Search results for "malware attacks"
-

 2.8KMalware
2.8KMalwareTA558 Hackers Weaponize Images for Wide-Scale Malware Attacks
The threat actor tracked as TA558 has been observed leveraging steganography as an obfuscation technique to deliver a wide range of malware...
-

 4.9KVulnerabilities
4.9KVulnerabilitiesCritical Flaws Leave 92,000 D-Link NAS Devices Vulnerable to Malware Attacks
Threat actors are actively scanning and exploiting a pair of security flaws that are said to affect as many as 92,000 internet-exposed...
-
 1.2KMalware
1.2KMalwareChinese Hackers Using Deepfakes in Advanced Mobile Banking Malware Attacks
A Chinese-speaking threat actor codenamed GoldFactory has been attributed to the development of highly sophisticated banking trojans, including a previously undocumented iOS...
-
 4.3KMalware
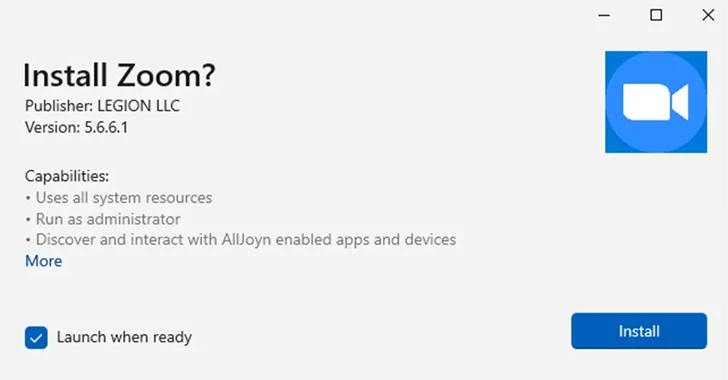
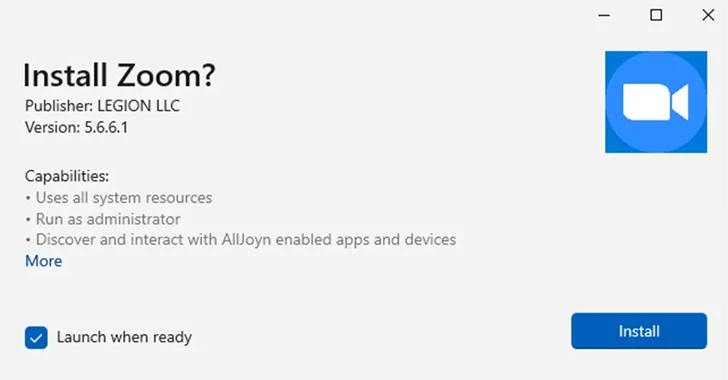
4.3KMalwareMicrosoft Disables MSIX App Installer Protocol Widely Used in Malware Attacks
Microsoft on Thursday said it’s once again disabling the ms-appinstaller protocol handler by default following its abuse by multiple threat actors to...
-

 591Malware
591MalwareLogoFAIL: UEFI Vulnerabilities Expose Devices to Stealth Malware Attacks
The Unified Extensible Firmware Interface (UEFI) code from various independent firmware/BIOS vendors (IBVs) has been found vulnerable to potential attacks through high-impact...
-

 4.5KCyber Attack
4.5KCyber AttackIranian Group Tortoiseshell Launches New Wave of IMAPLoader Malware Attacks
The Iranian threat actor known as Tortoiseshell has been attributed to a new wave of watering hole attacks that are designed to...
-
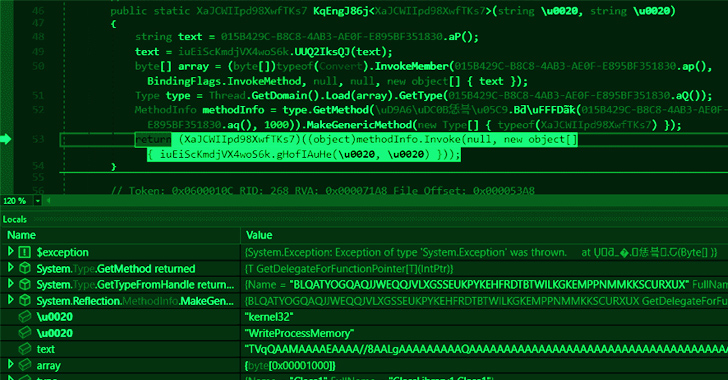
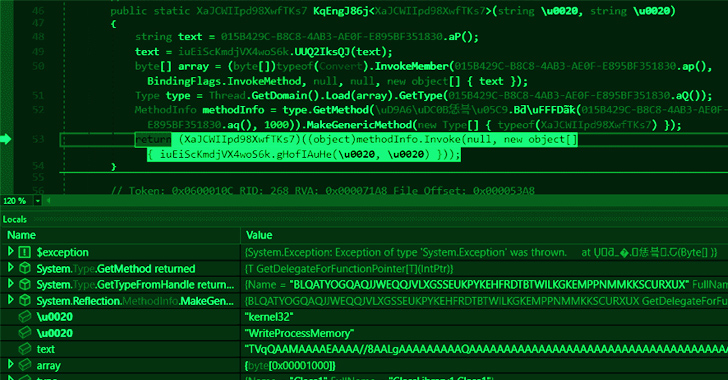 1.7KMalware
1.7KMalwareNew Attack Alert: Freeze[.]rs Injector Weaponized for XWorm Malware Attacks
Malicious actors are using a legitimate Rust-based injector called Freeze[.]rs to deploy a commodity malware called XWorm in victim environments. The novel...
-

 1.4KMalware
1.4KMalwareRust Infostealer Malware Attacks macOS Sonoma Ahead of Public Release
Based on recent reports, it was discovered that there has been info stealer malware that affects both Windows and macOS platforms. The...
-

 2.5KVulnerabilities
2.5KVulnerabilitiesCybersecurity Agencies Sound Alarm on Rising TrueBot Malware Attacks
Cybersecurity agencies have warned about the emergence of new variants of the TrueBot malware. This enhanced threat is now targeting companies in...
-

 2.4KMalware
2.4KMalwareNew Bandit Malware Attacks Browsers to Steal Personal & Financial Logins
Bandit Stealer, a recently discovered information stealer by Trend Micro, effectively targets cryptocurrency wallets and web browsers while skillfully avoiding detection. The...
-
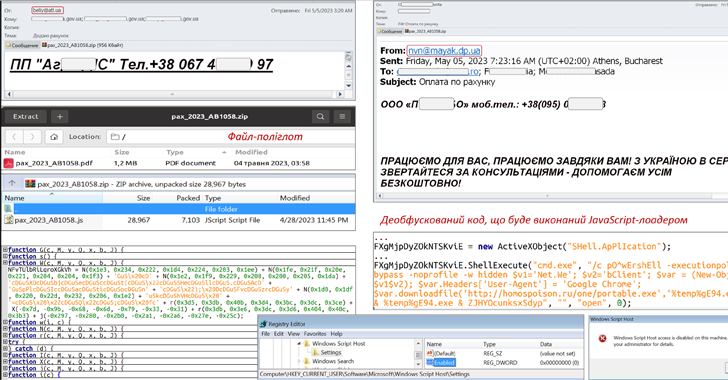
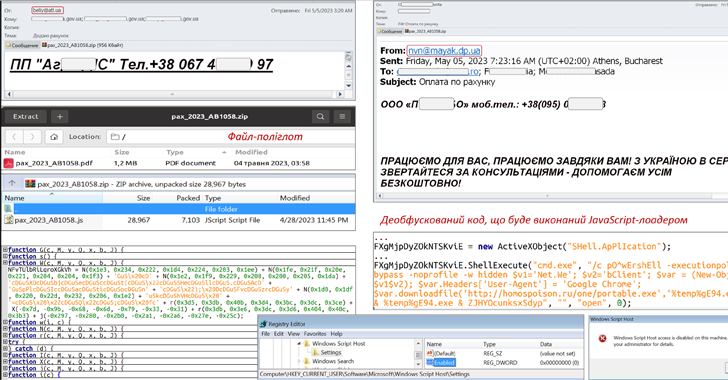 4.8KMalware
4.8KMalwareCERT-UA Warns of SmokeLoader and RoarBAT Malware Attacks Against Ukraine
An ongoing phishing campaign with invoice-themed lures is being used to distribute the SmokeLoader malware in the form of a polyglot file,...
-
 2.6KMalware
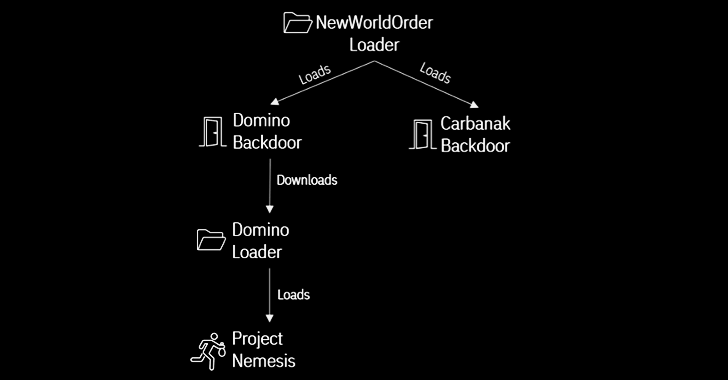
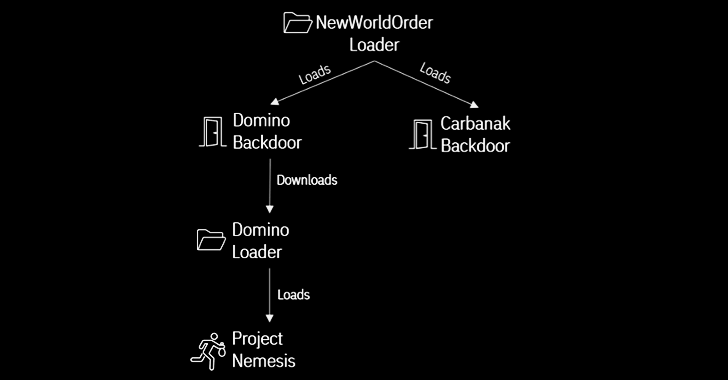
2.6KMalwareFIN7 and Ex-Conti Cybercrime Gangs Join Forces in Domino Malware Attacks
A new strain of malware developed by threat actors likely affiliated with the FIN7 cybercrime group has been put to use by...
-
 286Malware
286MalwareSamsung Introduces New Feature to Protect Users from Zero-Click Malware Attacks
Samsung has announced a new feature called Message Guard that comes with safeguards to protect users from malware and spyware via what’s...
-

 466Malware
466MalwareAustralian Healthcare Sector Targeted in Latest Gootkit Malware Attacks
A recent wave of Gootkit malware loader attacks has targeted the Australian healthcare sector by leveraging legitimate tools like VLC Media Player....
-
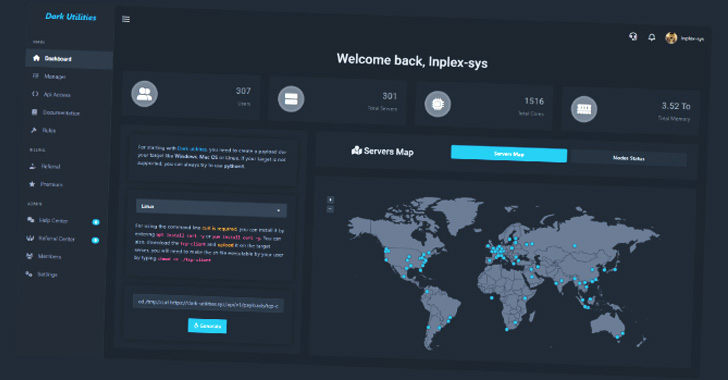
 3.8KMalware
3.8KMalwareA Growing Number of Malware Attacks Leveraging Dark Utilities ‘C2-as-a-Service’
A nascent service called Dark Utilities has already attracted 3,000 users for its ability to provide command-and-control (C2) services with the goal...
-

 4.5KMalware
4.5KMalwareVirusTotal Reveals Most Impersonated Software in Malware Attacks
Threat actors are increasingly mimicking legitimate applications like Skype, Adobe Reader, and VLC Player as a means to abuse trust relationships and...
-
 1.1KMalware
1.1KMalwareResearchers Find New Malware Attacks Targeting Russian Government Entities
An unknown advanced persistent threat (APT) group has been linked to a series of spear-phishing attacks targeting Russian government entities since the...
-

 1.6KMalware
1.6KMalware‘Purple Fox’ Hackers Spotted Using New Variant of FatalRAT in Recent Malware Attacks
The operators of the Purple Fox malware have retooled their malware arsenal with a new variant of a remote access trojan called...
-

 4.9KMalware
4.9KMalwareResearchers Link ShadowPad Malware Attacks to Chinese Ministry and PLA
Cybersecurity researchers have detailed the inner workings of ShadowPad, a sophisticated and modular backdoor that has been adopted by a growing number...
-

 3.3KMalware
3.3KMalwareMicrosoft Disables Internet Macros in Office Apps by Default to Block Malware Attacks
Microsoft on Monday said it’s taking steps to disable Visual Basic for Applications (VBA) macros by default across its products, including Word,...
-
 3.6KMalware
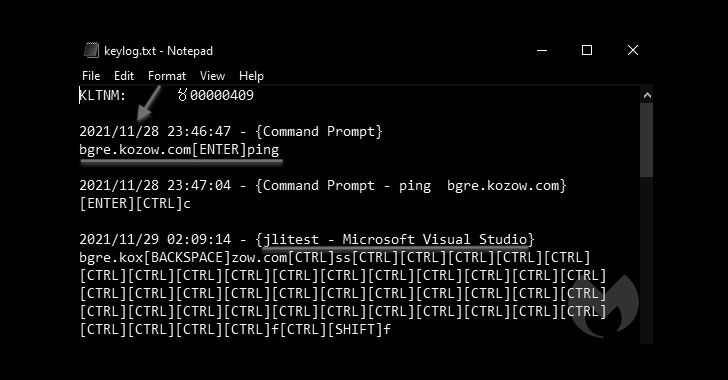
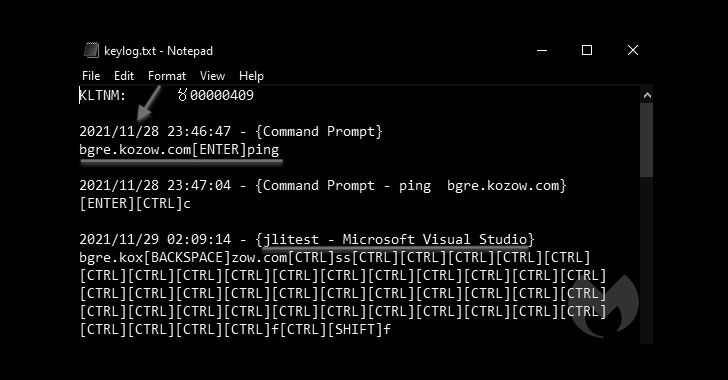
3.6KMalwareBADNEWS! Patchwork APT Hackers Score Own Goal in Recent Malware Attacks
Threat hunters have shed light on the tactics, techniques, and procedures embraced by an Indian-origin hacking group called Patchwork as part of...






