Search results for "malware attacks"
-

 4.1KMalware
4.1KMalwareChina-linked Daxin Malware Targeted Multiple Governments in Espionage Attacks
A previously undocumented espionage tool has been deployed against selected governments and other critical infrastructure targets as part of a long-running espionage...
-

 947Cyber Attack
947Cyber AttackIran’s MuddyWater Hacker Group Using New Malware in Worldwide Cyber Attacks
Cybersecurity agencies from the U.K. and the U.S. have laid bare a new malware used by the Iranian government-sponsored advanced persistent threat...
-

 2.7KMalware
2.7KMalwareNew Wave of Cyber Attacks Target Palestine with Political Bait and Malware
Cybersecurity researchers have turned the spotlight on a new wave of offensive cyberattacks targeting Palestinian activists and entities starting around October 2021...
-
 4.0KMalware
4.0KMalwareTrickBot Malware Using New Techniques to Evade Web Injection Attacks
The cybercrime operators behind the notorious TrickBot malware have once again upped the ante by fine-tuning its techniques by adding multiple layers...
-
 1.4KNews
1.4KNewsRansomware, Trojans, DDoS Malware and Crypto-Miners Delivered in Log4Shell Attacks
Every single day, hundreds of thousands of internet users are victims of some form of cyberattack. The number of hackers is daily...
-
 3.5KMalware
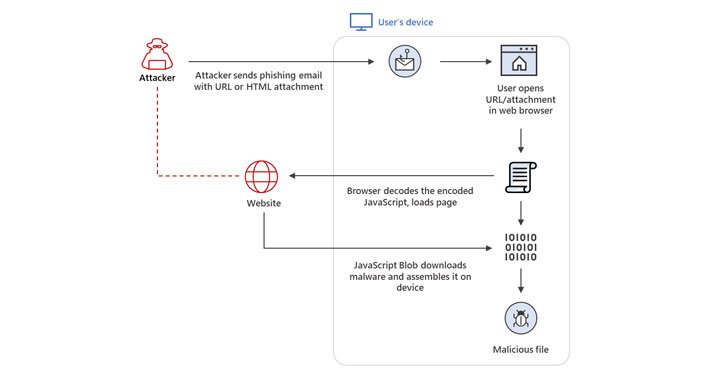
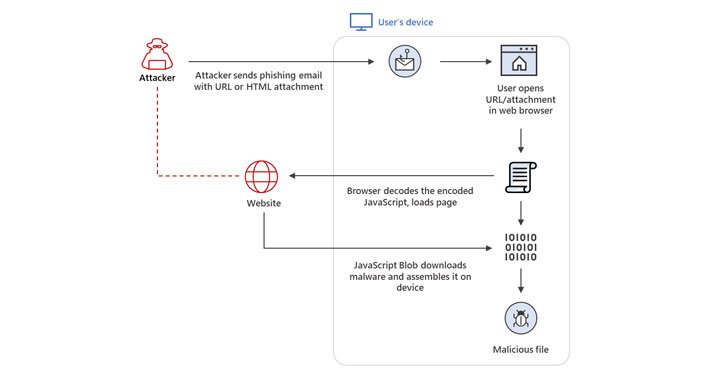
3.5KMalwareHackers Increasingly Using HTML Smuggling in Malware and Phishing Attacks
Threat actors are increasingly banking on the technique of HTML smuggling in phishing campaigns as a means to gain initial access and...
-
 2.1KMalware
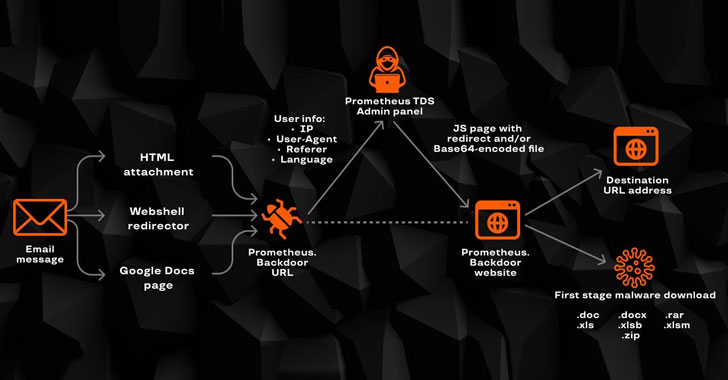
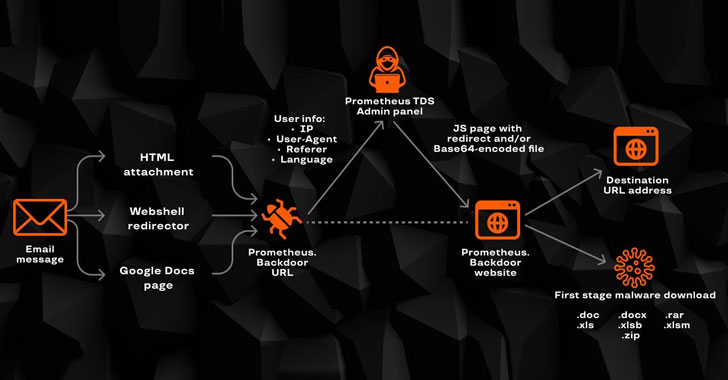
2.1KMalwareA Wide Range of Cyber Attacks Leveraging Prometheus TDS Malware Service
Multiple cybercriminal groups are leveraging a malware-as-a-service (MaaS) solution to carry out a wide range of malicious software distribution campaigns that result...
-
 1.4KCyber Attack
1.4KCyber AttackResearchers uncover a new Iranian malware used in recent cyberattacks
An Iranian threat actor has unleashed a new cyberespionage campaign against a possible Lebanese target with a backdoor capable of exfiltrating sensitive...
-
 2.8KMalware
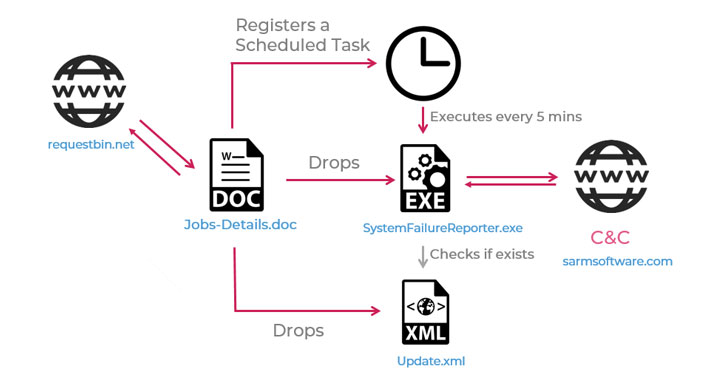
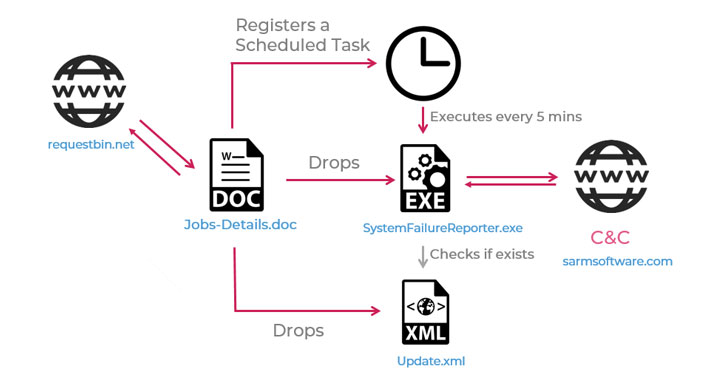
2.8KMalwareRaccoon Stealer Malware Delivered by .IMG File Attacks Financial Organization to Steal Sensitive Data
Malware authors continue to trick users abusing legitimate services, one recent example of this is the new campaign of Raccoon information-stealing malware....
-

 665Malware
665MalwareWinnti Hackers Group Launching New Malware via Supply-chain Attacks to Inject Backdoor in Windows
Researchers discovered a new malware campaign from the Winnti threat group that utilizes the supply-chain attacks with a new set of artifacts to...
-

 430Data Security
430Data SecurityMost SMB cybersecurity defence fail short to thwart malware & file-based attacks
29 percent of small to medium-sized businesses (SMBs) spend less than $1,000 for their IT security each year. This comes as a...
-

 429Malware
429MalwareIran retaliates against cyber warfare using dangerous malware and phishing attacks against LinkedIn users
The tension generated by the cyber warfare between the United States, and its allies, and Iran keeps growing. Although some information security...
-

 407Incidents
407IncidentsIran responds to US cyberattacks with malware that destroys IoT devices
Vulnerability testing specialists reported the emergence of a new malware variant capable of removing firmware from Internet of Things (IoT) devices. This...
-

 250Malware
250MalwarePlead malware distributed via MitM attacks at router level, misusing ASUS WebStorage
ESET researchers have discovered that the attackers have been distributing the Plead malware via compromised routers and man-in-the-middle attacks against the legitimate...
-

 341Malware
341MalwareHackers Using InfoStealer Malware that Attacks Windows Servers To Steal Sensitive Data
A new InfoStealer malware has been identified which targets the windows servers, stealing its sensitive data that includes the login credentials, OS...
-

 444Cryptocurrency
444CryptocurrencyCrypto Mining Malwares – One of the Most Practiced Attacks During 2018
Due to hard detection and easy execution of the attack, 2018 has seen excessive crypto mining malware. Cryptojacking attacks are based on...
-

 255Cryptocurrency
255CryptocurrencyPowerful Mobile Malware Rotexy Launched over 70,000 Attacks with Banking Trojan & Ransomware Modules
A new Mobile malware family called Rotexy, launched over 7000 attacks in wide within 3 months of the period from August to October...
-

 274Incidents
274IncidentsMalware campaign attacks freelancers
Attackers are spreading macros in a campaign aimed at users of freelance/occasional work platforms A new cyberattack campaign has specially focused on...
-
 389Malware
389MalwareDangerous PANDA Banking Malware Spreads Through Phishing Attacks Targets Banks, Cryptocurrency Sites and Social Media
The PANDA Malware first identified in the year 2016 by Fox IT, the malware primarily focused on banking sectors. With the last...
-

 366News
366NewsNew Android Malware Loapi Attacks Phones in Five Different Ways
Android phones have always remained the soft target of malicious threat actors since every now and then we hear about a new...
-

 279Incidents
279Incidents“Malware-free” attacks mount in big breaches, CrowdStrike finds
Stolen credentials, exploits of command-line tools used in 66 percent of attacks. Despite the rise of massive crypto-ransomware attacks, an even more...






