Data Security
-

 743
743GTA 5 Grand Theft Auto 5 Source Code published on GitHub
Yesterday evening, a number of Tweets with the “Grand Theft Auto V” source code appeared on social media. The source code was...
-
 3.7K
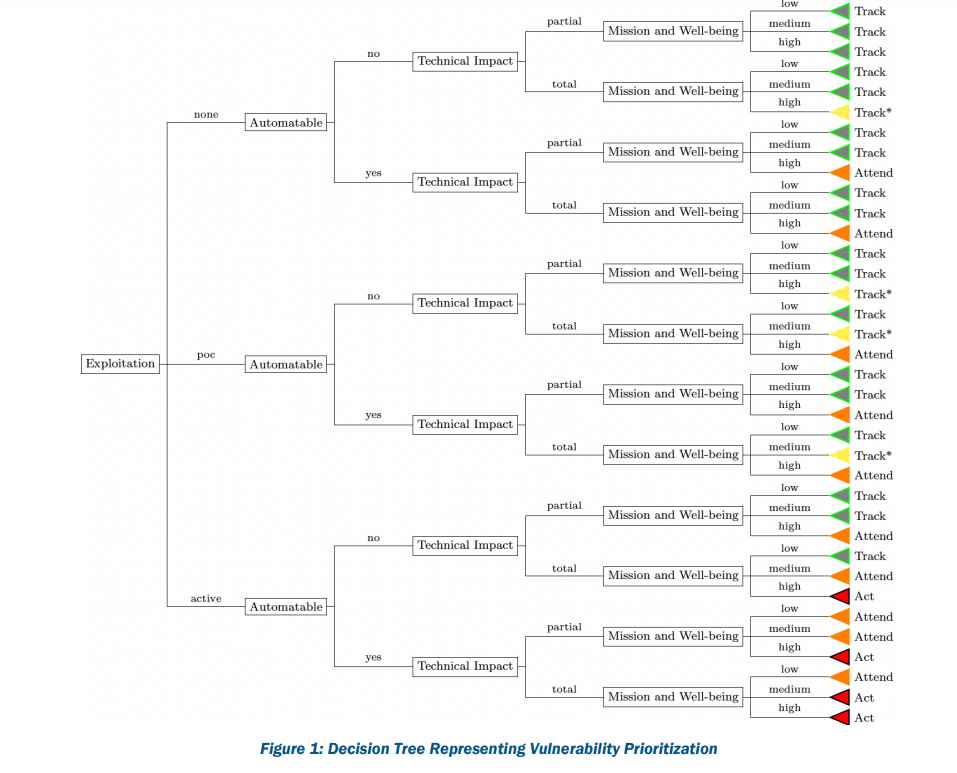
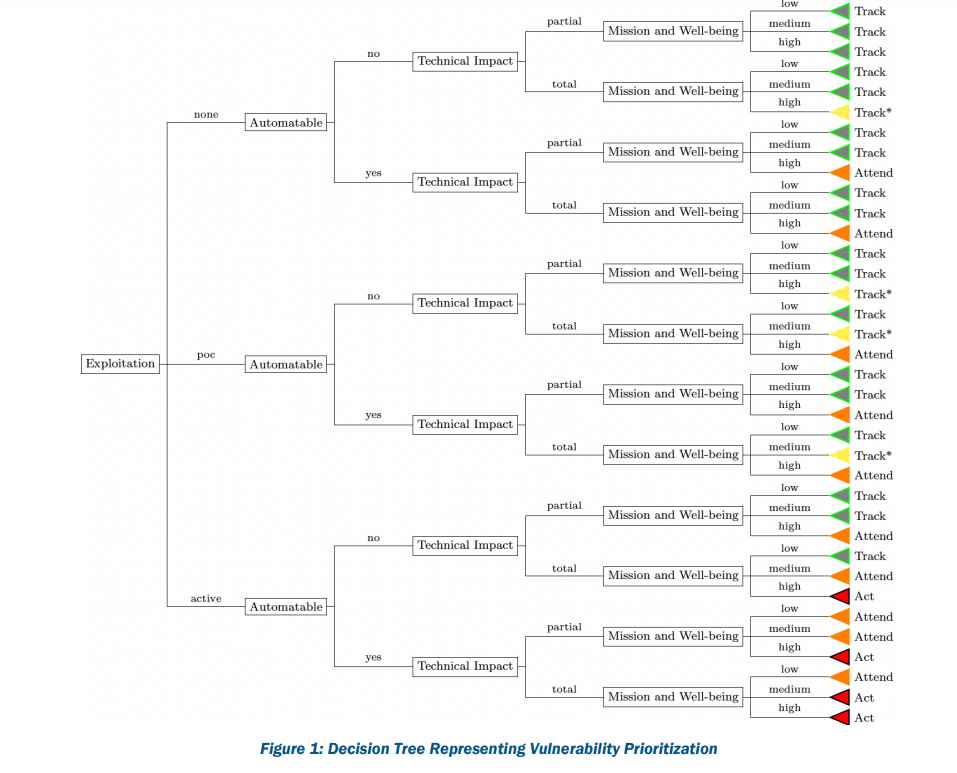
3.7K6 factors to consider for prioritizing remediation of vulnerabilities in a network using SSVC strategy
Given that 2021 set a record for the number of vulnerabilities disclosed and that threat actors improved their capacity to weaponize vulnerabilities,...
-

 3.5K
3.5KDon’t even think of taking your real smartphone to FIFA world cup matches in Qatar. Immigration officials will gain access to your phone data forever
It would be wise to get a burner phone if you were traveling to Qatar for the World Cup. Additionally, avoid taking...
-

 1.9K
1.9KAustralian government is issuing new driving licenses to millions and changing the license verification process because of the Optus data breach
Following the Optus data breach, Queenslanders are now required to give banks, telecoms, and utility firms a second number on their driver’s...
-

 1.1K
1.1KWhat is MFA, 2FA, 3FA and 4FA ? Just ways of user authentication?
Authentication is the process of demonstrating your identity. The user must verify their identity by supplying particular access credentials in order to...
-

 2.8K
2.8KUpdate firmware of these Lenovo ThinkBook, IdeaPad, and Yoga laptops models as 3 critical vulnerabilities allow them to be hacked forever, even after removing the hard drive
Critical flaws that affect many ThinkBook, IdeaPad, and Yoga laptop models have been resolved by Lenovo and may have allowed an attacker...
-
 5.0K
5.0KZ-Library biggest collection of 12 million pirated e-books shutdown by FBI & DOJ
The primary domain names under Z-ownership Library’s were lost. An updated seizure banner supports the hypothesis that the U.S. Department of Justice...
-
 1.4K
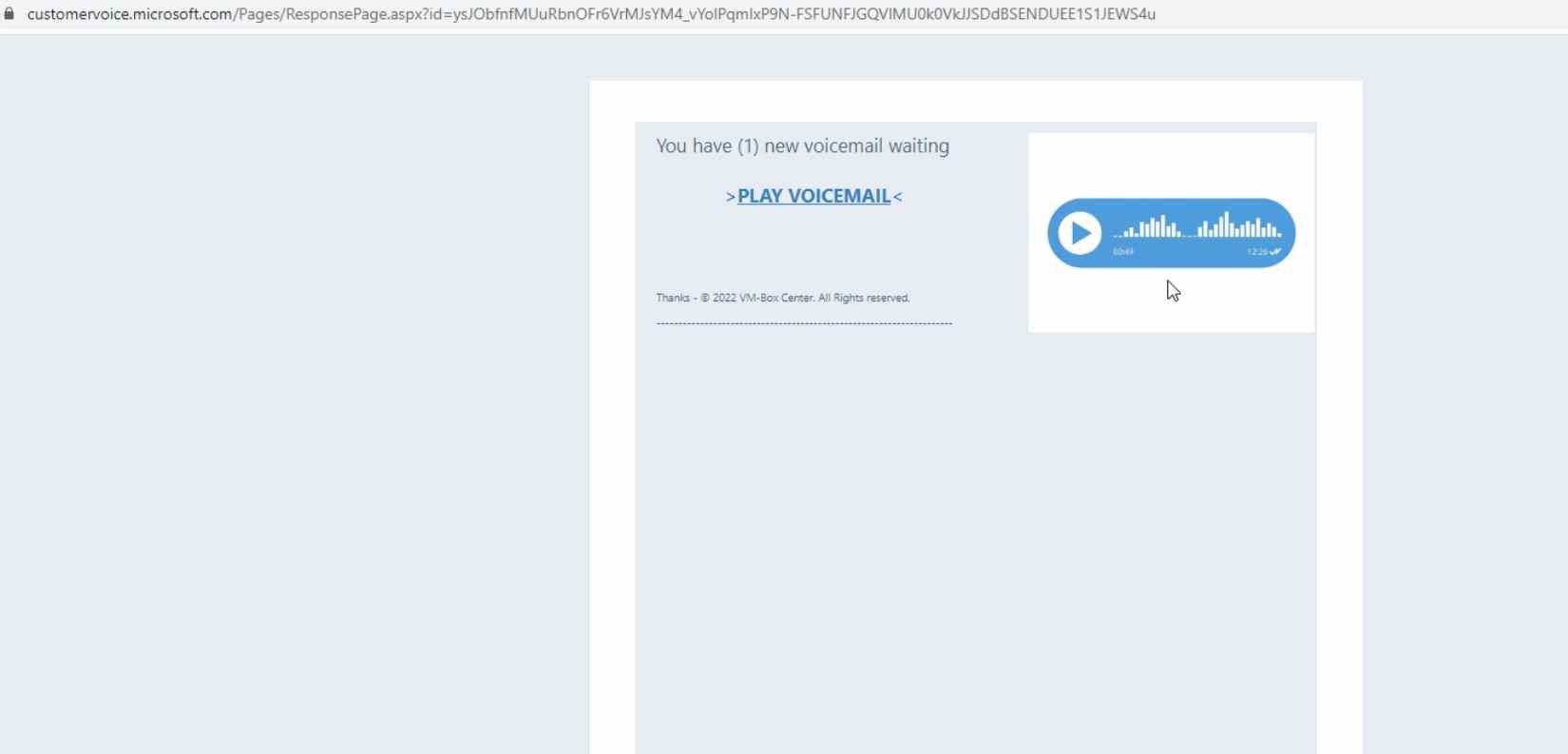
1.4KDon’t open emails from Microsoft Dynamics 365. Threat actors are exploiting its flaws to send phishing emails with legitimate Microsoft links
Microsoft’s Dynamics 365 Customer Voice is a software that is primarily used to collect customer feedback.It may be utilized to gather data...
-

 3.6K
3.6KHow a hacker who stole data of millions of people was tracked & arrested because his girlfriend uploaded this pic on Instagram
The United States Department of Justice has announced that a Ukrainian programmer has been charged, among other things, with computer and bank...
-

 3.4K
3.4KA proof-of-concept (PoC) exploit code released for critical privilege elevation vulnerability CVE-2022-37969 (CVSS score: 7.8) affecting Windows 10 & 11
The Windows Common Log File System (CLFS) Driver has an elevation of privilege vulnerability identified as CVE-2022-37969 (CVSS score: 7.8). For reporting...
-

 4.6K
4.6KMessage Encryption (OME) used by Office 365 can easily be broken to read encrypted emails via MiTM
The message encryption system employed by Microsoft in Office 365 has a system vulnerabilities, according to a warning from the Finnish cybersecurity...
-

 1.1K
1.1KGang of 31 cyber criminals arrested for stealing cars via hacking software
In a coordinated operation on October 10 throughout the three nations, 31 people were detained. A total of 22 addresses were raided,...
-

 4.3K
4.3KMinecraft Servers suffer Underwent a 2.5 Tbps DDoS Attack from the Mirai Botnet
According to Cloudflare, a Mirai botnet strain launched a distributed denial-of-service (DDoS) campaign that peaked at 2.5 terabytes per second (Tbps), making...
-
 4.3K
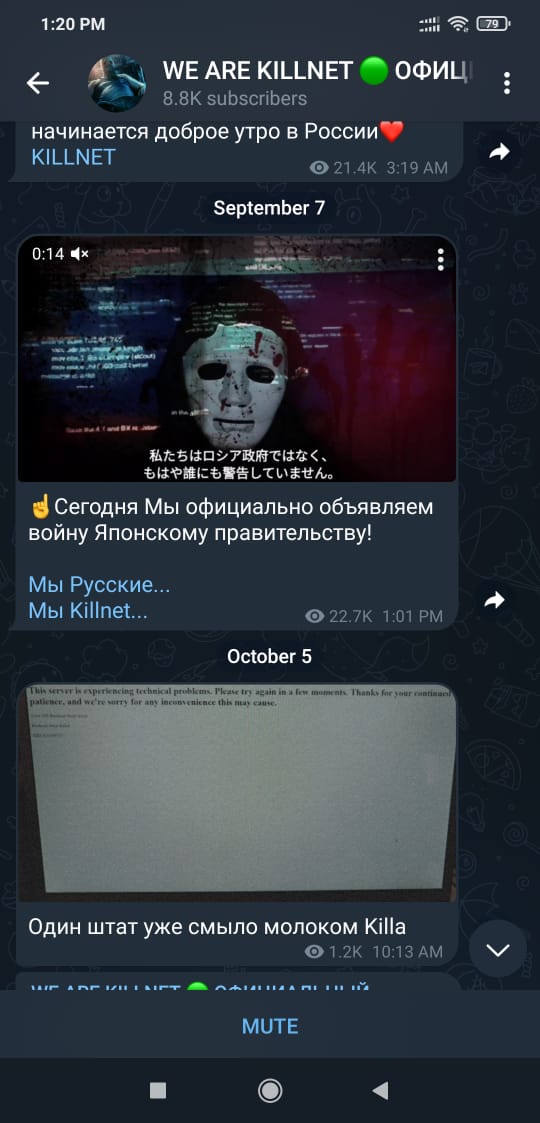
4.3KRussian hacker group Killnet launches USA OFFLINE: F**K NATO campaign to hack all governments websites
Over the next three days, Killnet hacking group intends to cause chaos on official US websites. State and federal websites are listed...
-

 4.5K
4.5KNew technique to jailbreak PlayStation PS5 published
Researchers have at last cracked the PlayStation’s security after nearly two years of work. The PS5 has been jailbroken and completely unlocked,...
-

 4.5K
4.5KHow Chinese threat actors are using recently discovered zero day flaws in office and Sophos firewall
By deploying a new Trojan named LOWZERO, integrated into an espionage campaign aimed against Tibetan organizations, the Chinese APT known as TA413...
-

 1.9K
1.9KAvast open sources two great YARA tools. YaraNG a YARA Scanner and YLS a YARA Development Environment
A well-known tool in the security sector for classifying and identifying malware samples is YARA. Avast just gave the open-source community two...
-
 3.6K
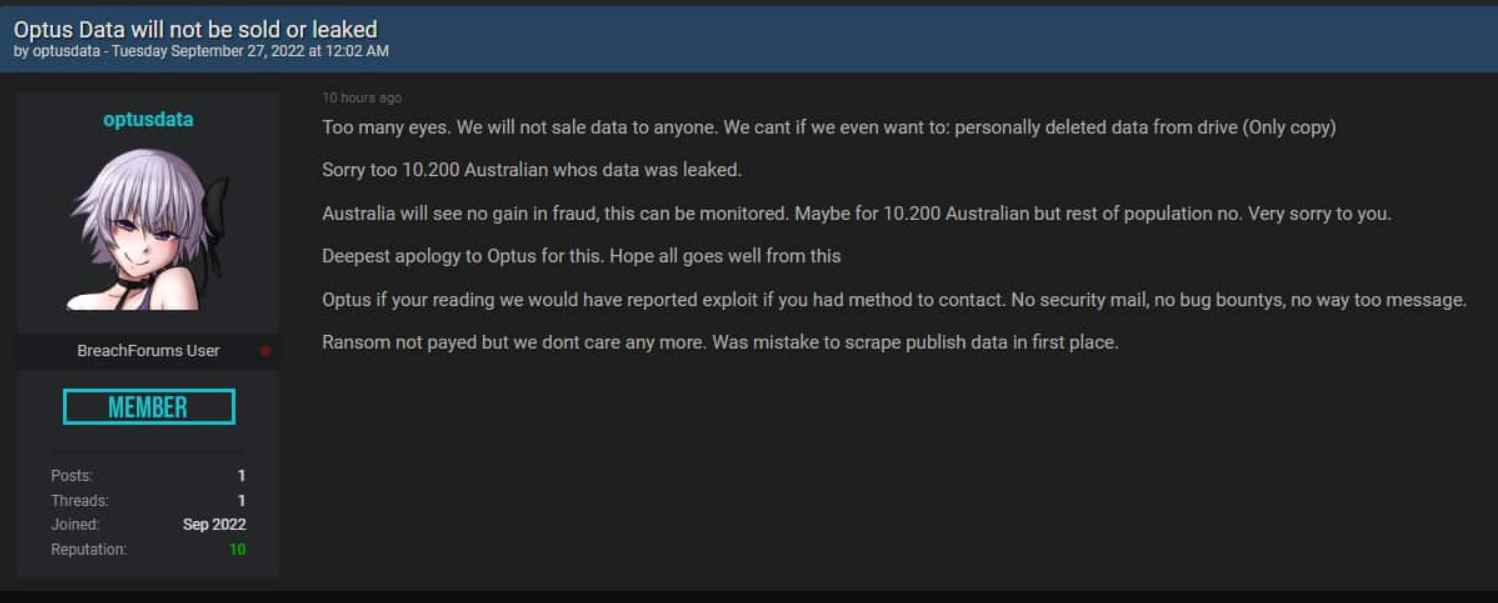
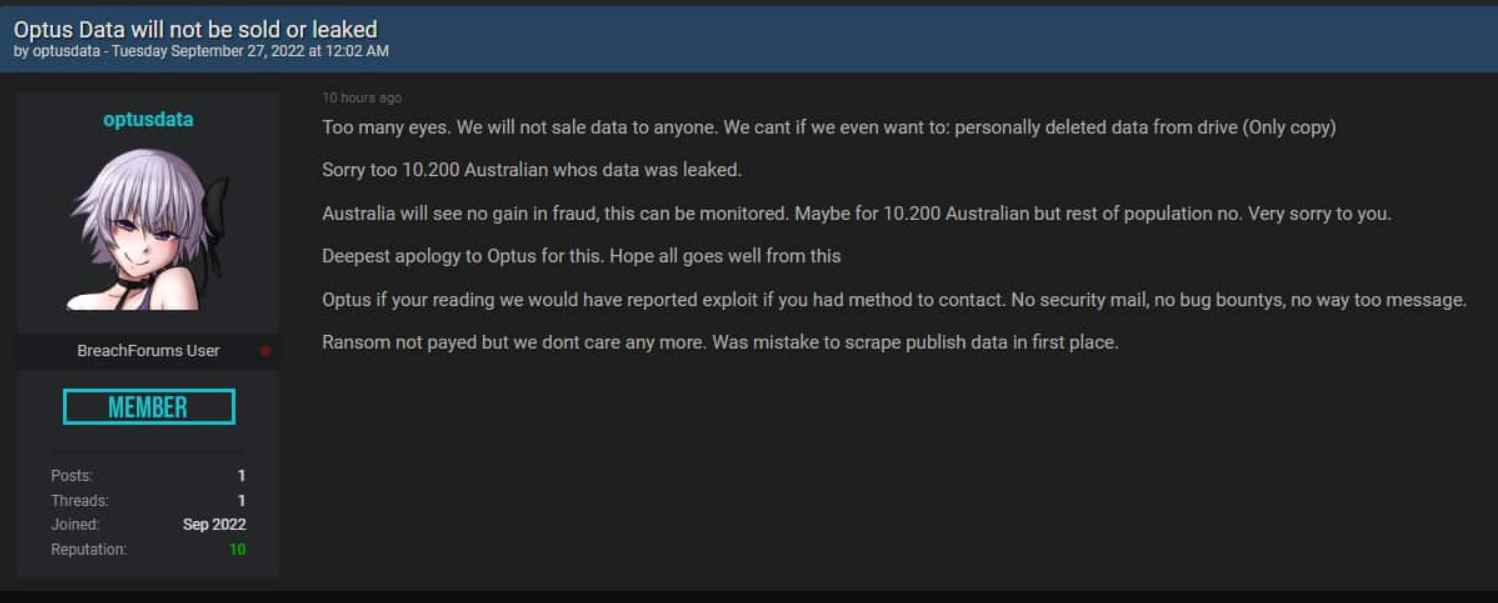
3.6KHacker who leaked data of millions of Australians is regretting his act and asking for an apology
A hacker who allegedly targeted Optus, Australia’s second-largest telecom company, and stole the personal information of millions of Australians, has posted more...
-

 664
664How fake news of “coup” in China and arrest of Xi Jinping started and who was responsible for spreading it
A rumor about the arrest of Chinese President Xi Jinping surfaced on Twitter last weekend. The source of this false information was...
-

 1.3K
1.3KPhishing alert: Giving your condolences for Queen Elizabeth II can leave your data in the hands of cybercriminals
Cybercriminals are taking advantage of the death of Queen Elizabeth II to launch phishing attacks, specifically these scammers directing users to malicious...
-

 2.3K
2.3KBiggest taxi firm in Russia hacked to order all the cabs to same place at once. Causing huge traffic jam like in James Bond movie
Unlike what happens worldwide, Google is not the first search engine in Russia, but a giant that brings together different services and...






