Data Security
-

 3.3K
3.3KChange these 20 passwords if you are using them in your accounts immediately
Are your passwords as secure as they can be? For many users, self-created passwords that are easy to remember are not as...
-
 1.7K
1.7KFTC sues a company that sells user location data and tracks their visit to fertility Clinics, temples, churches , and Other Sensitive Locations
The Federal Trade Commission launched a case against data broker Kochava on Monday, saying that the business sells geolocation data from hundreds...
-

 4.7K
4.7KMore than 80,000 Hikvision CCTV cameras exposed by a vulnerability
Security researchers have discovered over 80,000 cameras vulnerable to a critical command injection bug that can be easily exploited via messages sent...
-

 5.0K
5.0KMicrosoft shuts down over 1,400 email accounts and 531,000 URLs used by ransomware gang that collected stolen customer credentials
Microsoft has shut down more than 1,400 malicious email accounts used by cybercriminals to collect stolen customer passwords via ransomware in the...
-

 4.1K
4.1K“Half of Twitter’s roughly 7,000 full-time workers have complete access to its code and user confidential data” Says its former chief security officer Peiter Zatko
Twitter executives misled federal regulators and the company’s own board about “extreme and egregious shortcomings” in its defenses against hackers and its...
-
 2.4K
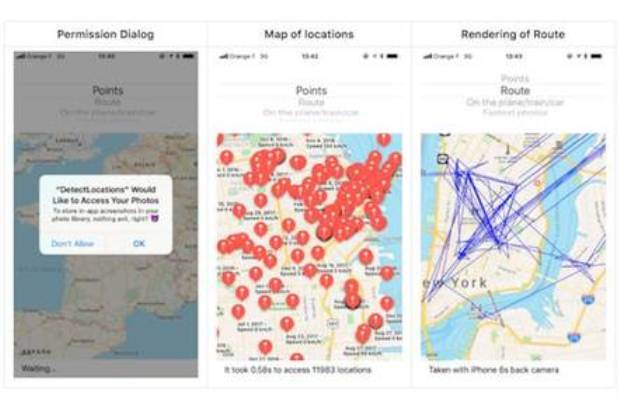
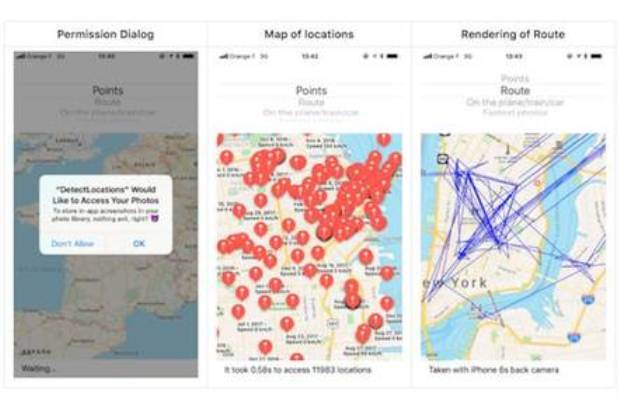
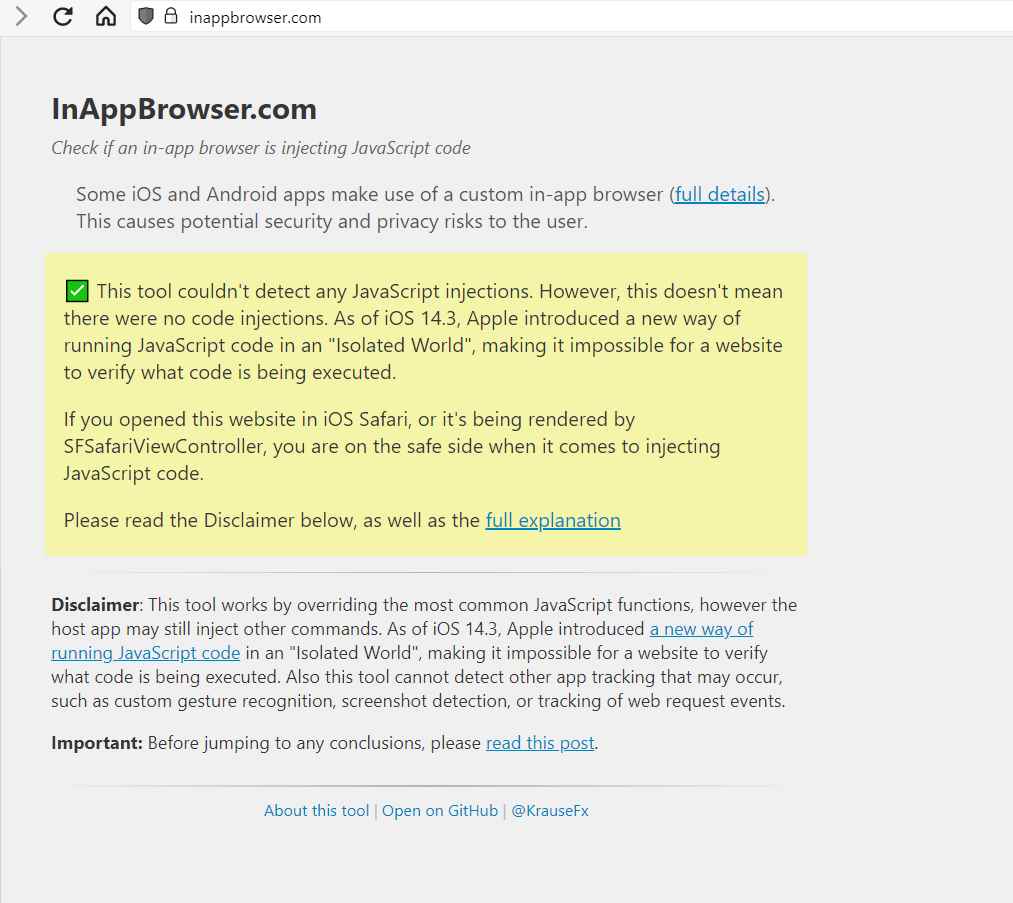
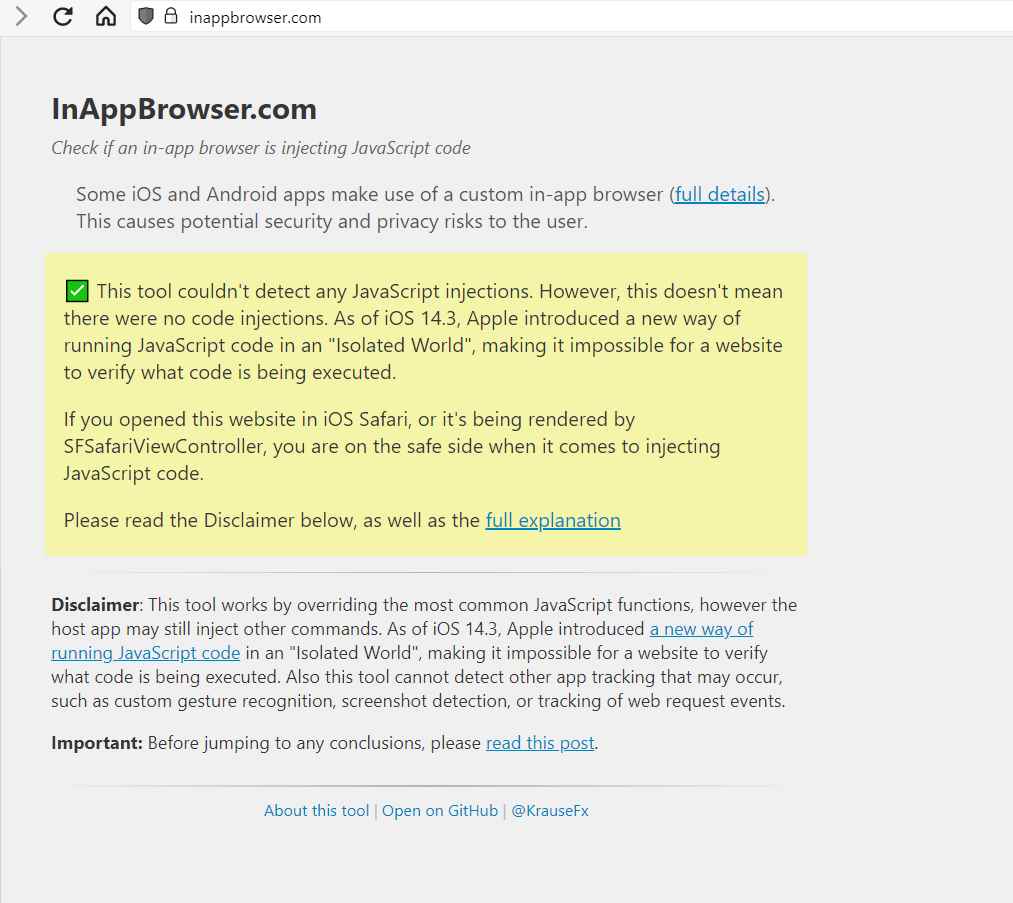
2.4KThis free tool easily lets you find if JavaScript code is being used in browser inside apps to track your activity
A researcher has created a free and open source tool that anybody can use to inspect what code is being injected by...
-

 4.5K
4.5KHow criminals are hacking key fobs to quickly and quietly steal cars
High-tech criminals are increasingly targeting push-start automobiles by hacking into key fobs, leaving many New Orleans car owners stranded according to WSDU...
-

 4.3K
4.3KNew ISO 27002:2022. The Swiss Army Knife of Security
They have kept us in suspense for a long time, but they finally published it in February of this year. The new...
-
 5.0K
5.0KElon Musk offers up to $25,000 to those who hack Starlink satellites
SpaceX has opened the door for investigative hackers to hack into Starlink, its satellite internet network. The company has also added that...
-
 2.4K
2.4KKali Linux 2022.3 released with new hacking tools and improved performance
We can say that Kali Linux is one of the most important distributions in terms of computer security. Now they have released...
-

 3.0K
3.0KSeifan: See the version of Pegasus spyware software designed just for Police
Details and screenshots of a version of the Pegasus spyware software designed for Israeli police were leaked. This spyware was referred to...
-

 876
876North Korean hackers found a new way to hack cryptocurrency companies by getting jobs there using fake resumes
North Koreans hackers are faking linkedin profiles and CVs and pretending to be cryptocurrency experts for getting full time or freelance remote...
-

 2.7K
2.7KThe average cost of a data breach increased 2.6% from $4.24 million in 2021 to $4.35 million in 2022
It is well known that the volume of security incidents has not stopped growing steadily for some years now. The cybercrime industry...
-

 5.1K
5.1KWindows enables default account lockout policy for RDP (Remote Desktop Protocol) to reduce ransomware attacks based on brute forcing RDP
Microsoft has chosen to add specific security measures against brute force attacks against RDP (Remote Desktop Protocol). These security improvements have been...
-
 4.5K
4.5KMICROSOFT MAKES THINGS HARDER FOR CYBER CRIMINALS BY DISABLING MACROS AGAIN BY DEFAULT IN OFFICE PRODUCTS
One of the attack methods that hackers can use is a simple Word document that they send in the mail. They use...
-

 1.4K
1.4KHow AitM attack was used to breach 10000 Organizations
Microsoft revealed on Tuesday that a large-scale phishing campaign targeted more than 10,000 organizations since September 2021 by attacking the Office 365...
-

 2.1K
2.1KNew Technique “SATAn” to hack Air-Gapped computers using SATA cables as Antenna
Cyber Security researchers at the Department of Software and Information Systems Engineering, Ben-Gurion University of the Negev, Israel, have discovered a new...
-

 3.5K
3.5KWhat is the Reverse QR social engineering attack and how to protect from it
A few days ago Spain police sighted a new type of scam that has been called Reverse QR Scam. A fraudulent technique...
-

 1.4K
1.4KNew version of Tor browser makes it easier for users to evade government attempts to block its use
We can say that the Tor browser is one of the most used when it comes to maintaining anonymity and privacy. It...
-

 2.7K
2.7KMICROSOFT MAKES THINGS EASIER FOR CYBER CRIMINALS BY ENABLING AGAIN MACROS BY DEFAULT IN OFFICE PRODUCTS
Microsoft has surprised key parts of the security community with its decision to quietly reverse course and allow untrusted macros to open...
-

 1.4K
1.4KRussian cyber army attempted to hack more than 128 organizations in 42 countries
Microsoft published an intelligence report on the Ukraine war that exposes Russia’s cyberattack strategy during the invasion. Brad Smith, president of the...






