Data Security
-

 175
175Secure messaging service Telegram blocks 78 ISIS-related channels
Telegram, the popular instant messaging service that offers end-to-end encryption, announced on Wednesday that they have “blocked 78 ISIS-related channels across 12...
-

 158
158Here’s a Spy Firm’s Price List for Secret Hacker Techniques
THE TRADE IN the secret hacker techniques known as “zero day exploits” has long taken place in the dark, hidden from the...
-
 166
166Spam Campaign Causes “DDoS” by Googlebot
Every once in a while we get a glimpse into rare and strange behavior that doesn’t involve the website being hacked, but...
-

 119
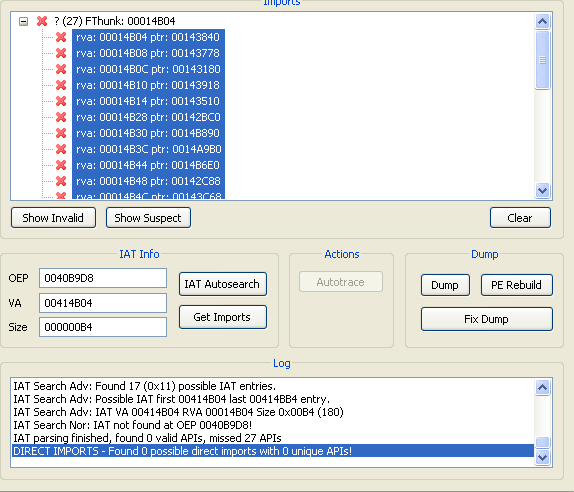
119Carnegie Mellon Denies FBI Paid for Tor-Breaking Research
CARNEGIE MELLON’S researchers pulled their talk on cracking the protections of the anonymity software Tor from the schedule of the Black Hat...
-

 181
181Seized: Fake EFF .org linked to hackers hitting NATO, White House PCs
Digital rights group takes down Pawn Storm base. The (EFF) has been awarded control of its namesake domain, which was being used...
-
 107
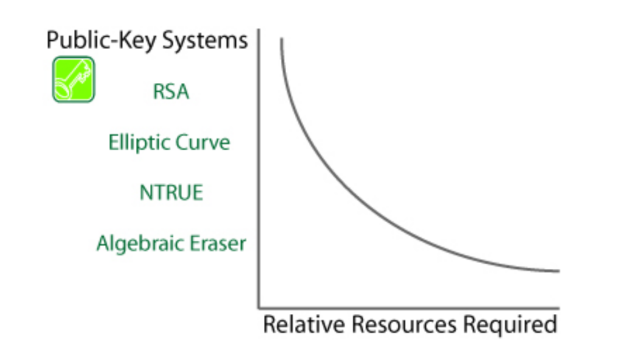
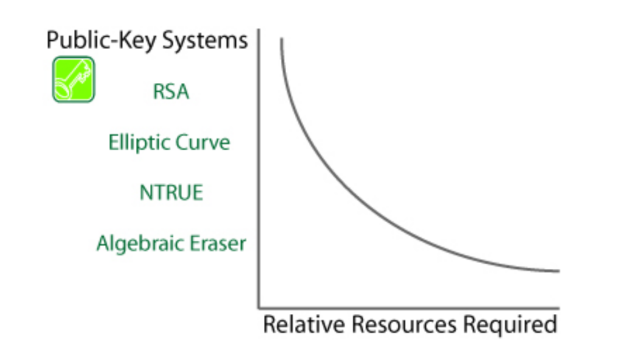
107Why Algebraic Eraser may be the riskiest cryptosystem you’ve never heard of
A potential standard for securing network-connected pacemakers, automobiles, and other lightweight devices has suffered a potentially game-over setback after researchers developed a...
-

 318
318ISIS May Have Used Sony PS4 to Plan Paris Attacks
French authorities after the Paris attacks are busy trying to find the source using which the whole massacre was planned. Last Friday,...
-
 319
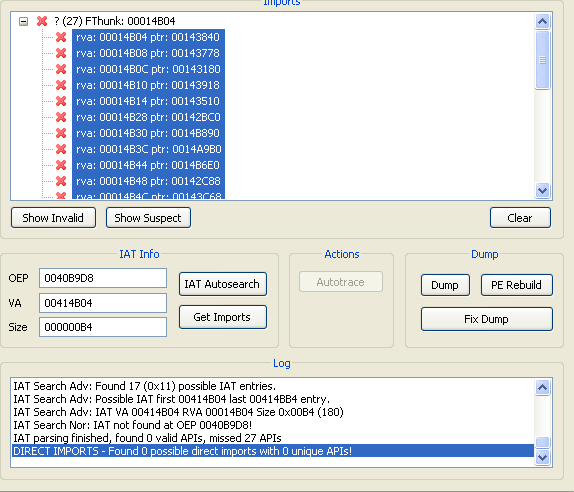
319A Guide to Malware Binary Reconstruction
Often we come across times where binary reconstruction while analyzing malware / unpacking malware is required . Taking leverage of automated tools...
-

 336
336BitLocker popper uses Windows authentication to attack itself
Microsoft squashes offline logic flaw that makes lost laptops dynamite. Blackhat Europe Synopsys security boffin Ian Haken says un-patched PCs in enterprises...
-

 133
133Linux.Encoder.1 Ransomware Spreads to 3,000 Websites
Expect a new ransomware version in the coming weeks.The Linux.Encoder.1 ransomware, a special strand that has a taste for Web hosting and...
-

 305
305Hacker Develops Undisputed KillerRat to Spy on Windows PCs
Egyptian Hacker Uses njRAT Codebase to Create KillerRat — The RAT goes completely hidden upon scanning. A new Remote Access Trojan/RAT has...
-

 152
152Anonymous Announces Payback for ISIS Paris Attacks
It didn’t take long for Anonymous members to rally and swear payback for the recent ISIS terror attacks that took place in...
-

 165
165Brazilian Army Gets Hacked Following Cyber-Games Cheating Accusations
Hackers leak data of over 7,000 officers. Hackers who declined to name themselves hacked the servers of the Brazilian Army, and later leaked...
-

 153
153CSI: CYBER SOMEHOW DIDN’T GET CAR HACKING TOTALLY WRONGCSI: CYBER SOMEHOW DIDN’T GET CAR HACKING TOTALLY WRONG
CSI: Cyber is known more for absurd drama than technical coherence, but it’s a big deal that hacking’s become so visible that...
-

 265
265Researchers Discover Two New Strains of POS Malware
Point of sale malware has gotten more sophisticated as we inch closer to the two-year anniversary of the Target data breach. Now,...
-
 89
89Tor: FBI Paid CMU $1 Million to De-Anonymize Users
More than a year ago, the Tor Project patched its software against a vulnerability being exploited by researchers at Carnegie Mellon University,...
-

 174
174Tablets with Pre-installed Trojan Being Sold on Amazon
Recently, researchers from the Cheetah Mobile Security Lab have found a dangerous Trojan, dubbed Cloudsota, pre-installed on certain Android tablets. Tablets infected...
-

 76
76SAP Security Patch for November 2015 Released
This post by SAP Product Security Response Team shares information on Patch Day Security Notes* that are released on second Tuesday of...
-

 94
94Facebook told by Belgian court to stop tracking non-users
A court has given Facebook 48 hours to stop tracking people in Belgium who are not members of its social network. Facebook...
-

 101
101Flaw in Linux.Encoder1 ransomware reveals the decryption key
Experts at Bitdefender have discovered a flaw in Linux Encryption Ransomware Linux.Encoder1 that exposes the decryption Key used to lock the files....
-

 166
166Badly coded ransomware locks away data forever
Coding mistakes in a malicious program that encrypts data mean anyone hit by the Power Worm virus will not be able to...






