Data Security
-

 191
191Stuxnet-style code signing of malware becomes darknet cottage industry
Even reports of crims offering signing-as-a-service. Underground cybercrooks are selling digital certificates that allow code signing of malicious instructions, creating a lucrative...
-
 236
236Return of the EXIF PHP Joomla Backdoor
Our Remediation and Research teams are in constant communication and collaboration. It’s how we stay ahead of the latest threats, but it...
-

 212
212Security Researcher Creates Tool to Extract Passwords from KeePass Databases
Denis Andzakovic, a security researcher for Security Assessment, has created a tool that can fool the KeePass password manager into exporting its...
-
 110
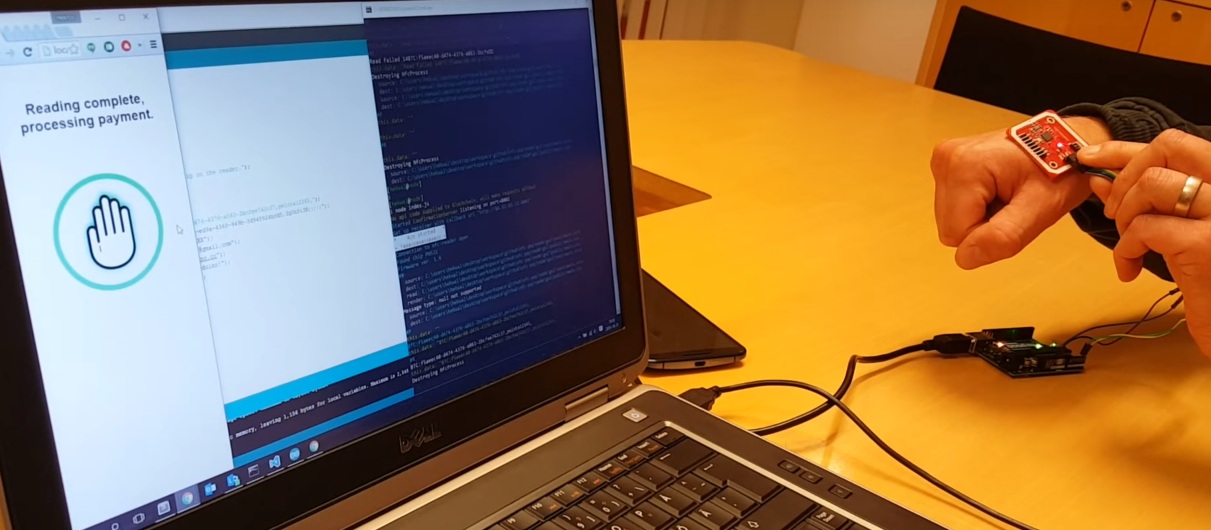
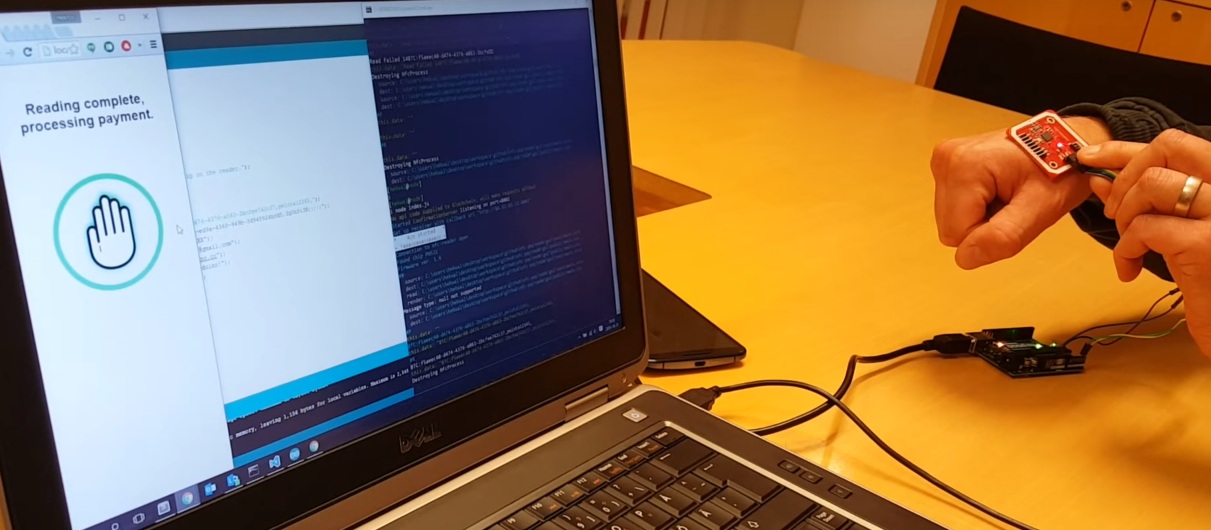
110This Chip Is Implanted Under The Skin And Used To Pay For Things Using Bitcoin
Wallets are becoming more integrated with other things. Soon, we might all use our phones as a way to pay for things....
-
 136
136Browser-Based iOS 9.1/9.2 Jailbreak Wins $1M Bounty, Will Be Sold for Corporate and Government Use
Earlier this month, exploit acquisition platform Zerodium debuted an iOS 9 bug bounty that would pay out up to three million dollars...
-

 119
119Android Malware Disguises itself as MS Word Doc, Spies on Your Phone
Researchers have discovered an Android malware disguising itself as a Microsoft word document which triggers a malicious code once opened. This Android malware was...
-

 188
188How to exploit new Facebook feature to access personal photos of people without being their friend?
Facebook’s is always changing and its team is adding new functionality every couple of months. With new changes there are chances of...
-

 85
85Yahoo’s “crypto witch” exploits web security feature, learns your site history
Timing attacks are an interesting part of computer security. As an extreme example, imagine that your computer took one second to verify...
-

 248
248Snapchat to save, modify and republish your private photos
Snapchat’s new term and conditions have resulted in outrage from its users and twitter has been flooded with tweets from users rejecting...
-

 120
120Leaving Laptops in Hotel Rooms: A Bad Idea
A laptop filled with data? An external HDD filled with even more data? There’s bound to be a phone – possibly two...
-

 330
330Vodafone Hacked, Customers’ Personal Data, Banking Information Stolen
In the wake of the TalkTalk Scandal, Vodafone finally admitted that hackers did manage to steal around 20,000 Vodafone customers’ bank details....
-

 83
83Home Network Analysis: DVRs and my Network Interact
My last on-topic post pontificated about the dangers and surprise of letting third parties into your house or codebase, where I discussed the...
-
 247
247European Parliament offers support to Edward Snowden
The European Parliament has voted in favour of a resolution that calls on all EU member states to “drop any criminal charges...
-
 164
164Report: CryptoWall Creators Earned $325 Million in Bitcoin Ransoms
A cyber-security industry group has published new research on the CryptoWall ransomware campaign, finding that the attacks have generated more than $300m...
-

 141
141Google merging Chrome OS and Android? Not so fast
The two platforms drive different devices. But would combining them really be a bad thing? On Thursday, the The Wall Street Journal...
-

 188
188Tor launches anti-censorship Messenger service
A new chat tool has been launched in an effort to improve the security of online messaging. Tor Messenger allows users to...
-

 163
163IETF recognizes .onion as special-use domain name
Calling the formal recognition of the .onion as a Special-use Domain Name by the Internet Engineering Task Force (IETF) “a small and...
-

 323
323Hacker Steals, Drives Away Jaguar XFR Exploiting Flaw in Wireless System
A silver Jaguar XFR parked in a parking lot in Auckland, New Zealand was stolen with the help of a hacking device that sends...
-
 95
95Google HTTP Search, yes, it is still possible
Google began to implement SSL on its search engine back in 2010. First on its own domain name, then as a...
-

 77
77US Army Experts Call for military bug bounty program AVRP
US Army Military experts urge the establishment of an Army Vulnerability Response Program (AVRP), a sort of military bug bounty program. What...
-
 229
229Timing attack vulnerability in most Zeus server-sides
Timing attacks has proven practical since 96′ as shown in a paper by Paul C. Kocher. In his paper Paul demonstrate how,...






