
Portable Document Format (PDF) is already by default one of the best formats when it comes to documents. The reasons are simple. One...
-

 515Vulnerabilities
515VulnerabilitiesFoxit Reader Vulnerability Let Hackers Run Malicious Code via PDFs
Aleksander Nikolic, the security expert of Cisco Talos has recently detected a vulnerability that is continuously targeting the “Foxit Reader.” However, Foxit...
-

 4.1KHow To
4.1KHow ToEditing Text in a PDF File
Computer users come across PDF files almost every day. However, many of them didn’t know that it is possible to edit the...
-

 3.3KTutorials
3.3KTutorialsHow to easily check if DOC, RTF, XLS, PPT, PPTX or PDF file has a malware without antivirus like a digital forensics expert
In most cyberattack variants threat actors use legitimate-looking documents loaded with malware, which is why researchers often say it all starts with...
-
 434Malware
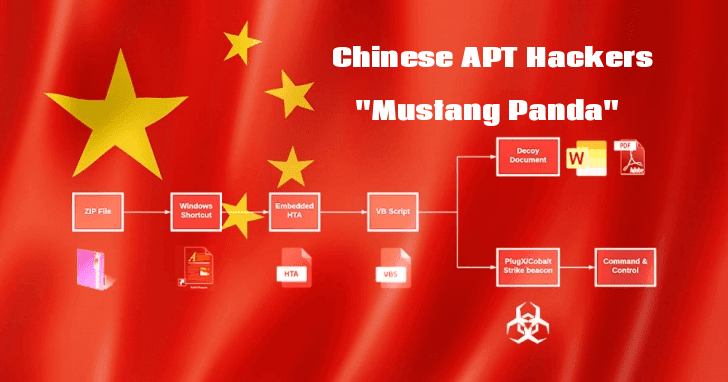
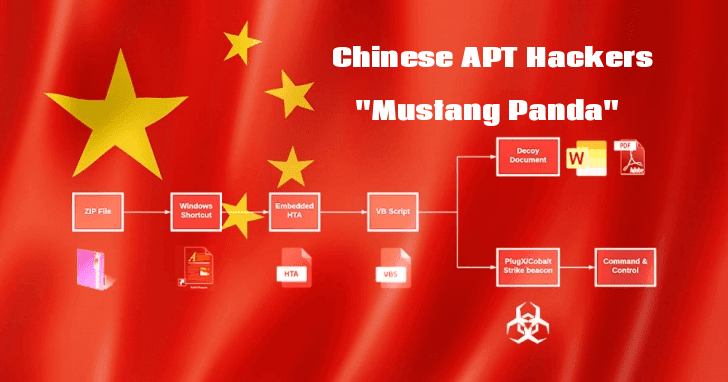
434MalwareChinese APT Hackers “Mustang Panda” Attack Public & Private Sectors Using Weaponized PDF and Word Documents
Researchers discovered an ongoing malware campaign that believed to be operating by a Chinese based threat group called “Mustang Panda” that targets...
-

 271Vulnerabilities
271VulnerabilitiesCritical Foxit PDF Reader Vulnerabilities: Update as soon as possible
A team of web application security experts has discovered multiple security vulnerabilities in Foxit PDF Reader, one of the most popular PDF...
-

 416Data Security
416Data SecurityPassword-protected PDFs are not enough to secure sensitive documents. No solutions available
Any deployment, no matter its protections, may be exposed to further hacking attacks. Ethical hacking experts have found a way to extract...
-

 606Lists
606ListsBest Free PDF Editors In 2019 To Edit And Annotate PDFs
Whether you work in an office or a college pursuing individual, PDFs are a commonly used file format. While PDF files are...
-
 523Lists
523Lists6 Best Free PDF Readers For Mac To Use In 2019
Portable Document Format or PDF is one of the most commonly used file types owing to its compatibility with different operating systems...
-

 466Data Breach
466Data BreachFoxit PDF Software Company Suffers Data Breach—Asks Users to Reset Password
If you have an online account with Foxit Software, you need to reset your account password immediately—as an unknown attacker has compromised...
-

 417Hackers Repository
417Hackers Repository50 Free Hacking Ebooks Collection PDF 2019 – HackingVision
50 Free Hacking Ebooks Collection PDF 2019 Ethical Hacking, Hacking ebooks pdf, Hacking ebooks free download, hacking ebooks collection, Best Hacking eBooks....






