Search results for "hacking"
-

 1.7KMalware
1.7KMalwareFinland Blames Chinese Hacking Group APT31 for Parliament Cyber Attack
The Police of Finland (aka Poliisi) has formally accused a Chinese nation-state actor tracked as APT31 for orchestrating a cyber attack targeting...
-
 3.2KData Security
3.2KData SecurityHacking Debian, Ubuntu, Redhat& Fedora servers using a single vulnerability in 2024
The recent discovery of a significant flaw in the GNU C Library (glibc), a fundamental component of major Linux distributions, has raised...
-
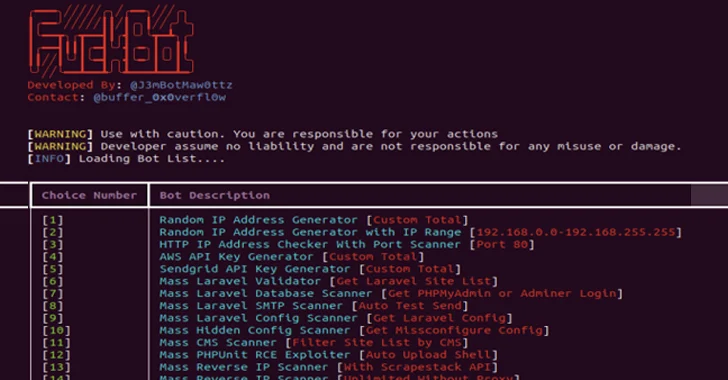
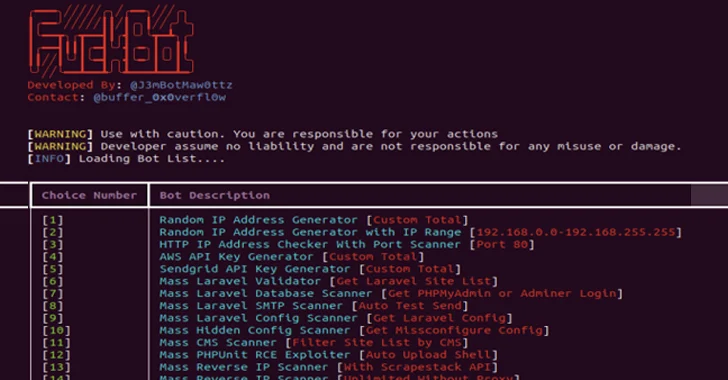 532Malware
532MalwareNew Python-based FBot Hacking Toolkit Aims at Cloud and SaaS Platforms
A new Python-based hacking tool called FBot has been uncovered targeting web servers, cloud services, content management systems (CMS), and SaaS platforms...
-
 492Tutorials
492Tutorials11 ways of hacking into ChatGpt like Generative AI systems
In the rapidly evolving landscape of artificial intelligence, generative AI systems have become a cornerstone of innovation, driving advancements in fields ranging...
-

 887Data Security
887Data SecurityBypassing pfSense firewall and hacking into application server and firewall itself
Recent cybersecurity research has unveiled a critical vulnerability impacting over 1,450 pfSense servers, exposing them to potential remote code execution (RCE) attacks....
-
 955Vulnerabilities
955VulnerabilitiesHacking the Human Mind: Exploiting Vulnerabilities in the ‘First Line of Cyber Defense’
Humans are complex beings with consciousness, emotions, and the capacity to act based on thoughts. In the ever-evolving realm of cybersecurity, humans...
-

 1.7KData Security
1.7KData SecurityYour Google Cloud Security Might Be at Risk. Hacking GCP via Google Workspace flaw
In a startling revelation, Bitdefender, a leading cybersecurity firm, has disclosed a series of sophisticated attack methods that could significantly impact users...
-
 2.2KData Security
2.2KData SecurityHacking Debian 12, 13, Ubuntu 22.04, 23.04 & Fedora 37, 38 servers using a single vulnerability
The team at Qualys Threat Research Unit has unveiled a fresh vulnerability within the Linux operating system, allowing local attackers to escalate...
-

 4.9KVulnerabilities
4.9KVulnerabilitiesZero day vulnerabilities in Qualcomm chips allow hacking into billion mobile phones in world
Qualcomm recently issued warnings about three zero-day vulnerabilities within its GPU and Compute DSP drivers that are currently being exploited by hackers....
-

 1.9KData Security
1.9KData SecurityHacking Cisco Routers firmware and replacing it with a malicious firmware using this flaw
A notorious threat actor with presumed ties to the Chinese government, known as “BlackTech”, has reportedly been exploiting Cisco routers to infiltrate...
-

 2.4KVulnerabilities
2.4KVulnerabilitiesHacking Atlassian Bitbucket & Confluence Data Center with a vulnerability
Within the expansive domain of collaboration tools, Atlassian’s Bitbucket and Confluence emerge as prominent figures, bestowing their enabling capabilities onto many developers...
-
 1.0KData Security
1.0KData Security“Prompt injection”attack allows hacking into LLM AI chatbots like ChatGPT, Bard
A kind of attack known as prompt injection is directed against LLMs, which are the language models that are the driving force...
-
 1.2KData Security
1.2KData SecurityHacking Microsoft Azure Entra ID using a vulnerability in Microsoft Power Platform
Following the disclosure of a serious flaw in the Microsoft Power Platform, researchers in the field of information security are advising users...
-

 5.0KData Security
5.0KData SecurityHacking Tp-Link smart bulbs to control smart home and your life
The Internet of Things (IoT) is now experiencing its zenith and is quickly growing its capabilities. This is being accomplished through the...
-

 2.5KData Security
2.5KData SecurityThese four vulnerabilities allow remote ATMs hacking and stealing millions
It is possible to remotely hack ATMs by taking advantage of a number of vulnerabilities that have been found in the ScrutisWeb...
-
 3.5KData Security
3.5KData SecurityHacking PostgreSQL applications with a SQL Injection vulnerability
Those that work with databases on a regular basis will know that PostgreSQL is more than just a name. It has an...
-
 3.0KVulnerabilities
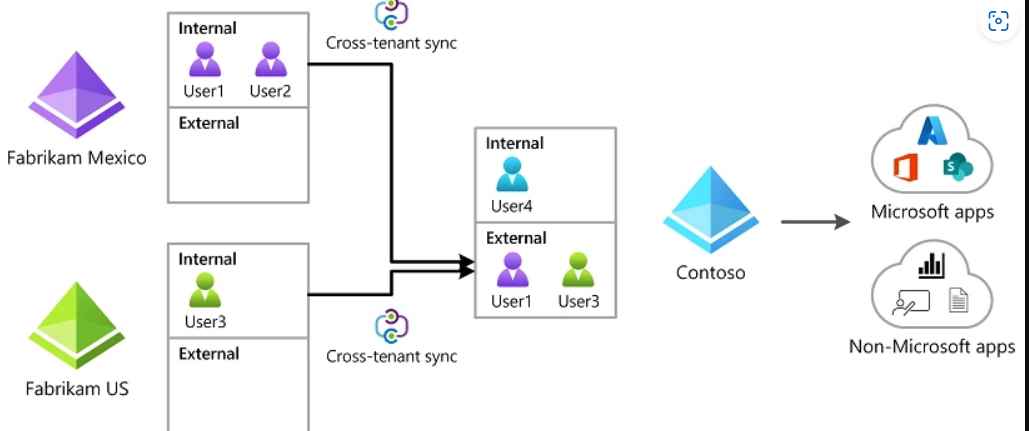
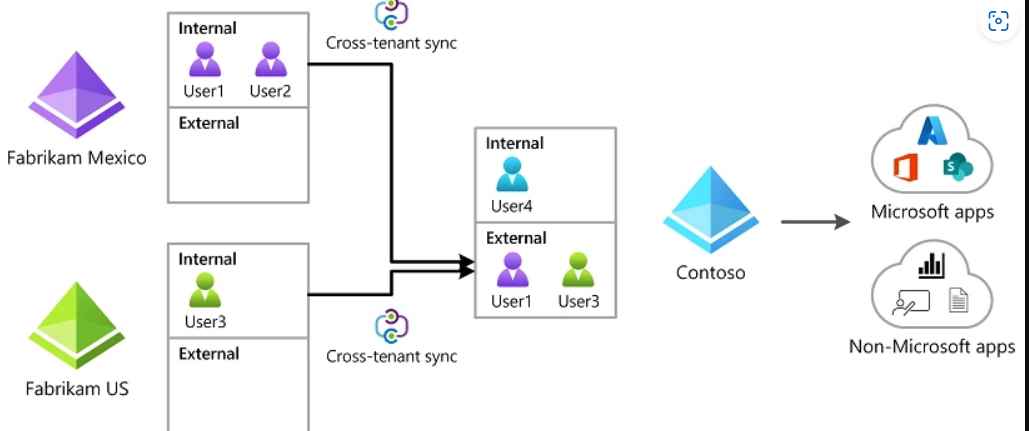
3.0KVulnerabilitiesNew Azure AD Cross-Tenant Synchronisation (CTS) Attack allows hacking tenants laterally
Attackers are still focusing their attention on Microsoft identities in the hopes of breaking into linked Microsoft apps and federated SaaS applications....
-

 695Vulnerabilities
695VulnerabilitiesHacking WordPress websites via vulnerabilities in Ninja Forms plugin
It has come to light that the Ninja Forms plugin for WordPress has many security flaws that might be abused by malicious...
-

 1.1KVulnerabilities
1.1KVulnerabilitiesCritical MikroTik RouterOS Vulnerability Exposes Over Half a Million Devices to Hacking
A severe privilege escalation issue impacting MikroTik RouterOS could be weaponized by remote malicious actors to execute arbitrary code and seize full...
-

 399Data Security
399Data SecurityHacking Encrypted Police and Military Radios exploiting 5 vulnerabilities
Global radios depend on the TETRA (Terrestrial Trunked Radio) standard, however a number of vulnerabilities have been found that have an influence...
-

 955Vulnerabilities
955VulnerabilitiesTwo serious zero-day vulnerabilities allow hacking iPhone, iPad and Mac
Recent news reports have brought attention to two serious zero-day vulnerabilities that pose a risk to the digital security of Apple products...






