Data Security
-

 176
176Chinese Hackers Breached LoopPay, Whose Tech Is Central to Samsung Pay
Months before its technology became the centerpiece of Samsung’s new mobile payment system, LoopPay, a small Massachusetts subsidiary of the South Korean...
-

 169
169SHA1 algorithm securing e-commerce and software could break by year’s end
Researchers warn widely used algorithm should be retired sooner. SHA1, one of the Internet’s most crucial cryptographic algorithms, is so weak to...
-

 114
114Bitcoin Transactions Were Under Attack for a Week, Prankster Reveals Himself
Transactions were being duplicated in a malleability attack.A Russian man that calls himself “Alister Maclin” has been disrupting the Bitcoin network for...
-

 110
110New Moker RAT Bypasses Detection
Researchers warned Tuesday the latest APT to make the rounds features a remote access Trojan that can effectively mitigate security measures on machines and grant...
-

 100
100Creators of the Benevolent Linux.Wifatch Malware Reveal Themselves
Linux.Wifatch’s creators call themselves The White Team.The Linux.Wifatch malware, also dubbed as the “vigilante malware” has been going around the Internet, infecting...
-
 203
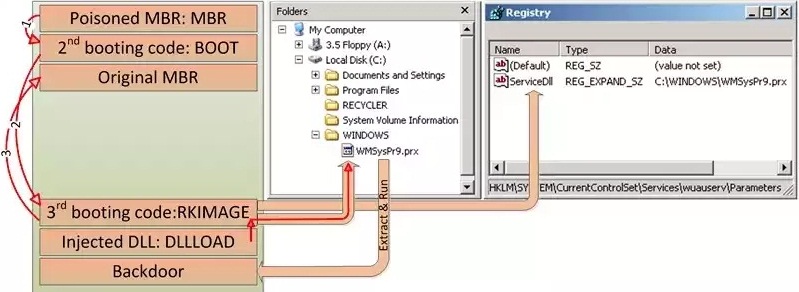
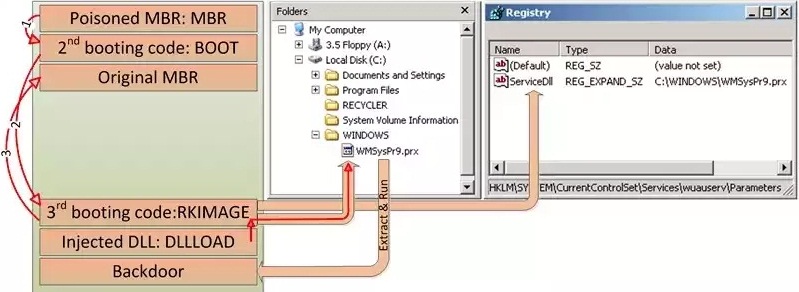
203HDRoot Bootkit Impersonates Microsoft’s Net Command
HDRoot is the work of the Winnti APT group. Hackers activating mainly in South-East Asia have developed a new bootkit trojan, which disguises...
-

 180
180Meet The New Virus Protecting Routers From Hackers
For hackers, routers are an easy target, perhaps because they are seldom updated and virus-scanned and are also easily cracked. But shockingly,...
-

 162
162How I could hack internet bank accounts of Danish largest bank in a few minutes
In August I visited the Chaos Communication Camp near Berlin. Once every four years this great and world’s greatest hacker festival is...
-

 183
183Hacking Wireless Printers With Phones on Drones
YOU MIGHT THINK that working on a secured floor in a 30-story office tower puts you out of reach of Wi-Fi hackers...
-

 184
184How to Hack and Decrypt WhatsApp Database on rooted devices
The post includes a detailed procedure to hack and decrypt WhatsApp Database remotely on rooted Android mobile devices. Very Interesting!. A few...
-

 85
85VW’s ‘neat hack’ exposes danger of corporate software
It was only old-fashioned detective work that forced Volkswagen to admit to the existence of its ‘defeat device’. And that should worry...
-

 315
315How to do hacking attacks over satellite communications?
Hack Satellite comunication In this article we will cover satellite based hacking attack which has been used by hacking groups since...
-

 383
383HOW TO INTERCEPT SATELLITE COMMUNICATIONS EASILY?
In today world we use satellite communication in many respects and industries and we all know how important they are in our...
-

 315
315Hackers Can Exploit Security Flaws In Drones To Hijack Flight Controller
Security flaws have been found in drones that could allow hackers to target and attack the flight controller which includes numerous sensors...
-

 165
165Car-Hacking Tool Turns Repair Shops Into Malware ‘Brothels’
the security research community has proven like never before that cars are vulnerable to hackers—via cellular Internet connections, intercepted smartphone signals, and...
-
 215
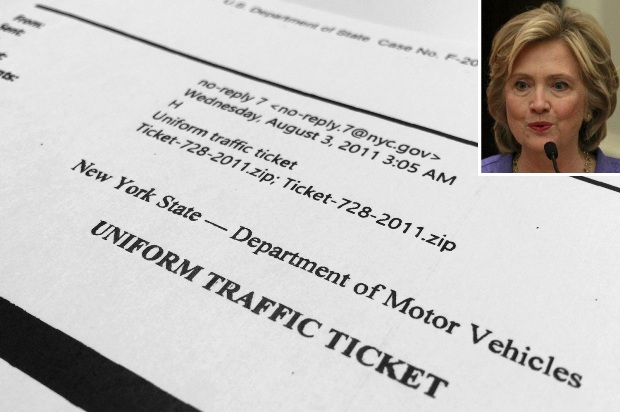
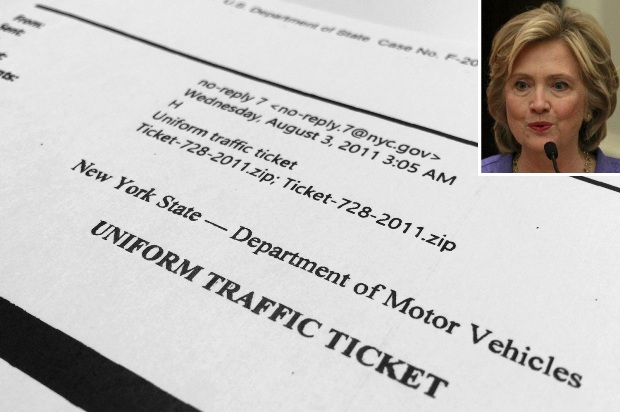
215Russian hackers tried to infiltrate Hillary Clinton’s home server
Hackers with links to Russia tried to infiltrate Hillary Rodham Clinton’s home e-mail server at least five times — even as other...
-
 154
154FBI: We unmasked and collared child porn creep on Tor with spy tool
Dark-web deadbeats may not be as anonymous as they think. A bloke in the US was charged on Friday after FBI spyware...
-

 107
107Cyber-Criminals Throw Molotov Cocktails at Dr.Web Antivirus Headquarters After Being Exposed
Cyber-crime syndicate tried to intimidate antivirus vendor. In some cases, cyber-security work can turn really dangerous, and even deadly, if you manage to...
-

 204
204XOR DDoS Attack Tool Being Used to Launch Over 20 Daily Attacks
Threat actors are using a previously discovered distributed denial-of-service (DDoS) attack tool dubbed XOR DDoS to launch upwards of 20 DoS attacks...
-

 266
266Edward Snowden joins Twitter and follows NSA
Fugitive US intelligence contractor Edward Snowden has opened an account on the social network website Twitter. His opening tweet was: “Can you...
-

 181
181Pirate Bay co-founder Gottfrid Svartholm Warg—aka Anakata—exits prison
Pirate Bay is online and playing a game of cat and mouse with IP regulators. Pirate Bay co-founder Gottfrid Svartholm Warg was released...






