Search results for "malware attacks"
-
 4.0KMalware
4.0KMalwareNew Agent Tesla Malware Variant Using ZPAQ Compression in Email Attacks
A new variant of the Agent Tesla malware has been observed delivered via a lure file with the ZPAQ compression format to...
-

 2.6KMalware
2.6KMalwareDarkGate and PikaBot Malware Resurrect QakBot’s Tactics in New Phishing Attacks
Phishing campaigns delivering malware families such as DarkGate and PikaBot are following the same tactics previously used in attacks leveraging the now-defunct...
-
 3.4KMalware
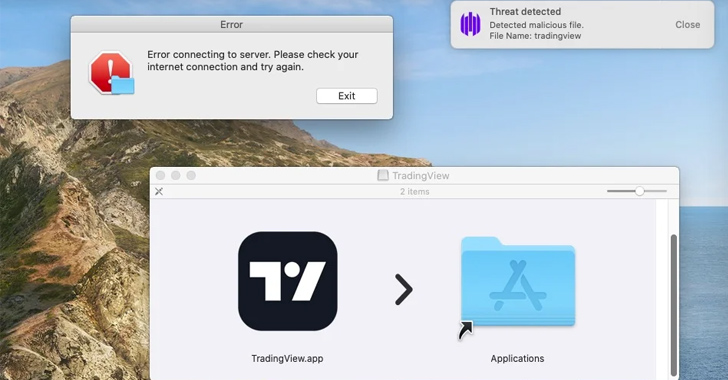
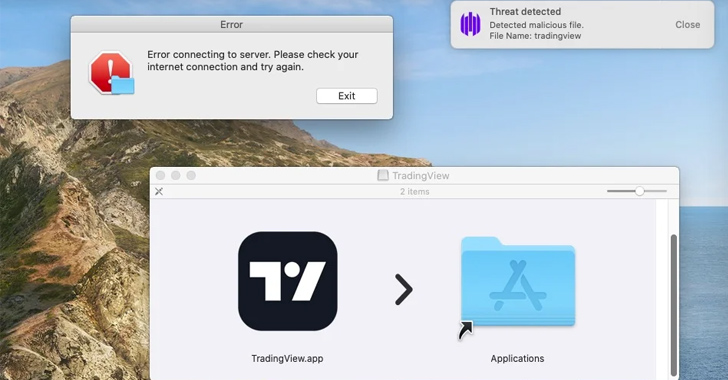
3.4KMalwareBeware: MetaStealer Malware Targets Apple macOS in Recent Attacks
A new information stealer malware called MetaStealer has set its sights on Apple macOS, making the latest in a growing list of...
-
 2.4KMalware
2.4KMalwarePicassoLoader Malware Used in Ongoing Attacks on Ukraine and Poland
Government entities, military organizations, and civilian users in Ukraine and Poland have been targeted as part of a series of campaigns designed...
-
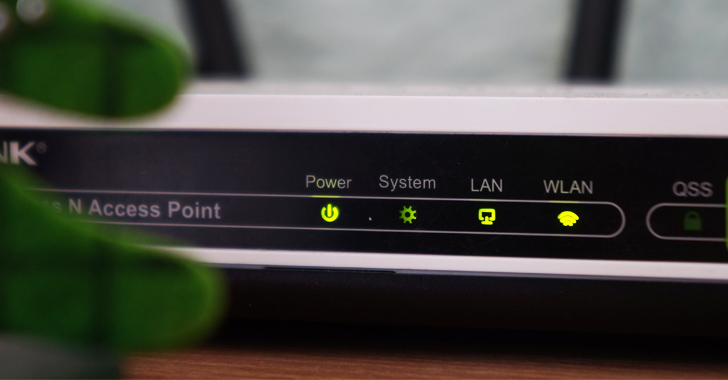
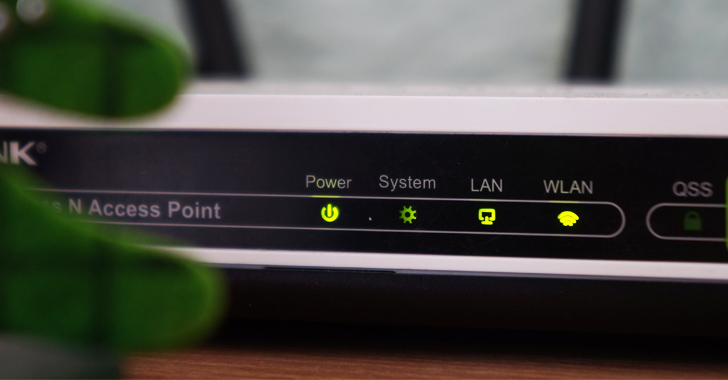 797Vulnerabilities
797VulnerabilitiesNew Condi Malware Hijacking TP-Link Wi-Fi Routers for DDoS Botnet Attacks
A new malware called Condi has been observed exploiting a security vulnerability in TP-Link Archer AX21 (AX1800) Wi-Fi routers to rope the...
-

 3.5KMalware
3.5KMalwareHackers Are Actively Using New Mystic Stealer Malware in Cyber Attacks
Recently, the cybersecurity researchers at CYFIRMA found that hackers are actively using “Mystic Stealer Malware,” a new information stealer. It’s been claimed...
-

 4.6KMalware
4.6KMalwareEvasive QBot Malware Leverages Short-lived Residential IPs for Dynamic Attacks
An analysis of the “evasive and tenacious” malware known as QBot has revealed that 25% of its command-and-control (C2) servers are merely...
-
 2.6KMalware
2.6KMalwareXWorm Malware Exploits Follina Vulnerability in New Wave of Attacks
Cybersecurity researchers have discovered an ongoing phishing campaign that makes use of a unique attack chain to deliver the XWorm malware on...
-
 3.6KCyber Attack
3.6KCyber AttackTonto Team Uses Anti-Malware File to Launch Attacks on South Korean Institutions
South Korean education, construction, diplomatic, and political institutions are at the receiving end of new attacks perpetrated by a China-aligned threat actor...
-
 1.3KMalware
1.3KMalwareCharming Kitten’s New BellaCiao Malware Discovered in Multi-Country Attacks
The prolific Iranian nation-state group known as Charming Kitten is actively targeting multiple victims in the U.S., Europe, the Middle East and...
-

 3.9KMalware
3.9KMalwareArid Viper Hacking Group Using Upgraded Malware in Middle East Cyber Attacks
The threat actor known as Arid Viper has been observed using refreshed variants of its malware toolkit in its attacks targeting Palestinian...
-
 3.0KMalware
3.0KMalwareGoBruteforcer: New Golang-Based Malware Breaches Web Servers Via Brute-Force Attacks
A new Golang-based malware dubbed GoBruteforcer has been found targeting web servers running phpMyAdmin, MySQL, FTP, and Postgres to corral the devices...
-
 1.7KMalware
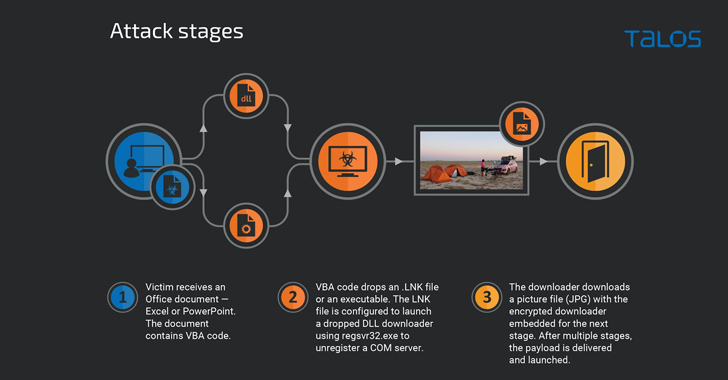
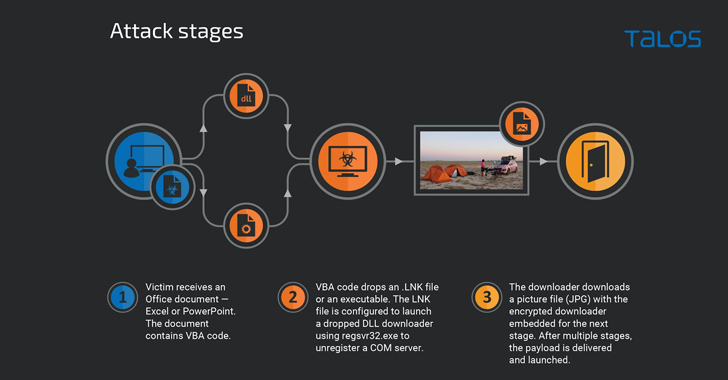
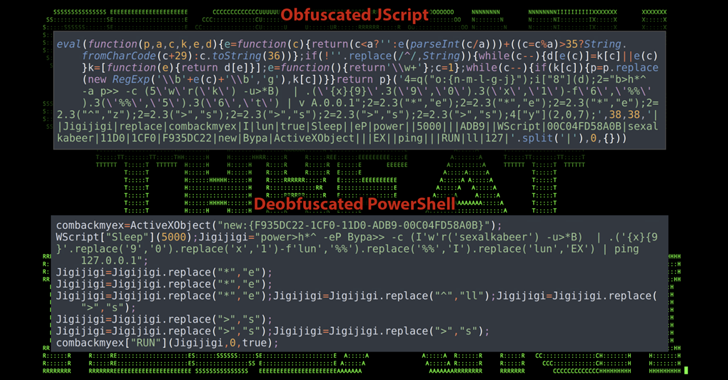
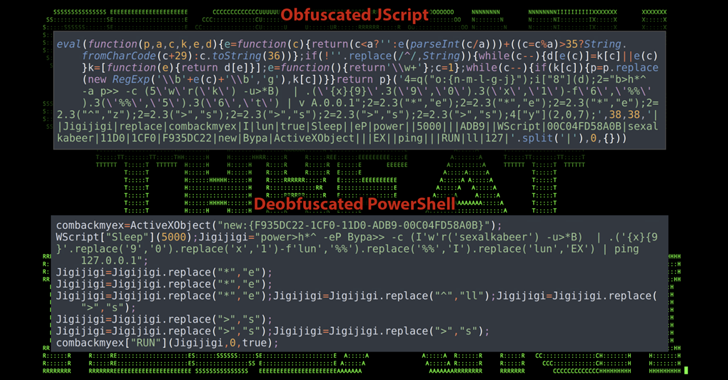
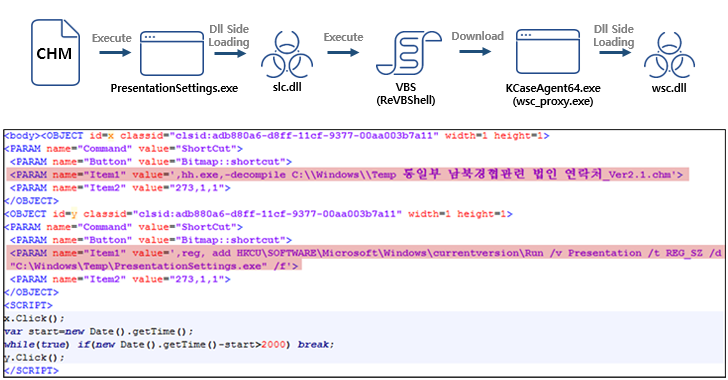
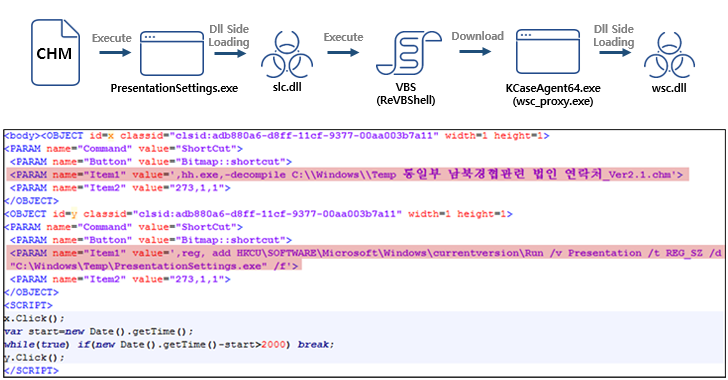
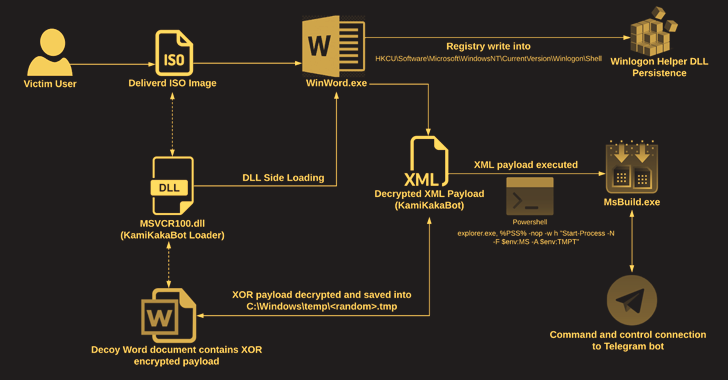
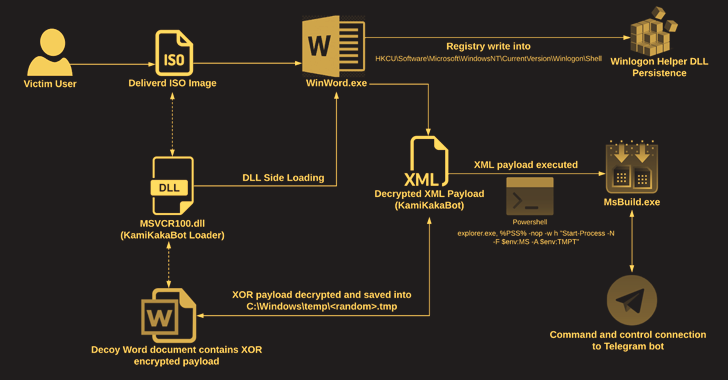
1.7KMalwareKamiKakaBot Malware Used in Latest Dark Pink APT Attacks on Southeast Asian Targets
The Dark Pink advanced persistent threat (APT) actor has been linked to a fresh set of attacks targeting government and military entities...
-

 4.6KCyber Attack
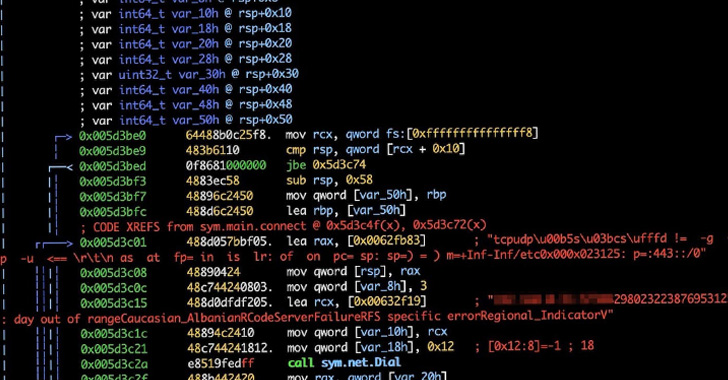
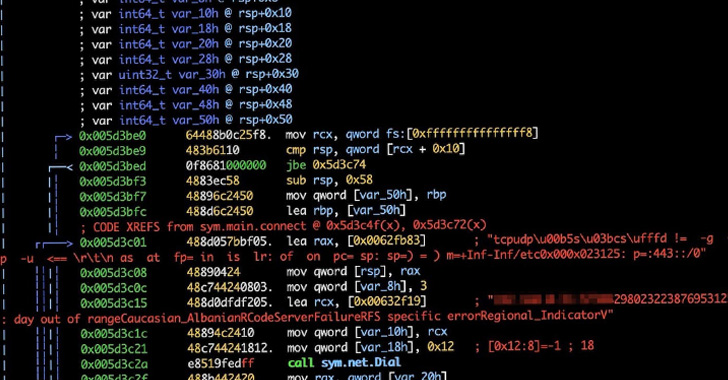
4.6KCyber AttackChinese Hackers Utilize Golang Malware in DragonSpark Attacks to Evade Detection
Organizations in East Asia are being targeted by a likely Chinese-speaking actor dubbed DragonSpark while employing uncommon tactics to go past security...
-
 2.3KMalware
2.3KMalwareNew KmsdBot Malware Hijacking Systems for Mining Crypto and Launch DDoS Attacks
A newly discovered evasive malware leverages the Secure Shell (SSH) cryptographic protocol to gain entry into targeted systems with the goal of...
-

 664Malware
664MalwareCyber Attacks Against Middle East Governments Hide Malware in Windows Logo
An espionage-focused threat actor has been observed using a steganographic trick to conceal a previously undocumented backdoor in a Windows logo in...
-

 2.4KMalware
2.4KMalwareHackers Launching Self-Spreading Malware To Attacks Gamers via YouTube
If you are a gamer and looking for cheats and cracks for games then you should be aware that YouTube has become...
-
 646Malware
646MalwareHackers Behind Cuba Ransomware Attacks Using New RAT Malware
Threat actors associated with the Cuba ransomware have been linked to previously undocumented tactics, techniques and procedures (TTPs), including a new remote...
-

 3.4KMalware
3.4KMalwareIranian Hackers Spotted Using a new DNS Hijacking Malware in Recent Attacks
The Iranian state-sponsored threat actor tracked under the moniker Lyceum has turned to using a new custom .NET-based backdoor in recent campaigns...
-
 2.5KCyber Attack
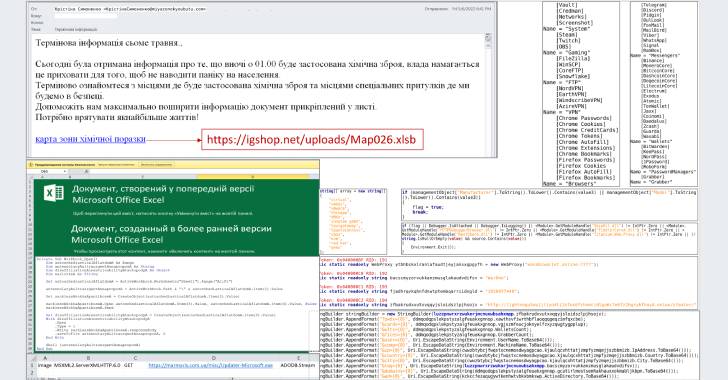
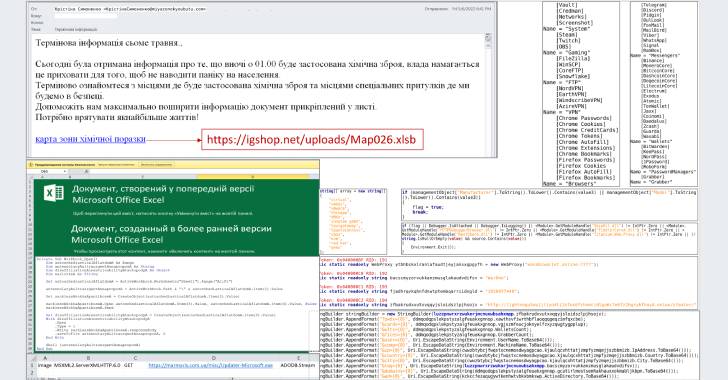
2.5KCyber AttackUkrainian CERT Warns Citizens of a New Wave of Attacks Distributing Jester Malware
The Computer Emergency Response Team of Ukraine (CERT-UA) has warned of phishing attacks that deploy an information-stealing malware called Jester Stealer on...
-

 461Malware
461MalwareThis new malware has a keylogger, ransomware and can perform DDoS attacks
Cybersecurity specialists report the detection of a new remote access Trojan (RAT) that, in addition to including the functions of this malware...






