Search results for "PDF"
-
 344Malware
344MalwareBeware!! 100 Million Users Downloaded CamScanner PDF App Drops a Malware in Android Phone
Its time to uninstall the CamScanner App from your Android Phone. Yes, dangerous malware component found in popular phone PDF creator app...
-

 411Malware
411MalwareMalware-as-a-service – Adwind Malware Attack Utilities Industry Via Weaponized PDF File
Researchers discovered a new wave of a phishing campaign that bypassing the Microsoft APT protection and delivery the Adwind malware via weaponized...
-
 321Malware
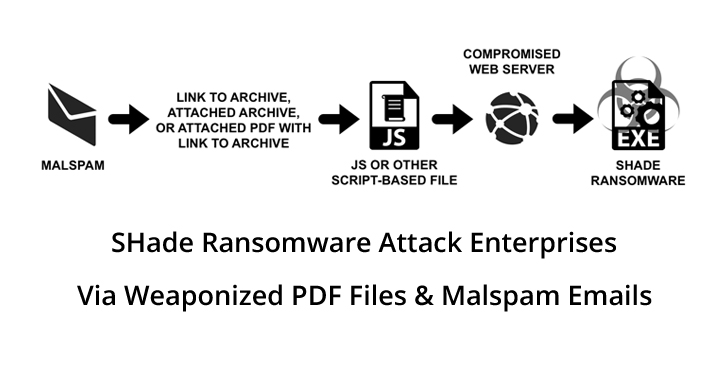
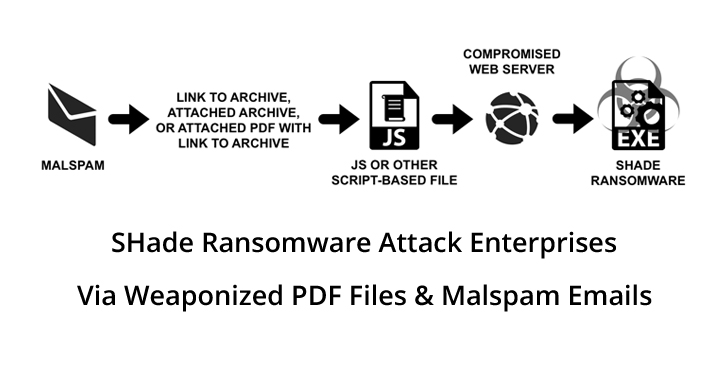
321MalwareShade Ransomware Attack Enterprise Networks through Weaponized PDF Files & Malspam Emails
Shade Ransomware emerged in late 2014; it includes malicious spam emails or exploits kits as their primary attack vectors. In a recent...
-

 495Lists
495Lists10 Best Free PDF Editors Online Reviewed For 2019
Achieving a productivity boost shouldn’t be a hassle for anyone in 2019, therefore I have created a list of the best free...
-

 241Malware
241MalwareHackers Distributing Malware Via Weaponized PDF & MS Word Version of New Zealand Terror Suspect’s Manifesto
Cyber Criminals launching a new malware via weaponized PDF & MS Word Version of New Zealand terror suspect’s manifesto. Researchers noticed 8chan,...
-
 410Malware
410MalwareHackers Exploit Google Chrome Zero-day using Weaponized PDF – If PDF Viewed in Chrome
Researchers discovered a new malicious PDF sample that has an ability to exploit the Google Chrome zero-day flaw when victims using Chrome...
-
 353Hackers Repository
353Hackers RepositoryKali Linux CTF Blueprints PDF eBook Cameron Buchanan
Kali Linux CTF Blueprints PDF eBook Cameron Buchanan Download Kali Linux CTF Blueprints PDF eBook Cameron Buchanan (Author) About This...
-

 351Data Security
351Data SecurityA new malware using Google App Engine to create malicious PDF files
Cobalt Strike malicious hackers group is abusing Google App Engine to distribute malware embedded in PDF documents Network security and ethical hacking...
-

 454Malware
454MalwareHackers Using Google Cloud Computing Platform To Deliver Targeted Malware Attacks via Weaponized PDF
Threat actors using Google computing platform (GCP) to deliver the malware through malicious PDF files. The attack targeting governments and financial firms...
-
 279Malware
279MalwareHackers Now Launching Powerful Weaponized PDF Exploit using Steganography Technique
Cyber Criminals now using new Stenography technique to distribute a powerful Obfuscated PDF exploit in order to compromise the targets and evade...
-

 367Geek
367GeekHackers abusing Google App Engine to spread PDF malware
The Cobalt Strike advanced persistent threat (APT) group is using Google App Engine to spread PDF malware against financial firms. The IT security researchers at Netskope have...
-

 414Lists
414Lists10 Best PDF Reader Apps For iPhone & iPad | View And Edit PDFs In 2019
Portable Document Format or PDF is one of the most widely used file formats today. A majority of ebooks online exist in...
-
 280Malware
280MalwareAndroid Malware Delivered Through Malicious PDF Attachments Collects Phone Numbers
A new campaign that delivers malicious PDF file that leads to download the file malicious APK file to the user’s device. Quick...
-
 193eBooks
193eBooksThe Little Black Book of Computer Virus PDF
The Little Black Book of Computer Viruses by Mark Ludwig The Little Black Book of Computer Viruses has seen five good years...
-
 188eBooks
188eBooksGray Hat Python PDF eBook
Gray Hat Python PDF eBook Gray Hat Python PDF eBook Download Python is fast becoming the programming language of choice for hackers,...
-
 190eBooks
190eBooksBegin Ethical Hacking with Python eBook PDF
Begin Ethical Hacking with Python Disclaimer The contributor(s) cannot be held responsible for any misuse of the data. This repository is just...
-
 225eBooks
225eBooksAdvanced Penetration Testing Hacking 2017 eBook PDF
Advanced Penetration Testing Hacking 2017 Disclaimer The contributor(s) cannot be held responsible for any misuse of the data. This repository is just...
-
 468Lists
468Lists8 Best Online PDF To Word Converters You Can Use in 2018
Portable Document Format or PDF is one of the most popular file formats in offices and the corporate world mainly because of...
-
 354Malware
354MalwareBeware!! Hackers Now Spreading Dangerous FlawedAmmyy Malware Through PDF & IQY File
Cyber criminals now using IQY Files as a new technique for spreading dangerous FlawedAmmyy malware which is a dangerous backdoor tool that...
-

 337Vulnerabilities
337VulnerabilitiesFoxit PDF Reader fixes serious remote code execution vulnerability
Users of the PDF reader Foxit must upgrade their software to Reader 9.3 and Foxit PhantomPDF 9.3 to correct over 100 flaws...
-

 170Malware
170MalwareEvil Clone Attack – Hackers Injecting Crypto-mining Malware into Legitimate PDF Software
Cybercriminals using a new type of attack called Evil clone to inject Cryptocurrency malware into legitimate PDF software to Mine cryptocurrency with...






