Data Security
-

 1.6K
1.6KGoogle Agrees to Pay $29.5 Million to Settle Lawsuits Regarding the Tracking of Users’ Locations
In order to resolve two separate cases launched by the states of Indiana and the District of Columbia about the “deceptive” location...
-

 785
7857 Cybersecurity predictions & trends for 2023
At the beginning of the year 2022, there was a surge in employment opportunities within the technology industry. However, by the end...
-

 3.4K
3.4KWhat exactly is social engineering, and how can you safeguard yourself from becoming a victim of it?
In the world of cybercrime, social engineering refers to a method of manipulation that is used to collect sensitive information from people....
-
 3.5K
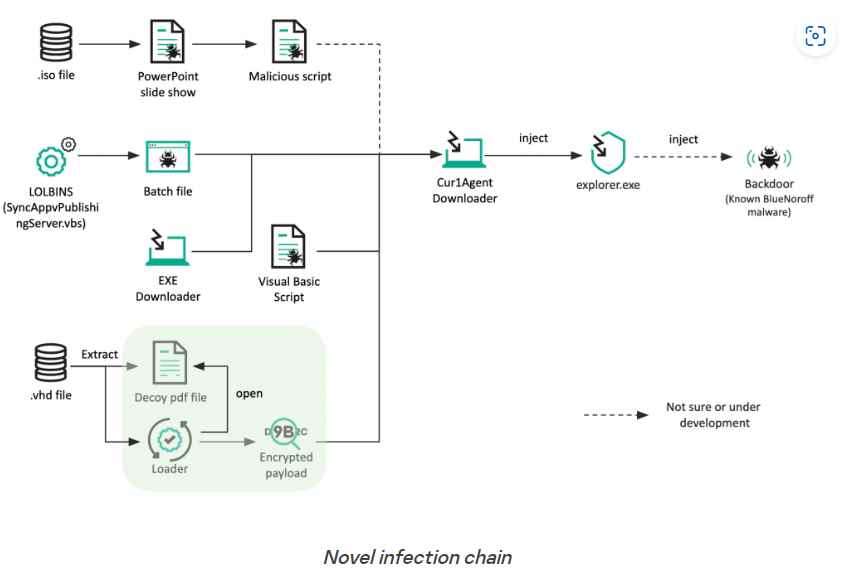
3.5KNew attack technique uses .ISO and .VHD file formats to bypass Windows MotW Security
BlueNoroff is a part of the infamous Lazarus Group, and it has been detected incorporating new strategies into its playbook. These new strategies...
-

 444
444Customers of Comcast Xfinity accounts getting hacked despite having 2FA enabled
On December 19th, several Xfinity email users started getting messages informing them that their account information had been updated. In spite of...
-

 4.1K
4.1KNew Microsoft Exchange exploit allows ransomware infection via ProxyNotShell vulnerability
Recent cyberattacks utilizing the Play ransomware were spotted targeting Exchange servers. These attacks used a novel exploit chain that circumvented the protections...
-

 1.4K
1.4KScammer behind the “OneCoin” cryptocurrency pyramid scheme, which included several billions of dollars, pleads guilty
At least nine persons, including Greenwood and Ignatova, have been charged with fraud in connection with OneCoin by the United States government...
-
 4.3K
4.3KExploit code for remotely executing code on victim device exploiting Foxit PDF Reader Vulnerability
Researchers from HackSys Inc. have provided further information on a security issue in the code execution of Foxit PDF Reader. On vulnerable...
-

 4.9K
4.9K8 social media influencers arrested for using Twitter & Discord to manipulate exchange-traded stocks and making $114 million
The Securities and Exchange Commission (SEC) has just announced that it will be filing charges against eight individuals in connection with a...
-

 873
873PCI Security Standards Council (PCI SSC) releases PCI Secure Software Standard v1.2
By offering industry-driven, adaptable, and efficient data security standards and programs that assist businesses in identifying, mitigating, and preventing cyberattacks and breaches,...
-

 3.2K
3.2KTor Browser 12.0 released with major changes
The most recent version of the Tor Browser is a specially packaged version of Firefox 102 ESR that automates the process of...
-
 1.9K
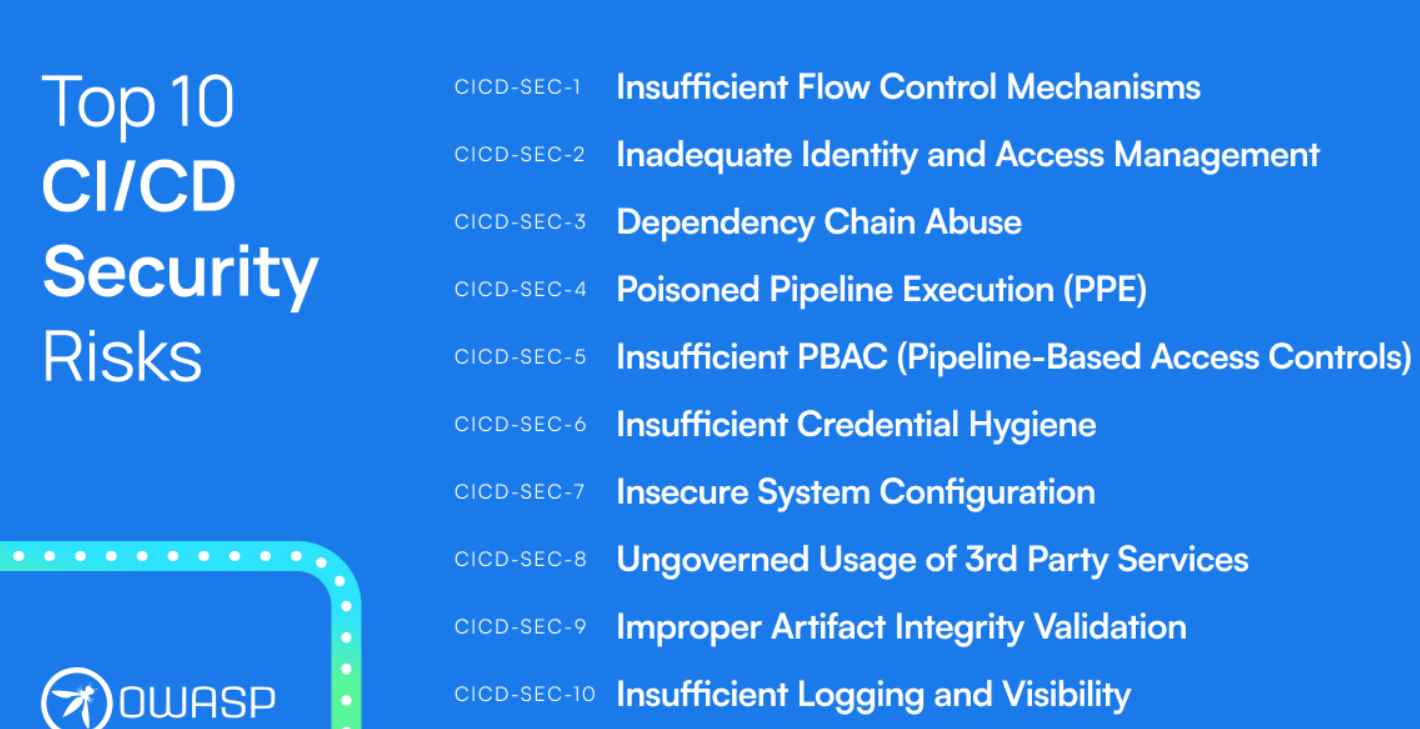
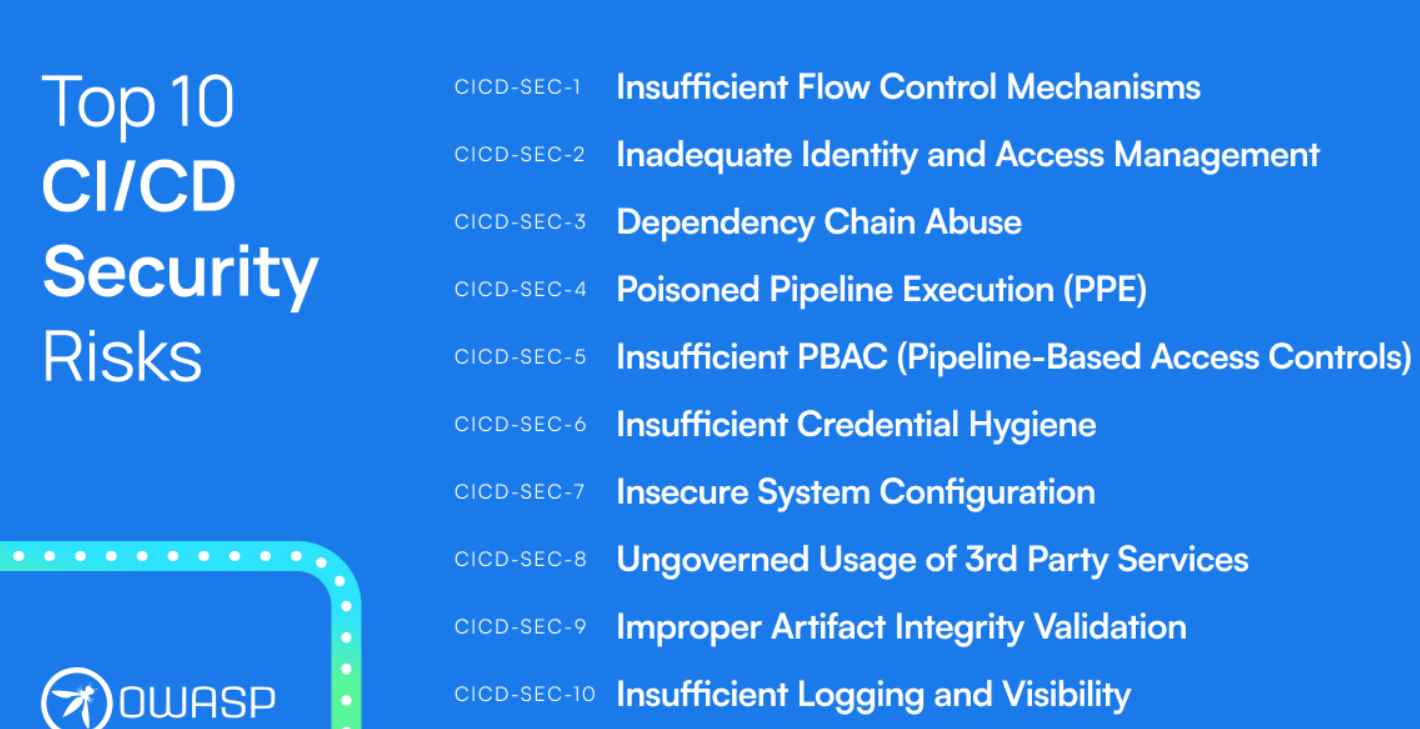
1.9KOWASP publishes Top 10 CI/CD Security Risks Guidelines
Any contemporary software company must have environments, procedures, and systems for continuous integration and continuous delivery. They transport the code written at...
-
 3.6K
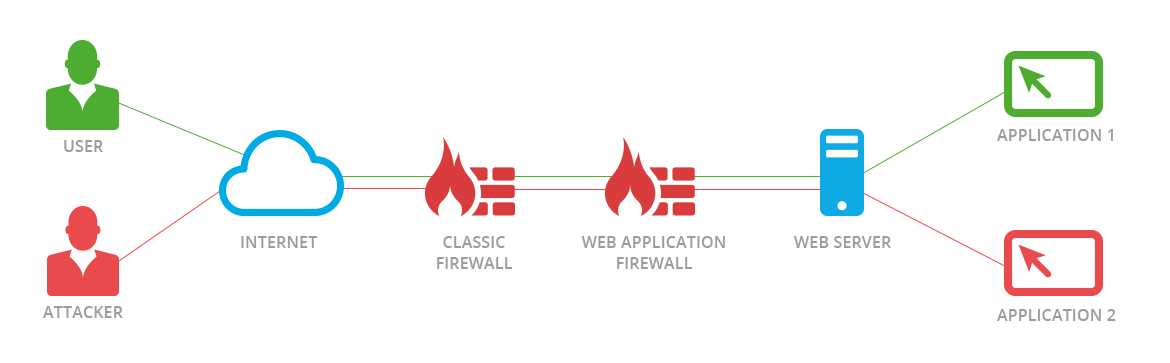
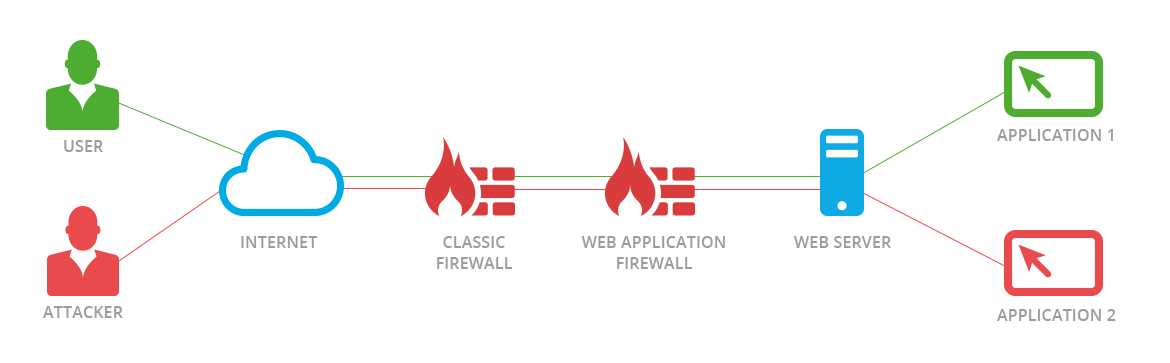
3.6KNew JSON-Based SQL Injection attacks allow bypassing Palo Alto, F5, AWS, Cloudflare, and Imperva WAF
Web application firewalls, also known as WAFs, are intended to protect web-based applications and application programming interfaces (APIs) from malicious HTTPS traffic...
-

 5.0K
5.0K6 reasons to secure your email in 2023 without investing much
Because companies either do not teach their staff enough or have inadequate email security measures in place, many firms, ranging from start-ups to...
-
 978
978Bad news! The platform certificates of many phone manufactures have been hacked. These are used to sign trusted apps on Android phones. Now these certificates are being used to certify malicious Android applications
Platform certificates, also known as platform keys, are used by OEM Android device makers to certify the core ROM images of their...
-
 2.9K
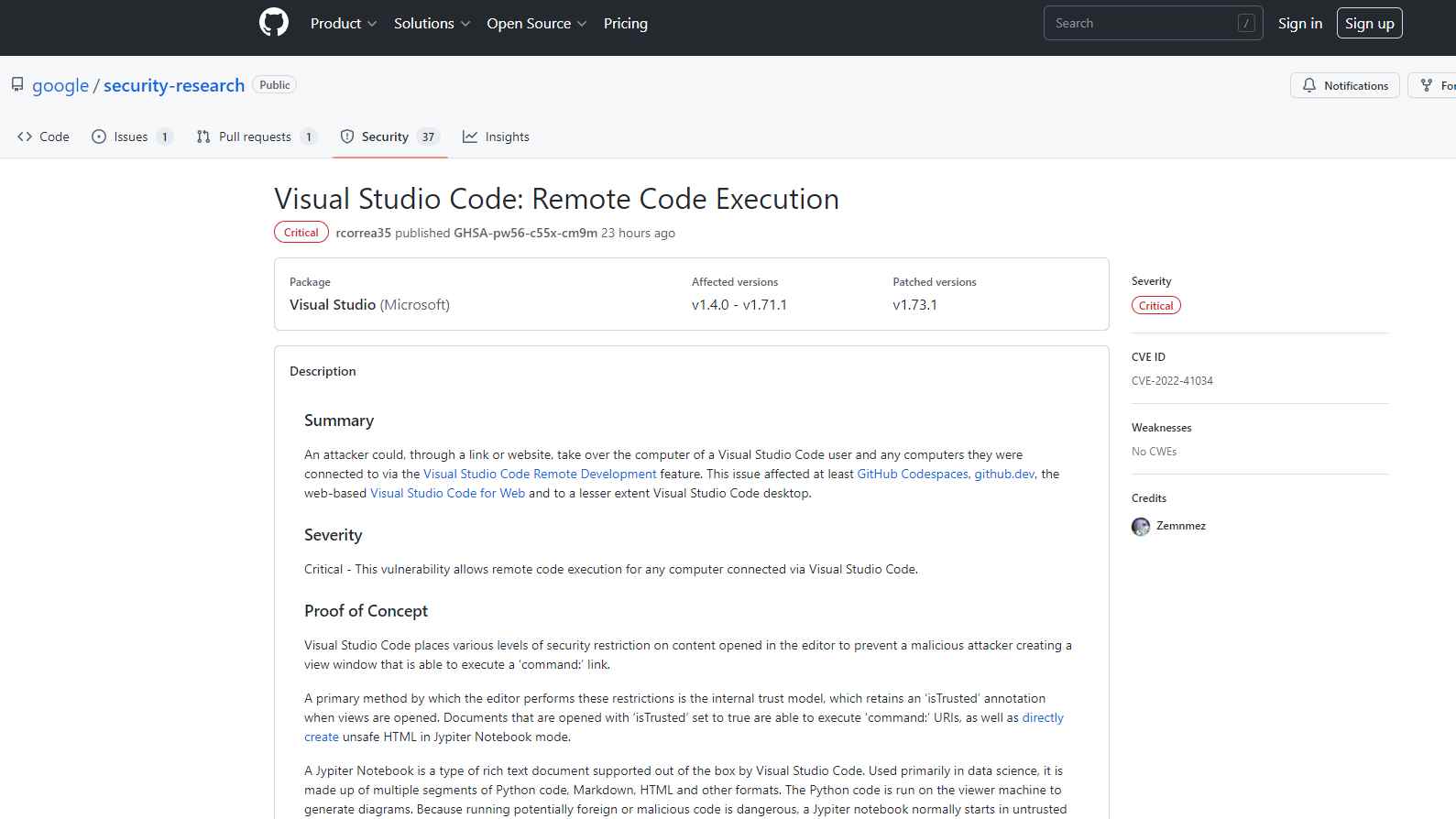
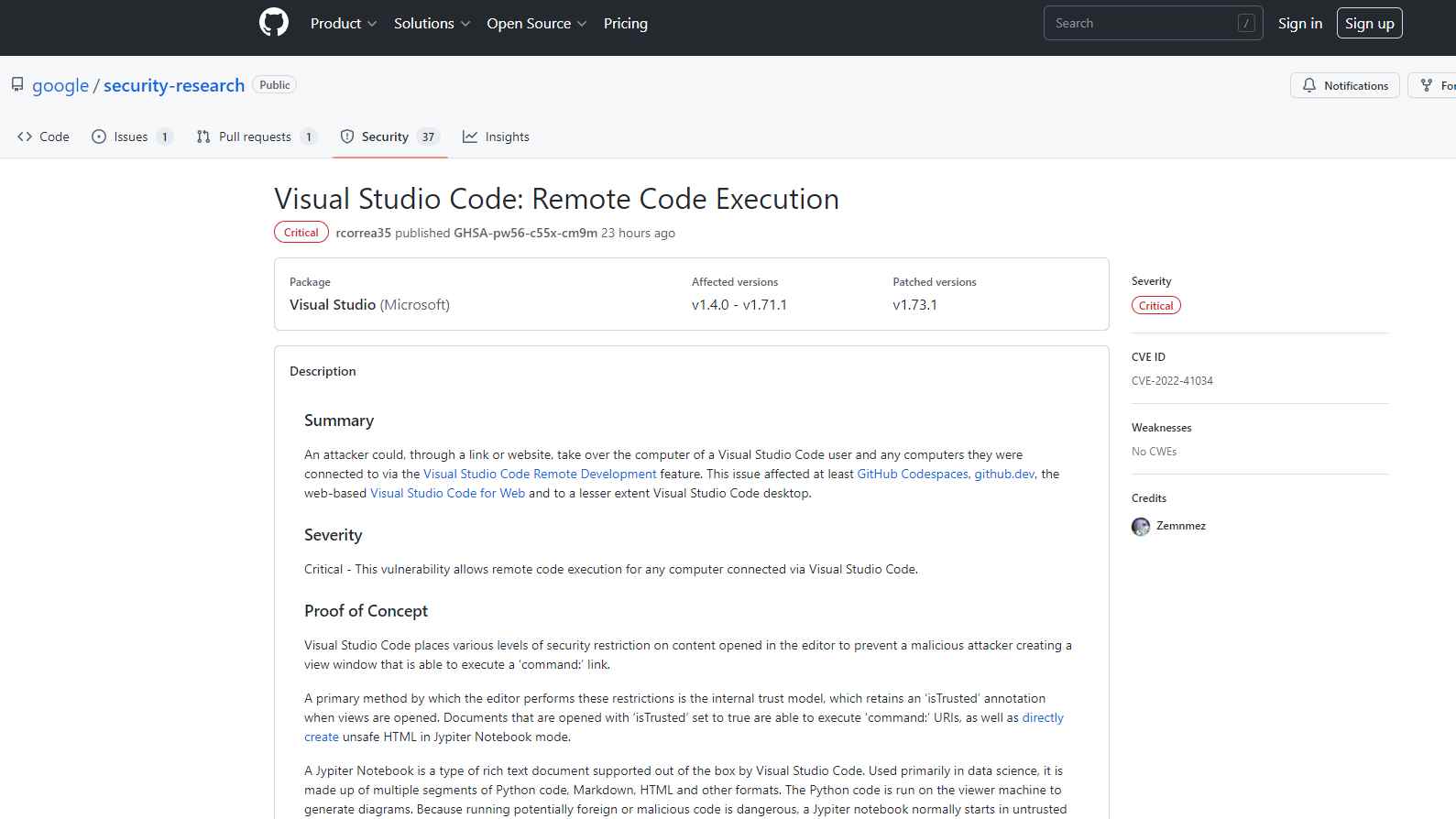
2.9KExploit PoC for Remote code execution flaw in Visual Studio Code released
The remote code execution vulnerability that affected Visual Studio Code and was fixed by Microsoft in October was the subject of a...
-

 896
896Seventy thousand individuals who police believe may have been victims of phone scams are receiving messages with instructions on what they should do next
Over 70,000 individuals are receiving text messages from the police informing them that they have been victims of online banking frauds and...
-

 1.0K
1.0KWhat should you do if your WhatsApp number is leaked by cybercriminals in the recent WhatsApp hack
A gang of hackers has been responsible for the hacking of WhatsApp in recent days, which resulted in the disclosure of a...
-

 3.7K
3.7KAustralian government is looking to hire hackers for its “hack back” program to disrupt ransomware gangs
Recent data breaches have driven fast reforms to Australia’s cybersecurity and data protection rules, and the most recent development looks to be...
-

 2.7K
2.7KMost exploited API Vulnerabilities in 2022
It is common knowledge that maintaining a high level of cyber security has rapidly become one of the top priorities for businesses...
-

 2.7K
2.7K3 Techniques that allow bypassing phishing emails through Cisco Secure Email Gateway and are being actively used by ransomware gangs
The following techniques have been made public by a researcher who wishes to remain anonymous. They can be used to bypass certain of...






